Cross-device clipboard revolutionizes workflow, making it indispensable for multitasking users.
Published on: 2025-11-28
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Once you try cross-device clipboard theres no going back
1. BLUF (Bottom Line Up Front)
The cross-device clipboard technology, while enhancing productivity through seamless data transfer across devices, presents potential security vulnerabilities and privacy concerns. The most likely hypothesis is that this technology will see widespread adoption due to its convenience, despite these risks. This assessment is made with moderate confidence, considering the current technological trends and user behavior patterns.
2. Competing Hypotheses
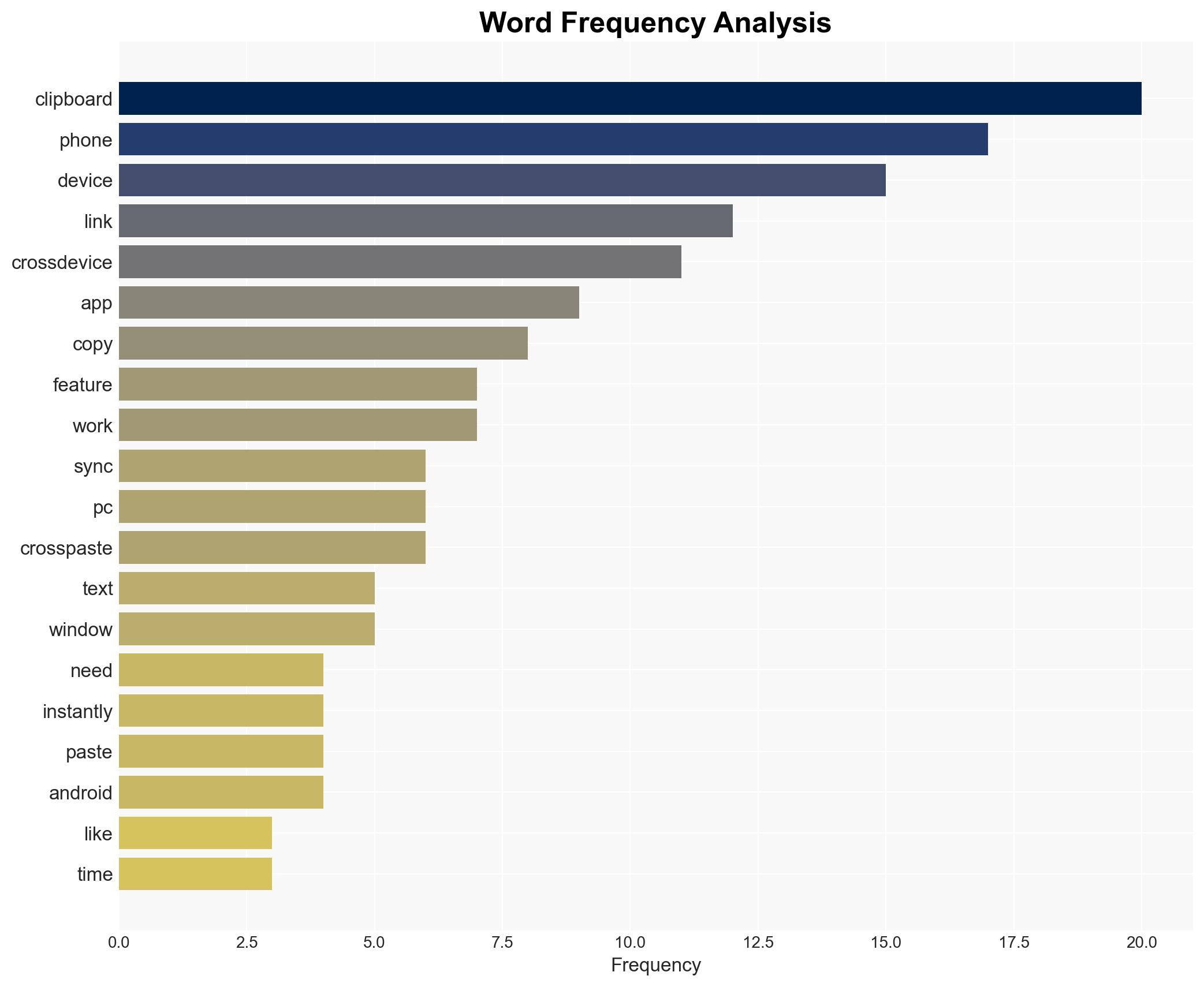
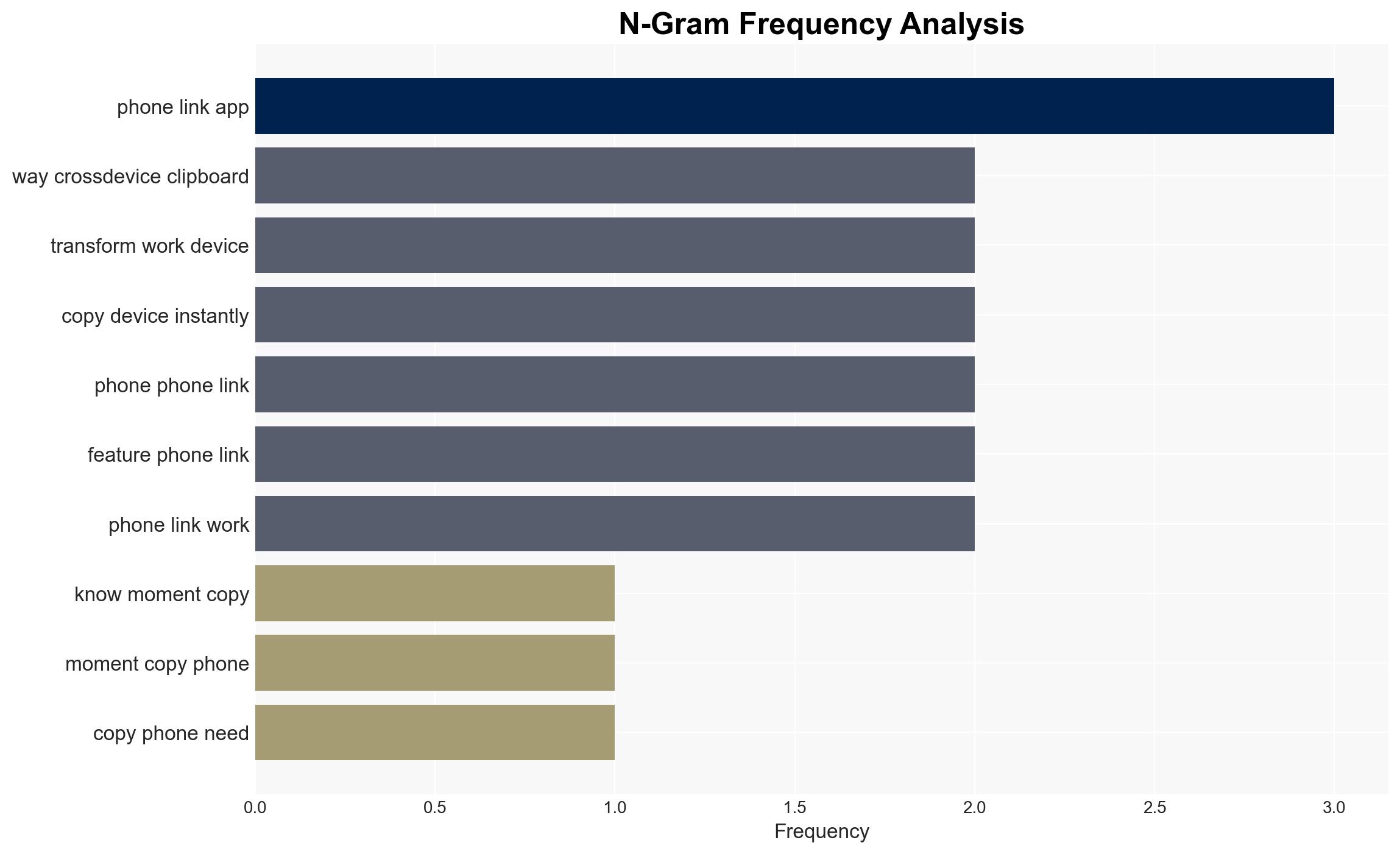
- Hypothesis A: Cross-device clipboard technology will become a standard feature across all major operating systems, driven by user demand for convenience and productivity. Supporting evidence includes the integration of such features in major platforms like Microsoft’s ecosystem. However, uncertainties remain regarding the full extent of security measures implemented.
