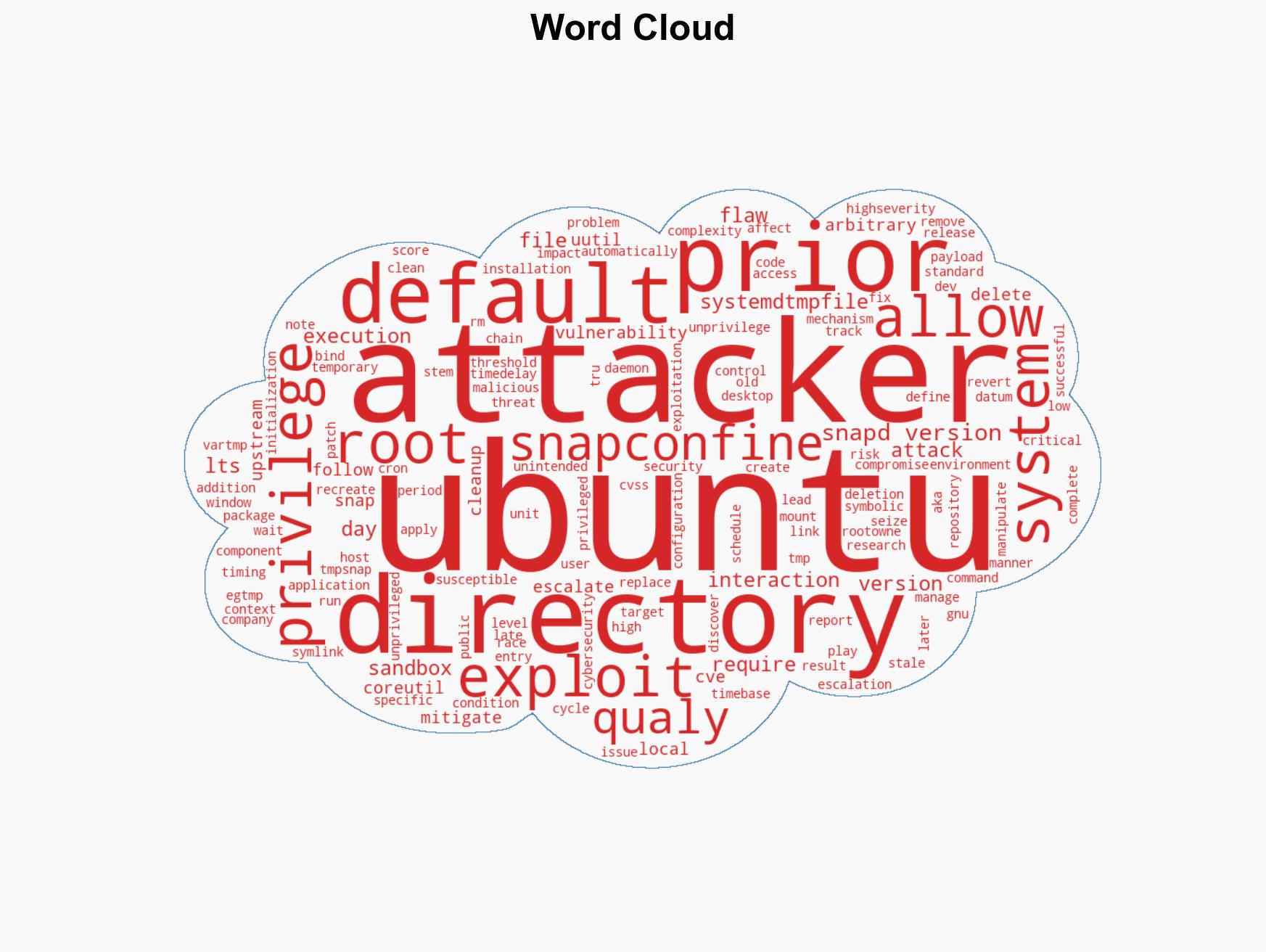
Critical Ubuntu Vulnerability CVE-2026-3888 Allows Local Privilege Escalation to Root Access
Published on: 2026-03-18
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Ubuntu CVE-2026-3888 Bug Lets Attackers Gain Root via systemd Cleanup Timing Exploit
1. BLUF (Bottom Line Up Front)
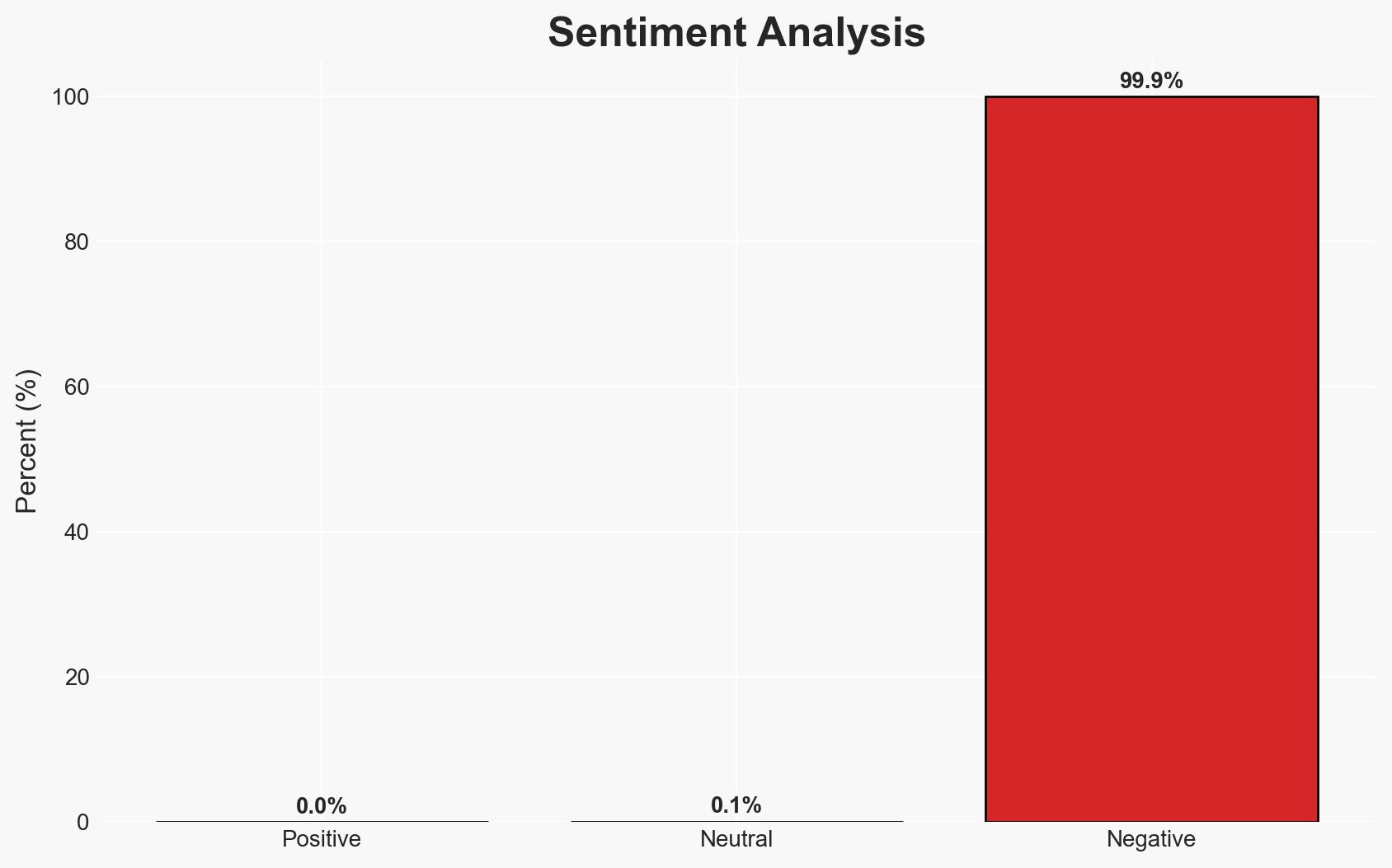
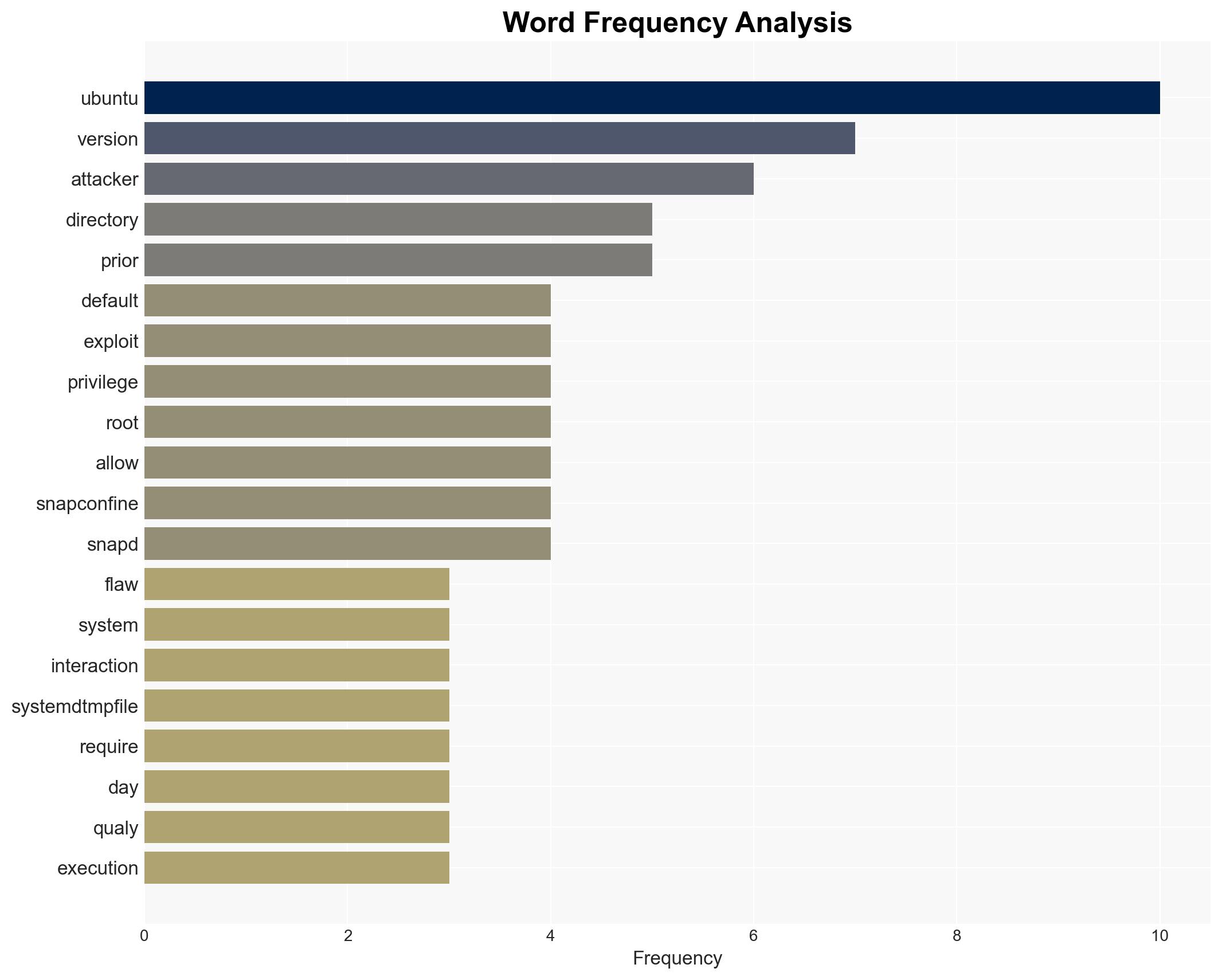
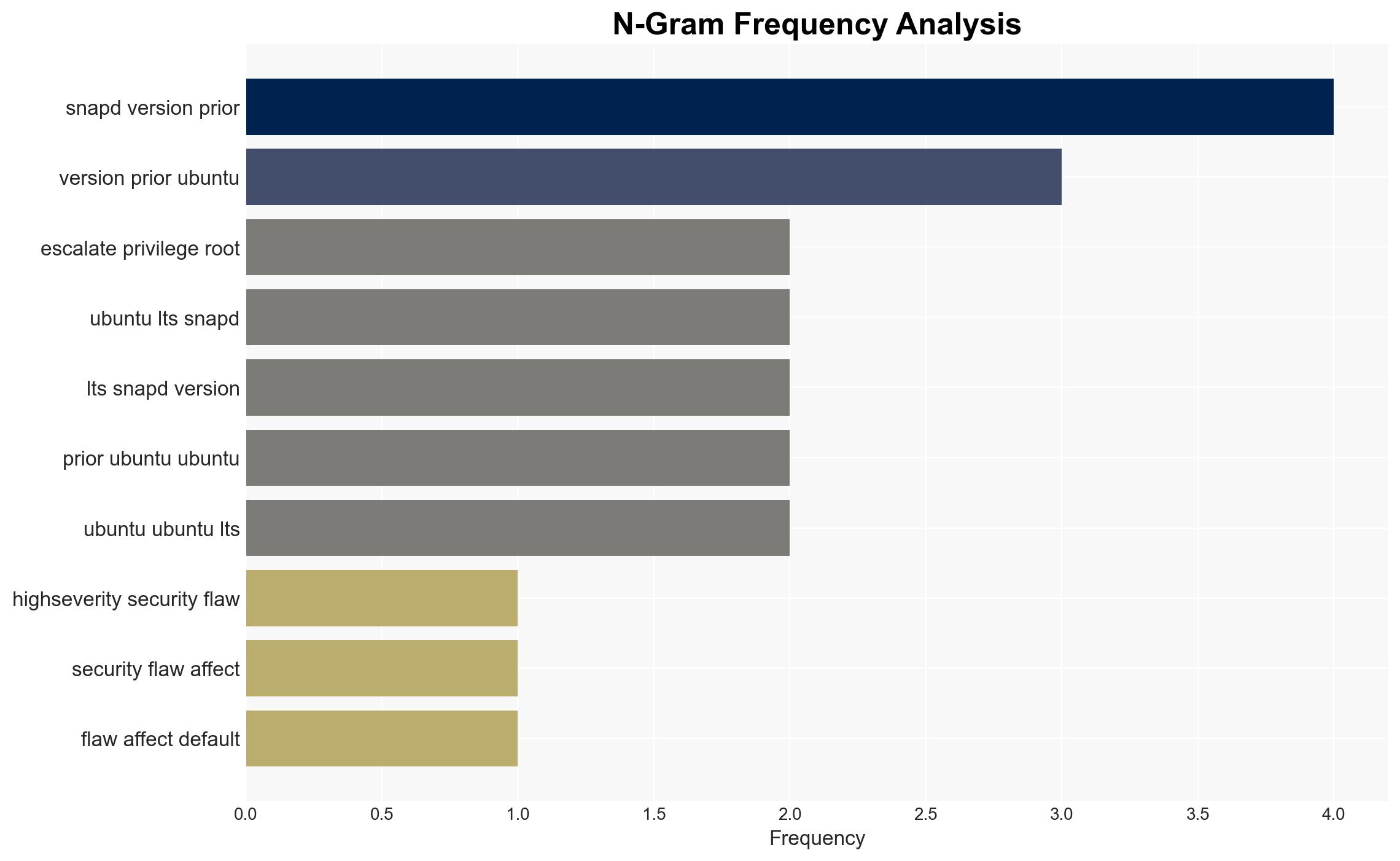
The CVE-2026-3888 vulnerability in Ubuntu Desktop versions 24.04 and later poses a significant security risk by allowing local attackers to escalate privileges to root. The exploit leverages a timing flaw between snap-confine and systemd-tmpfiles. This vulnerability has been patched in newer versions, but systems not updated remain at risk. Overall confidence in this assessment is moderate due to the specificity of the exploit conditions and the availability of patches.
2. Competing Hypotheses
- Hypothesis A: The vulnerability is primarily a result of a design flaw in the interaction between snap-confine and systemd-tmpfiles, which can be mitigated by timely