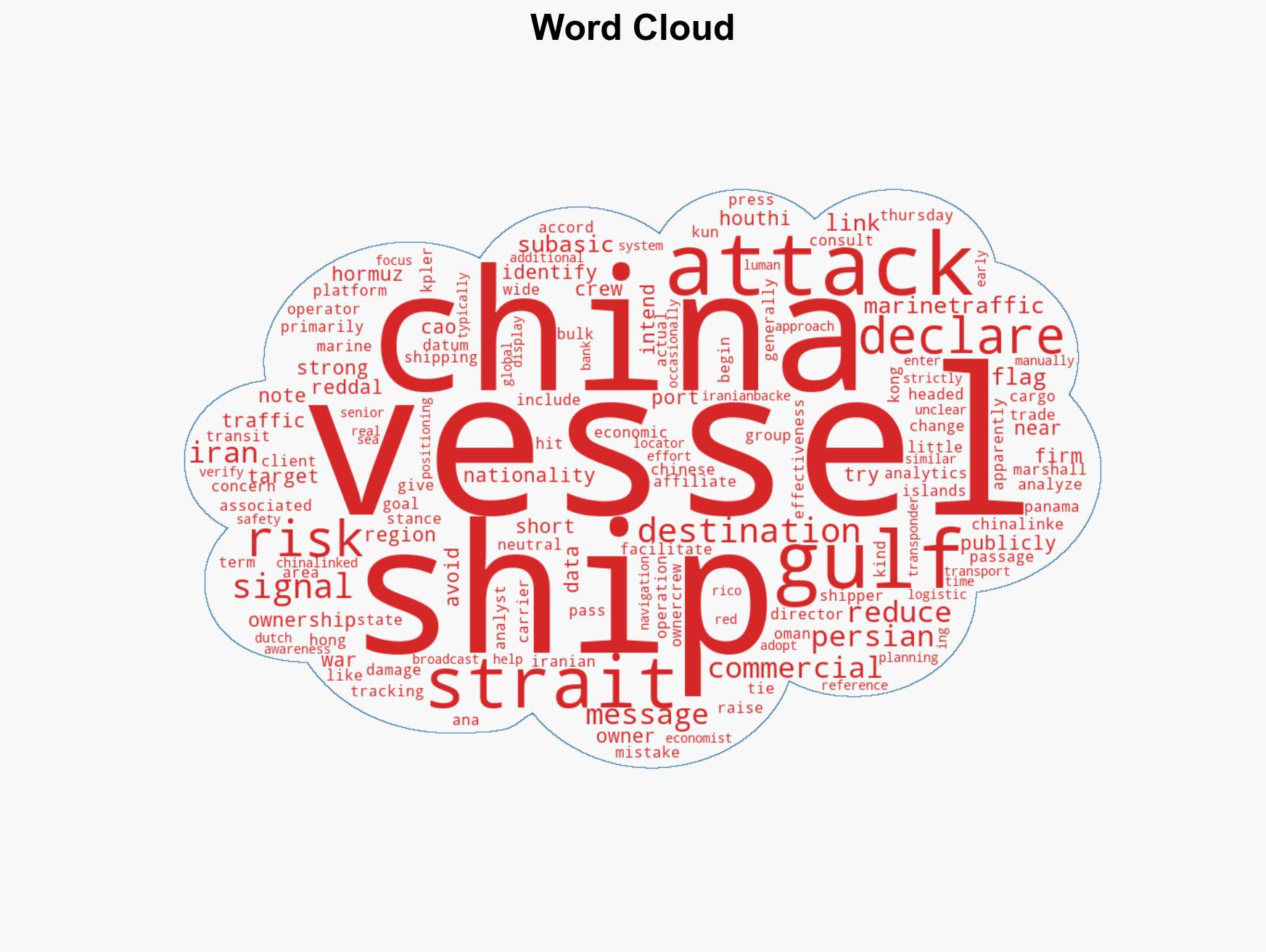
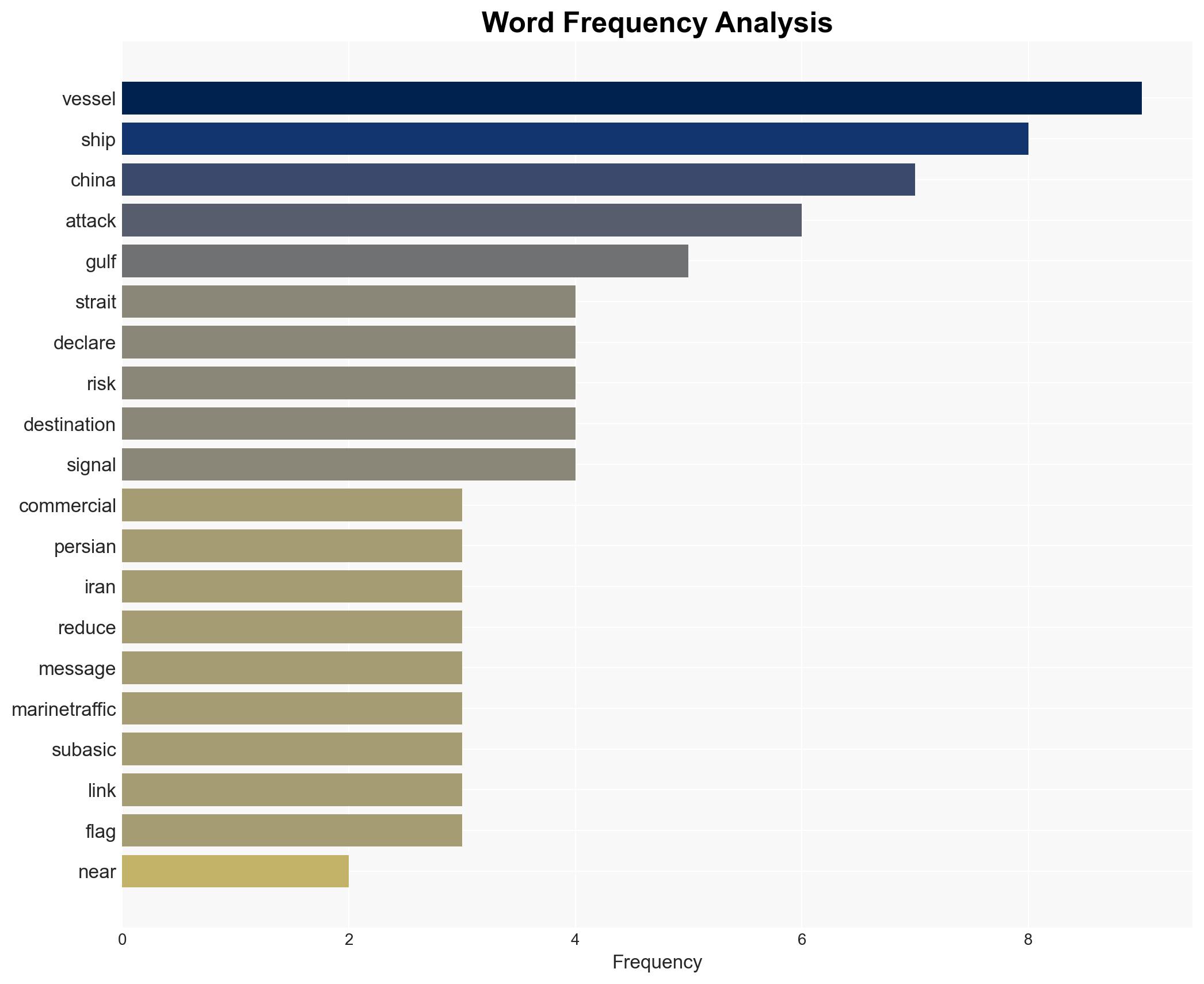
Commercial vessels in Strait of Hormuz rebrand as Chinese to mitigate attack risks amid Iran conflict
Published on: 2026-03-12
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Ships identify themselves as Chinese around Strait of Hormuz during Iran war to avoid attacks
1. BLUF (Bottom Line Up Front)
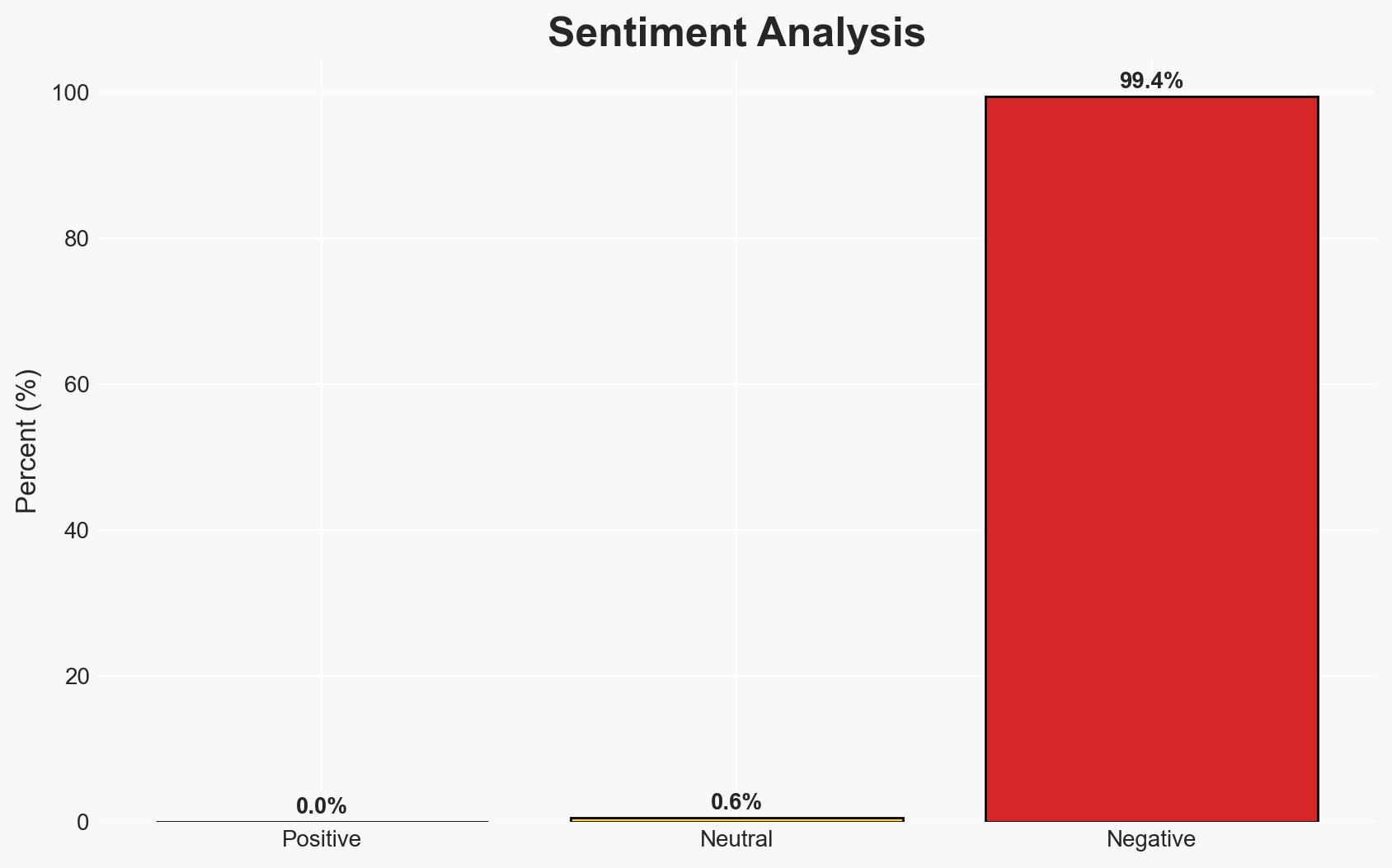
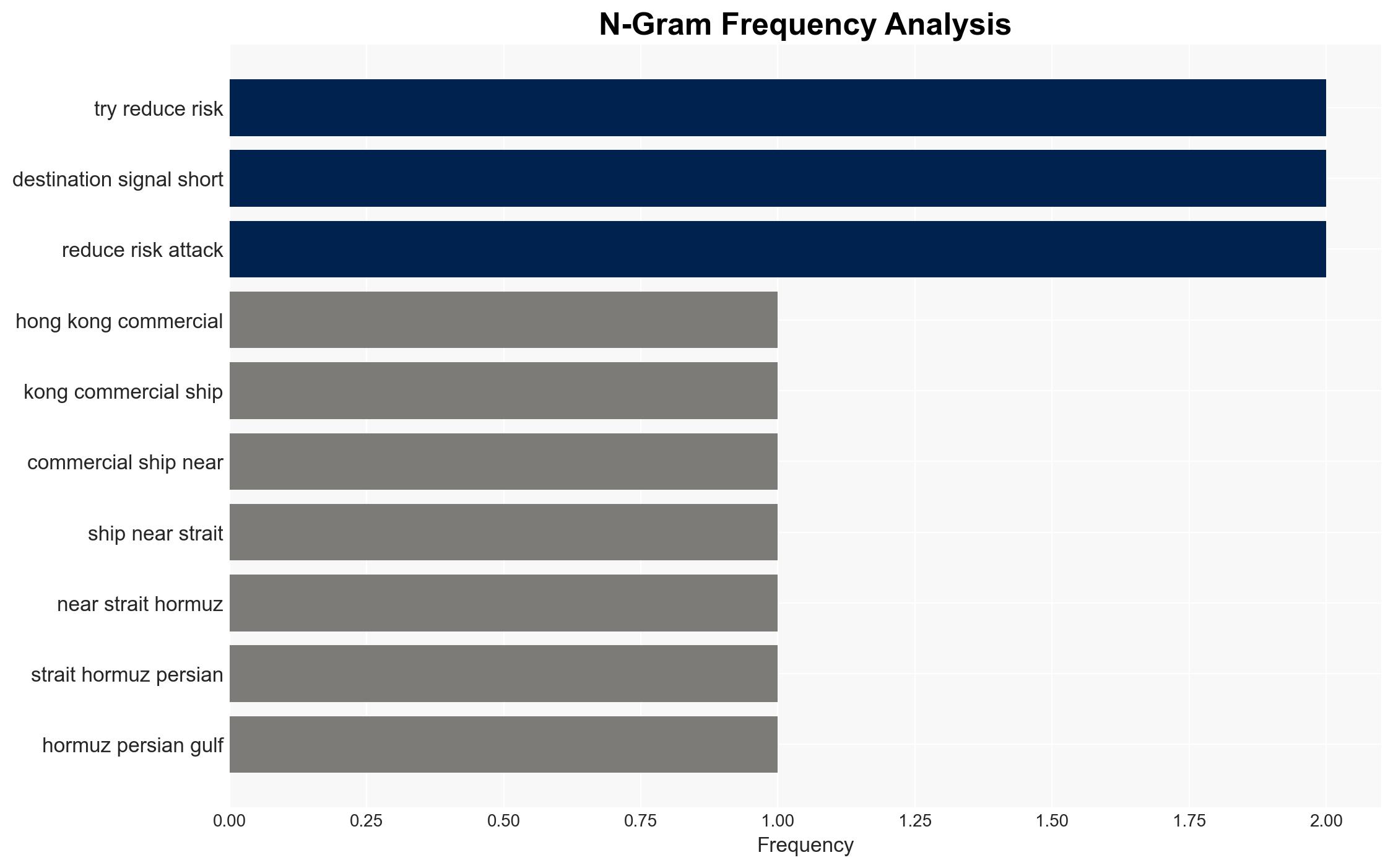
Commercial vessels in the Strait of Hormuz are declaring themselves as China-linked to avoid attacks amid ongoing conflict involving Iran. This tactic leverages China’s neutral stance and economic ties with Iran. The effectiveness of this strategy remains uncertain, but it reflects heightened security concerns in the region. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: Vessels are declaring themselves as China-linked to leverage China’s neutral stance and avoid attacks. Supporting evidence includes historical avoidance of Chinese-linked ships by Iranian forces and the use of similar tactics in past conflicts. Key uncertainties include the actual effectiveness of this strategy in preventing attacks.
