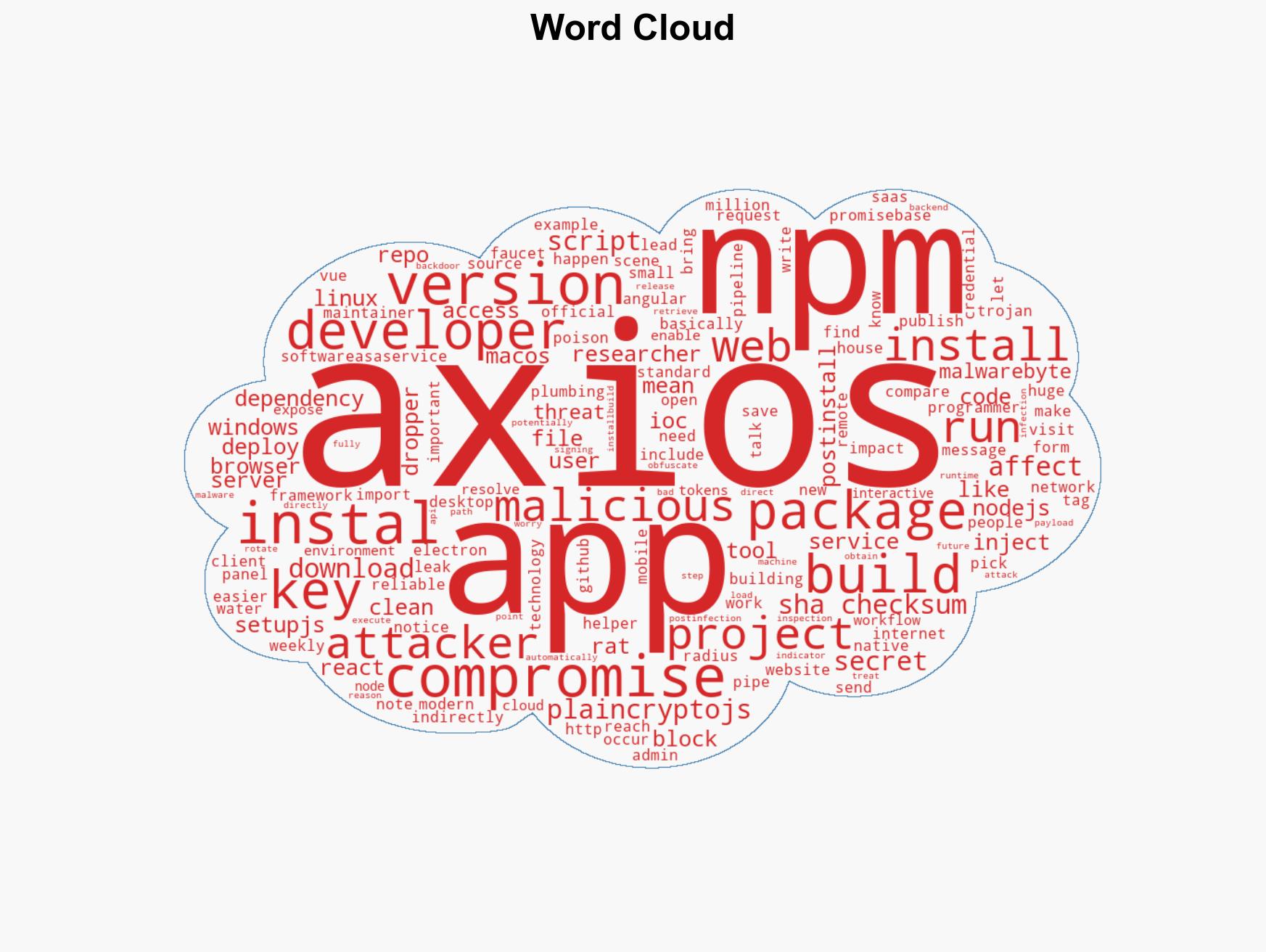
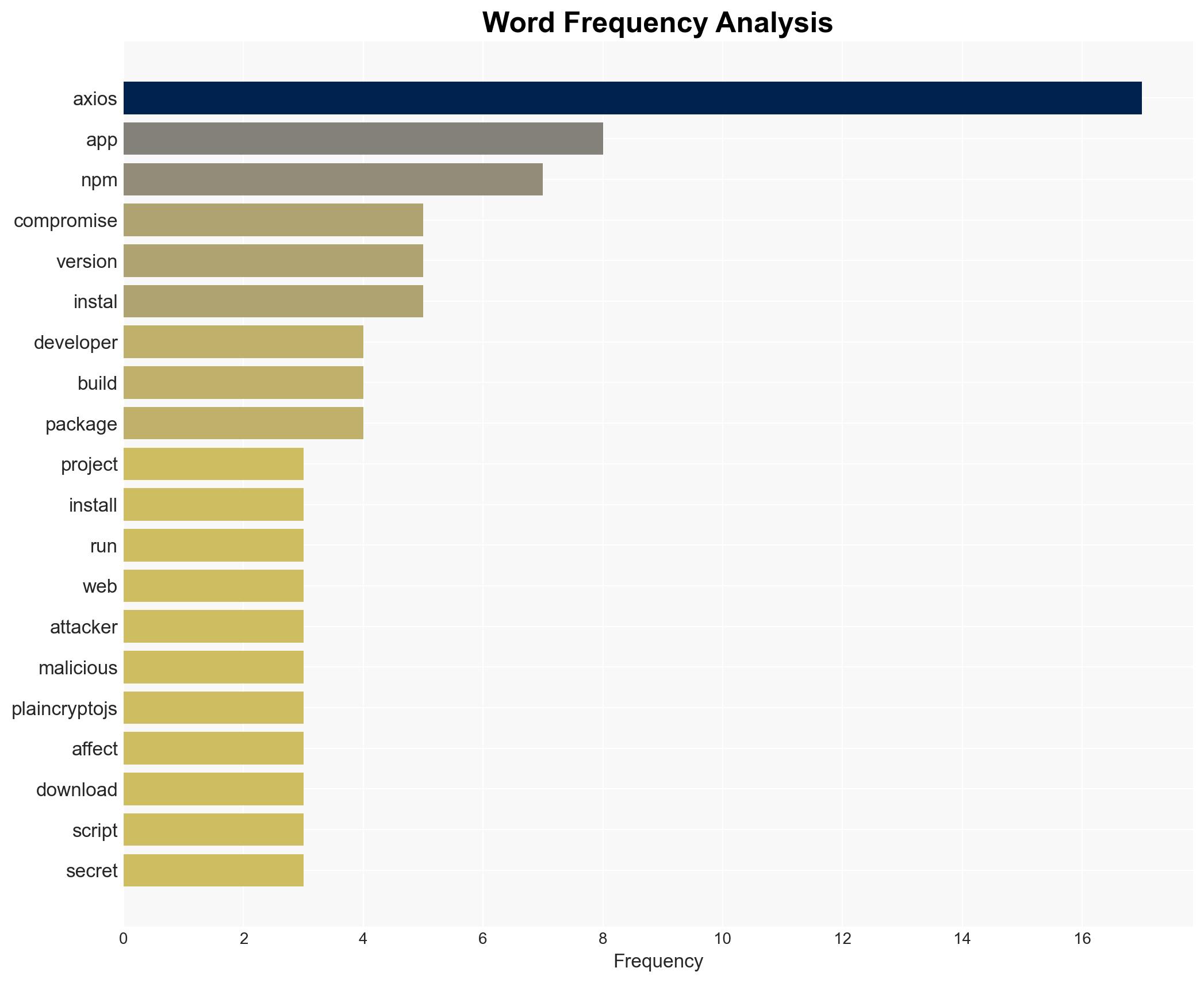
Compromised Axios Versions Introduce Remote Access Trojan, Eroding Trust in npm Ecosystem
Published on: 2026-03-31
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Axios supply chain attack chops away at npm trust
1. BLUF (Bottom Line Up Front)
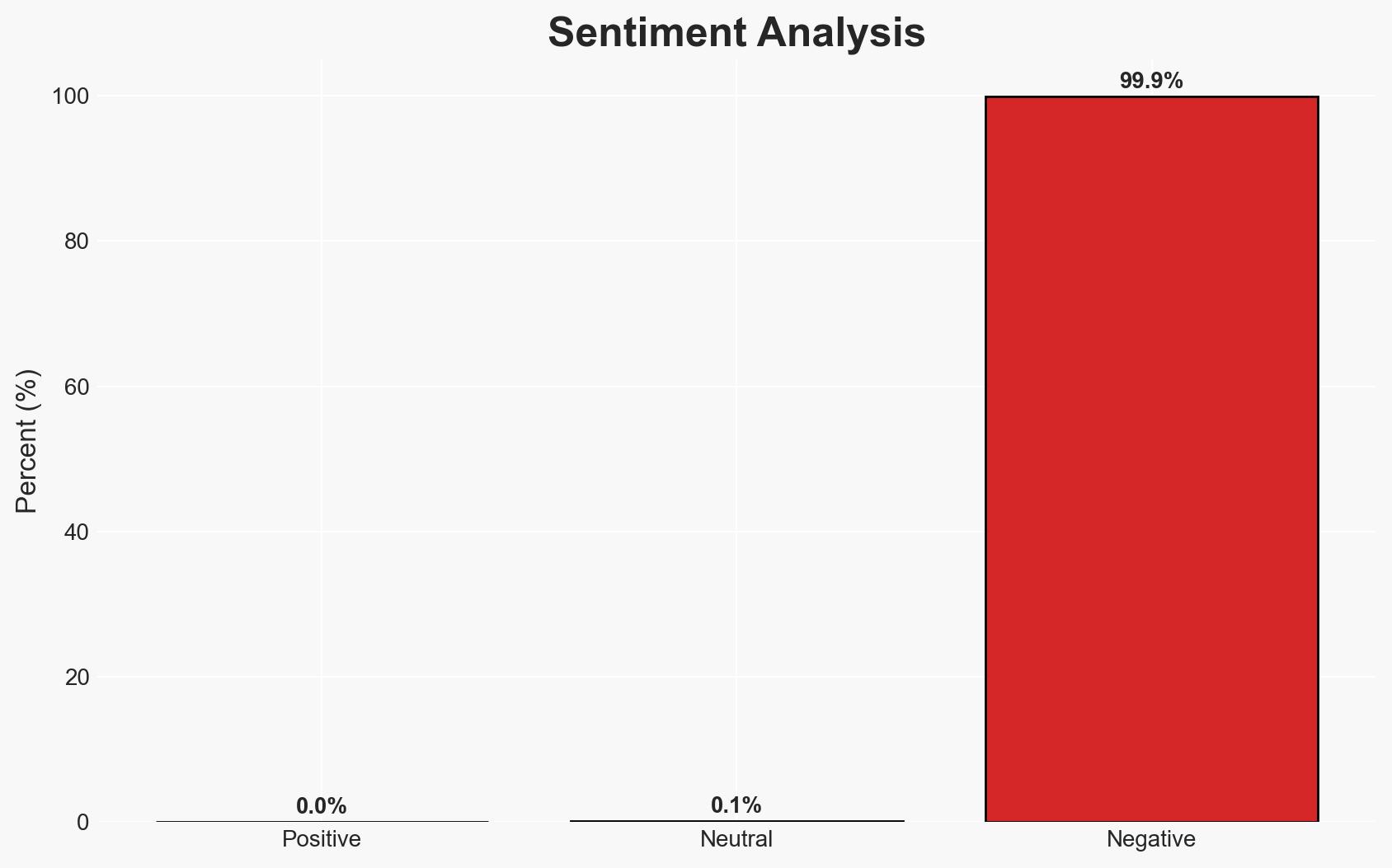
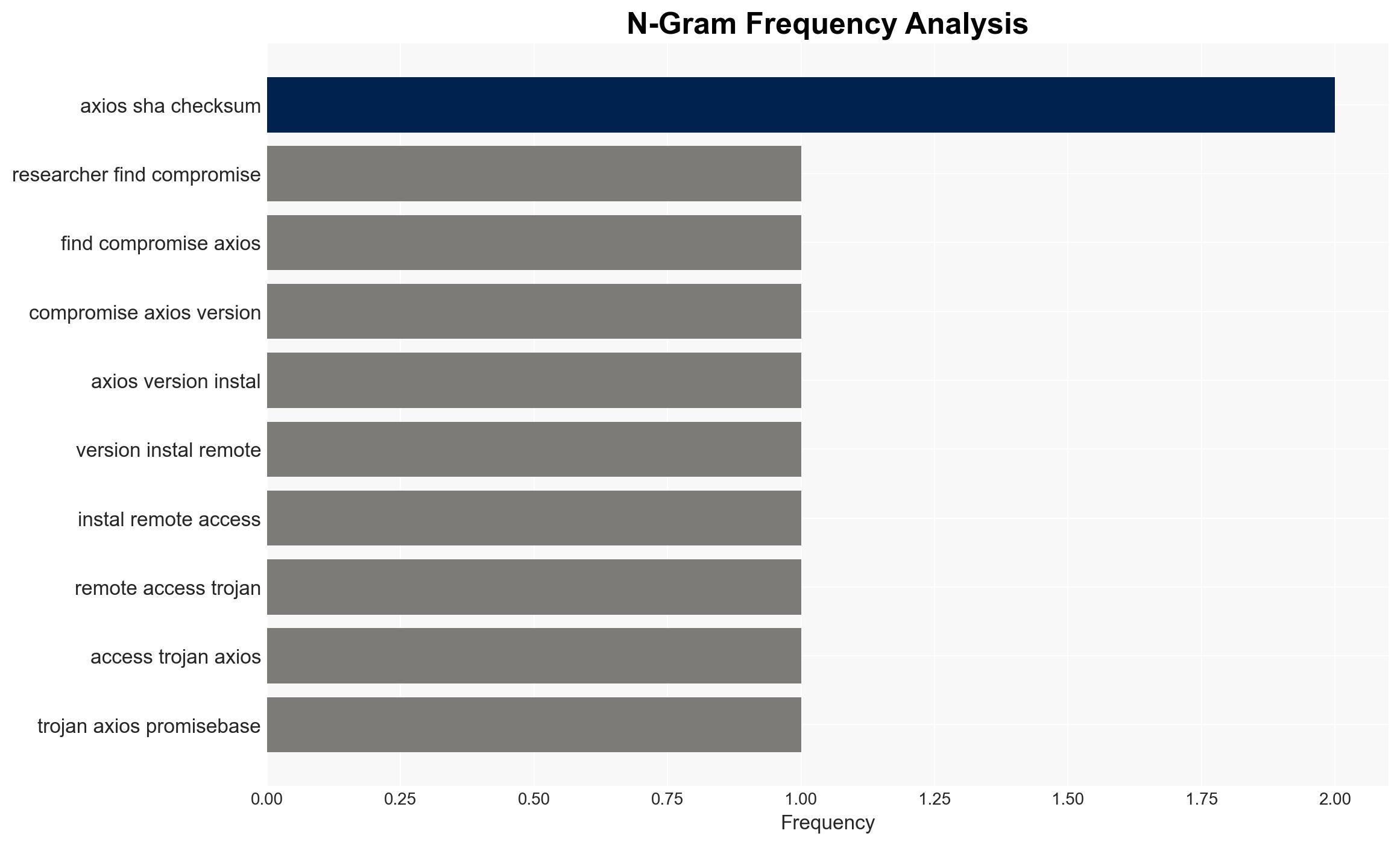
The Axios supply chain attack has compromised npm packages, potentially exposing sensitive developer secrets and affecting a vast number of JavaScript-based projects. The most supported hypothesis is that the attack was executed through compromised maintainer credentials, leading to the distribution of a Remote Access Trojan (RAT). This incident poses significant risks to software supply chains with moderate confidence in the assessment due to existing information gaps.
2. Competing Hypotheses
