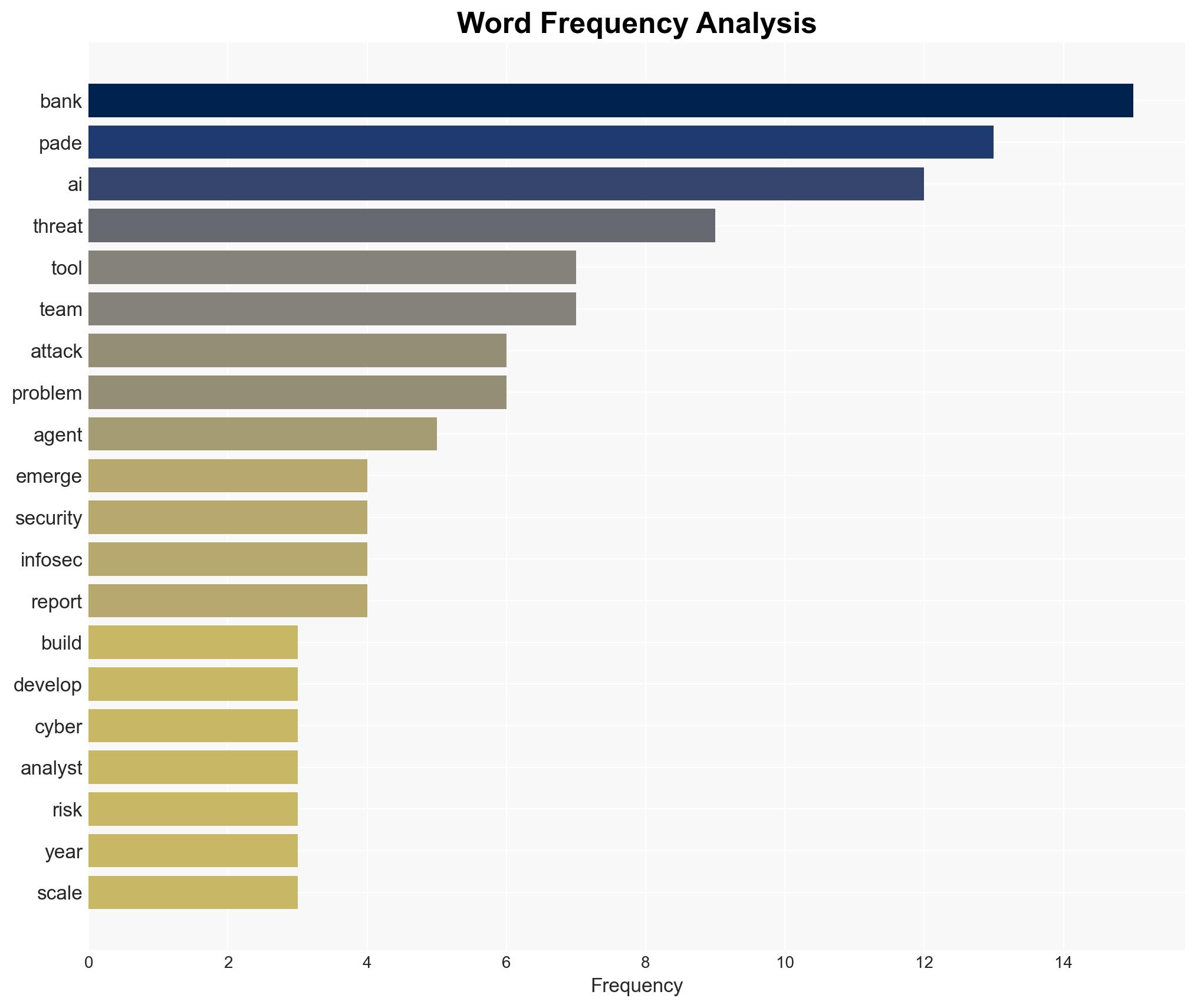
Commonwealth Bank develops in-house AI threat detection tools to address rapid evolution of cyber threats
Published on: 2026-03-17
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
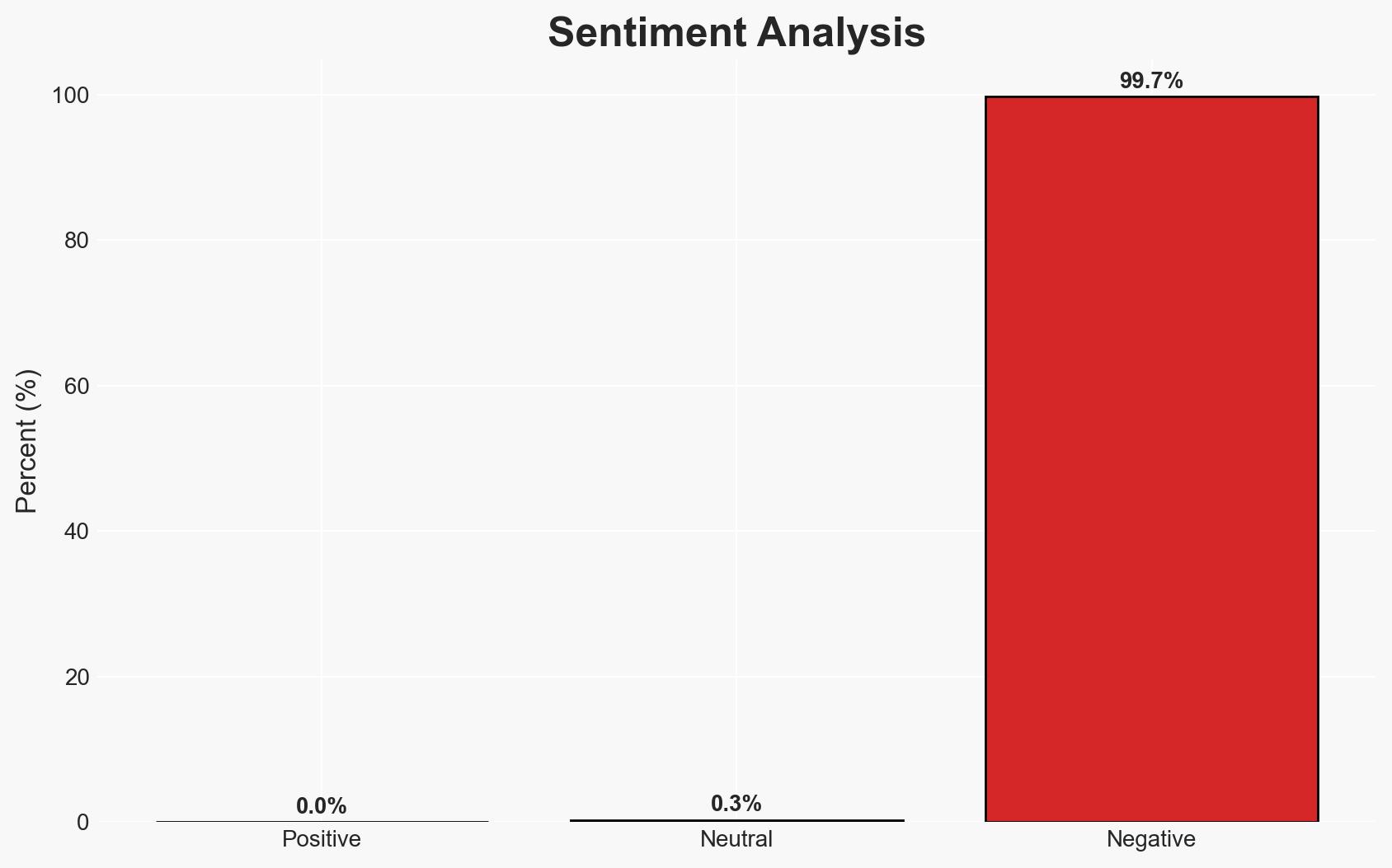
