CoffeeLoader uses a GPU-based packer to evade detection – Securityaffairs.com
Published on: 2025-03-31
Intelligence Report: CoffeeLoader uses a GPU-based packer to evade detection – Securityaffairs.com
1. BLUF (Bottom Line Up Front)
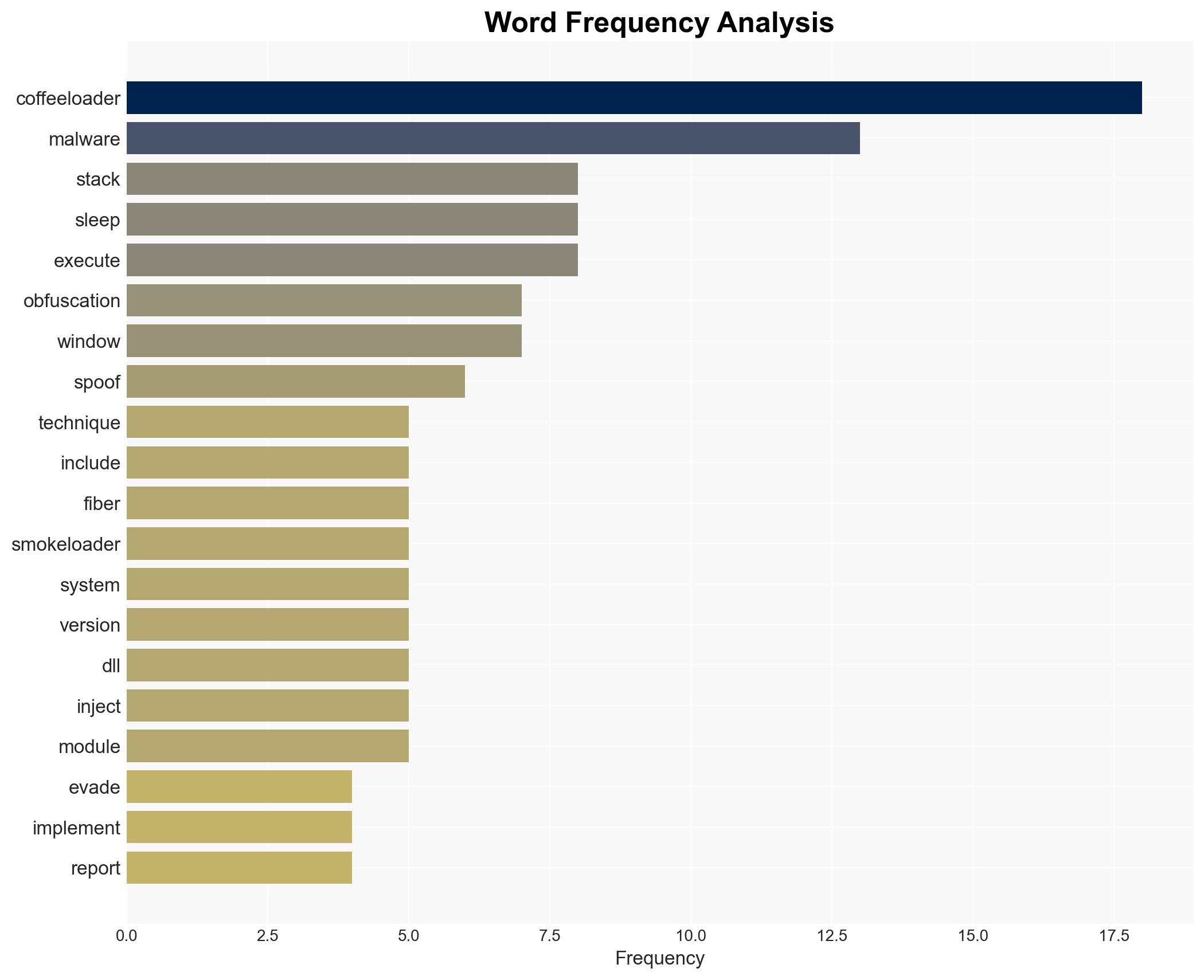
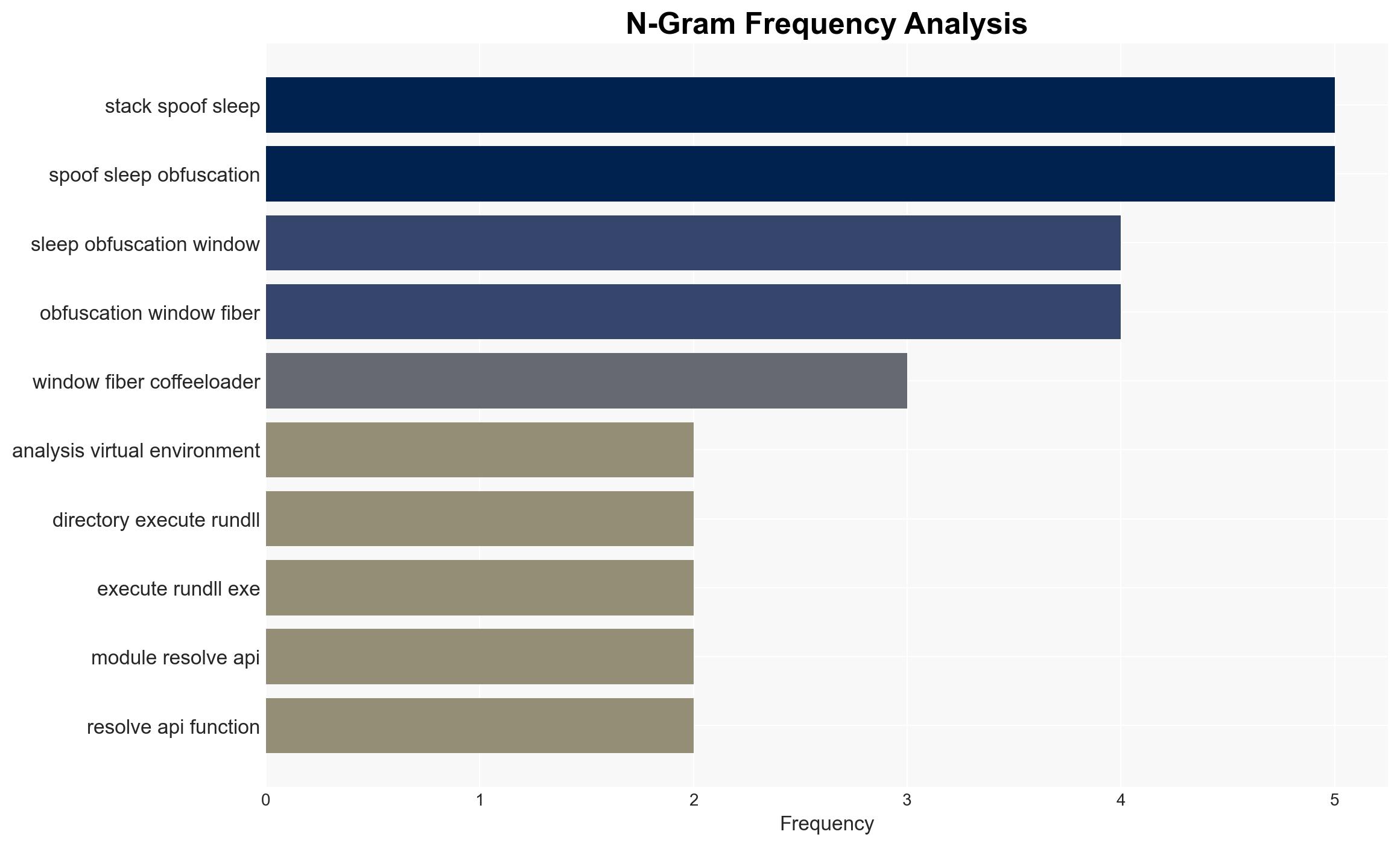
The CoffeeLoader malware family, identified by Zscaler ThreatLabZ, employs advanced evasion techniques, including a GPU-based packer named Armoury, to bypass endpoint security measures. This malware is capable of downloading secondary payloads and shares behavioral similarities with SmokeLoader. The use of a domain generation algorithm (DGA) for command and control, along with sophisticated obfuscation methods, poses significant challenges for detection and analysis. Immediate attention is required to develop countermeasures and enhance security protocols.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
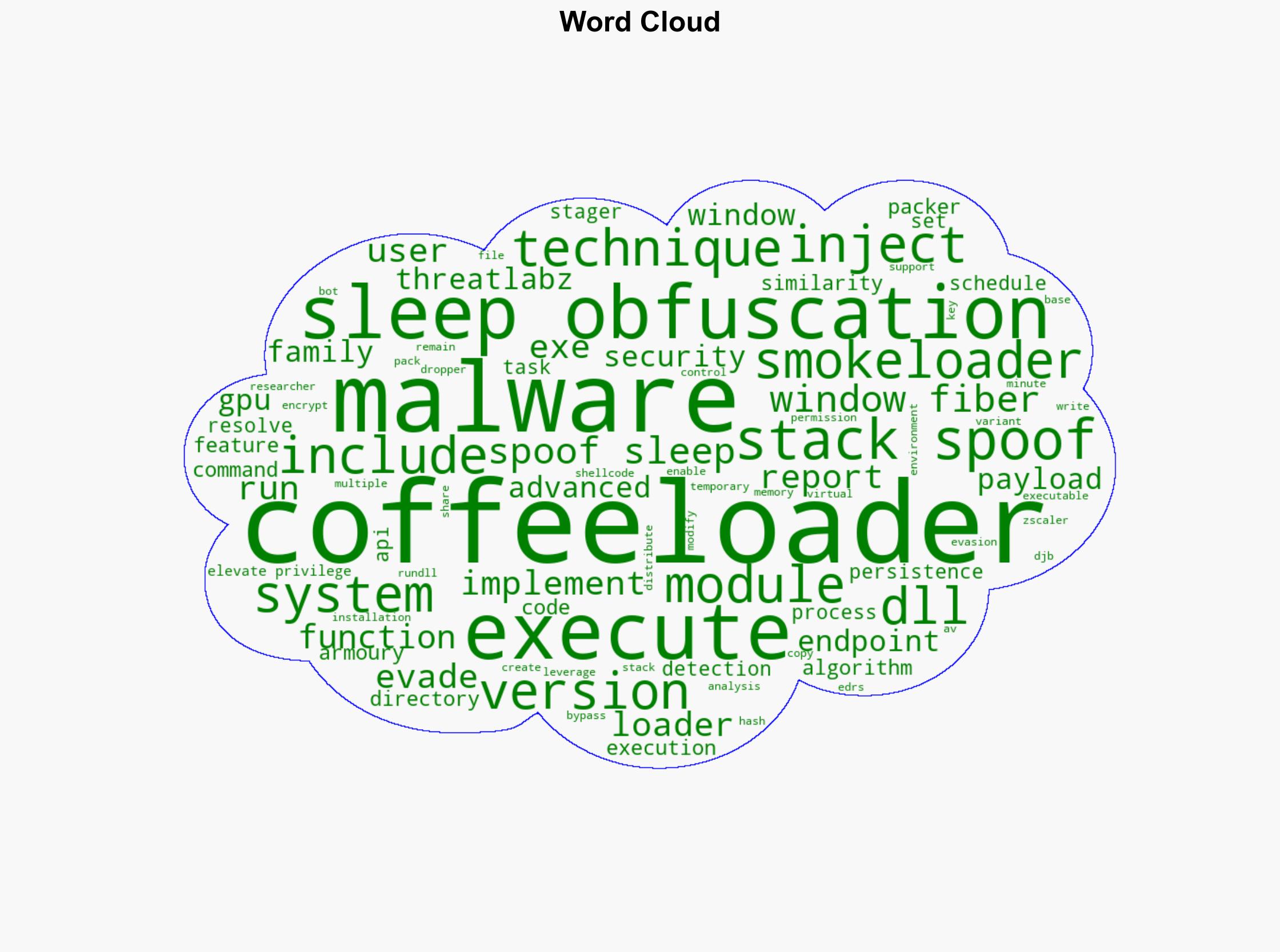