- Hypothesis A: The attack was conducted by exploiting compromised credentials of a lead maintainer, allowing the attacker to publish malicious versions of Axios on npm. This is supported by the fact that the affected versions do not appear in the official GitHub tags, indicating unauthorized access. However, the identity and motives of the attacker remain uncertain.
- Hypothesis B: The attack could have been an insider threat or a coordinated effort by a group with access to npm infrastructure. This hypothesis is less supported due to the lack of evidence suggesting insider involvement or broader coordination beyond the compromised credentials.
- Assessment: Hypothesis A is currently better supported due to the direct evidence of credential compromise and unauthorized package publication. Key indicators that could shift this judgment include discovery of additional compromised accounts or evidence of insider involvement.
3. Key Assumptions and Red Flags
- Assumptions: The attacker used stolen credentials; npm’s security measures were bypassed; affected developers have not yet fully mitigated the risk.
- Information Gaps: Identity and motives of the attacker; full scope of affected developers and projects; extent of potential data exfiltration.
- Bias & Deception Risks: Potential bias in attributing the attack solely to credential compromise without considering other vectors; risk of deception in attacker’s methods to obscure true intent.
4. Implications and Strategic Risks
This development could lead to increased scrutiny on open-source software supply chains and prompt broader security reforms. The incident may also influence developer trust in npm and similar platforms.
- Political / Geopolitical: Potential for increased regulatory pressure on software supply chain security.
- Security / Counter-Terrorism: Heightened awareness of supply chain vulnerabilities may lead to improved security practices, but also increased targeting by malicious actors.
- Cyber / Information Space: The attack highlights vulnerabilities in widely-used development tools, potentially prompting similar attacks on other platforms.
- Economic / Social: Disruption to development processes and potential financial losses for affected companies; erosion of trust in open-source ecosystems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Developers should rotate secrets, audit systems for compromise, and update affected packages. npm should enhance credential security measures.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing; implement stronger authentication mechanisms for package maintainers.
- Scenario Outlook:
- Best: Rapid mitigation and improved security measures prevent further incidents.
- Worst: Additional attacks exploit similar vulnerabilities, leading to widespread disruptions.
- Most-Likely: Incremental improvements in security practices with sporadic similar incidents.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, supply chain security, npm, cyber-attack, open-source software, remote access trojan, developer security, credential compromise
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us