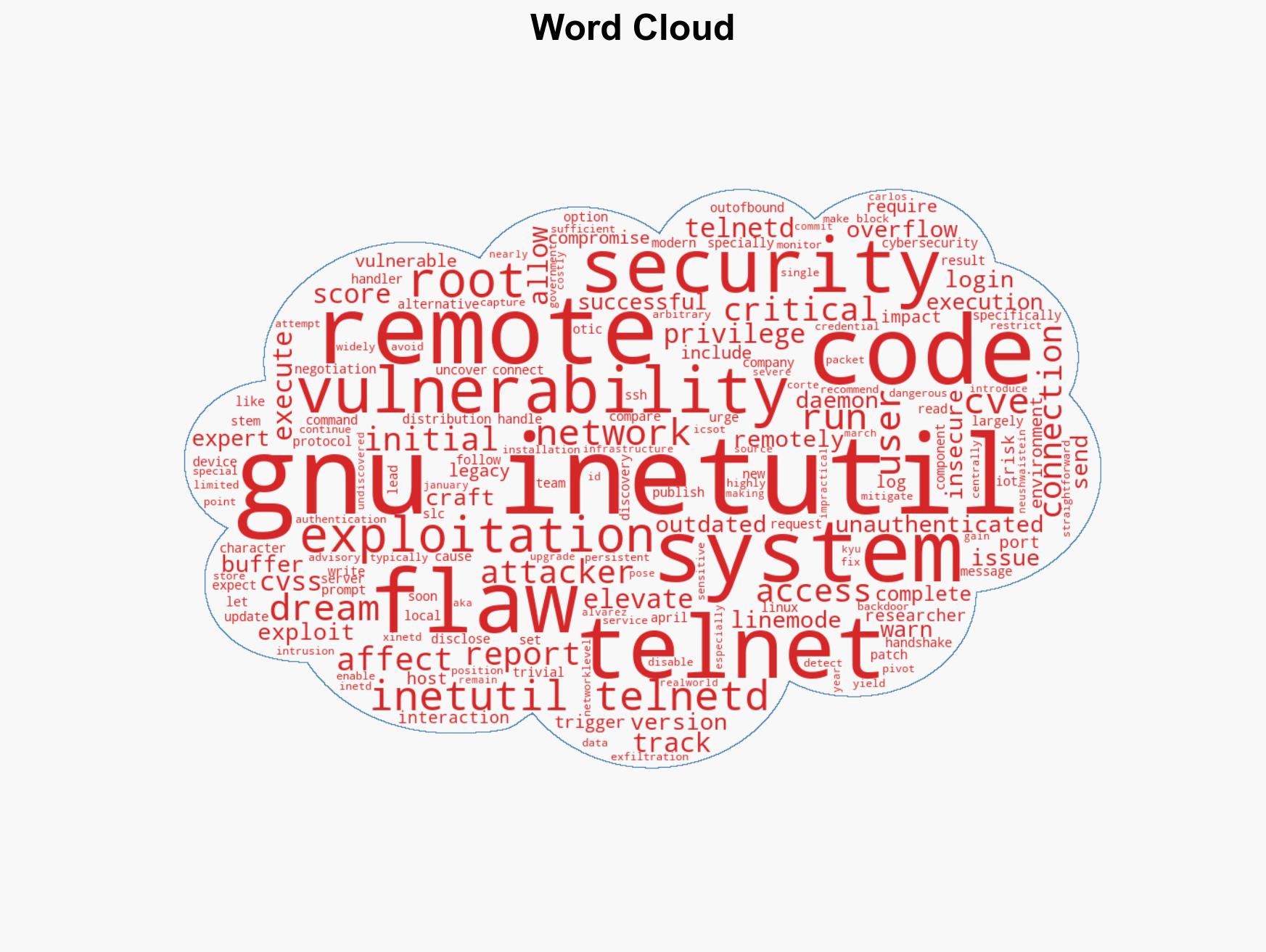
Critical CVE-2026-32746 flaw in GNU InetUtils telnetd exposes all versions to remote code execution risks
Published on: 2026-03-18
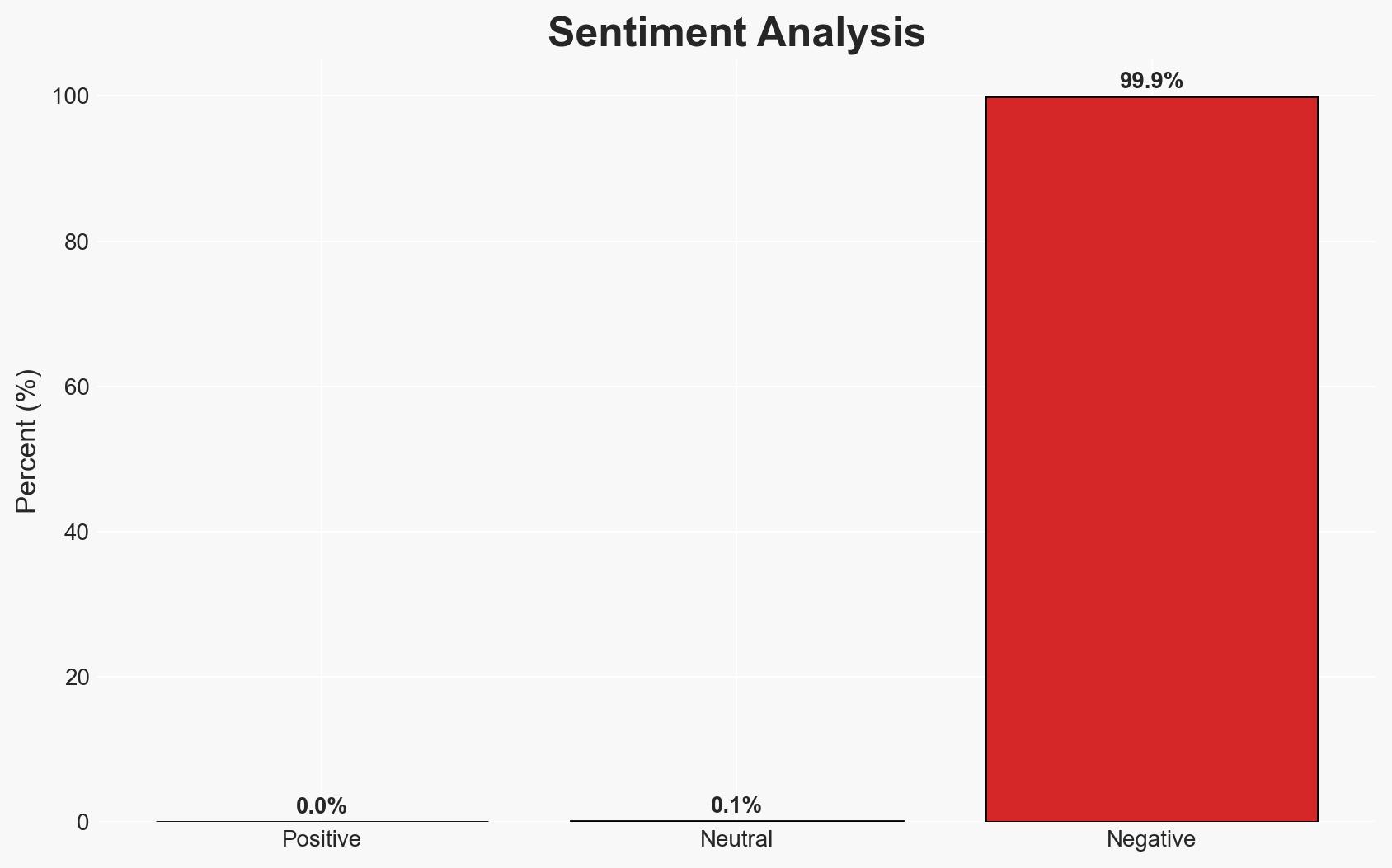
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Researchers warn of unpatched critical Telnetd flaw affecting all versions
1. BLUF (Bottom Line Up Front)
The critical vulnerability CVE-2026-32746 in GNU InetUtils telnetd allows unauthenticated remote code execution with elevated privileges, posing significant risks to systems using Telnet, particularly in legacy environments. The flaw’s trivial exploitation method makes it a high-priority threat. Moderate confidence is placed in the assessment that legacy systems in critical infrastructure sectors are most at risk.
2. Competing Hypotheses
- Hypothesis A: The vulnerability will be actively exploited by threat actors targeting legacy systems in critical infrastructure due to the ease of exploitation and potential for significant impact. Supporting evidence includes the widespread use of Telnet in these environments and the lack of immediate patching. Key uncertainties include the speed of patch deployment and the effectiveness of interim mitigations.
- Hypothesis B: The vulnerability will not lead to widespread exploitation due to increased awareness and proactive defensive measures by system administrators. This hypothesis is less supported due to the historical persistence of outdated systems in critical sectors and the delayed patch timeline.
- Assessment: Hypothesis A is currently better supported given the vulnerability’s high CVSS score, ease of exploitation, and the prevalence of Telnet in vulnerable environments. Indicators such as increased network scanning activity on port 23 and reports of exploitation attempts could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Telnet remains widely used in critical infrastructure; patch deployment will be delayed; attackers have the capability to exploit the vulnerability.