updates. Supporting evidence includes the detailed exploit mechanism and the availability of patches. However, uncertainties exist regarding the extent of systems still vulnerable due to delayed updates.
- Hypothesis B: The vulnerability is indicative of a broader systemic issue within Ubuntu’s security architecture, potentially affecting other components. This hypothesis is less supported due to the lack of evidence of similar vulnerabilities in other components, but it cannot be entirely ruled out without further investigation.
- Assessment: Hypothesis A is currently better supported due to the specific nature of the exploit and the targeted patching that addresses the identified flaw. Key indicators that could shift this judgment include reports of similar vulnerabilities in other components or widespread exploitation despite patch availability.
3. Key Assumptions and Red Flags
- Assumptions: The patch effectively mitigates the vulnerability; most users will apply updates promptly; the exploit requires specific timing conditions that limit its practicality.
- Information Gaps: The extent of systems that remain unpatched; potential for similar vulnerabilities in other system components; detailed attacker capabilities and intentions.
- Bias & Deception Risks: Potential over-reliance on vendor-provided information; lack of independent verification of patch efficacy; possible underestimation of attacker sophistication.
4. Implications and Strategic Risks
This vulnerability could lead to increased scrutiny of Ubuntu’s security practices and potentially erode trust in its security posture. If exploited, it may serve as a vector for broader cyber-attacks, affecting both individual users and organizations.
- Political / Geopolitical: Potential for state actors to exploit the vulnerability for espionage or disruption, particularly if unpatched systems are in critical infrastructure.
- Security / Counter-Terrorism: Increased risk of cyber-attacks targeting vulnerable systems, potentially impacting national security if critical systems are affected.
- Cyber / Information Space: Heightened awareness and potential increase in cyber defense measures; possible exploitation by cybercriminals for financial gain.
- Economic / Social: Potential economic impact from data breaches or system downtimes; loss of consumer confidence in Ubuntu as a secure platform.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urge users to apply patches immediately; monitor for signs of exploitation; increase awareness campaigns about the vulnerability.
- Medium-Term Posture (1–12 months): Develop partnerships for information sharing on vulnerabilities; enhance patch management processes; invest in security audits of similar system components.
- Scenario Outlook:
- Best Case: Rapid patch adoption minimizes impact, and no significant exploitation occurs.
- Worst Case: Widespread exploitation leads to significant data breaches and loss of trust in Ubuntu.
- Most Likely: Moderate exploitation occurs, primarily affecting systems slow to update, with limited broader impact.
6. Key Individuals and Entities
- Qualys Threat Research Unit
- Ubuntu (Canonical Ltd.)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, vulnerability management, Ubuntu, privilege escalation, systemd, snap-confine, patch management
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us