CrushFTP Vulnerability Exploited Following Disclosure Issues – Infosecurity Magazine
Published on: 2025-04-03
Intelligence Report: CrushFTP Vulnerability Exploited Following Disclosure Issues – Infosecurity Magazine
1. BLUF (Bottom Line Up Front)
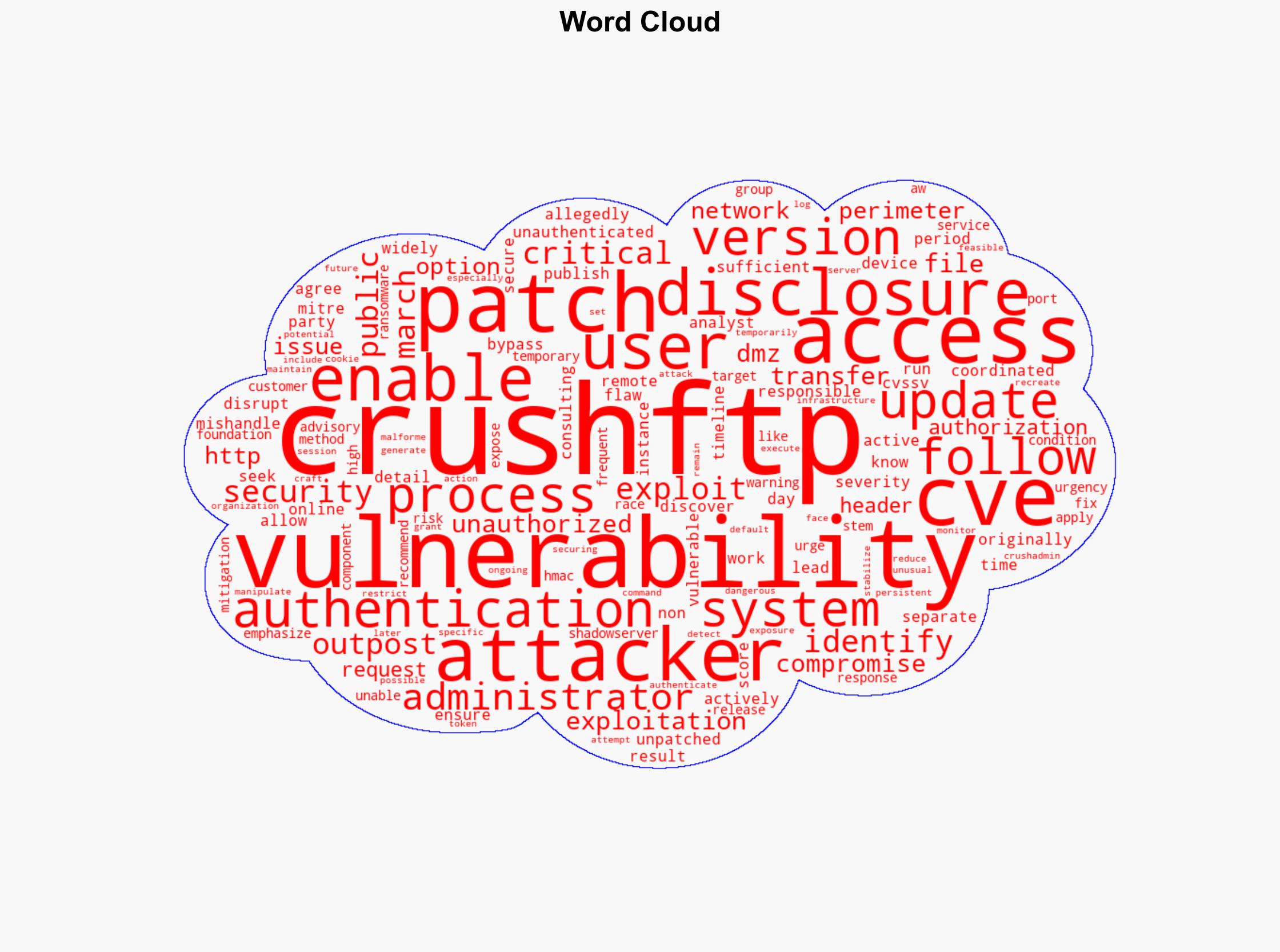
A critical authentication bypass vulnerability in CrushFTP has been actively exploited following a mishandled disclosure process. This flaw allows remote attackers to gain unauthorized access to systems running unpatched versions of CrushFTP. The vulnerability, identified as CVE, poses a high risk due to its potential for exploitation by ransomware groups. Immediate patching and security measures are recommended to mitigate risks.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
The vulnerability in CrushFTP was discovered by security analysts at Outpost, who initially followed a responsible disclosure timeline. However, the process was disrupted when a separate party allegedly published a different CVE, leading to widespread knowledge of the vulnerability. This has resulted in active exploitation, with vulnerable instances identified online by the Shadowserver Foundation. The vulnerability stems from issues in the AW HMAC authentication method within CrushFTP’s HTTP component, allowing attackers to exploit a race condition for unauthorized access.
