CrowdStrike Reports Nearly Double Increase in AI-Driven Cyber Attacks Over Past Year
Published on: 2026-02-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: AI-powered Cyber-Attacks Up Significantly in the Last Year Warns CrowdStrike
1. BLUF (Bottom Line Up Front)
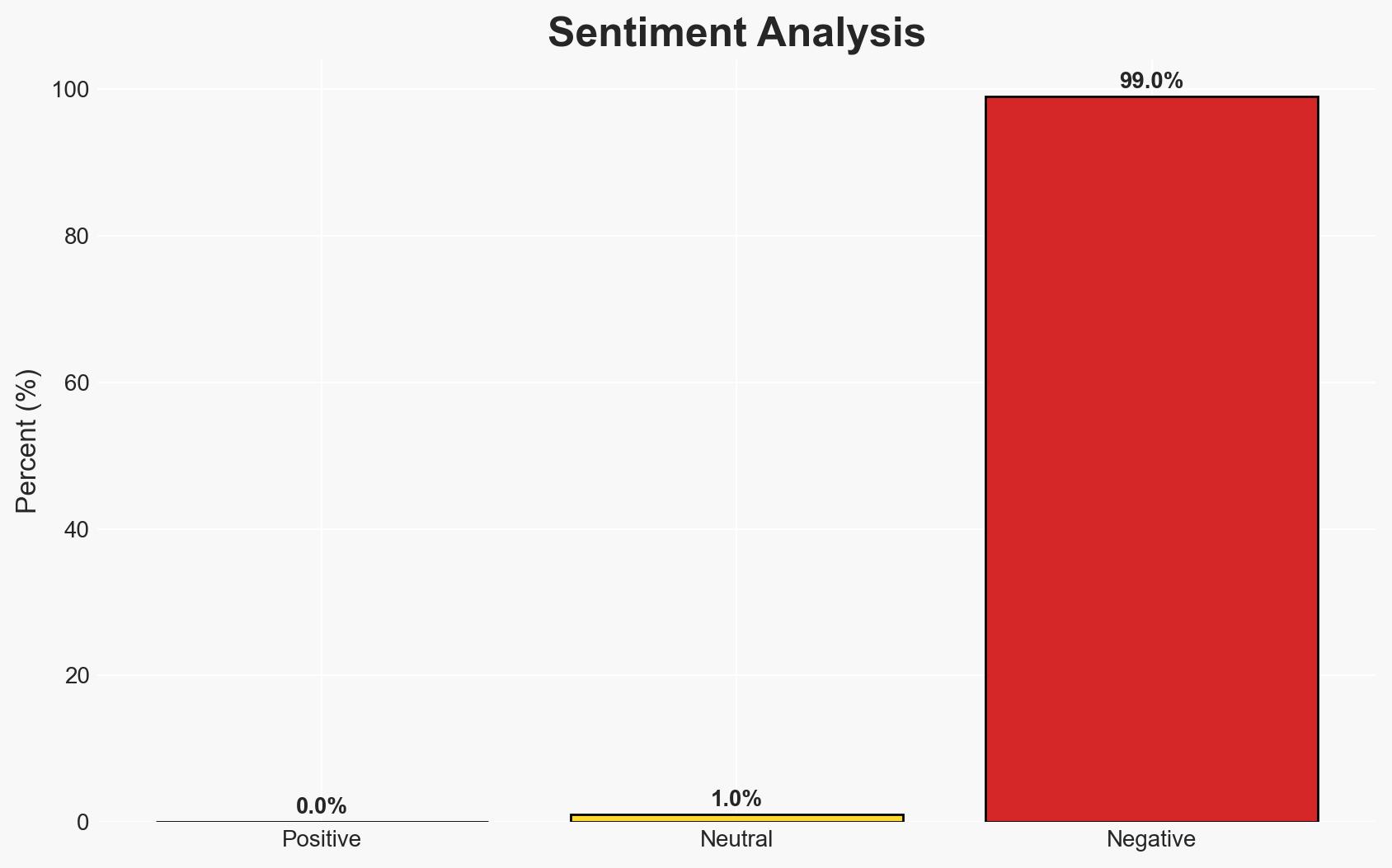
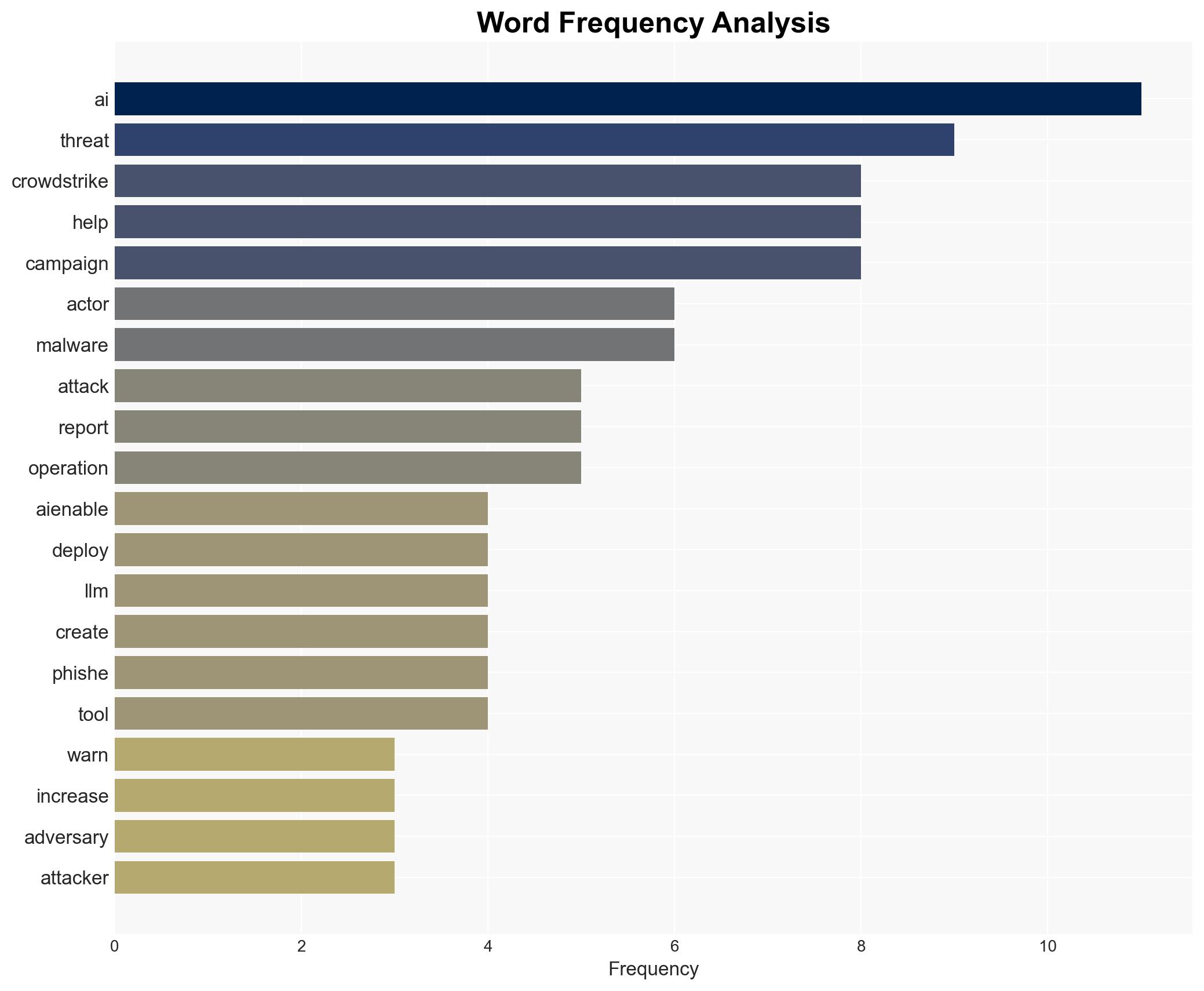
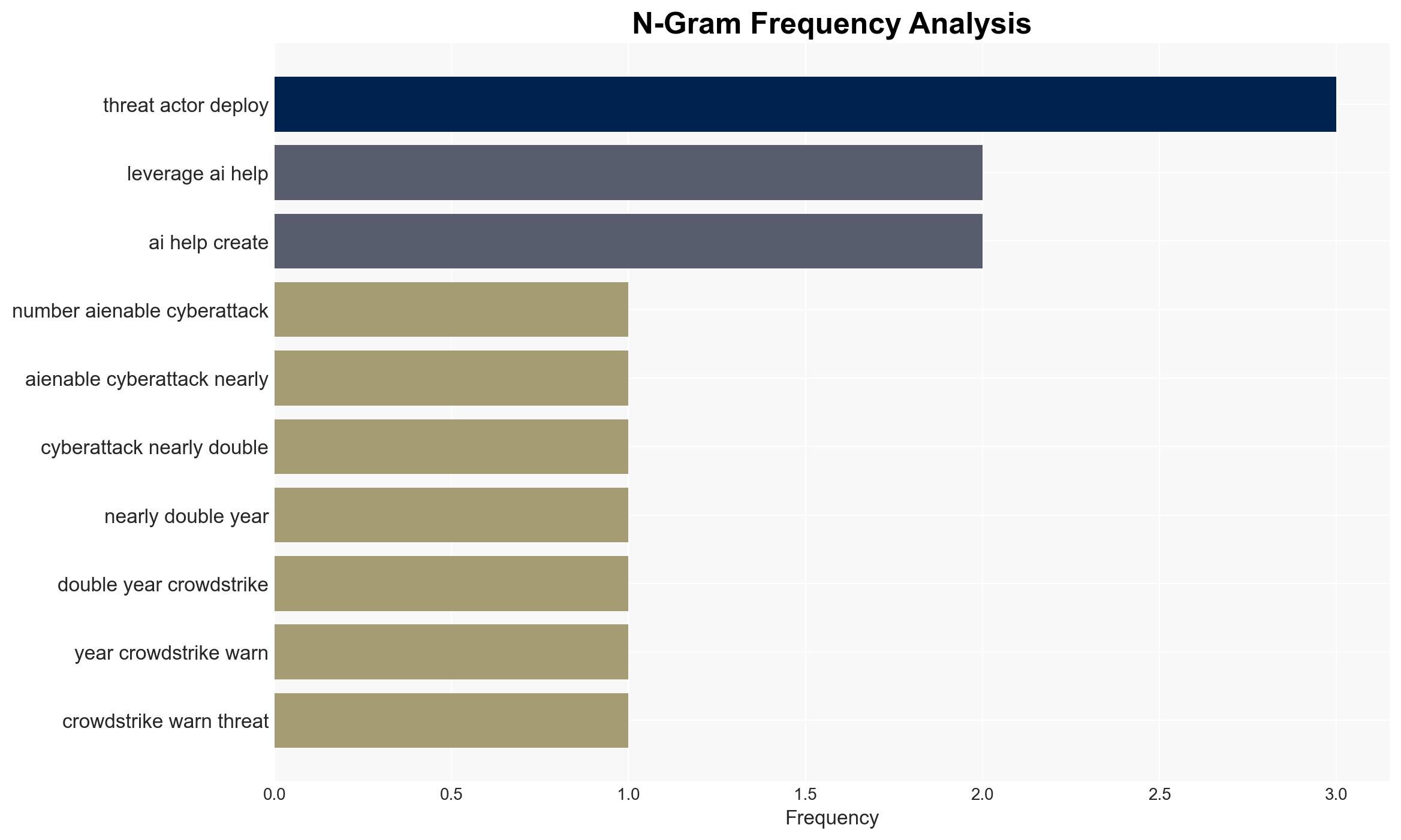
The use of AI in cyber-attacks has increased significantly, with an 89% rise in AI-enabled attacks in 2025 compared to the previous year. This trend is primarily driven by the optimization of existing attack methods rather than the creation of new ones. The primary targets include government entities and individuals, with moderate confidence in the assessment due to existing information gaps.
2. Competing Hypotheses
- Hypothesis A: The increase in AI-enabled attacks is primarily due to the enhanced capabilities of threat actors using AI to optimize existing methods. Supporting evidence includes the use of LLMs for phishing and malware development. However, the lack of novel attack vectors suggests limitations in AI’s current application.
