Court dismisses terrorism claims against Binance as CZ asserts centralized exchanges lack incentive to suppor…
Published on: 2026-03-08
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
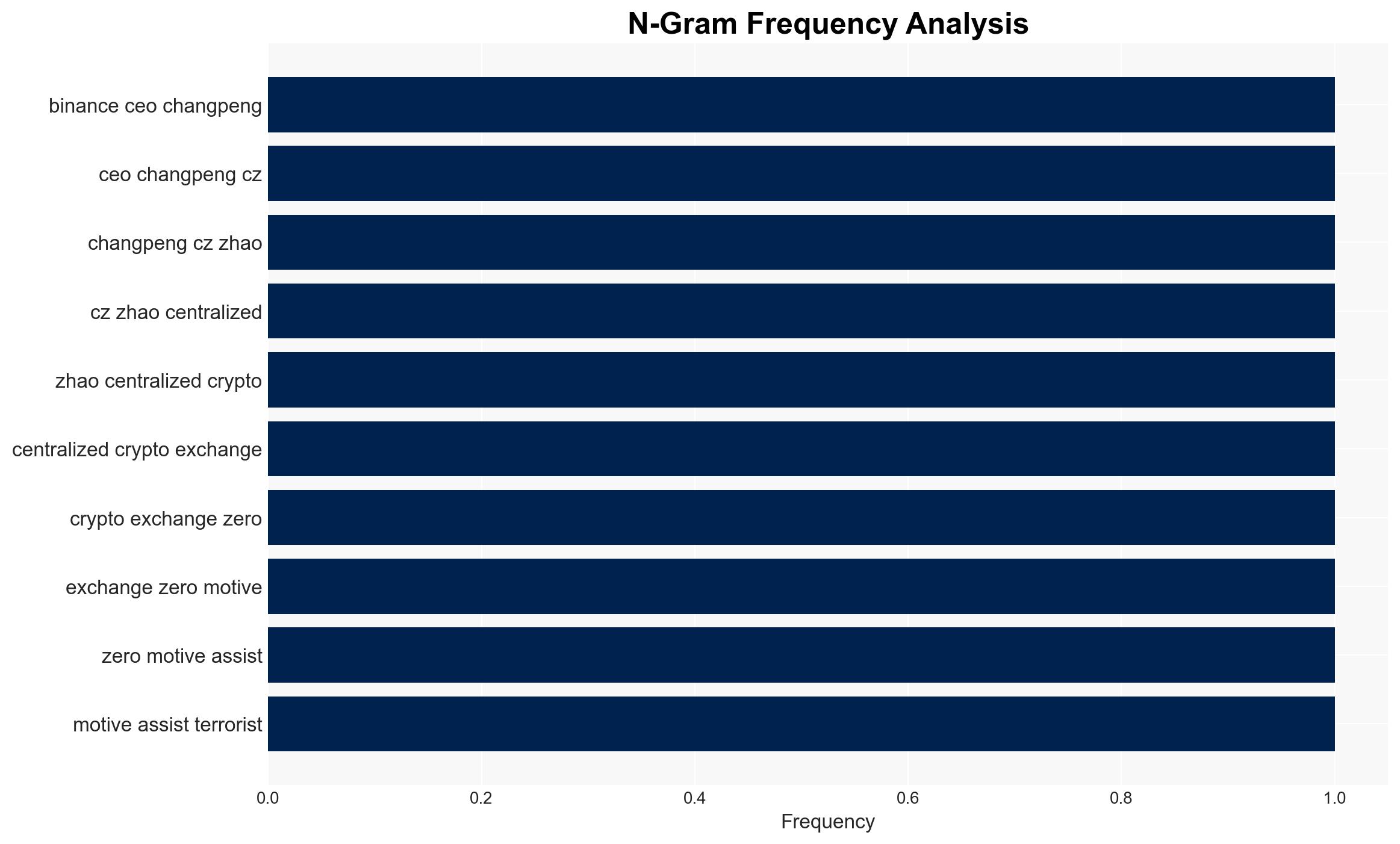
Intelligence Report: CZ says CEXs have zero motive to aid terrorists as court dismisses terrorism case