Intelligence Report: Bank built its own threat hunting agent because vendors cant keep pace with new threats
1. BLUF (Bottom Line Up Front)
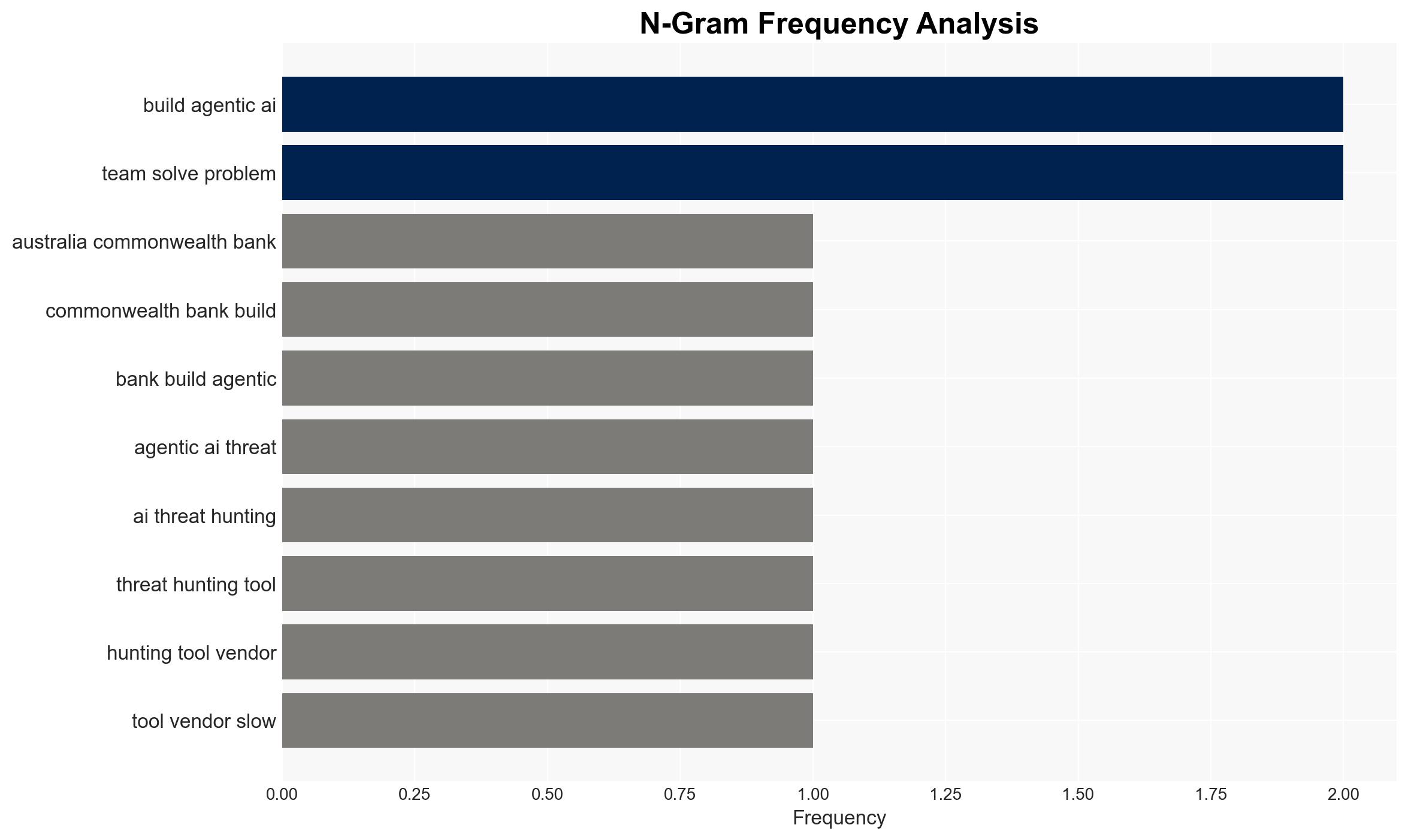
The Commonwealth Bank of Australia has developed its own AI threat hunting tools due to the inability of vendors to keep up with rapidly evolving AI-powered threats. This decision highlights a significant shift in cybersecurity strategy, emphasizing the need for internal capabilities to manage escalating threat volumes. This development affects financial institutions and cybersecurity sectors, with moderate confidence in the assessment.
