Conduent Data Breach Escalates to Over 25 Million Affected Individuals, Marking One of the Largest in US Hist…
Published on: 2026-02-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
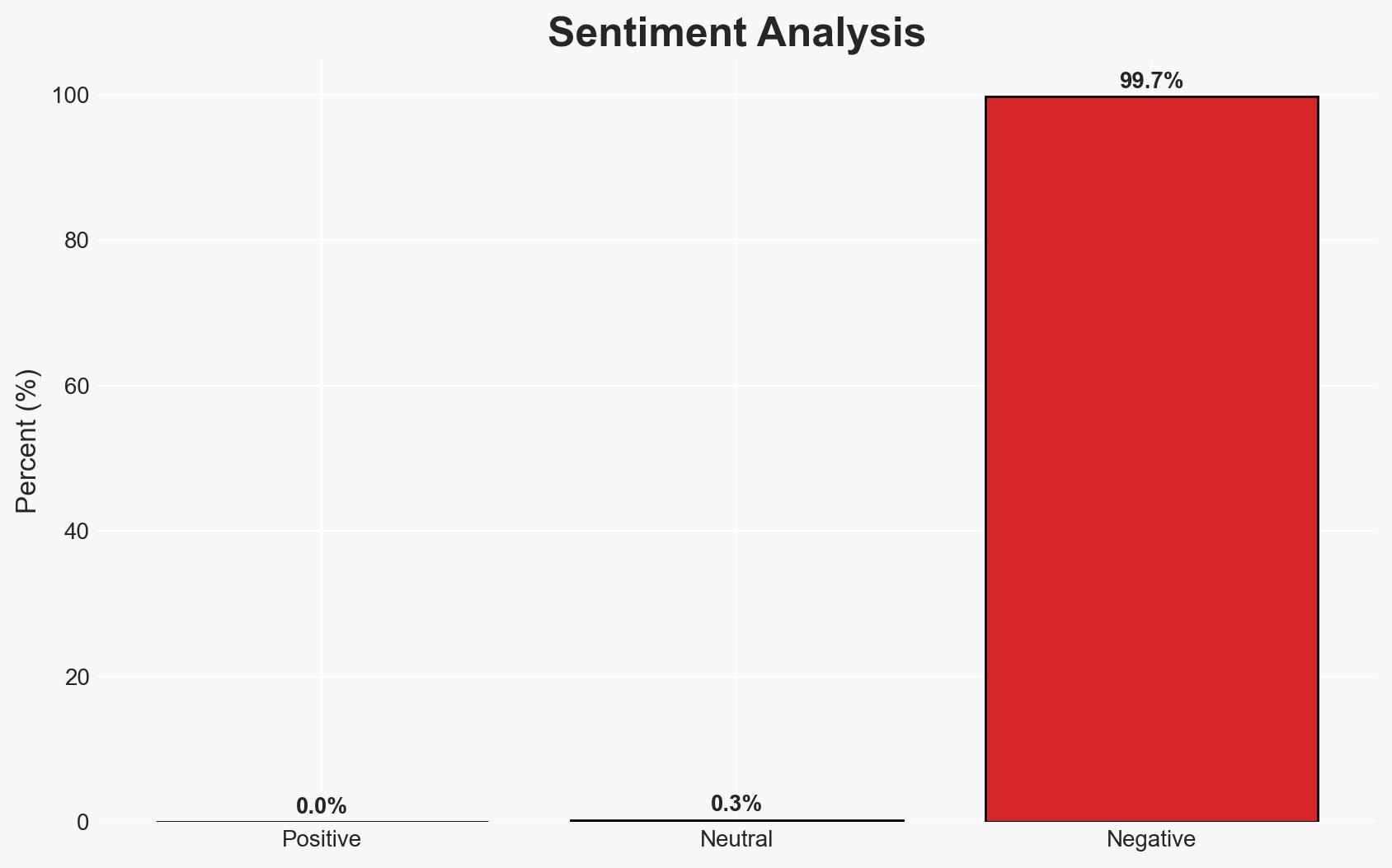
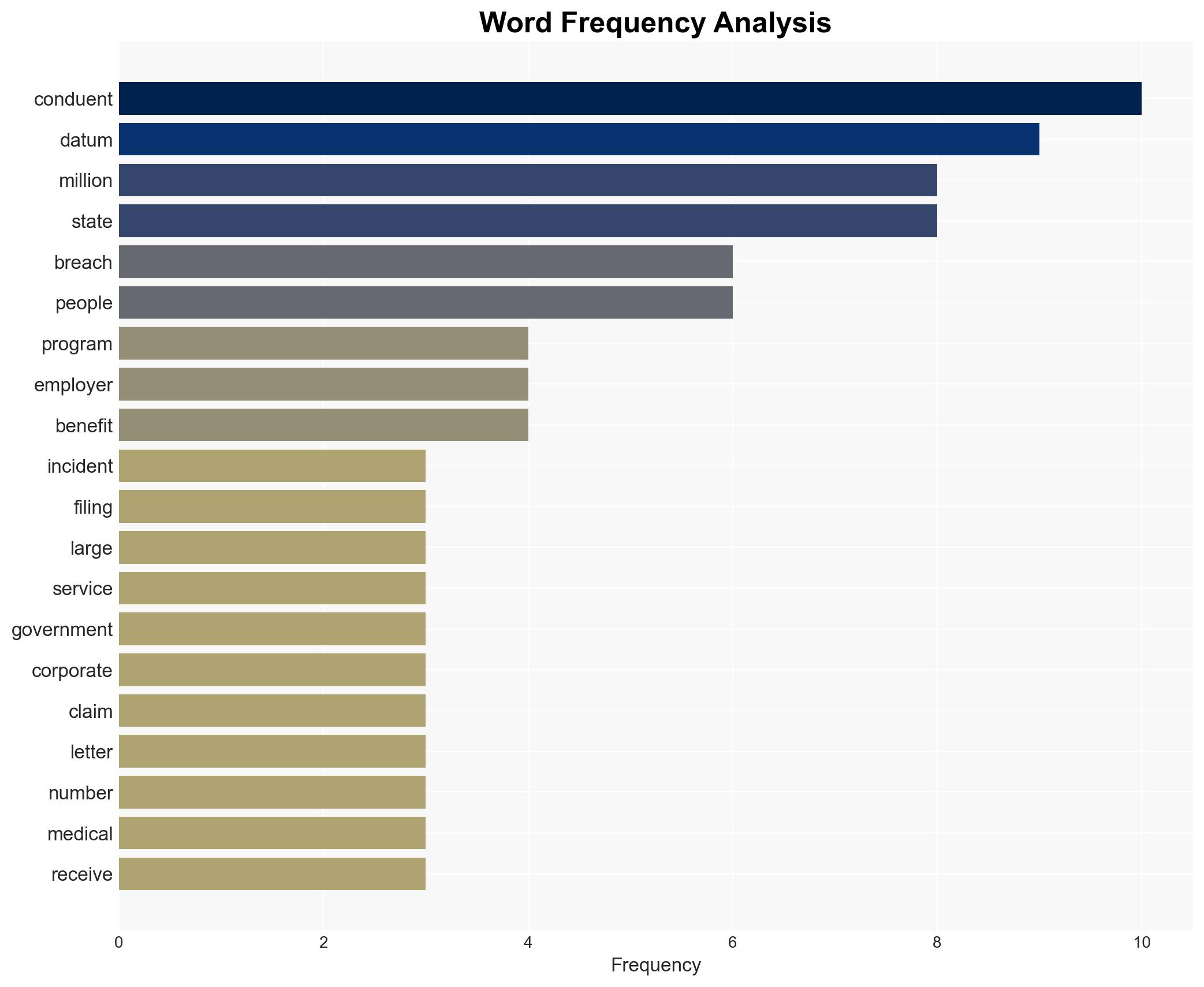
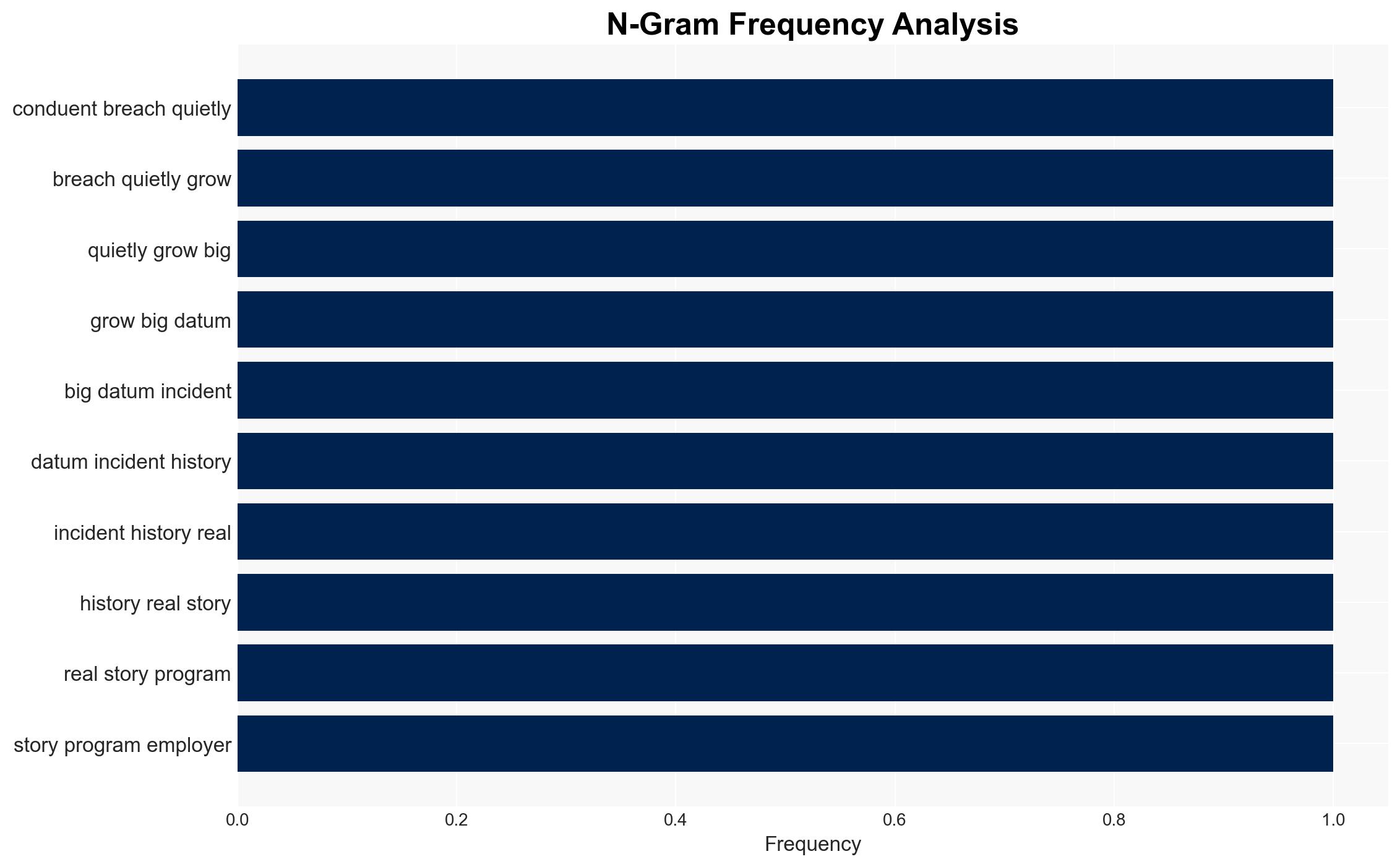
Intelligence Report: The Conduent breach from 10 million to 25 million and counting
1. BLUF (Bottom Line Up Front)
The Conduent data breach has expanded significantly, now affecting over 25 million individuals across the United States, with a substantial impact on state benefit programs and corporate services. The breach’s scale and the nature of the data involved pose significant risks to personal privacy and national security. The most likely hypothesis is that the breach resulted from a sophisticated cyberattack by the SafePay ransomware gang, exploiting Conduent’s extensive integration into public and private sector services. Overall confidence in this assessment is moderate, given the evolving nature of the incident and incomplete information.
2. Competing Hypotheses
