Critical vulnerability CVE-2026-1731 exploited in BeyondTrust products for remote system control and attacks
Published on: 2026-02-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
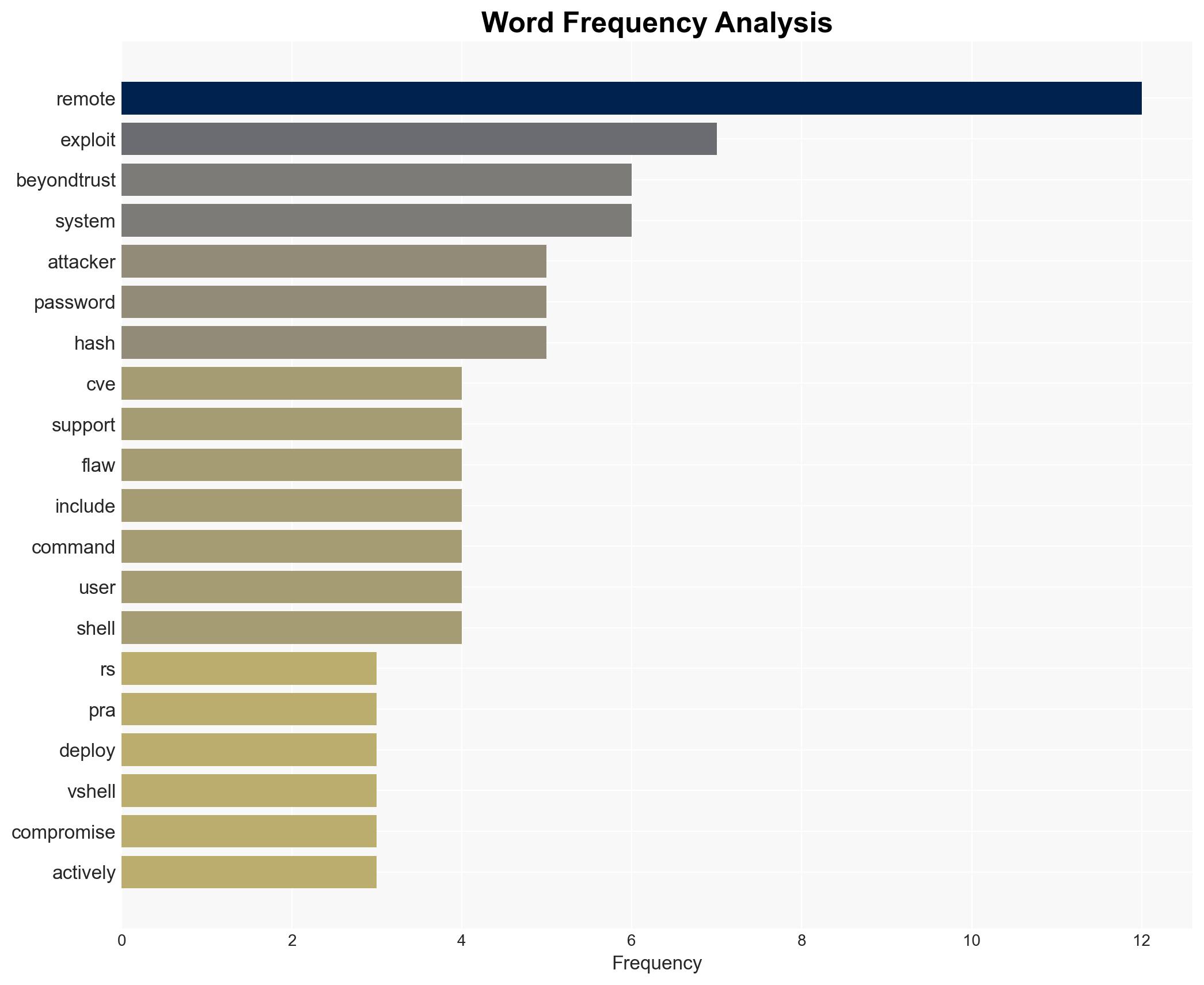
Intelligence Report: CVE-2026-1731 fuels ongoing attacks on BeyondTrust remote access products
1. BLUF (Bottom Line Up Front)
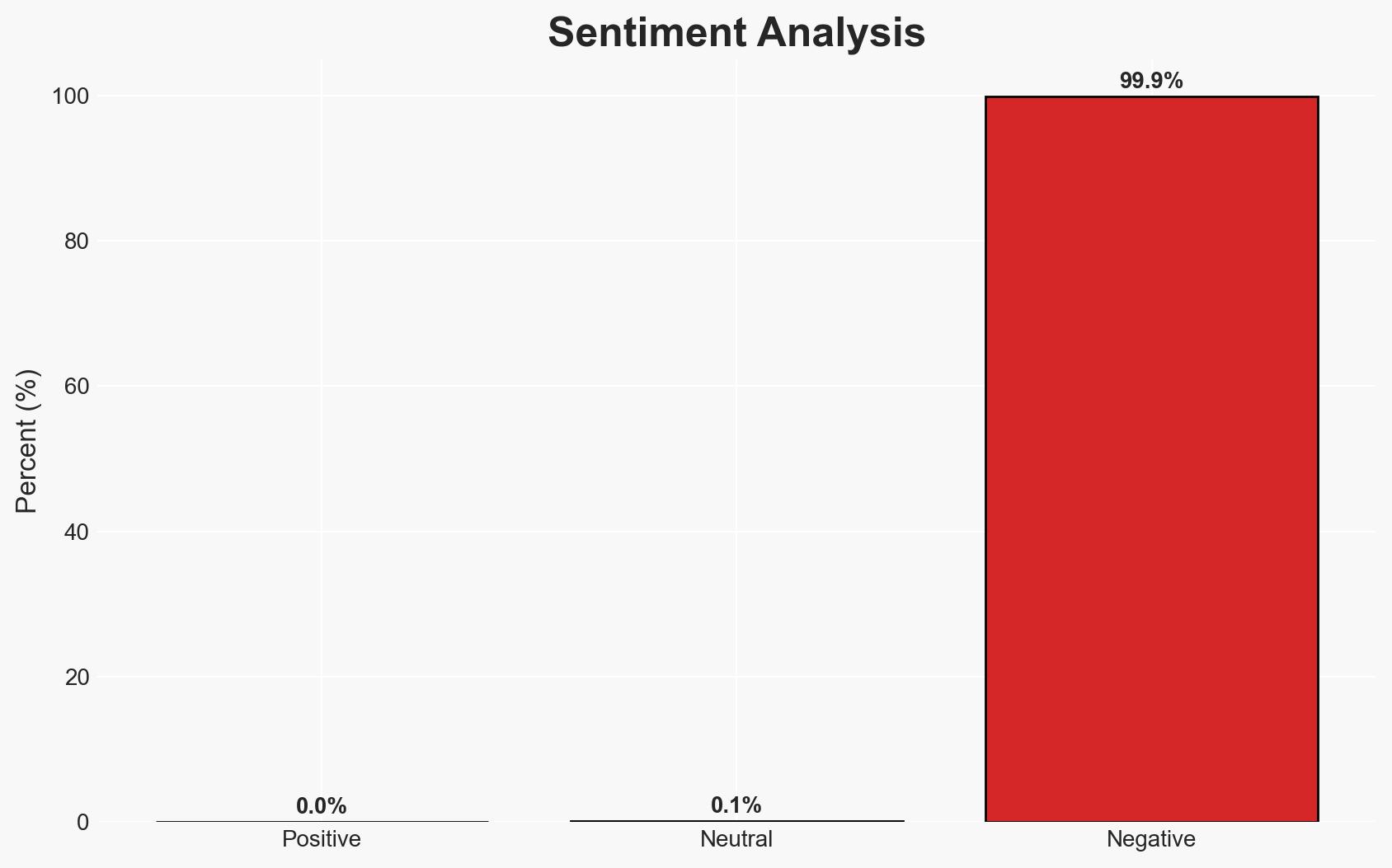
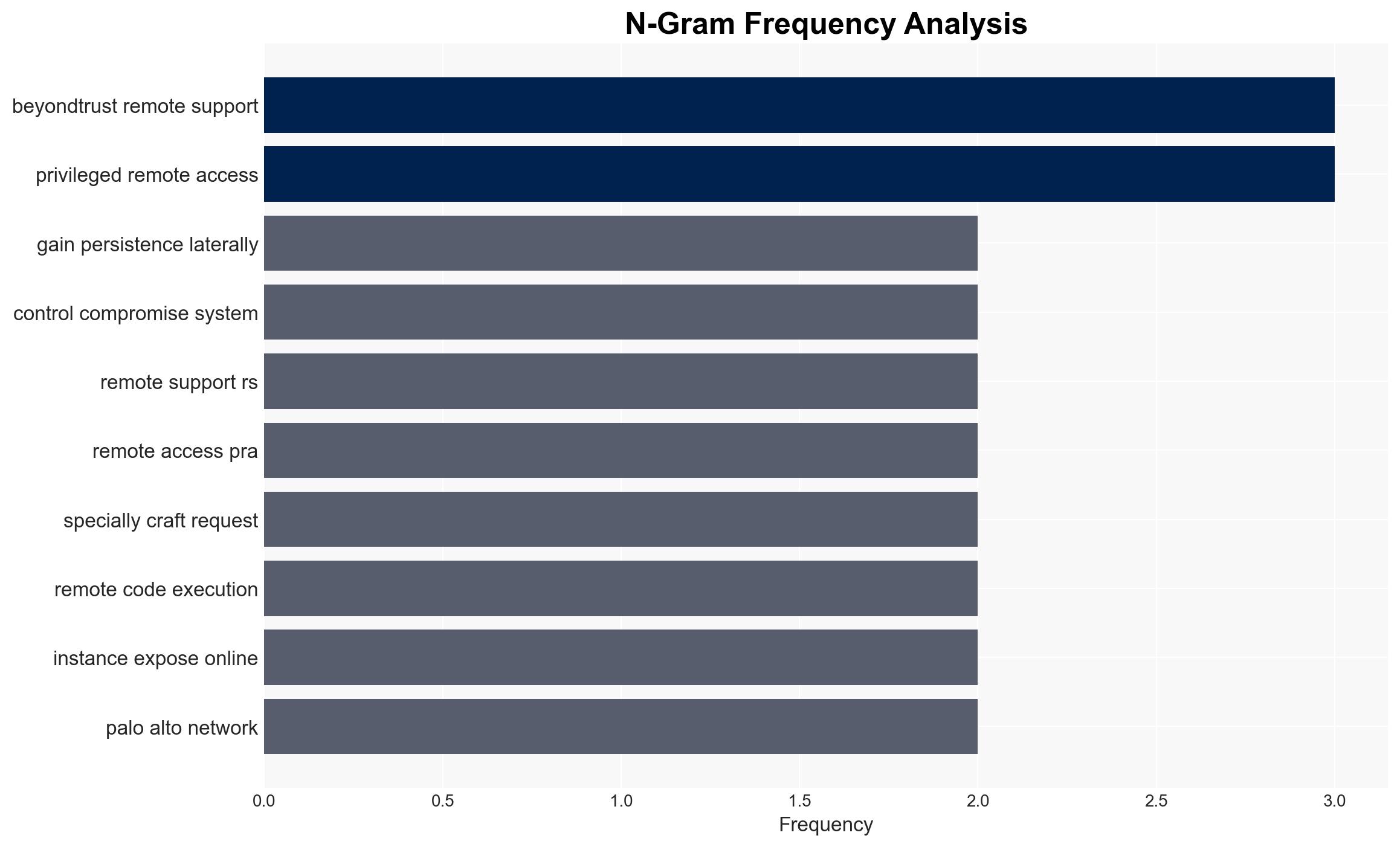
The exploitation of CVE-2026-1731 in BeyondTrust products poses a significant threat to organizations across multiple sectors, with active campaigns targeting systems globally. The most likely hypothesis is that threat actors are leveraging this vulnerability for broad cyber-espionage and data theft operations. This assessment is made with moderate confidence due to the rapid exploitation following the public release of a proof-of-concept exploit.
2. Competing Hypotheses
- Hypothesis A: Threat actors are exploiting CVE-2026-1731 primarily for cyber-espionage and data theft, supported by evidence of data exfiltration and lateral movement activities. However, the specific actors and their ultimate objectives remain unclear.