- Information Gaps: The exact number of vulnerable systems and the timeline for patch deployment are unknown.
- Bias & Deception Risks: Potential bias in underestimating the speed of patch adoption; no clear indicators of deception in the reporting.
4. Implications and Strategic Risks
The vulnerability could lead to increased cyber threats against critical infrastructure, potentially disrupting essential services. The reliance on outdated systems exacerbates this risk.
- Political / Geopolitical: Potential for increased tensions if state-sponsored actors exploit the vulnerability against adversaries.
- Security / Counter-Terrorism: Heightened risk of cyber-attacks on critical infrastructure, necessitating enhanced defensive measures.
- Cyber / Information Space: Increased activity in the cyber domain, with potential for misinformation or disinformation campaigns exploiting the vulnerability.
- Economic / Social: Possible economic impacts from disrupted services, particularly in sectors reliant on legacy systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Disable Telnet services, block port 23, and implement network monitoring. Urge rapid patch deployment once available.
- Medium-Term Posture (1–12 months): Transition to more secure protocols like SSH, enhance cybersecurity training, and develop incident response capabilities.
- Scenario Outlook:
- Best Case: Rapid patch deployment and mitigation measures prevent widespread exploitation.
- Worst Case: Significant exploitation leads to major disruptions in critical infrastructure.
- Most Likely: Targeted attacks on vulnerable systems with moderate impact, prompting gradual improvements in cybersecurity posture.
6. Key Individuals and Entities
- Dream Security (Cybersecurity company)
- GNU InetUtils Security Team
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, critical infrastructure, vulnerability management, legacy systems, remote code execution, Telnet, network security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us