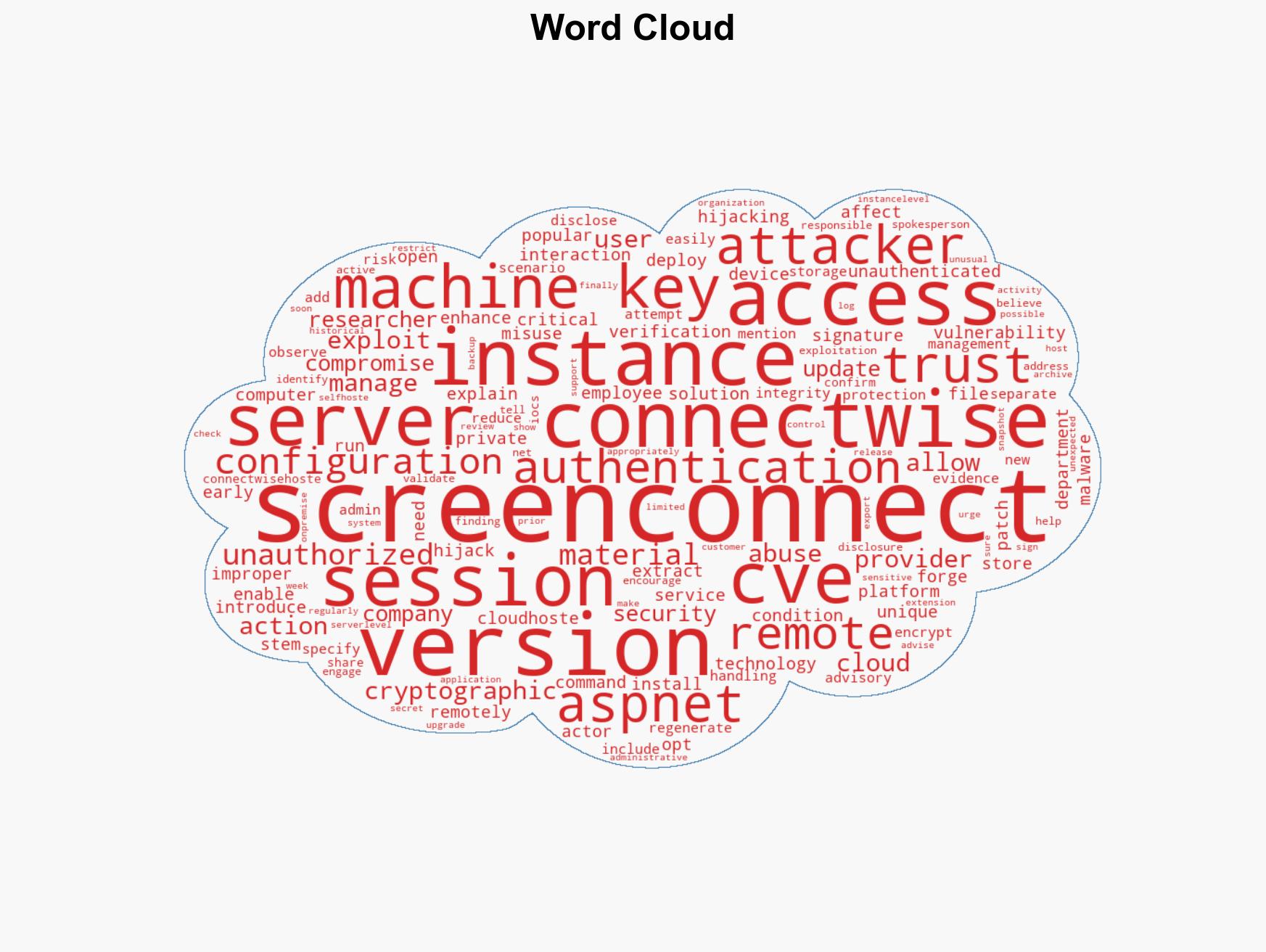
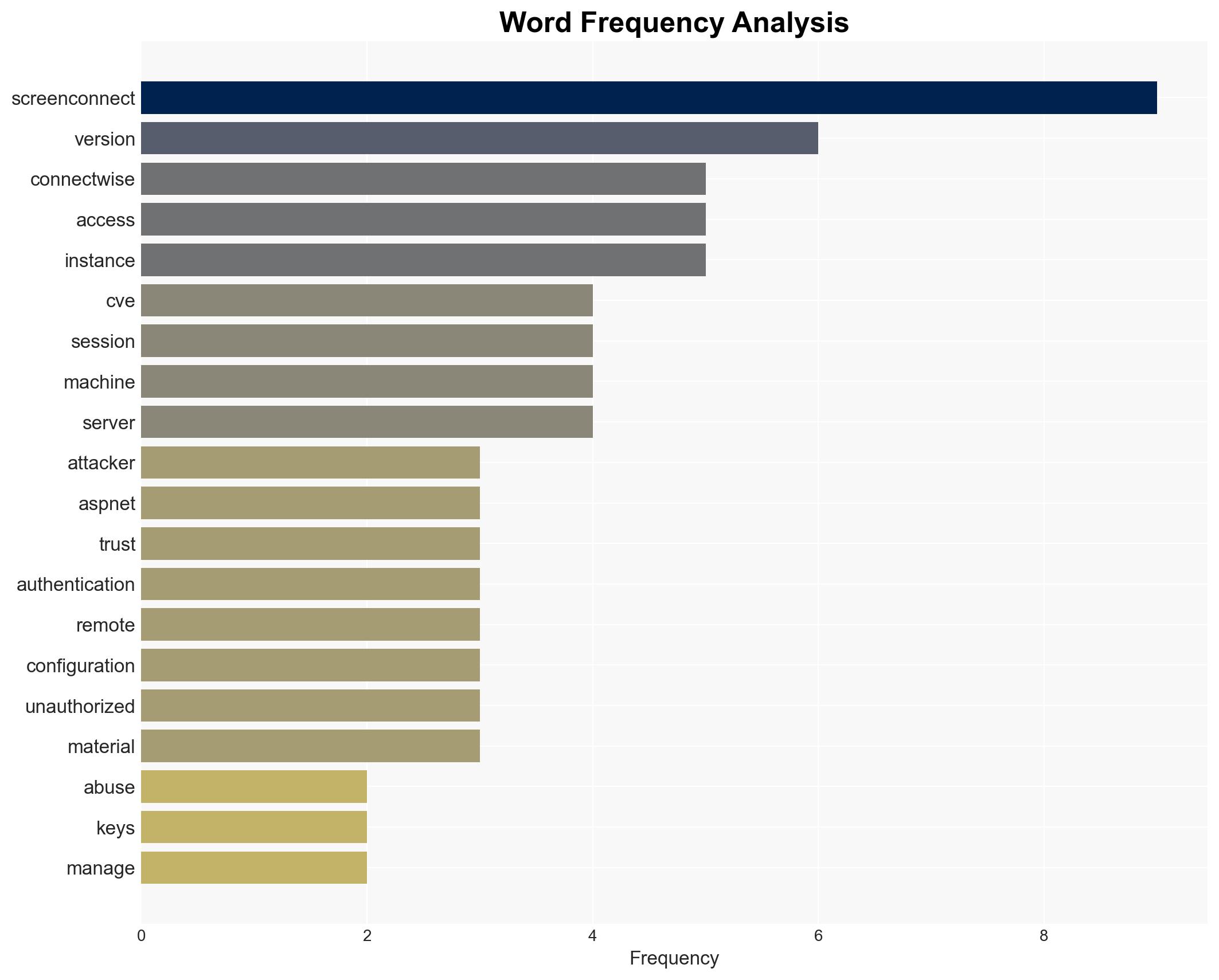
Critical vulnerability CVE-2026-3564 exposes ScreenConnect servers to remote session hijacking risks
Published on: 2026-03-20
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Unpatched ScreenConnect servers open to attack CVE-2026-3564
1. BLUF (Bottom Line Up Front)
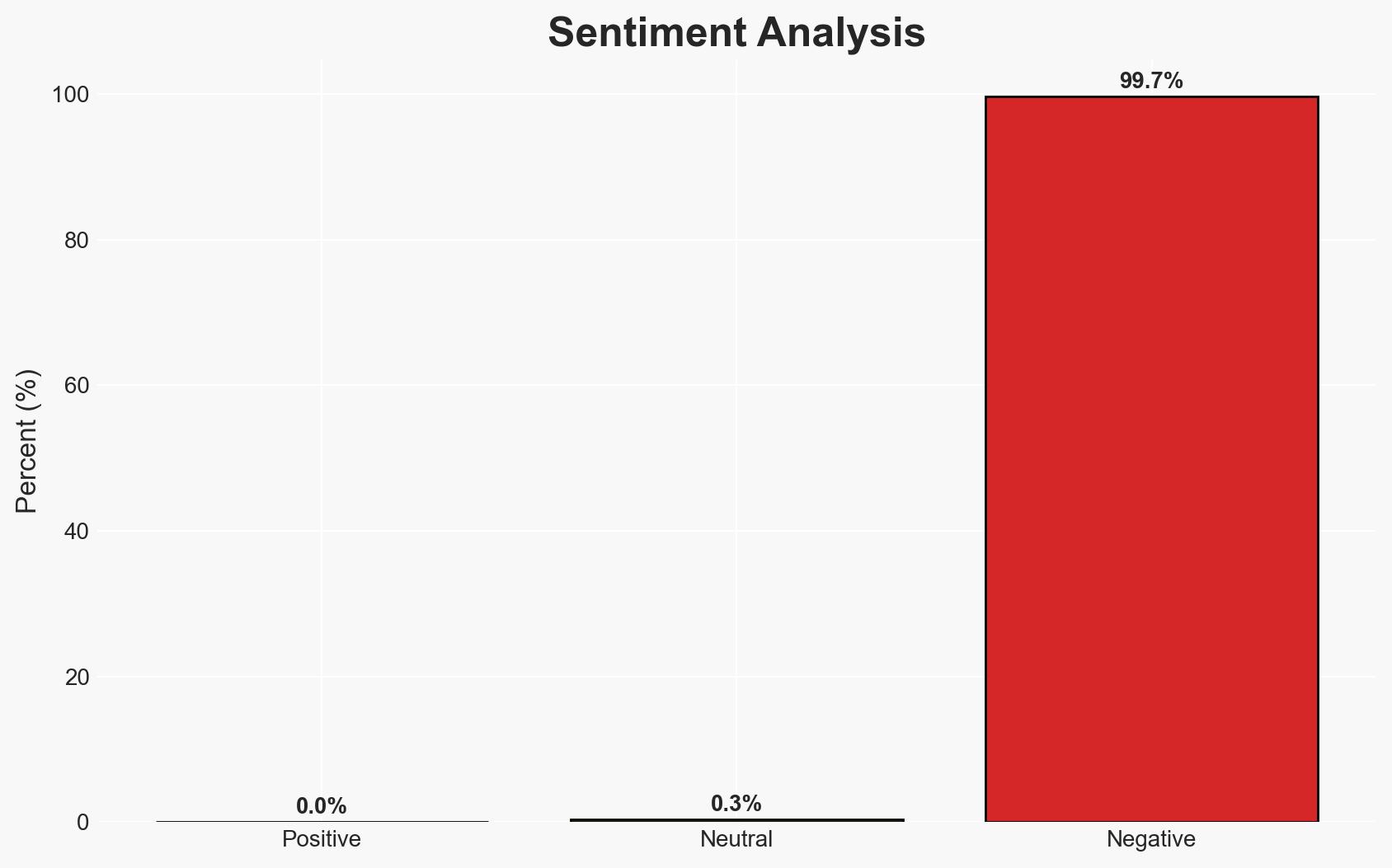
The critical vulnerability CVE-2026-3564 in ScreenConnect servers poses a significant risk of unauthorized access and control over remote sessions, affecting managed service providers and IT departments. The vulnerability, if exploited, could lead to widespread cyber intrusions. The most likely hypothesis is that attackers will target unpatched systems, leveraging the vulnerability for unauthorized access. Overall confidence in this judgment is moderate due to limited evidence of active exploitation.
2. Competing Hypotheses
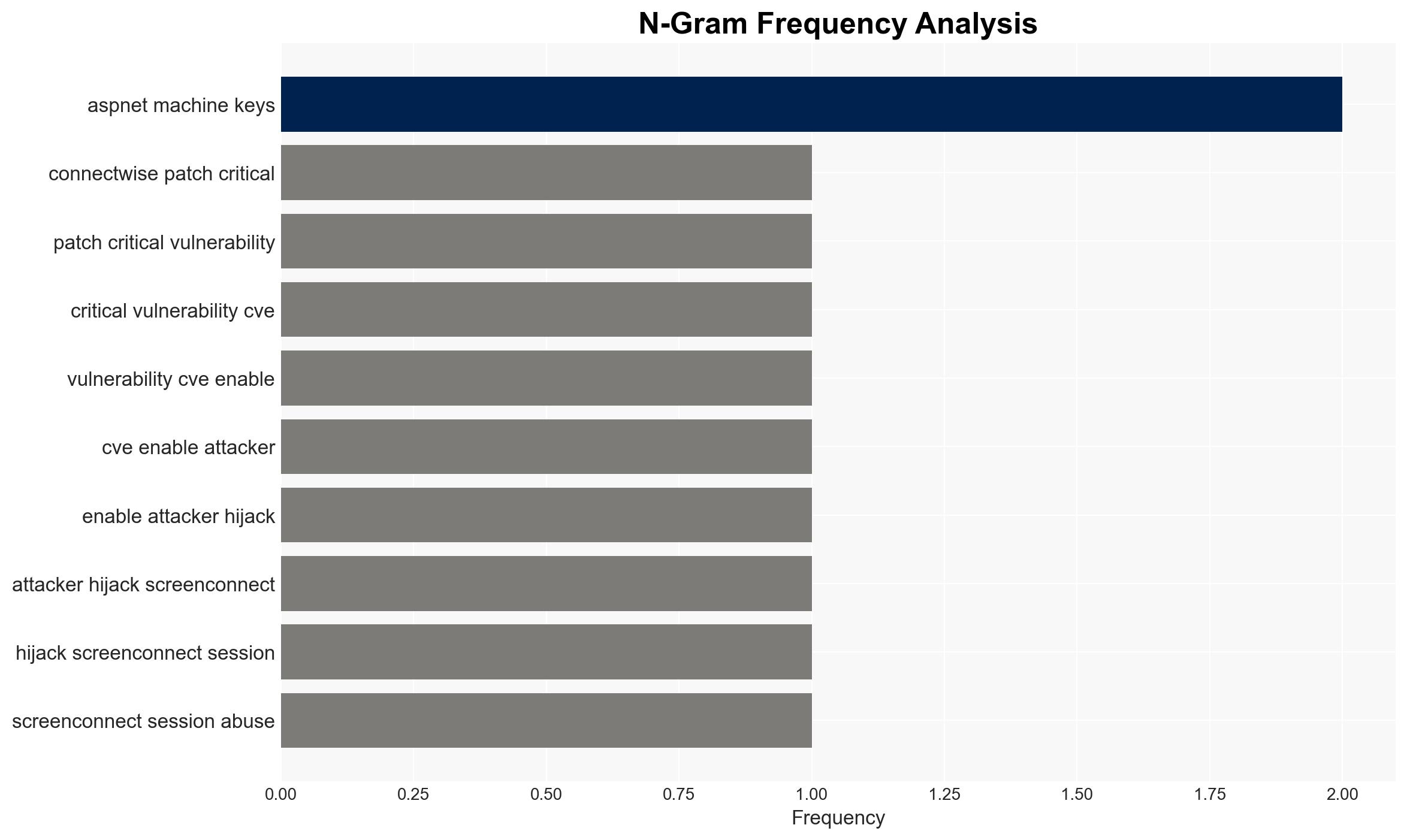
