Conduent Data Breach Expands, Impacting Over 25 Million Individuals Nationwide
Published on: 2026-02-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Conduent data breach grows affecting at least 25M people TechCrunch
1. BLUF (Bottom Line Up Front)
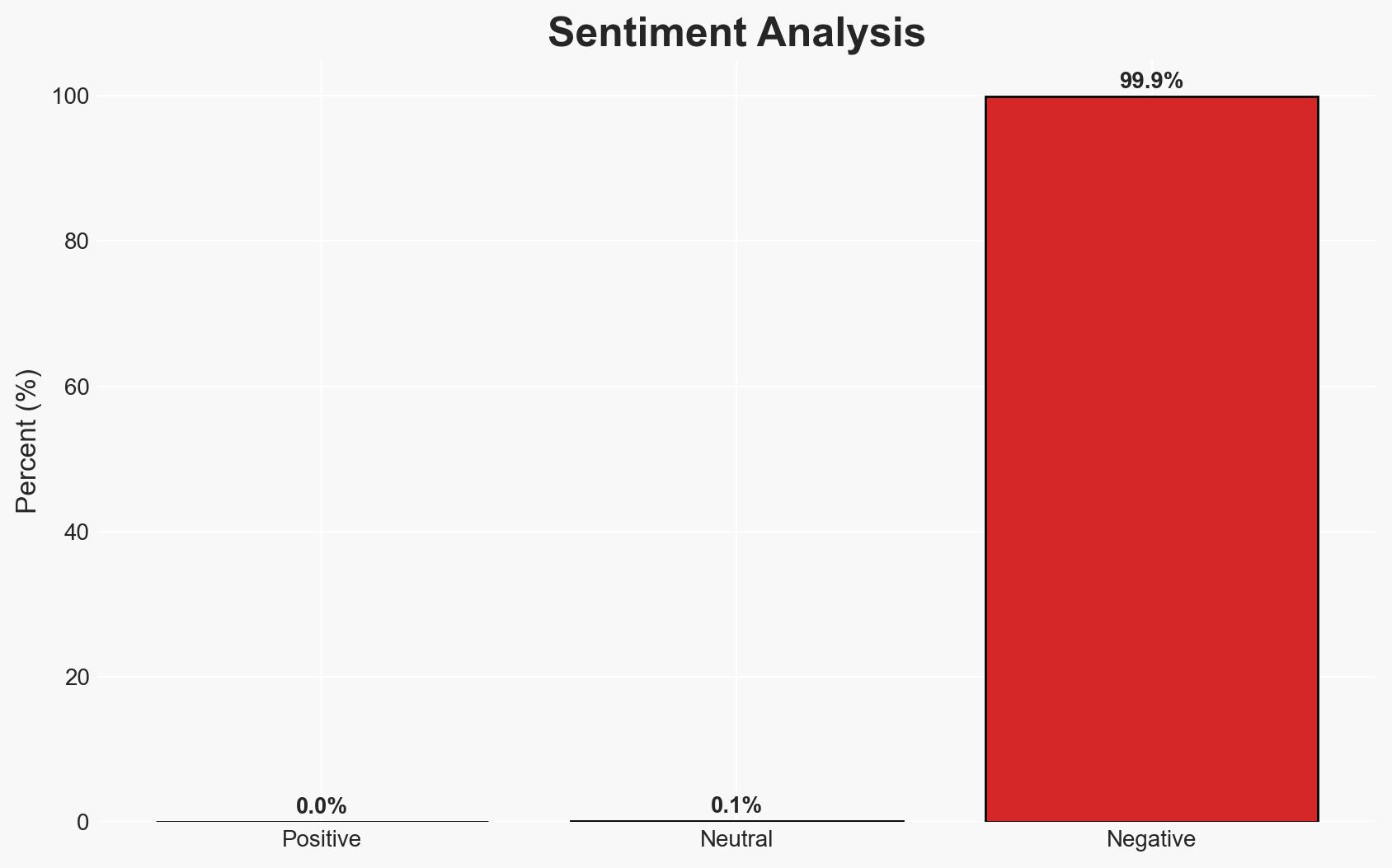
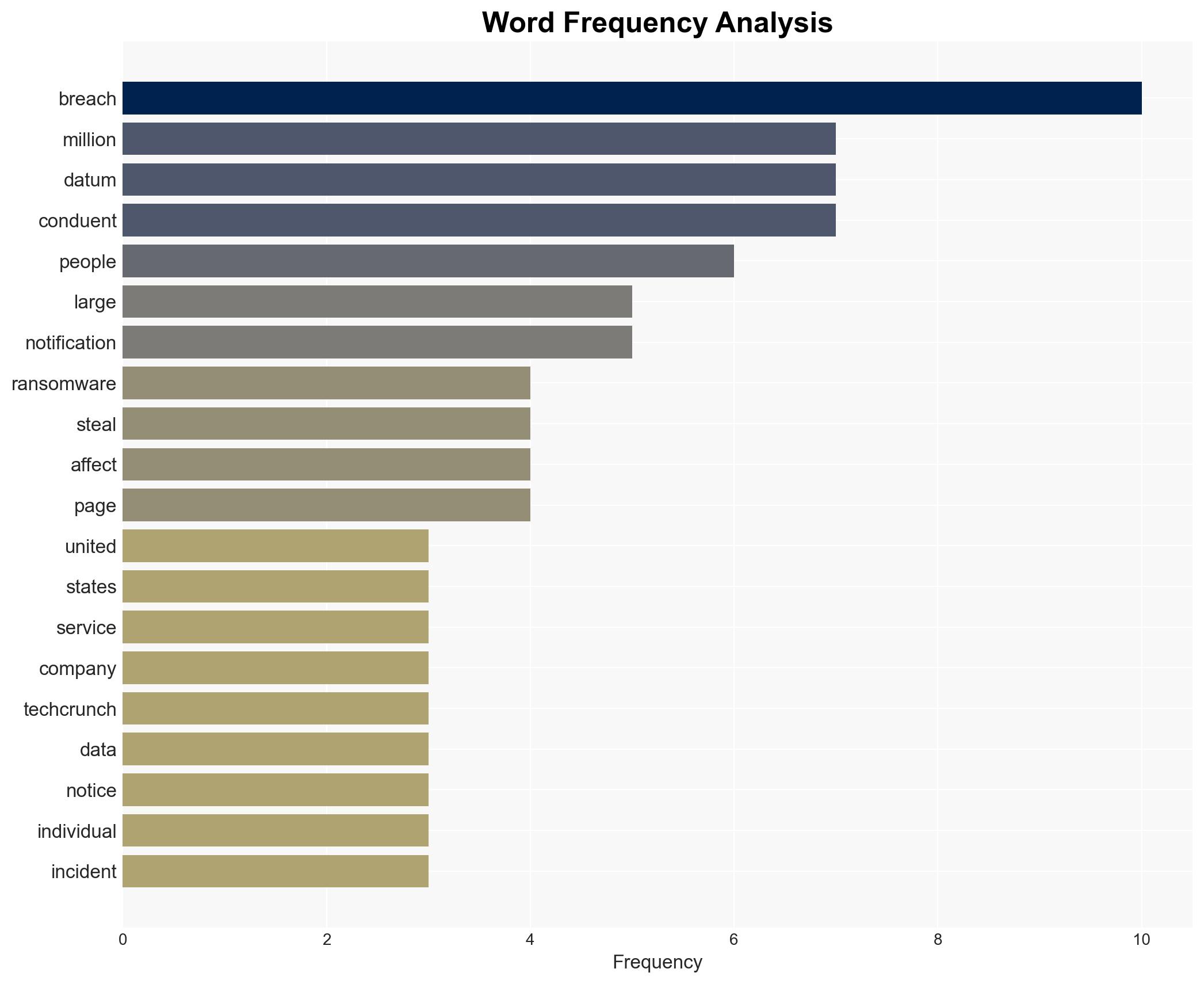
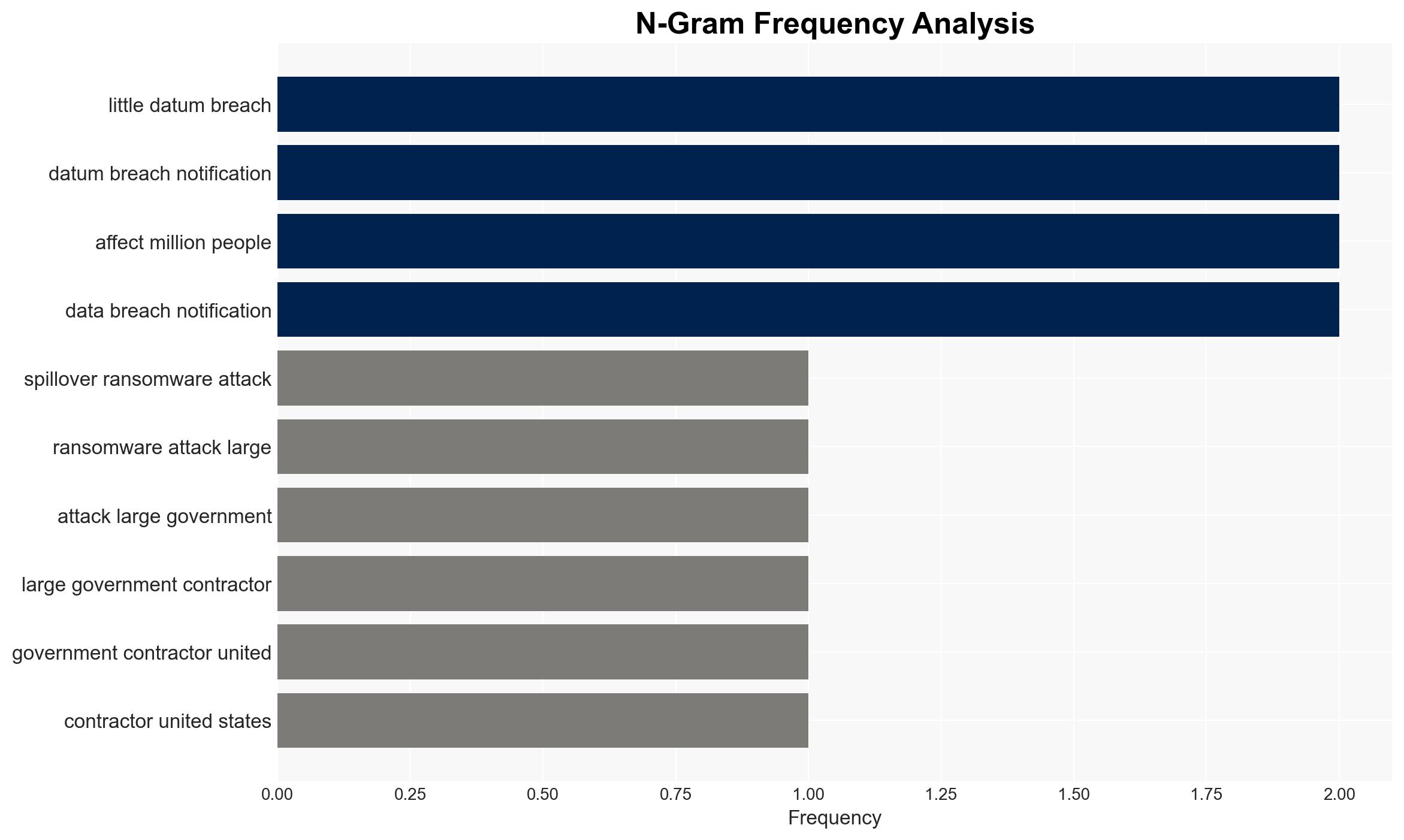
The Conduent data breach has compromised the personal information of at least 25 million individuals, primarily in Oregon and Texas. The breach, attributed to a ransomware attack, raises significant concerns about data security practices within major government contractors. The company’s limited transparency and potential efforts to obscure the incident exacerbate these concerns. Overall confidence in this assessment is moderate due to incomplete information about the breach’s specifics and the company’s response.
2. Competing Hypotheses
