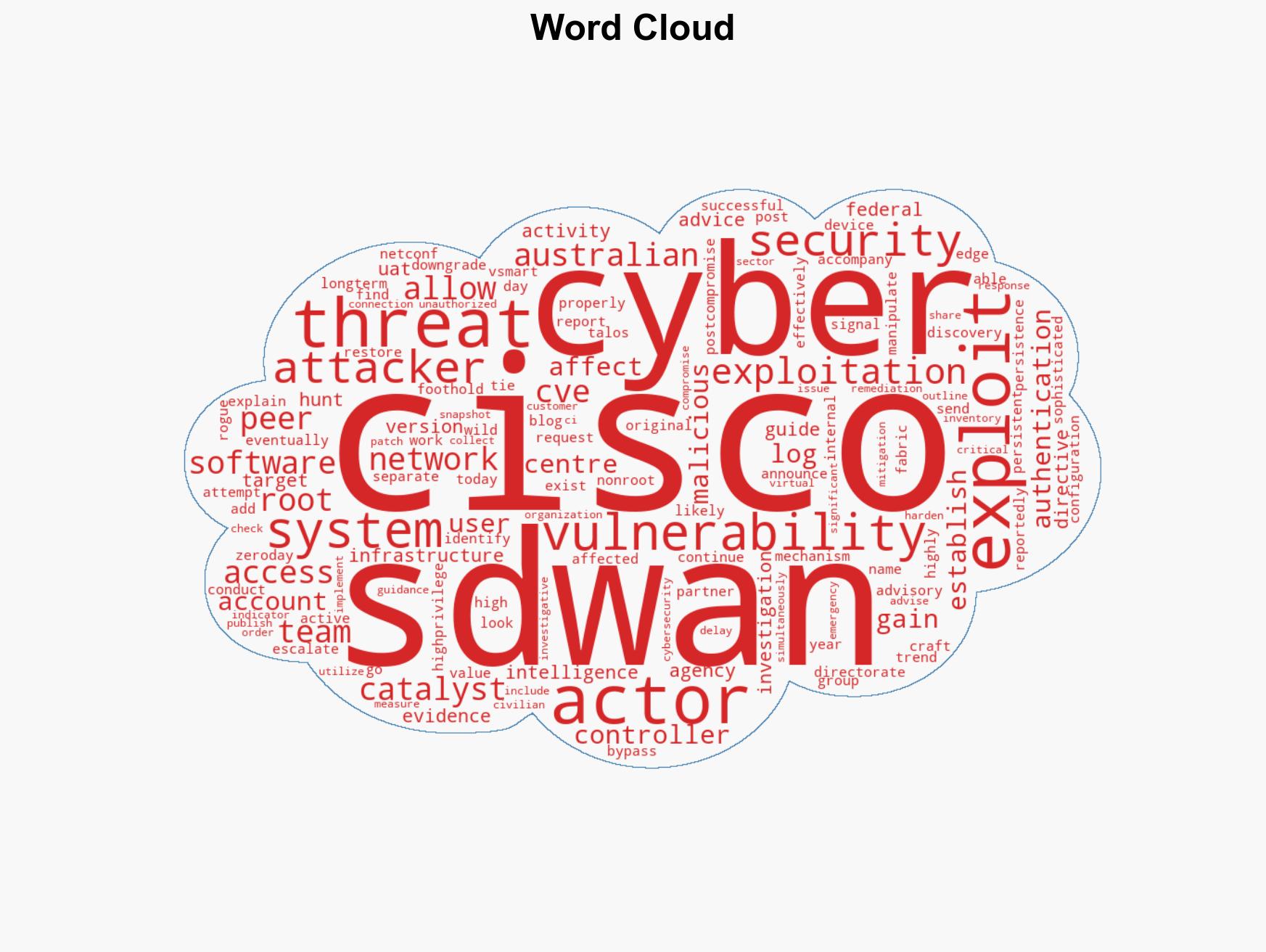
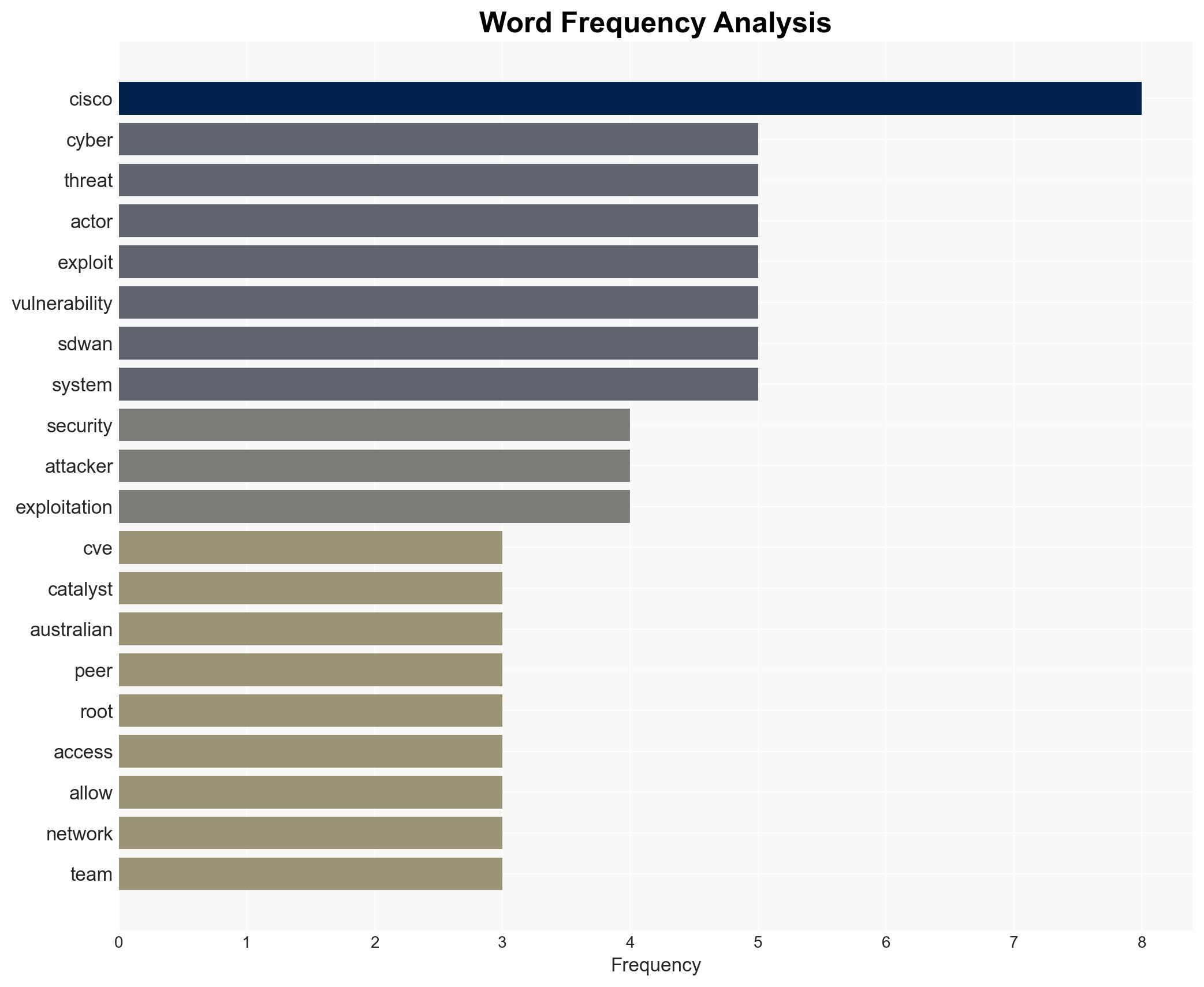
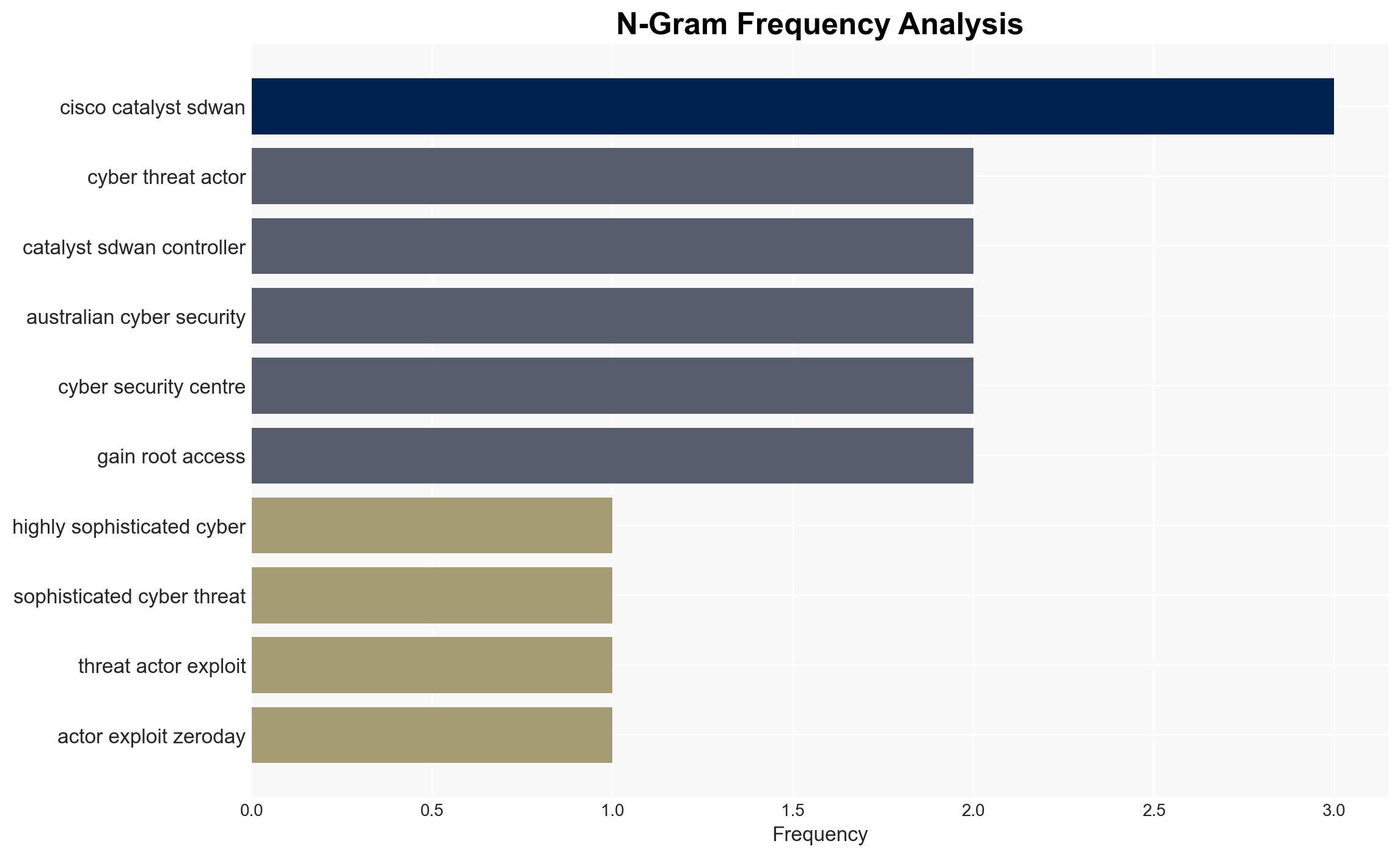
Cyber Threat Actor Exploits Cisco SD-WAN Zero-Day Vulnerability CVE-2026-20127 for Root Access
Published on: 2026-02-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Threat actor leveraged Cisco SD-WAN zero-day since 2023 CVE-2026-20127
1. BLUF (Bottom Line Up Front)
A sophisticated cyber threat actor, identified as UAT-8616, has been exploiting a zero-day vulnerability (CVE-2026-20127) in Cisco SD-WAN systems since 2023, targeting high-value organizations including critical infrastructure sectors. The exploitation allows attackers to gain root access and establish persistence. The overall confidence in this assessment is moderate due to identified information gaps and potential biases in source reporting.
2. Competing Hypotheses
- Hypothesis A: UAT-8616 is a state-sponsored group targeting critical infrastructure for strategic advantage. This is supported by the sophistication of the attack and the targeting of high-value sectors. However, there is uncertainty about the exact state affiliation and objectives.
- Hypothesis B: UAT-8616 is an independent cybercriminal group motivated by financial gain, exploiting vulnerabilities for ransom or data theft. This is contradicted by the lack of immediate financial demands and the strategic nature of the targets.
