Cisco warns of CSLU backdoor admin account used in attacks – BleepingComputer
Published on: 2025-04-02
Intelligence Report: Cisco warns of CSLU backdoor admin account used in attacks – BleepingComputer
1. BLUF (Bottom Line Up Front)
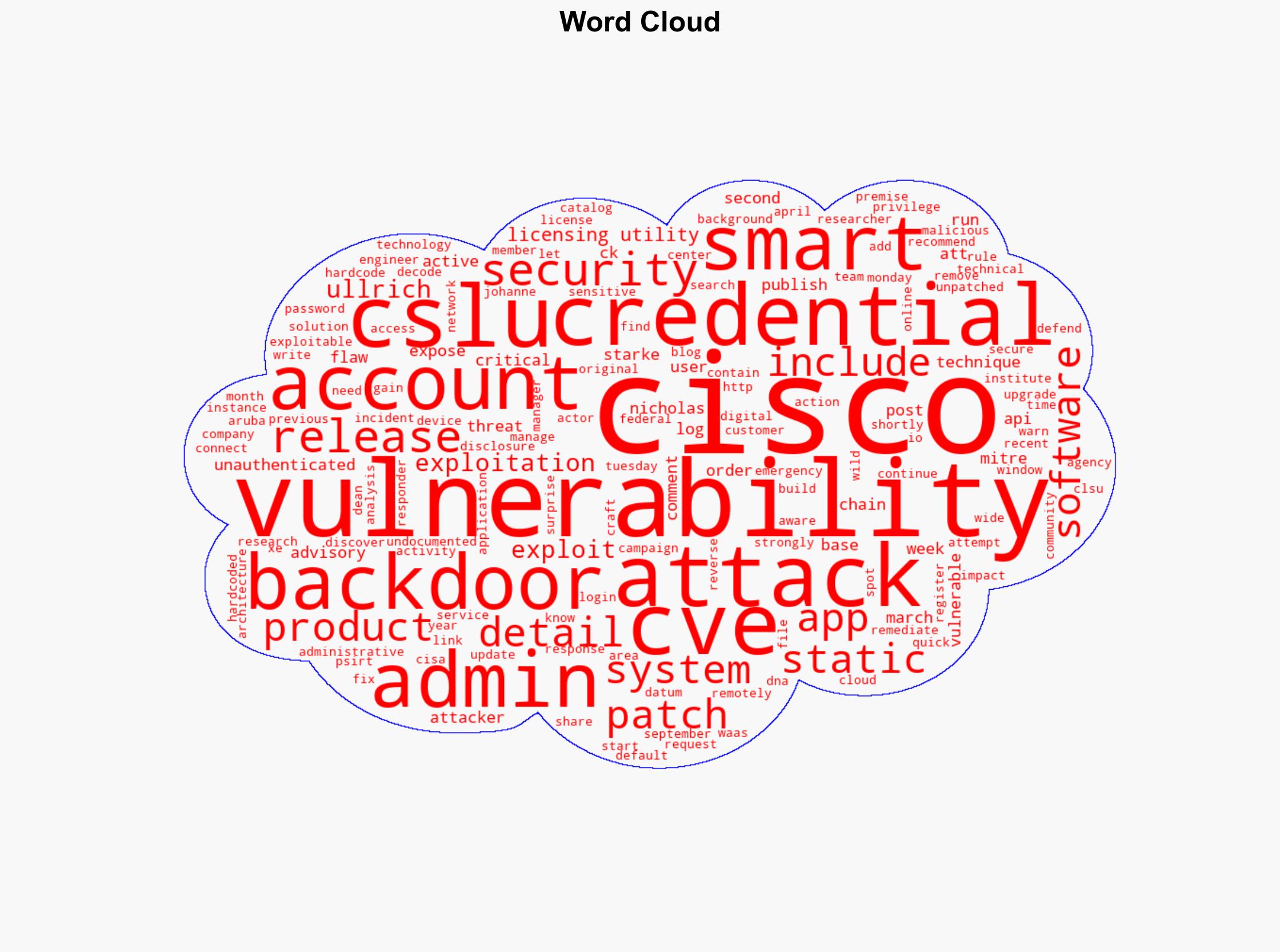
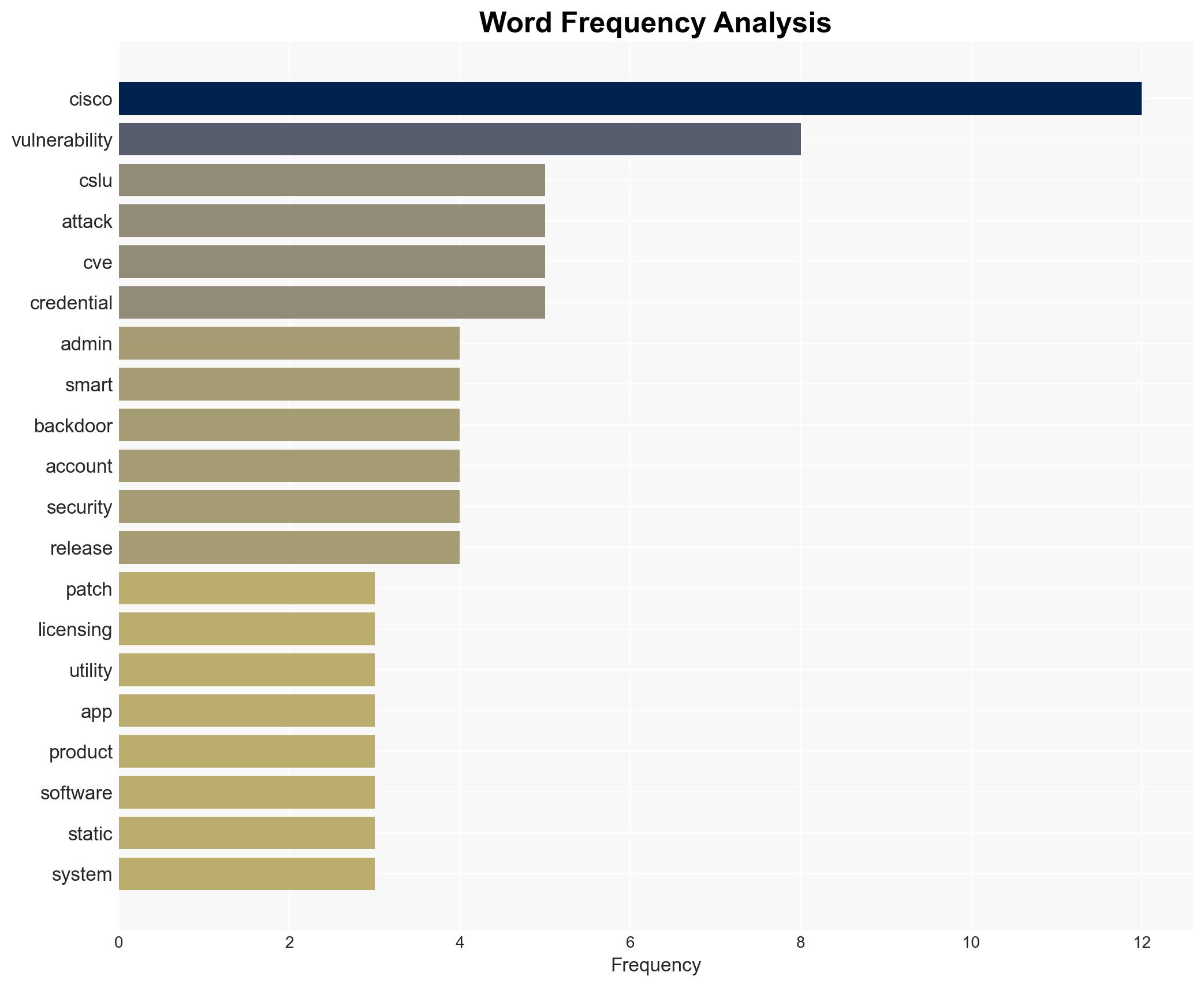
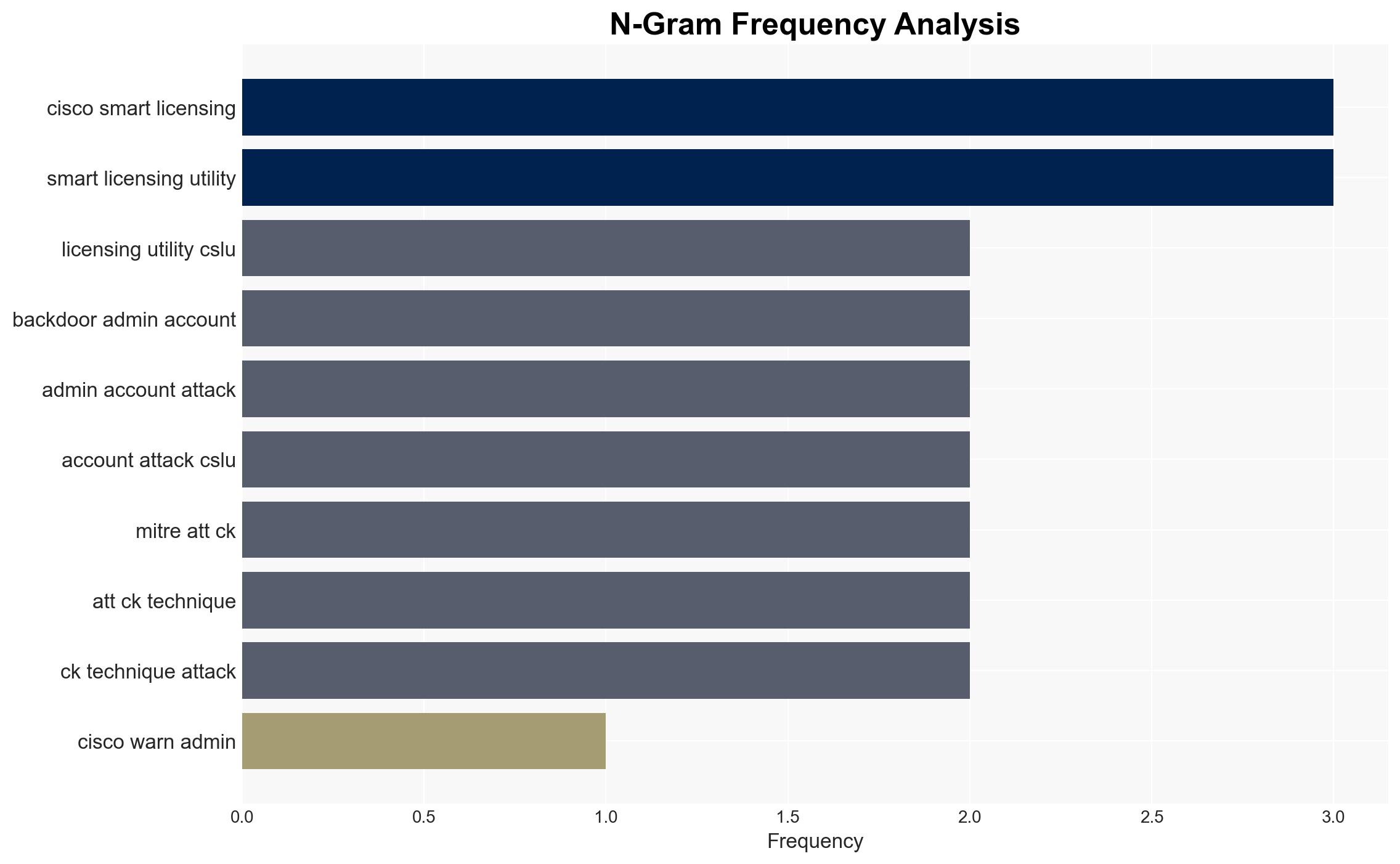
A critical vulnerability has been identified in the Cisco Smart Licensing Utility (CSLU), which exposes systems to unauthorized access through a backdoor administrative account. This vulnerability, tracked as CVE, allows attackers to gain remote admin privileges on unpatched systems. Cisco has released a security patch to address this flaw and strongly recommends immediate updates to mitigate the risk of exploitation. Failure to patch could lead to significant security breaches, affecting both organizational operations and data integrity.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