- Hypothesis B: The rise in AI-enabled attacks is overstated, with traditional methods still dominating the threat landscape. This is contradicted by the reported 89% increase and specific campaigns leveraging AI, though the effectiveness of AI in these attacks remains questionable.
- Assessment: Hypothesis A is currently better supported due to documented cases of AI usage in optimizing attacks. Indicators such as increased sophistication in phishing and malware could further validate this hypothesis.
3. Key Assumptions and Red Flags
- Assumptions: AI will continue to be used primarily for optimizing existing attack methods; AI capabilities will not rapidly advance to create novel attack vectors; threat actors will have consistent access to AI technologies.
- Information Gaps: Detailed data on the effectiveness of AI-optimized attacks compared to traditional methods; specifics on the extent of AI integration in various threat actor operations.
- Bias & Deception Risks: Potential over-reliance on vendor reports; risk of threat actors exaggerating AI capabilities to mislead adversaries.
4. Implications and Strategic Risks
The integration of AI in cyber-attacks is likely to evolve, impacting various domains. The optimization of attack methods could lead to more frequent and sophisticated threats, challenging existing defense mechanisms.
- Political / Geopolitical: Escalation in cyber tensions, particularly involving state actors like China and Russia, could strain international relations.
- Security / Counter-Terrorism: Increased threat to national security infrastructure and personnel, necessitating enhanced cyber defense strategies.
- Cyber / Information Space: Greater complexity in cyber defense due to AI-enhanced phishing and malware, requiring advanced detection and response capabilities.
- Economic / Social: Potential economic disruptions from successful cyber-attacks, impacting public trust in digital systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of AI-related cyber threats; increase collaboration with cybersecurity firms for threat intelligence sharing.