CoffeeLoader has been active since September and utilizes multiple techniques to evade detection, including stack spoofing, sleep obfuscation, and Windows fiber manipulation. The malware’s ability to execute code via the system’s GPU complicates analysis in virtual environments. CoffeeLoader’s distribution method, similar to SmokeLoader, and its use of a unique malware packer, suggest a potential connection between these malware families. The malware’s persistence mechanisms, such as DLL copying and task scheduling, further enhance its resilience against traditional security measures.
3. Implications and Strategic Risks
The advanced evasion techniques employed by CoffeeLoader present significant risks to national security and economic interests. The malware’s ability to bypass endpoint detection and response (EDR) systems could lead to unauthorized data access and potential breaches in critical infrastructure. The use of GPU-based execution and DGA for command and control indicates a trend towards more sophisticated and resilient malware threats, necessitating enhanced cybersecurity measures across sectors.
4. Recommendations and Outlook
Recommendations:
- Develop and deploy advanced detection algorithms capable of identifying GPU-based malware execution.
- Enhance endpoint security solutions to detect and mitigate stack spoofing and sleep obfuscation techniques.
- Implement stricter access controls and monitoring for systems vulnerable to DLL injection and task scheduling exploits.
Outlook:
In the best-case scenario, rapid adaptation of security measures and collaboration among cybersecurity entities could mitigate the threat posed by CoffeeLoader. In the worst-case scenario, failure to address these advanced evasion techniques could result in widespread data breaches and significant economic impact. The most likely outcome involves a continued arms race between malware developers and cybersecurity professionals, with incremental improvements in detection and response capabilities.
5. Key Individuals and Entities
The report mentions Zscaler ThreatLabZ as the entity responsible for identifying the CoffeeLoader malware family. No specific individuals are referenced in the analysis.