Coruna Exploit Kit Compromises Older iPhones, Targeting Financial Data Through Advanced Techniques
Published on: 2026-03-05
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Coruna Exploit Kit Targets Older iPhones in Multi-Stage Campaigns
1. BLUF (Bottom Line Up Front)
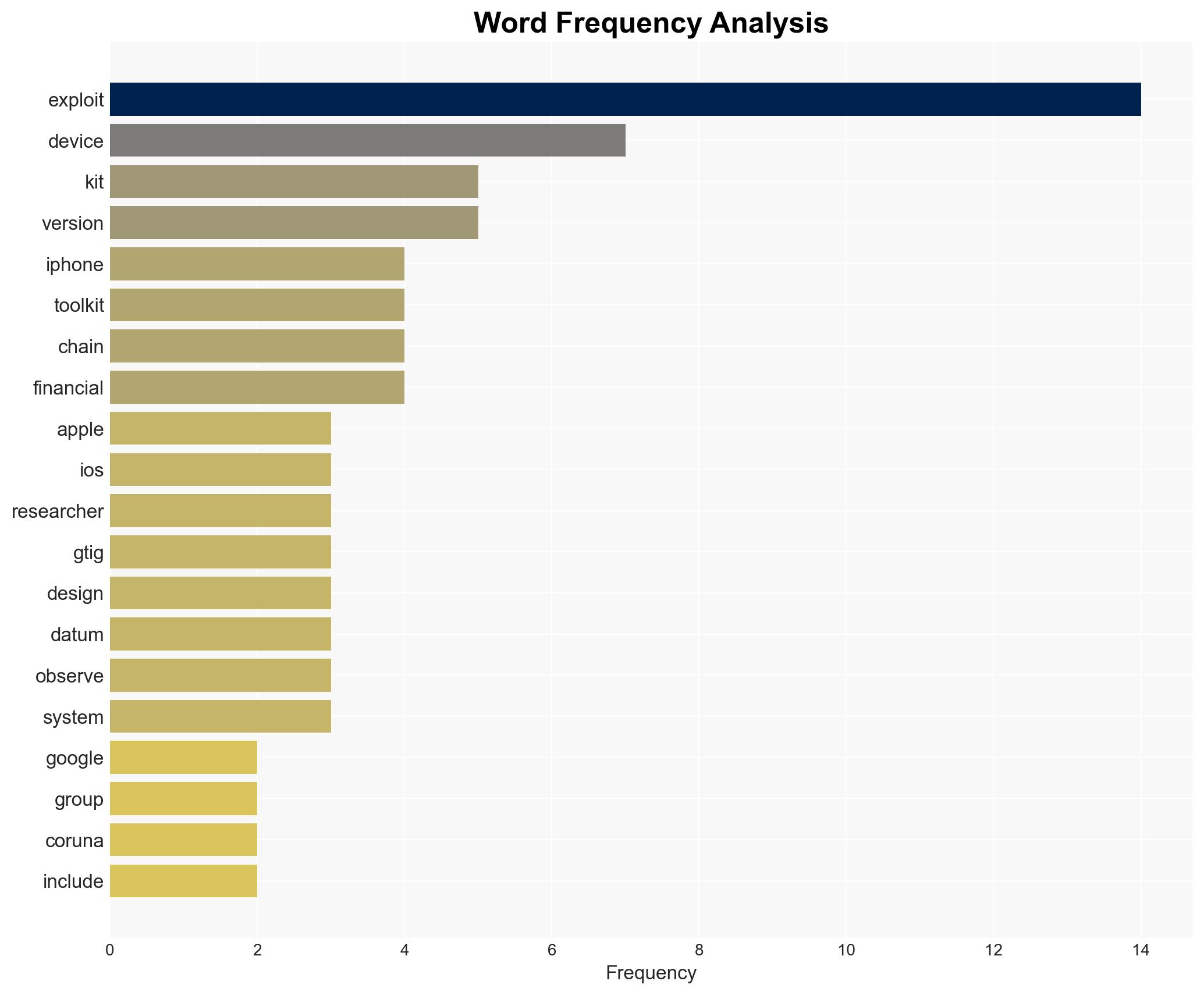
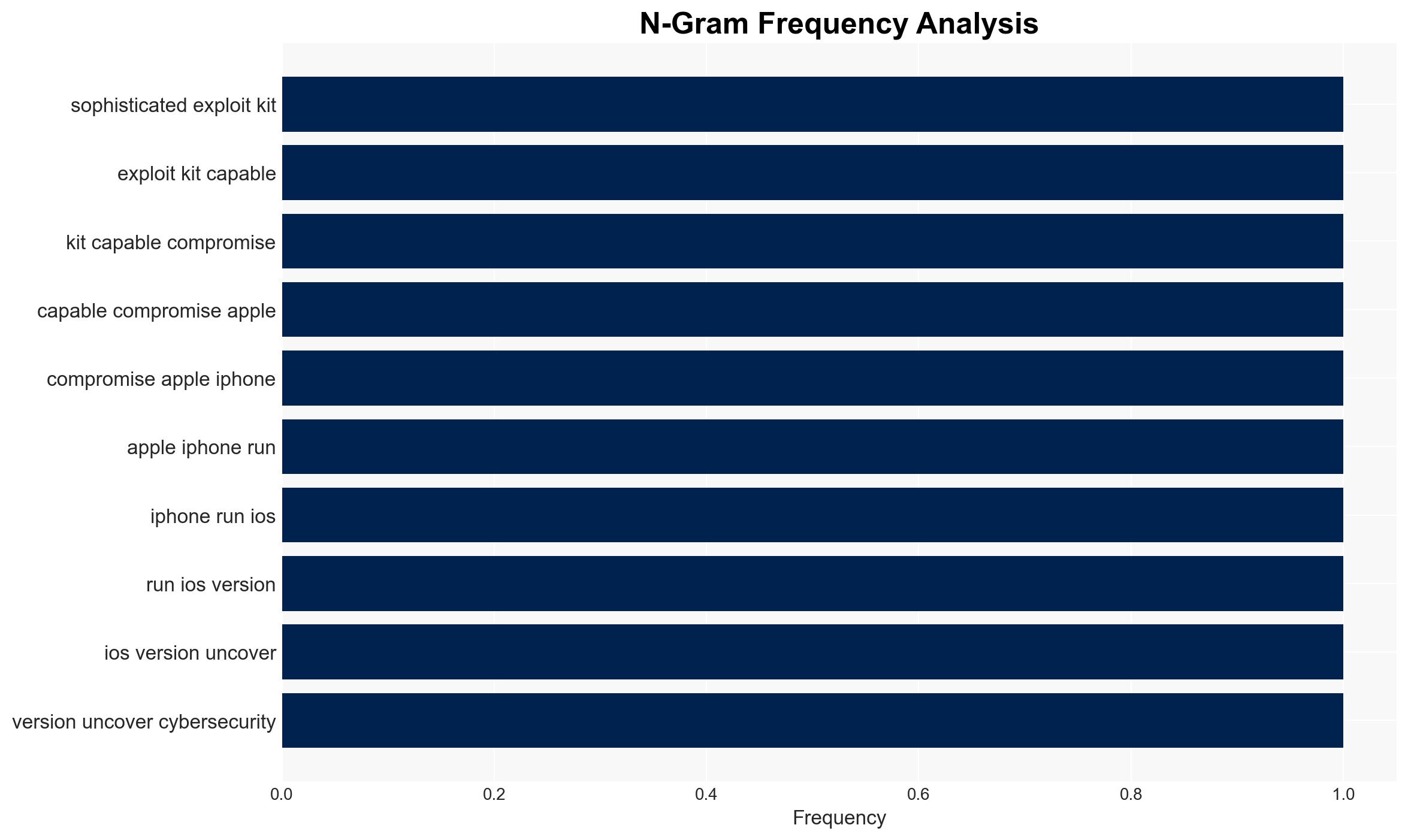
The Coruna Exploit Kit is a sophisticated tool targeting older iPhones, exploiting vulnerabilities in iOS versions 13.0 through 17.2.1. It has been linked to both espionage and financially motivated actors, with significant implications for cybersecurity and user privacy. The most likely hypothesis is that it serves dual purposes for espionage and financial gain, with moderate confidence due to the diverse actor involvement and technical complexity.
2. Competing Hypotheses
- Hypothesis A: The Coruna Exploit Kit is primarily an espionage tool used by state-sponsored actors, evidenced by its initial use against Ukrainian targets by a suspected Russian group. However, its later use by a financially motivated Chinese actor suggests a broader application.
- Hypothesis B: The kit is a commercial tool designed for financial exploitation, evidenced by its deployment in campaigns targeting financial data. The initial espionage use may have been opportunistic or secondary.
- Assessment: Hypothesis A is currently better supported due to the initial state-sponsored targeting and the sophistication of the exploit chains, which are more indicative of espionage capabilities. Key indicators such as further state-sponsored attacks or exclusive financial targeting could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The exploit kit’s complexity implies state-level resources; the actors identified are accurately linked to the campaigns; the vulnerabilities are not patched in older iOS versions.
- Information Gaps: The full extent of the toolkit’s deployment and the identities of all actors involved remain unclear.
- Bias & Deception Risks: Potential bias in attributing the toolkit to state actors without definitive proof; possibility of false-flag operations to mislead attribution.
4. Implications and Strategic Risks
This development could lead to increased tensions between involved states and heightened cybersecurity measures globally. The evolution of such exploit kits may influence broader cyber defense strategies and international norms.
- Political / Geopolitical: Potential escalation in cyber conflicts, particularly involving Russia and China.
- Security / Counter-Terrorism: Increased threat to personal and national security through data breaches and espionage.
- Cyber / Information Space: Possible proliferation of similar tools, enhancing cyber threat landscapes.