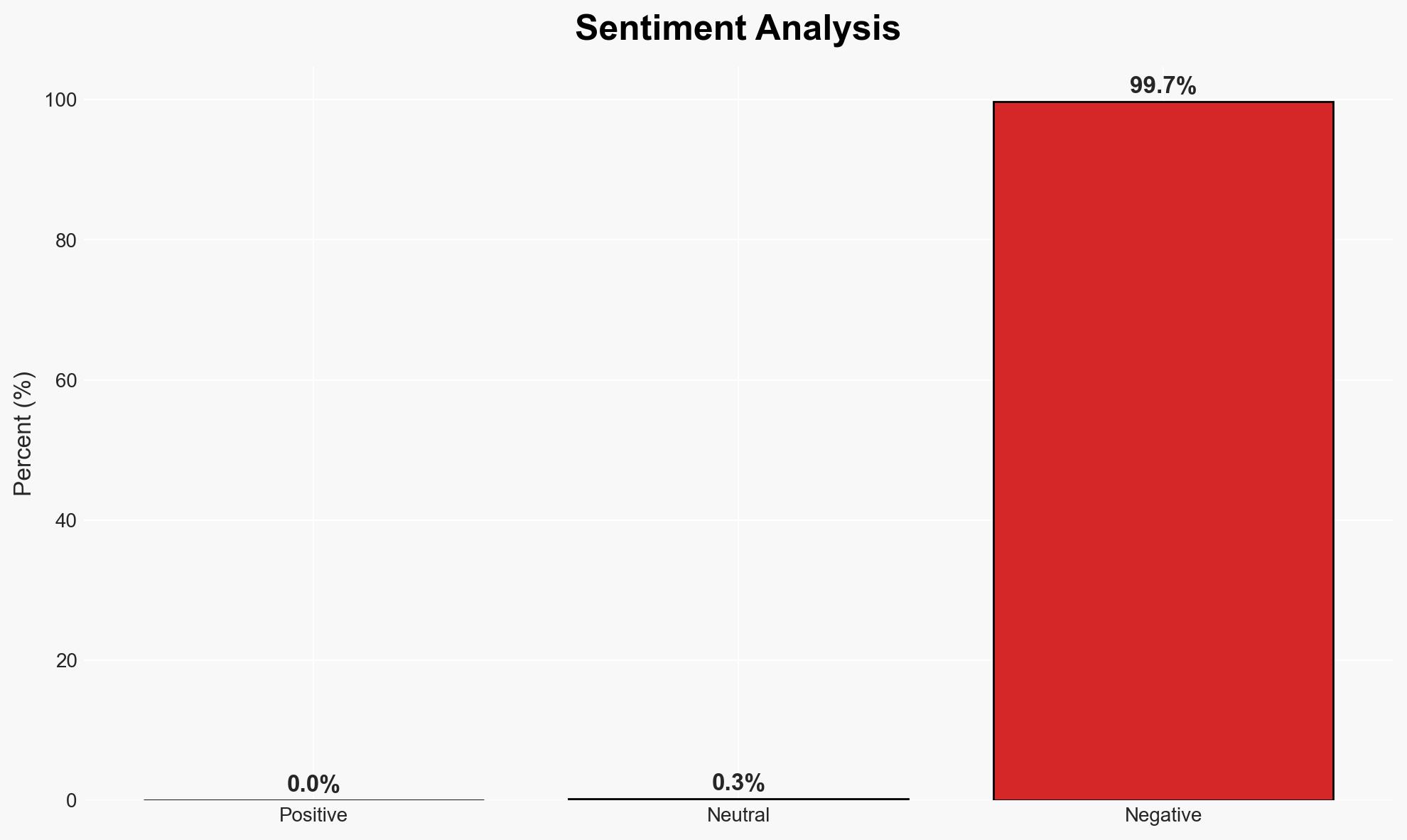
- Hypothesis B: Security and privacy concerns will hinder the widespread adoption of cross-device clipboard technology. While there are privacy-first solutions like CrossPaste, the general user base may not prioritize these concerns over convenience. Contradicting evidence includes the lack of widespread public awareness and understanding of the potential risks.
- Assessment: Hypothesis A is currently better supported due to the observed trend of increasing integration of cross-device features by major tech companies, indicating a market-driven push towards adoption. Indicators that could shift this judgment include major security breaches or regulatory actions addressing privacy concerns.
3. Key Assumptions and Red Flags
- Assumptions: Users prioritize convenience over security; Major tech companies will continue to enhance security features; Cross-device clipboard technology will remain free or low-cost.
- Information Gaps: Detailed security protocols of cross-device clipboard technologies; User adoption rates and satisfaction metrics; Regulatory stances on data privacy in this context.
- Bias & Deception Risks: Potential bias from tech companies promoting convenience over security; Lack of user awareness may lead to underestimation of risks; Marketing materials may downplay security vulnerabilities.
4. Implications and Strategic Risks
The adoption of cross-device clipboard technology could significantly impact data handling and security protocols across industries. Its evolution will likely influence user expectations and regulatory frameworks.
- Political / Geopolitical: Potential for increased scrutiny and regulation concerning data privacy and cross-border data flows.
- Security / Counter-Terrorism: New attack vectors could emerge, exploiting clipboard synchronization for data exfiltration or malware distribution.
- Cyber / Information Space: Increased risk of cyber espionage and data breaches; potential for misinformation if clipboard data is intercepted or altered.