- Hypothesis B: The exploitation is primarily opportunistic, driven by cybercriminals seeking financial gain through ransomware or other monetization strategies. This is less supported due to the lack of reported ransom demands or financial motives in the observed activities.
- Assessment: Hypothesis A is currently better supported due to the nature of the activities observed, such as reconnaissance and data theft, which align more closely with espionage objectives. Indicators that could shift this judgment include evidence of financial transactions or ransom demands linked to the attacks.
3. Key Assumptions and Red Flags
- Assumptions: The vulnerability is being exploited by sophisticated threat actors; the patches released by BeyondTrust are effective if applied promptly; organizations are aware of the vulnerability and are taking steps to mitigate it.
- Information Gaps: Specific identities and affiliations of the threat actors exploiting the vulnerability; comprehensive data on the number of systems that have been patched since the release of the updates.
- Bias & Deception Risks: Potential bias in reporting from security vendors with vested interests; possibility of threat actors using false flags to mislead attribution efforts.
4. Implications and Strategic Risks
The continued exploitation of CVE-2026-1731 could lead to significant disruptions and data breaches, affecting critical infrastructure and sensitive sectors. The situation may evolve with increased sophistication in attack methods and broader targeting.
- Political / Geopolitical: Potential for diplomatic tensions if state-sponsored actors are involved, especially if critical national infrastructure is targeted.
- Security / Counter-Terrorism: Increased operational challenges for cybersecurity and intelligence agencies in defending against and attributing these attacks.
- Cyber / Information Space: Heightened risk of information operations leveraging stolen data to influence public opinion or disrupt organizational operations.
- Economic / Social: Potential economic impact from data breaches and service disruptions, particularly in sectors like healthcare and finance.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently apply patches to vulnerable systems; enhance monitoring for signs of exploitation; share threat intelligence with relevant stakeholders.
