Cisco SD-WAN zero-day vulnerability exploited since 2023, granting full admin access to attackers
Published on: 2026-02-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Hackers abused Cisco SD-WAN zero-day since 2023 to gain full admin control
1. BLUF (Bottom Line Up Front)
A critical vulnerability in Cisco SD-WAN systems, exploited since 2023, allows attackers to gain full administrative control, posing significant risks to critical infrastructure. The threat actor, identified as UAT-8616, is highly sophisticated and has been active for at least three years. Immediate patching is essential to mitigate risks. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The exploitation of the Cisco SD-WAN vulnerability is primarily conducted by a state-sponsored actor aiming to infiltrate critical infrastructure. This is supported by the sophistication of the attack and the targeting of high-value networks. However, the specific state affiliation remains unconfirmed.
- Hypothesis B: The exploitation is conducted by a non-state actor, such as a cybercriminal group, motivated by financial gain or data theft. The use of sophisticated techniques could be indicative of a well-funded criminal organization rather than a state actor.
- Assessment: Hypothesis A is currently better supported due to the complexity and strategic nature of the targets, suggesting state-level resources and objectives. Indicators that could shift this judgment include evidence of financial transactions or demands linked to the exploitation.
3. Key Assumptions and Red Flags
- Assumptions: The actor’s sophistication implies access to significant resources; the vulnerability is a primary vector for network access; affected organizations have not yet fully patched systems.
- Information Gaps: Specific attribution to a state actor, the full scope of affected entities, and the actor’s ultimate objectives remain unclear.
- Bias & Deception Risks: Potential confirmation bias in attributing the attack to state actors; reliance on Cisco’s reporting could introduce source bias.
4. Implications and Strategic Risks
This development could lead to increased tensions in cyber diplomacy and a reevaluation of network security protocols globally. The exploitation of network edge devices highlights vulnerabilities in critical infrastructure.
- Political / Geopolitical: Potential for increased geopolitical tensions if state sponsorship is confirmed.
- Security / Counter-Terrorism: Heightened threat environment for critical infrastructure, necessitating enhanced security measures.
- Cyber / Information Space: Increased focus on securing network edge devices and potential for further sophisticated cyber operations.
- Economic / Social: Potential economic impact from disrupted services and increased cybersecurity spending.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently apply Cisco’s security patches, conduct network audits, and enhance monitoring for suspicious activity.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing, invest in cybersecurity training, and review network security architectures.
- Scenario Outlook:
- Best: Rapid patching and threat mitigation prevent further exploitation.
- Worst: Exploitation leads to significant disruptions in critical infrastructure.
- Most-Likely: Continued exploitation attempts with varying success, leading to incremental security improvements.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
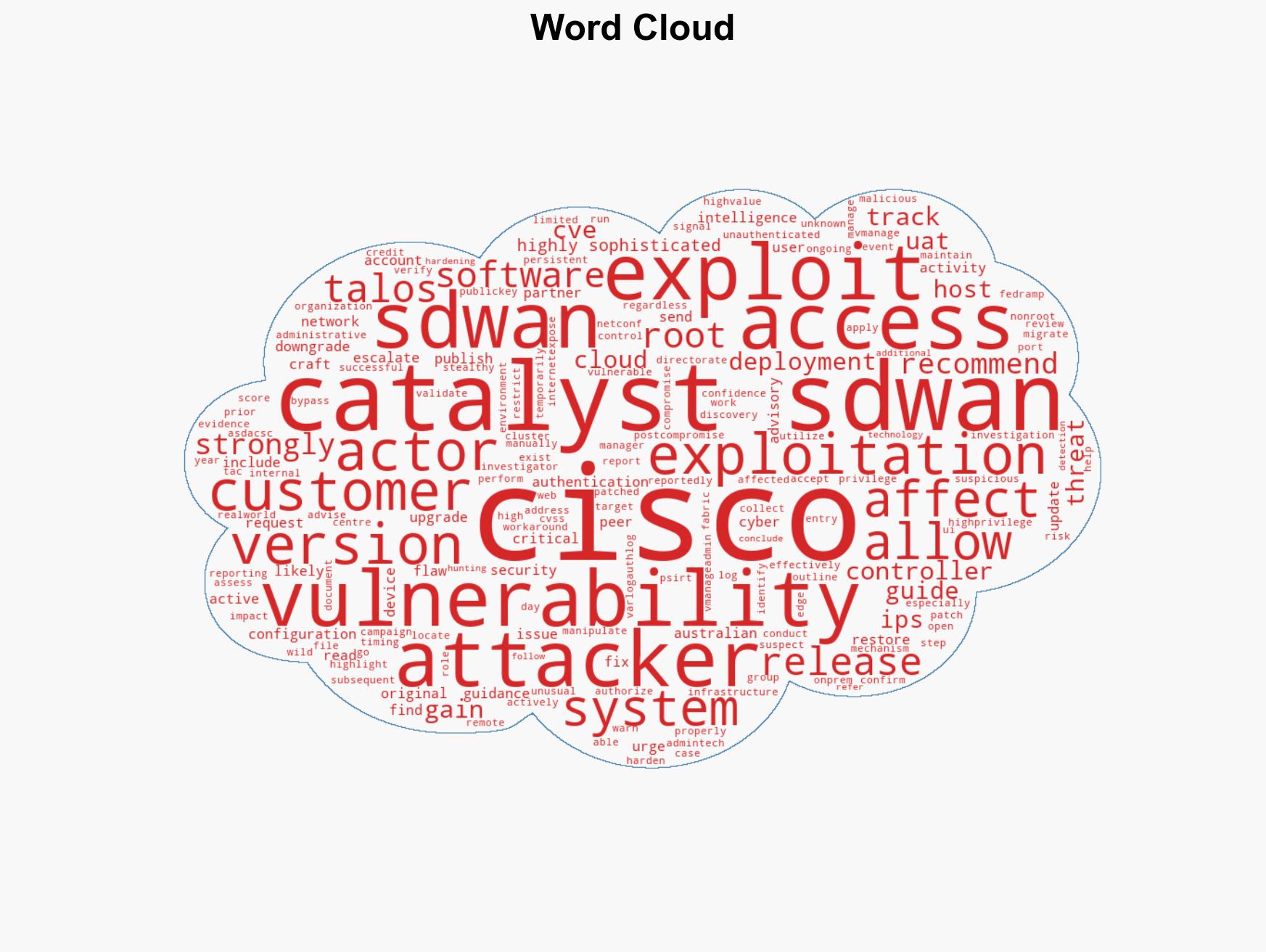
cybersecurity, critical infrastructure, state-sponsored threats, network vulnerabilities, cyber-espionage, Cisco SD-WAN, zero-day exploitation
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us