1. BLUF (Bottom Line Up Front)
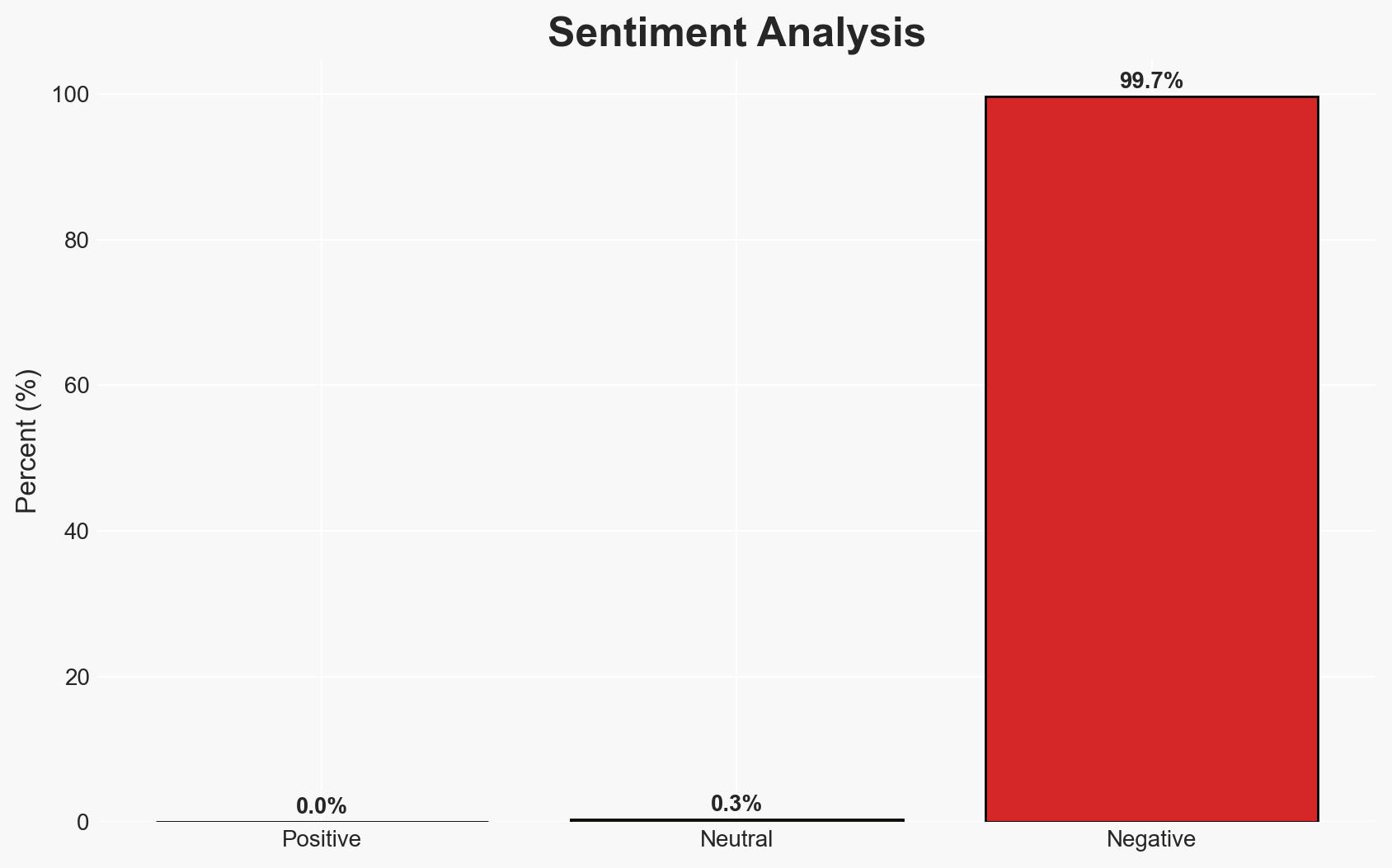
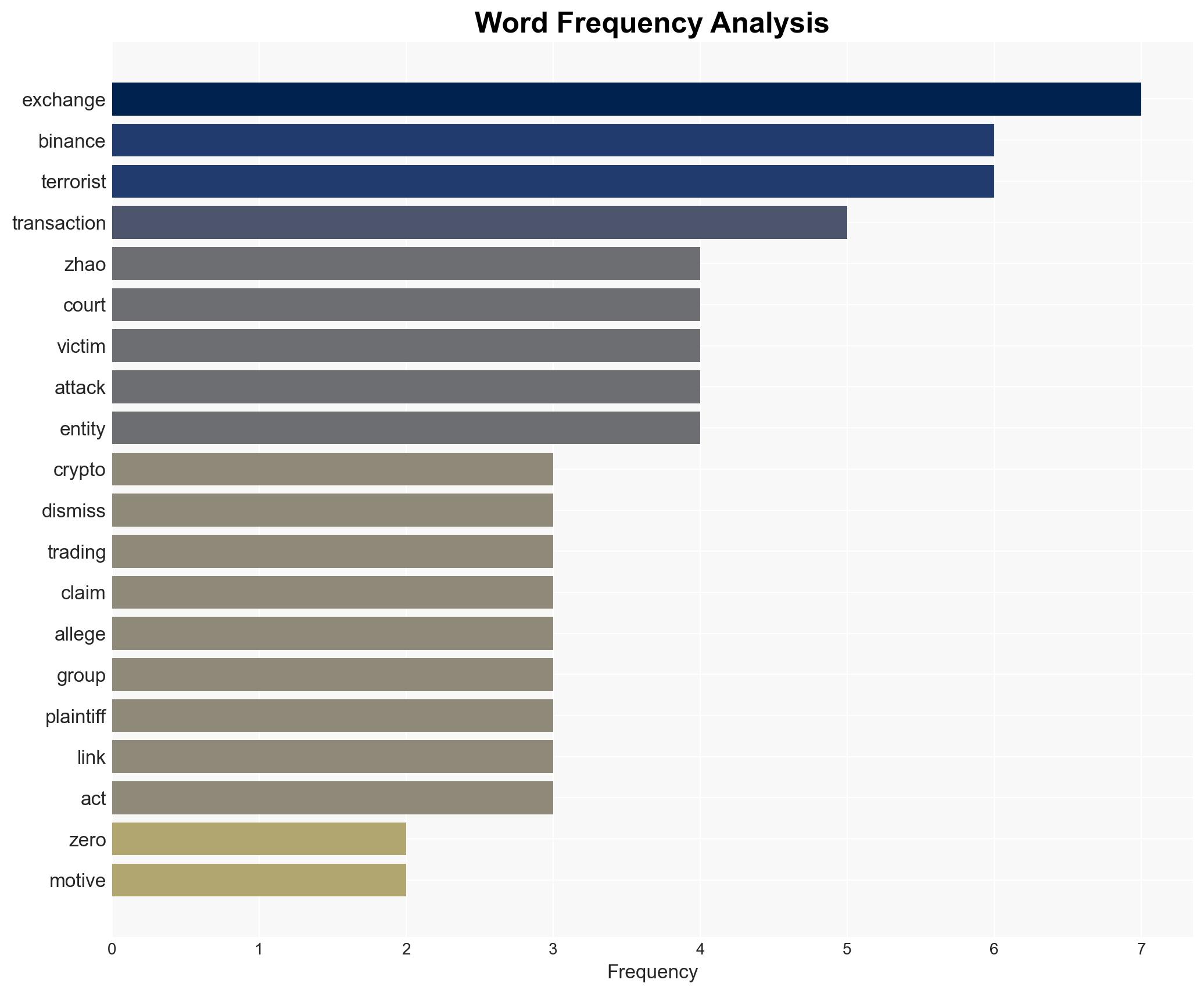
The dismissal of the lawsuit against Binance by the US District Court underscores the lack of direct evidence linking centralized crypto exchanges (CEXs) to terrorist financing. The court’s decision highlights the challenges in proving such connections under current legal frameworks. This development affects regulatory scrutiny on crypto exchanges and their compliance practices. Overall confidence in this judgment is moderate.