- Hypothesis A: The breach was a targeted cyberattack by the SafePay ransomware gang, exploiting vulnerabilities in Conduent’s systems. This is supported by the claim of responsibility by the gang and the extended dwell time in Conduent’s environment. However, the exact method of intrusion and the full extent of data exfiltration remain uncertain.
- Hypothesis B: The breach resulted from an internal security failure or misconfiguration within Conduent, inadvertently exposing sensitive data. While plausible, there is currently no direct evidence supporting this, and the claim by SafePay suggests external malicious intent.
- Assessment: Hypothesis A is currently better supported due to the claim by SafePay and the nature of the data exfiltrated. Indicators that could shift this judgment include evidence of internal negligence or further technical details on the breach methodology.
3. Key Assumptions and Red Flags
- Assumptions: Conduent’s systems were adequately secured prior to the breach; SafePay’s claim of responsibility is genuine; the breach primarily affected data processed through Conduent’s services.
- Information Gaps: Detailed technical analysis of the breach vector; full scope of data exfiltrated; motivations and capabilities of the SafePay group.
- Bias & Deception Risks: Potential bias in attributing the breach solely to SafePay without corroborative evidence; risk of underestimating internal security failures.
4. Implications and Strategic Risks
The Conduent breach could have far-reaching implications for data security practices and public trust in third-party service providers. The incident underscores vulnerabilities in integrated service networks and could prompt regulatory scrutiny and policy changes.
- Political / Geopolitical: Increased pressure on government agencies to enhance cybersecurity measures and accountability for third-party vendors.
- Security / Counter-Terrorism: Potential exploitation of stolen data for identity theft or other malicious activities, increasing the threat landscape.
- Cyber / Information Space: Heightened awareness and potential for increased cyber defense initiatives among affected entities.