2. Competing Hypotheses
- Hypothesis A: The Commonwealth Bank’s internal development of AI threat hunting tools is primarily driven by the inadequacy of existing vendor solutions to address the scale and sophistication of AI-driven cyber threats. Supporting evidence includes the exponential increase in threat signals and the bank’s need for rapid threat assessment capabilities. However, uncertainties remain regarding the long-term sustainability and scalability of this internal approach.
- Hypothesis B: The bank’s decision is motivated by a strategic desire to gain competitive advantage and control over its cybersecurity processes, rather than solely by vendor inadequacies. This hypothesis is supported by the bank’s emphasis on elevating analyst roles and reducing burnout, but lacks direct evidence linking these motivations to competitive strategy.
- Assessment: Hypothesis A is currently better supported due to the explicit statements by the bank’s General Manager of Cyber Defence Operations about vendor limitations and the immediate operational needs. Indicators that could shift this judgment include evidence of similar strategic moves by other financial institutions or changes in vendor capabilities.
3. Key Assumptions and Red Flags
- Assumptions: The bank’s internal AI tools are more effective than vendor solutions; AI-driven threats will continue to grow in complexity; internal development is cost-effective in the long term.
- Information Gaps: Detailed performance metrics of the bank’s AI tools compared to vendor solutions; cost analysis of internal development versus vendor procurement; potential impacts on vendor relationships.
- Bias & Deception Risks: Potential bias in the bank’s public statements to justify internal investments; lack of independent verification of the tool’s effectiveness; possible underestimation of vendor capabilities.
4. Implications and Strategic Risks
This development could lead to increased self-reliance among financial institutions for cybersecurity, potentially reshaping vendor relationships and market dynamics. The reliance on AI tools may also introduce new vulnerabilities if not properly managed.
- Political / Geopolitical: Limited direct implications, but potential for influencing national cybersecurity policies.
- Security / Counter-Terrorism: Enhanced threat detection capabilities could improve overall security posture but may also escalate the arms race in cyber capabilities.
- Cyber / Information Space: Increased focus on AI-driven solutions may spur innovation but also raise concerns about AI reliability and security.
- Economic / Social: Potential job market shifts in cybersecurity, with increased demand for AI expertise and possible impacts on mental health due to high-pressure environments.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor the performance and impact of the bank’s AI tools; engage with vendors to assess their response strategies; evaluate internal cybersecurity capabilities.
- Medium-Term Posture (1–12 months): Develop partnerships with AI research institutions; invest in workforce training to manage AI tools; explore collaborative frameworks with other financial institutions.
- Scenario Outlook: Best: Enhanced security and competitive edge; Worst: Increased vulnerabilities and operational failures; Most-Likely: Gradual improvement in threat management with ongoing challenges in AI tool optimization.