2. Competing Hypotheses
- Hypothesis A: Centralized crypto exchanges like Binance have no incentive to facilitate terrorist financing due to the economic and reputational risks involved. Supporting evidence includes the court’s dismissal of the case and statements from Binance leadership. However, uncertainties remain regarding the full extent of compliance failures.
- Hypothesis B: Centralized crypto exchanges may inadvertently facilitate terrorist financing due to inadequate compliance mechanisms. Contradicting evidence includes allegations of compliance failures and transactions linked to sanctioned entities, though these remain unproven in court.
- Assessment: Hypothesis A is currently better supported due to the court’s ruling and lack of direct evidence linking Binance to specific terrorist activities. Key indicators that could shift this judgment include new evidence of compliance failures or successful legal challenges.
3. Key Assumptions and Red Flags
- Assumptions: CEXs prioritize legal compliance to maintain market position; legal frameworks are sufficient to address crypto-related terrorism financing; the court’s ruling reflects a comprehensive review of evidence.
- Information Gaps: Detailed internal compliance records of Binance; extent of crypto transactions linked to terrorist groups beyond those identified in the lawsuit.
- Bias & Deception Risks: Potential bias in public statements by Binance leadership; risks of selective disclosure of compliance practices; possibility of deceptive practices by entities using crypto for illicit purposes.
4. Implications and Strategic Risks
This development may influence regulatory approaches to crypto exchanges and their role in financial crimes. It could also impact the perceived legitimacy of crypto markets.
- Political / Geopolitical: Potential for increased regulatory scrutiny and international cooperation on crypto regulation.
- Security / Counter-Terrorism: Ongoing challenges in tracking and preventing crypto-based terrorist financing.
- Cyber / Information Space: Possible increase in cyber threats targeting crypto exchanges for financial gain.
- Economic / Social: Impacts on investor confidence in crypto markets; potential shifts in market dynamics if regulatory actions intensify.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of crypto transactions for illicit activities; engage with regulatory bodies to clarify compliance expectations.
- Medium-Term Posture (1–12 months): Develop partnerships with law enforcement for better information sharing; invest in compliance and monitoring technologies.
- Scenario Outlook: Best: Strengthened compliance leads to reduced regulatory pressure. Worst: New evidence emerges, leading to legal challenges and market instability. Most-Likely: Continued scrutiny with incremental regulatory adjustments.