- Medium-Term Posture (1–12 months): Develop AI-based defensive capabilities; invest in training for cybersecurity personnel to counter AI-enhanced threats.
- Scenario Outlook:
- Best: Successful adaptation to AI threats, minimizing impact.
- Worst: Significant breaches due to AI-optimized attacks, leading to major disruptions.
- Most-Likely: Gradual increase in AI-related incidents, with moderate disruptions.
6. Key Individuals and Entities
- Chinese intelligence service
- Renaissance Spider (Russian-based cyber-criminal operation)
- Fancy Bear (Russian state-backed hacking group)
- Adam Meyers (Head of counter adversary operations at CrowdStrike)
7. Thematic Tags
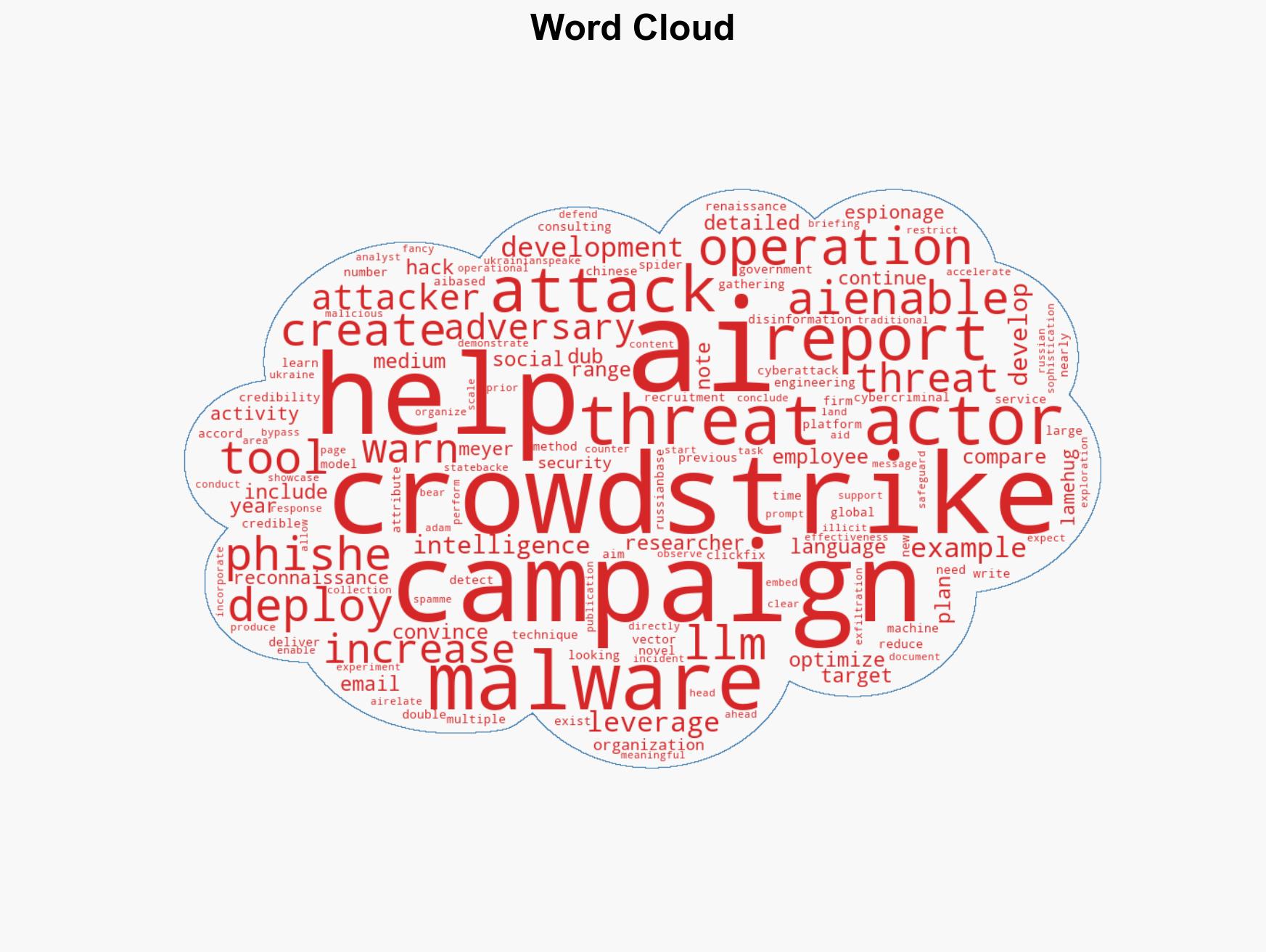
cybersecurity, AI in cyber-attacks, phishing, malware development, state-sponsored cyber operations, threat intelligence, cyber defense
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us