6. Key Individuals and Entities
- Andrew Pade, General Manager of Cyber Defence Operations, Commonwealth Bank of Australia
- Commonwealth Bank of Australia
- Gartner (as event host)
7. Thematic Tags
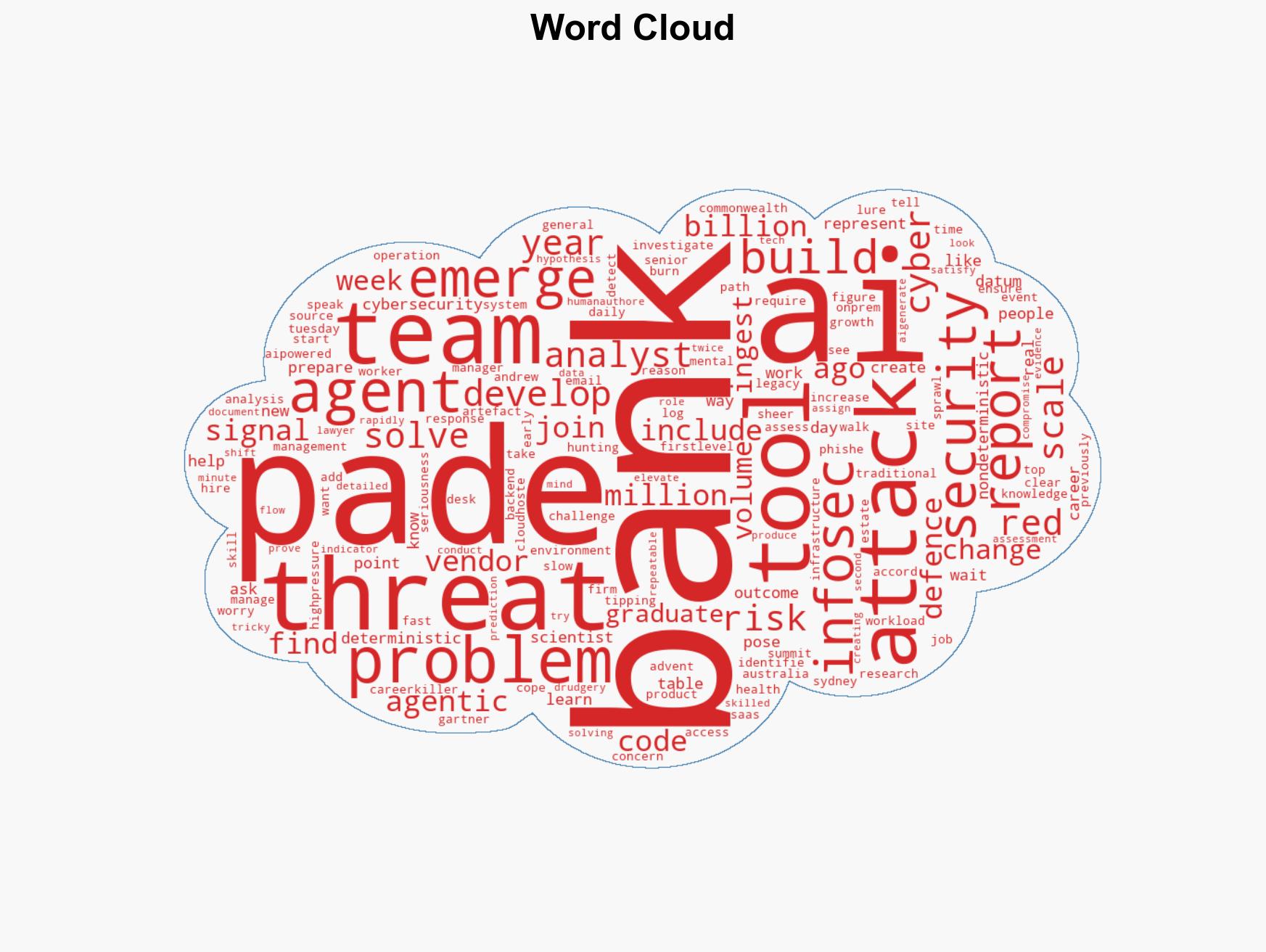
cybersecurity, AI threat detection, financial sector, vendor solutions, internal development
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- ACH 2.0: Machine-assisted hypothesis testing for intent reconstruction.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us