- Hypothesis A: The breach resulted from a sophisticated ransomware attack exploiting vulnerabilities in Conduent’s systems. Evidence includes the scale of the breach and the targeting of a major contractor handling sensitive data. However, the lack of detailed technical information about the breach limits certainty.
- Hypothesis B: The breach was facilitated by internal negligence or insufficient cybersecurity measures, such as inadequate multi-factor authentication. This is supported by comparisons to similar breaches, but contradicted by the absence of explicit evidence of internal failings.
- Assessment: Hypothesis A is currently better supported due to the known involvement of a ransomware group and the scale of the breach. Indicators such as further technical details or insider testimony could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Conduent’s systems were targeted due to their role in handling sensitive data; the breach was primarily external in origin; affected individuals’ data is at risk of misuse.
- Information Gaps: Specific vulnerabilities exploited, the identity and motivations of the attackers, and Conduent’s internal cybersecurity posture remain unclear.
- Bias & Deception Risks: Potential bias in reporting due to reliance on company statements; possible deception by Conduent in minimizing the breach’s visibility and impact.
4. Implications and Strategic Risks
This breach could lead to increased scrutiny of government contractors’ cybersecurity practices and influence future regulatory measures. The incident may also embolden other cyber actors to target similar entities.
- Political / Geopolitical: Potential for increased regulatory oversight and political pressure on contractors handling sensitive data.
- Security / Counter-Terrorism: Heightened risk environment for government contractors and critical infrastructure sectors.
- Cyber / Information Space: Increased focus on ransomware threats and the need for robust cybersecurity frameworks.
- Economic / Social: Potential financial liabilities for Conduent and loss of public trust in data security measures.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive audit of Conduent’s cybersecurity measures; enhance monitoring of affected data; engage with stakeholders to assess breach impact.