- Assessment: Hypothesis A is currently better supported due to the complexity of the attack and the strategic targeting of critical infrastructure, which aligns more closely with state-sponsored objectives. Further intelligence on the group’s motivations and affiliations could shift this assessment.
3. Key Assumptions and Red Flags
- Assumptions: The threat actor has the technical capability to exploit zero-day vulnerabilities; the targeting of critical infrastructure indicates strategic intent; the reported timeline of exploitation is accurate.
- Information Gaps: Specific state affiliation of UAT-8616; detailed motivations and objectives of the group; full scope of affected organizations and sectors.
- Bias & Deception Risks: Potential bias in source reporting from Cisco and associated intelligence partners; risk of deception by the threat actor to mislead attribution efforts.
4. Implications and Strategic Risks
The exploitation of this vulnerability could lead to increased geopolitical tensions if state sponsorship is confirmed. It may also prompt a reassessment of cyber defense postures globally.
- Political / Geopolitical: Potential for diplomatic fallout and increased cyber defense collaboration among affected nations.
- Security / Counter-Terrorism: Heightened alert levels and resource allocation to protect critical infrastructure from further cyber threats.
- Cyber / Information Space: Increased scrutiny on Cisco systems and potential for further exploitation of similar vulnerabilities by other actors.
- Economic / Social: Potential economic disruptions in affected sectors and erosion of public trust in cybersecurity measures.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct thorough audits of Cisco SD-WAN systems, apply patches, and monitor for indicators of compromise. Enhance information sharing among affected entities.
- Medium-Term Posture (1–12 months): Develop resilience measures, including regular vulnerability assessments and incident response planning. Strengthen international partnerships for cyber threat intelligence sharing.
- Scenario Outlook:
- Best Case: Successful mitigation and patching prevent further exploitation, and attribution leads to diplomatic resolution.
- Worst Case: Continued exploitation leads to significant disruptions in critical infrastructure and escalates geopolitical tensions.
- Most-Likely: Ongoing remediation efforts stabilize the situation, but the threat persists, requiring sustained vigilance and adaptation.
6. Key Individuals and Entities
- UAT-8616 (Threat Actor Group)
- Cisco (Technology Company)
- Australian Signals Directorate’s Australian Cyber Security Centre (Reporting Entity)
- US Cybersecurity and Infrastructure Security Agency (CISA)
7. Thematic Tags
cybersecurity, cyber-espionage, critical infrastructure, zero-day vulnerability, state-sponsored threat, Cisco SD-WAN, cyber defense
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us