- Economic / Social: Potential economic impact on Conduent and its clients, alongside public concern over data privacy and security.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive forensic investigation; enhance monitoring of affected systems; notify affected individuals and entities.
- Medium-Term Posture (1–12 months): Implement robust cybersecurity measures; review and update data protection policies; foster partnerships for threat intelligence sharing.
- Scenario Outlook:
- Best: Rapid containment and mitigation, leading to minimal long-term impact.
- Worst: Further data leaks and exploitation, resulting in significant financial and reputational damage.
- Most-Likely: Gradual resolution with increased regulatory oversight and improved cybersecurity practices.
6. Key Individuals and Entities
- Conduent
- SafePay ransomware gang
- State benefit programs (e.g., Medicaid, SNAP)
- Blue Cross Blue Shield
- Volvo Group
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
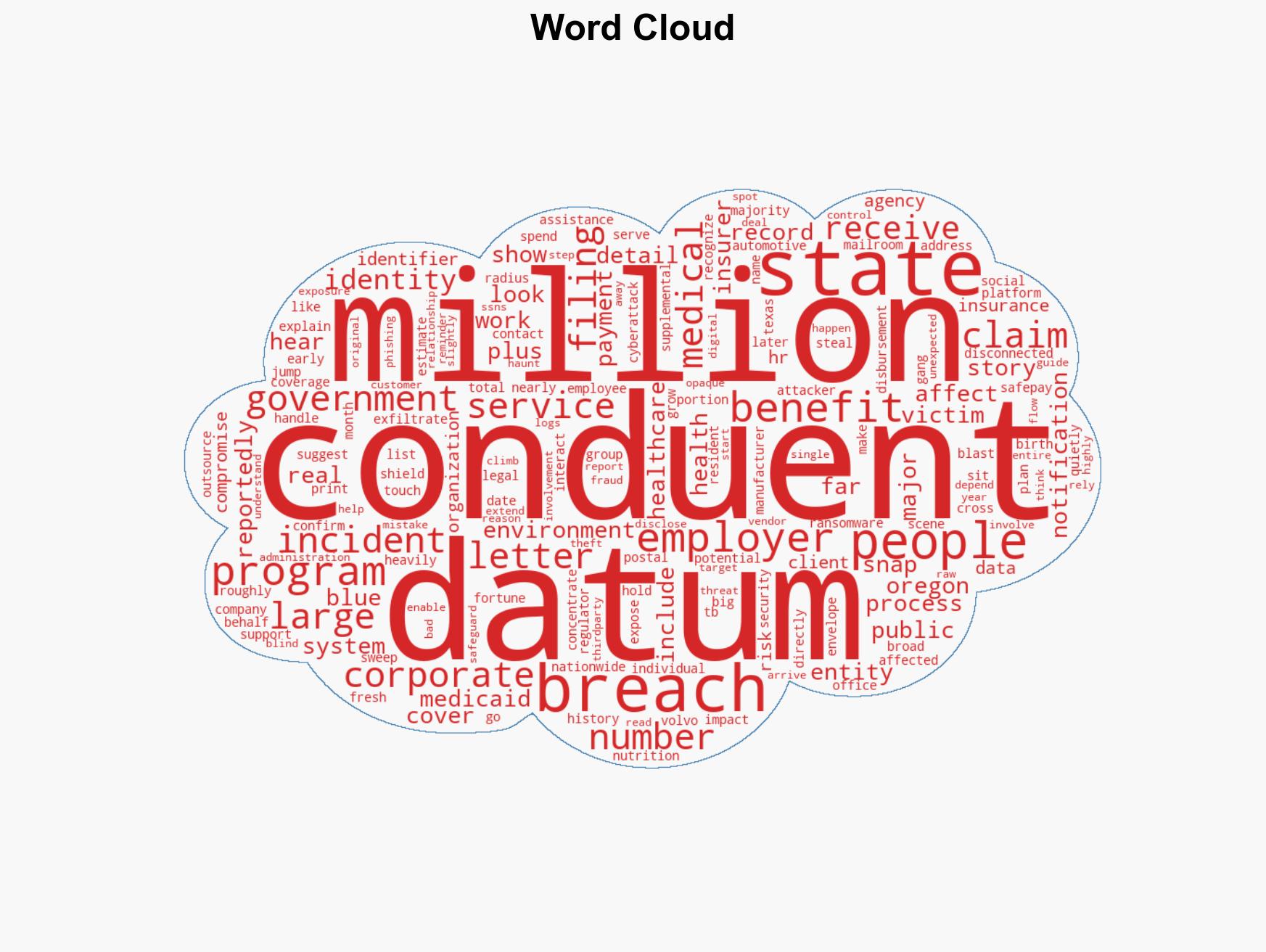
cybersecurity, data breach, ransomware, third-party risk, healthcare data, information security, regulatory compliance
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us