- Economic / Social: Potential economic impacts from financial data theft and loss of consumer trust in digital security.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of iOS vulnerabilities, collaborate with tech companies for patch development, and increase public awareness of potential threats.
- Medium-Term Posture (1–12 months): Develop international partnerships for cyber threat intelligence sharing and invest in research for advanced threat detection capabilities.
- Scenario Outlook:
- Best: Rapid patching of vulnerabilities and international cooperation reduces threat impact.
- Worst: Exploit kit evolves, leading to widespread data breaches and geopolitical tensions.
- Most-Likely: Continued use in targeted campaigns with gradual mitigation as patches are deployed.
6. Key Individuals and Entities
- UNC6353 (Suspected Russian espionage group)
- UNC6691 (Financially motivated actor from China)
- Google’s Threat Intelligence Group (GTIG)
7. Thematic Tags
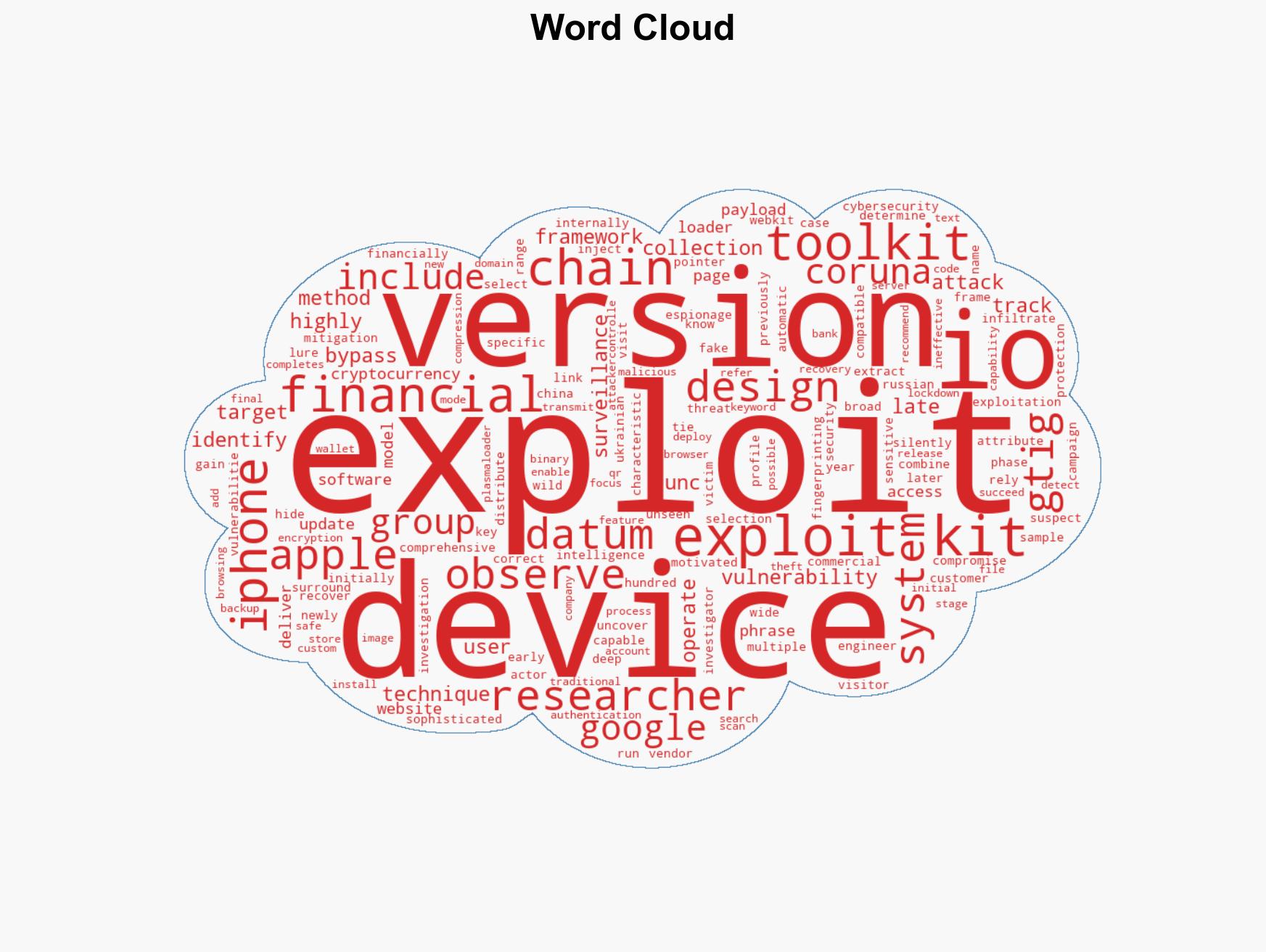
cybersecurity, cyber-espionage, financial cybercrime, iOS vulnerabilities, state-sponsored hacking, exploit kits, international cyber threats
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us