- Medium-Term Posture (1–12 months): Develop partnerships for information sharing on cyber threats; invest in cybersecurity infrastructure and training; review and update data protection policies.
- Scenario Outlook:
- Best: Enhanced security measures prevent further breaches, restoring trust.
- Worst: Additional breaches occur, leading to significant financial and reputational damage.
- Most-Likely: Incremental improvements in cybersecurity posture with ongoing regulatory scrutiny.
6. Key Individuals and Entities
- Conduent
- Sean Collins (Conduent spokesperson)
- State governments of Oregon, Texas, Massachusetts, New Hampshire, Washington
- Unnamed Russian-speaking ransomware group
7. Thematic Tags
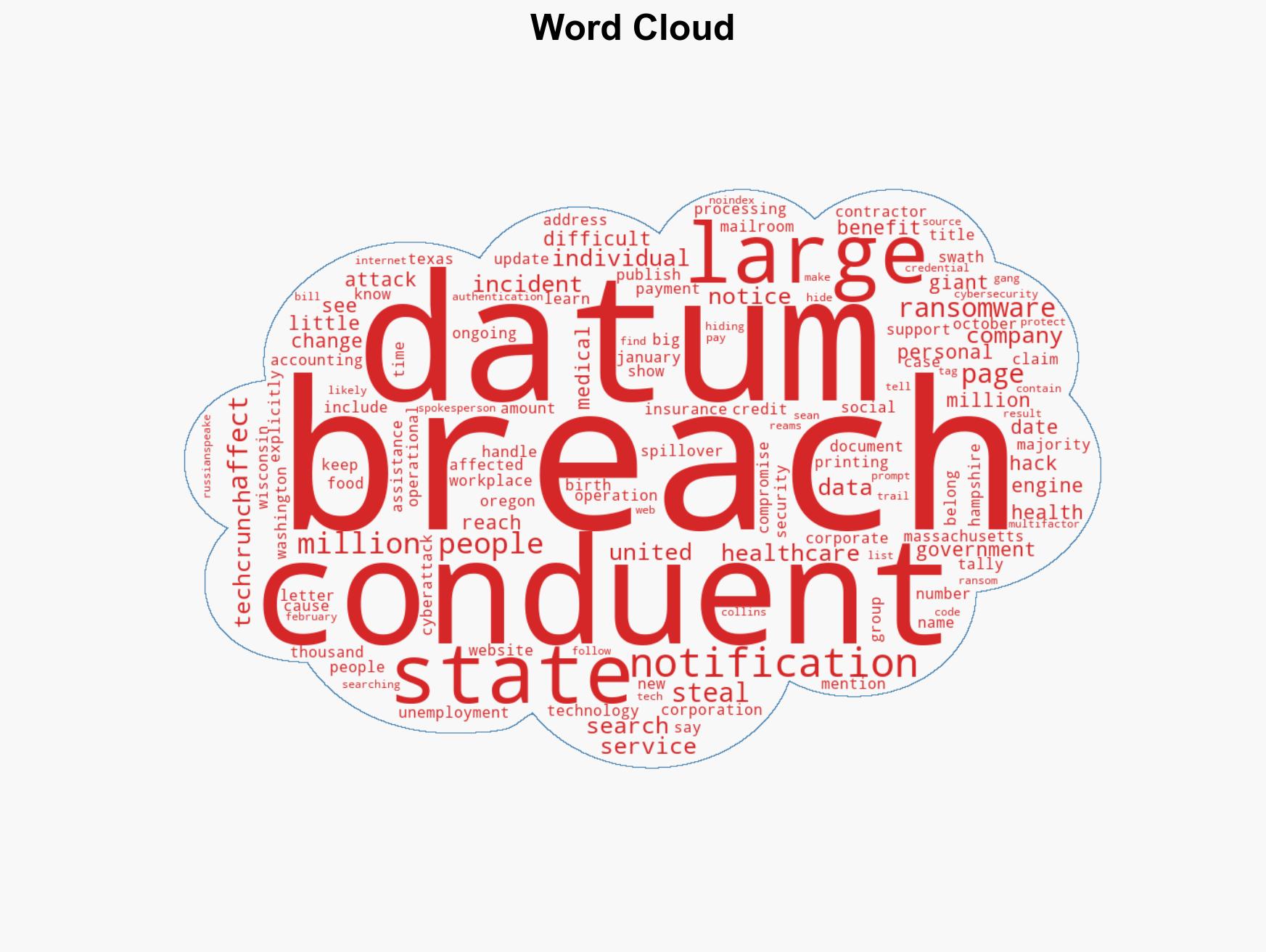
cybersecurity, data breach, ransomware, government contractors, information security, regulatory oversight, personal data protection
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us