3. Implications and Strategic Risks
The exploitation of this vulnerability poses significant risks to organizations using CrushFTP, particularly those with exposed ports. The potential for ransomware attacks is high, threatening data integrity and operational continuity. National security could be impacted if critical infrastructure relies on vulnerable systems. Economic interests are also at risk due to potential data breaches and service disruptions.
4. Recommendations and Outlook
Recommendations:
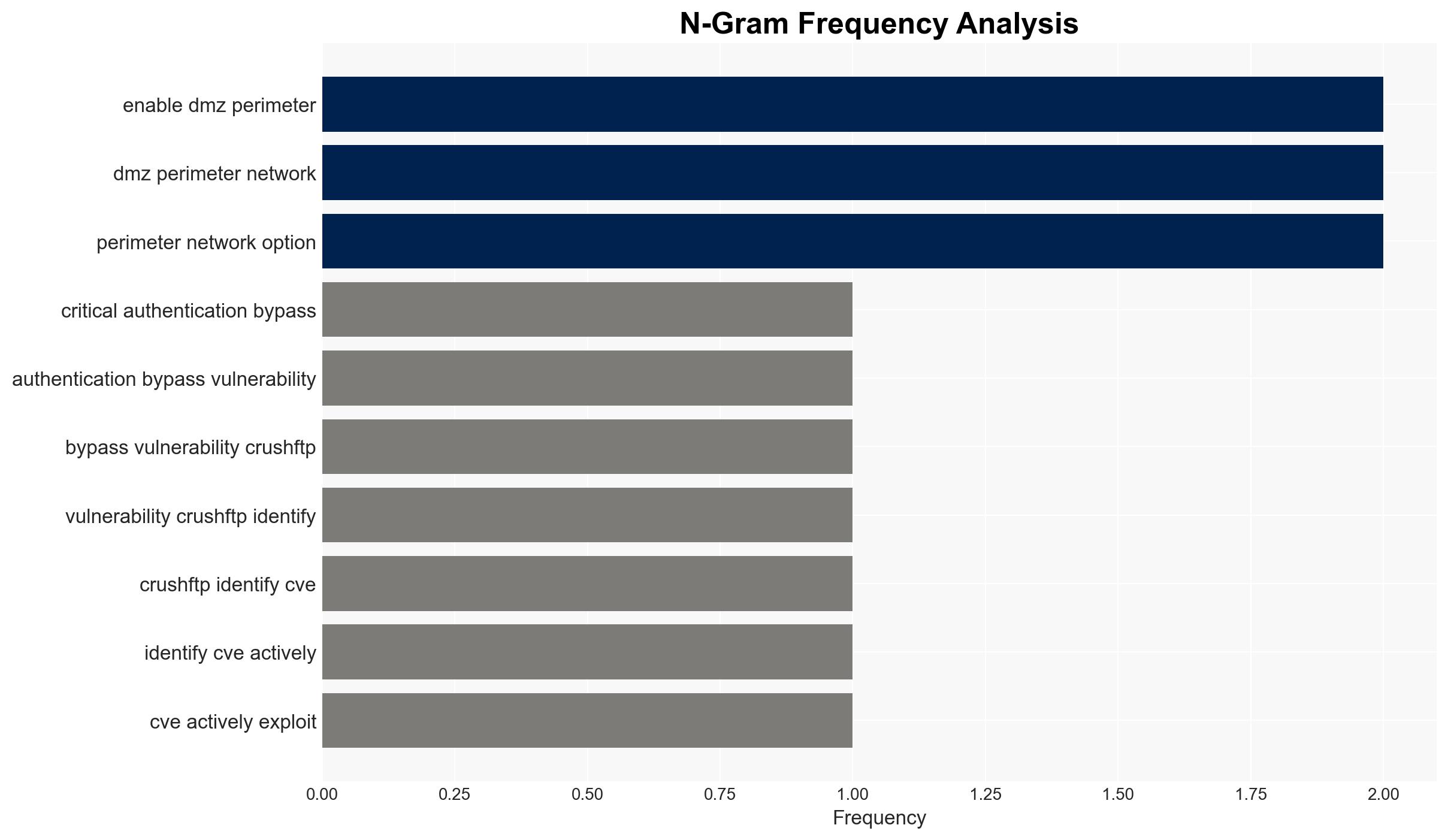
- Update CrushFTP to the latest version to patch the vulnerability immediately.
- Enable the DMZ perimeter network option as a temporary mitigation if patching is not feasible.
- Monitor system logs for unusual authentication attempts to detect potential compromises.
- Restrict public-facing access to CrushFTP servers to reduce exposure.
Outlook:
In the best-case scenario, rapid patch adoption will mitigate the vulnerability’s impact. In the worst-case scenario, continued exploitation could lead to significant data breaches and operational disruptions. The most likely outcome involves a moderate level of exploitation until patches are widely implemented.
5. Key Individuals and Entities
The report mentions significant individuals and organizations, including Outpost, Shadowserver Foundation, and CrushFTP. These entities play critical roles in the discovery, analysis, and mitigation of the vulnerability.