- Medium-Term Posture (1–12 months): Develop resilience measures including regular security audits and incident response planning; foster partnerships for intelligence sharing and collaborative defense.
- Scenario Outlook: Best: Rapid patch adoption mitigates threat; Worst: Widespread breaches and critical infrastructure impact; Most-Likely: Continued targeted attacks with gradual mitigation as patches are applied.
6. Key Individuals and Entities
- BeyondTrust (vendor of affected products)
- Hacktron AI (researchers who reported the exposure)
- Palo Alto Networks Unit 42 (reported on active exploitation)
- GreyNoise (detected initial attack attempts)
- Not clearly identifiable from open sources in this snippet for specific threat actors.
7. Thematic Tags
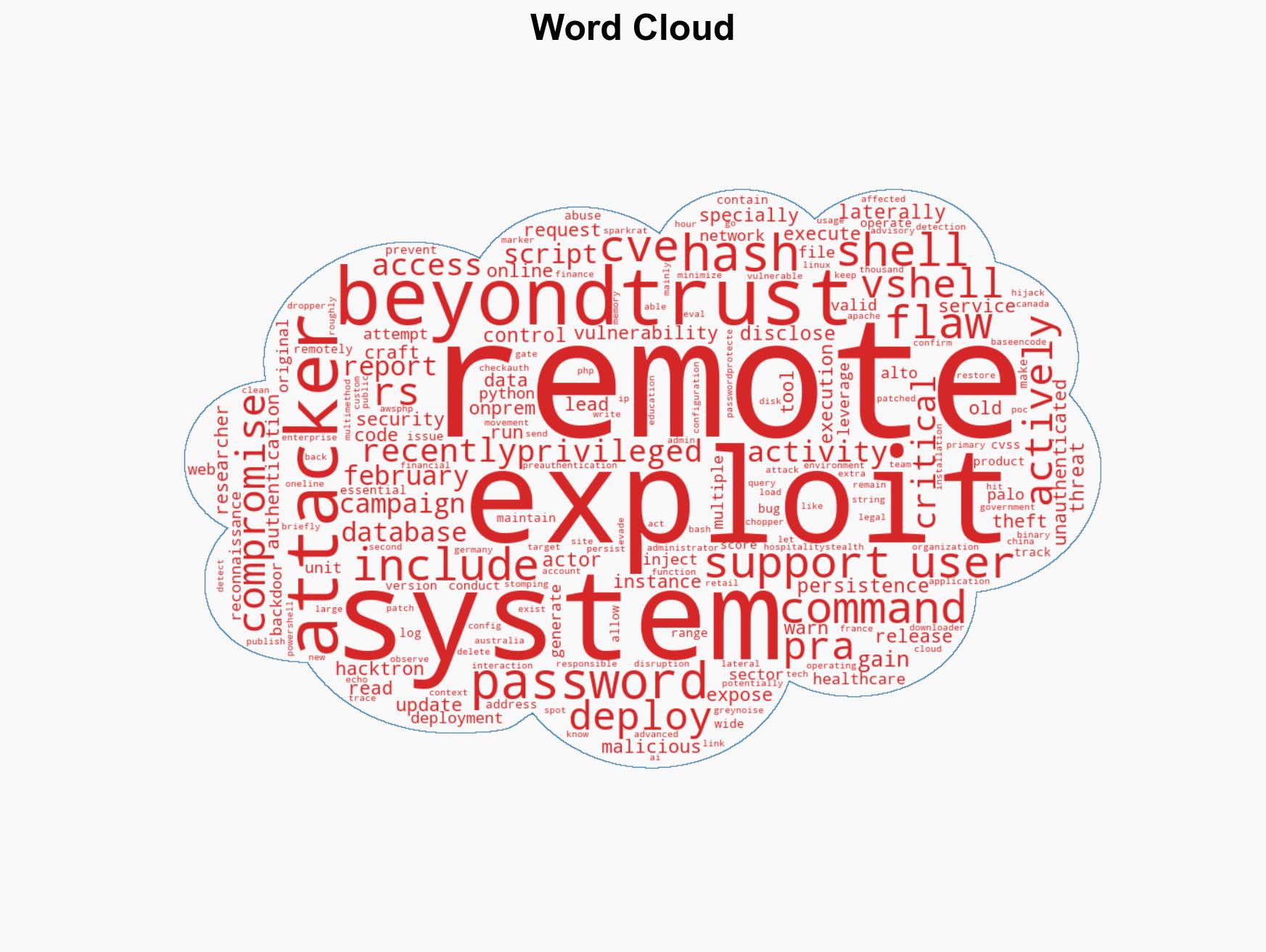
cybersecurity, remote code execution, data theft, vulnerability exploitation, cyber-espionage, threat intelligence, critical infrastructure
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us