The vulnerability in the Cisco Smart Licensing Utility (CSLU) is due to undocumented static user credentials that create a backdoor for unauthorized access. This flaw allows unauthenticated attackers to log into systems with admin privileges. The vulnerability impacts systems running the vulnerable version of CSLU, particularly those connected to Cisco’s cloud-based Smart Software Manager. Reverse engineering by Nicholas Starke revealed the technical details and hardcoded password, prompting Cisco to release a security patch. Despite the patch, there is evidence of attempted exploitation in the wild, emphasizing the urgency for organizations to update their systems.
3. Implications and Strategic Risks
The exploitation of this vulnerability poses significant risks, including unauthorized access to sensitive data and potential disruptions to critical infrastructure. The presence of a backdoor admin account could lead to data breaches, loss of intellectual property, and compromised operational capabilities. For national security, the risk extends to potential espionage and sabotage activities. Economically, affected organizations may face financial losses due to operational downtime and reputational damage.
4. Recommendations and Outlook
Recommendations:
- Organizations should immediately apply the Cisco security patch to all affected systems to close the backdoor vulnerability.
- Conduct a thorough audit of network security protocols and implement enhanced monitoring for suspicious activities.
- Consider regulatory measures to enforce timely patch management and vulnerability disclosures across critical sectors.
Outlook:
In the best-case scenario, rapid patch deployment will mitigate the immediate threat, preventing widespread exploitation. In the worst-case scenario, failure to patch could lead to significant breaches, with cascading effects on national security and economic stability. The most likely outcome is a mixed response, with some organizations successfully mitigating the risk while others remain vulnerable due to delayed action.
5. Key Individuals and Entities
The report mentions significant individuals and organizations, including Nicholas Starke and Johanne Ullrich. These individuals have contributed to the identification and analysis of the vulnerability, highlighting the collaborative efforts required to address cybersecurity threats effectively.