- Economic / Social: Enhanced productivity could drive economic efficiencies; however, privacy breaches could lead to social distrust in technology.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor developments in cross-device clipboard technology; assess security protocols of major providers; educate users on potential risks.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies to enhance security measures; advocate for regulatory frameworks that protect user data.
- Scenario Outlook:
- Best: Secure and privacy-compliant cross-device clipboard technology becomes standard, enhancing productivity.
- Worst: Major security breaches lead to loss of user trust and regulatory crackdowns.
- Most-Likely: Gradual adoption with incremental improvements in security, driven by user demand and regulatory pressure.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
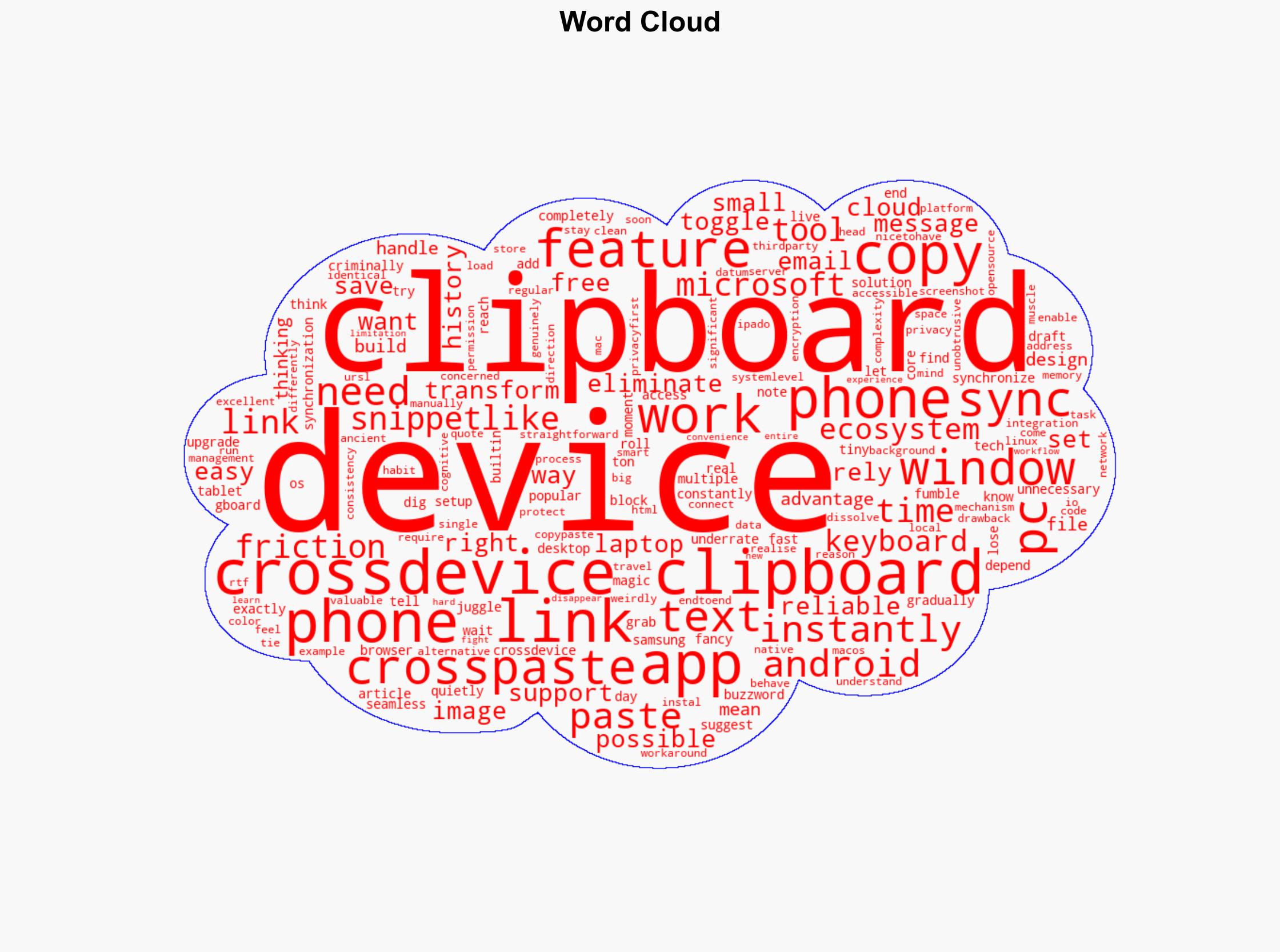
Cybersecurity, cross-device technology, data privacy, productivity tools, user behavior, regulatory impact, technological adoption
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us