6. Key Individuals and Entities
- Changpeng “CZ” Zhao, Binance
- US District Court for the Southern District of New York
- BAM Trading Services
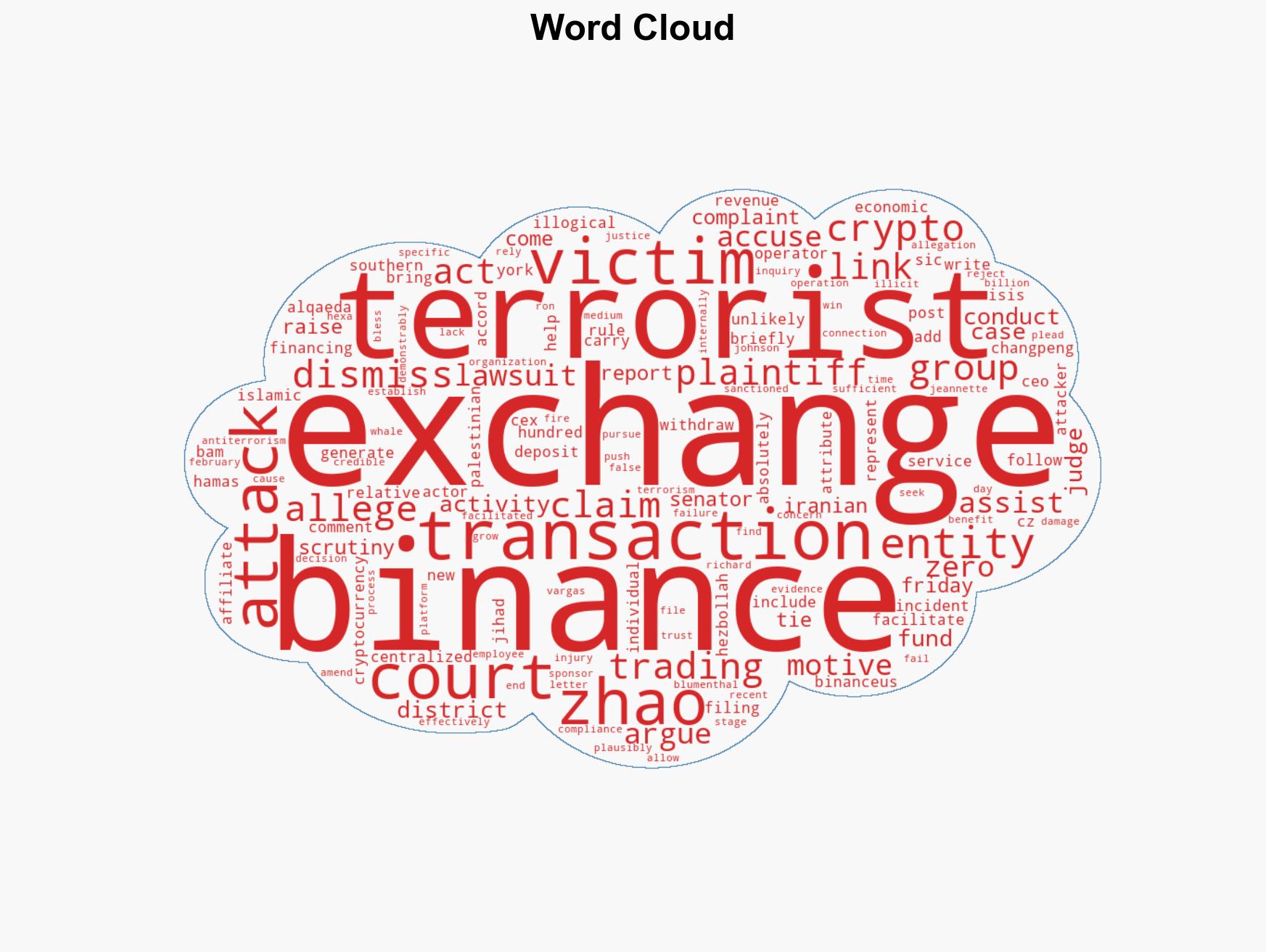
- Hezbollah, Hamas, ISIS, al-Qaeda, Palestinian Islamic Jihad
- Senators Richard Blumenthal and Ron Johnson
7. Thematic Tags
Counter-Terrorism, cryptocurrency regulation, legal frameworks, compliance, financial crime, sanctions, cyber-security
Structured Analytic Techniques Applied
- ACH 2.0: Reconstruct likely threat actor intentions via hypothesis testing and structured refutation.
- Indicators Development: Track radicalization signals and propaganda patterns to anticipate operational planning.
- Narrative Pattern Analysis: Analyze spread/adaptation of ideological narratives for recruitment/incitement signals.
Explore more:
Counter-Terrorism Briefs ·
Daily Summary ·
Support us