- Hypothesis A: Attackers will exploit CVE-2026-3564 to gain unauthorized access to unpatched ScreenConnect servers. This is supported by the vulnerability’s potential for remote exploitation without user interaction and the observed attempts to abuse ASP.NET machine key material. However, there is no confirmed evidence of exploitation in ConnectWise-hosted instances.
- Hypothesis B: The vulnerability will not be widely exploited due to rapid patch deployment and heightened awareness among users. This is supported by ConnectWise’s prompt release of a patched version and advisories urging immediate upgrades. The lack of confirmed Indicators of Compromise (IOCs) also suggests limited exploitation so far.
- Assessment: Hypothesis A is currently better supported due to the nature of the vulnerability and observed attempts to exploit it. Key indicators that could shift this judgment include confirmed reports of exploitation or widespread patch adoption.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will prioritize patching vulnerable systems; attackers have the capability to exploit the vulnerability; ConnectWise’s advisories are accurate and comprehensive.
- Information Gaps: Lack of detailed timelines for observed exploitation attempts; absence of specific IOCs; unclear scope of unpatched systems.
- Bias & Deception Risks: Potential underreporting of exploitation due to reputational concerns; reliance on vendor-provided information may introduce bias.
4. Implications and Strategic Risks
The exploitation of CVE-2026-3564 could lead to significant disruptions in IT operations and potential data breaches. This development may influence broader cybersecurity practices and policies.
- Political / Geopolitical: Escalation in cyber tensions if state-sponsored actors exploit the vulnerability.
- Security / Counter-Terrorism: Increased risk of cyber-attacks on critical infrastructure managed via ScreenConnect.
- Cyber / Information Space: Potential for increased cyber espionage and data theft activities.
- Economic / Social: Financial losses for affected organizations and potential erosion of trust in remote access solutions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently patch all vulnerable ScreenConnect instances; monitor for unusual authentication activity; engage in threat intelligence sharing.
- Medium-Term Posture (1–12 months): Enhance cybersecurity training for IT staff; develop incident response plans; strengthen partnerships with cybersecurity firms.
- Scenario Outlook:
- Best: Rapid patch adoption mitigates risk, and no significant exploitation occurs.
- Worst: Widespread exploitation leads to major data breaches and operational disruptions.
- Most-Likely: Sporadic exploitation incidents occur, prompting increased security measures and awareness.
6. Key Individuals and Entities
- ConnectWise (vendor of ScreenConnect)
- Managed service providers and IT departments using ScreenConnect
- Security researchers observing exploitation attempts
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, vulnerability management, remote access, IT infrastructure, cyber-espionage, threat intelligence, patch management
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us