- Hypothesis B: The declarations are primarily for operational or logistical reasons unrelated to security, such as facilitating navigation or port access. Contradicting evidence includes the specific context of ongoing conflict and the historical precedent of using such declarations for security purposes.
- Assessment: Hypothesis A is currently better supported due to the specific security context and historical precedent. Indicators that could shift this judgment include evidence of attacks on vessels despite their declarations or changes in Iranian targeting behavior.
3. Key Assumptions and Red Flags
- Assumptions: Iran continues to avoid targeting Chinese-linked vessels; China maintains a neutral stance in the conflict; vessel operators have accurate intelligence on threat levels.
- Information Gaps: Detailed data on Iranian targeting criteria; confirmation of the effectiveness of the declarations in avoiding attacks.
- Bias & Deception Risks: Potential bias in interpreting vessel declarations as purely security-driven; risk of deception by vessel operators to manipulate threat perceptions.
4. Implications and Strategic Risks
This development could lead to increased complexity in maritime operations and influence regional security dynamics. The tactic may prompt changes in Iranian targeting strategies or diplomatic responses from China.
- Political / Geopolitical: Potential diplomatic tensions if China is perceived as indirectly involved; shifts in regional alliances or maritime policies.
- Security / Counter-Terrorism: Increased risk of misidentification or escalation; changes in threat assessment protocols for maritime operations.
- Cyber / Information Space: Potential for misinformation or cyber operations targeting vessel tracking systems.
- Economic / Social: Disruptions to shipping routes could impact global trade; increased insurance costs for vessels operating in the region.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of vessel declarations and Iranian responses; engage in diplomatic channels to clarify China’s position.
- Medium-Term Posture (1–12 months): Develop resilience measures for shipping operations; strengthen partnerships with regional allies to ensure maritime security.
- Scenario Outlook:
- Best: De-escalation of conflict reduces need for deceptive declarations.
- Worst: Increased attacks despite declarations, leading to broader conflict.
- Most-Likely: Continued use of declarations with mixed effectiveness, prompting strategic adjustments by involved parties.
6. Key Individuals and Entities
- Ana Subasic, trade risk analyst at Kpler
- Kun Cao, client director at Reddal
- Rico Luman, senior economist at ING
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
Counter-Terrorism, maritime security, Iran conflict, geopolitical strategy, shipping logistics, economic impact, information operations, regional stability
Structured Analytic Techniques Applied
- ACH 2.0: Reconstruct likely threat actor intentions via hypothesis testing and structured refutation.
- Indicators Development: Track radicalization signals and propaganda patterns to anticipate operational planning.
- Narrative Pattern Analysis: Analyze spread/adaptation of ideological narratives for recruitment/incitement signals.
Explore more:
Counter-Terrorism Briefs ·
Daily Summary ·
Support us