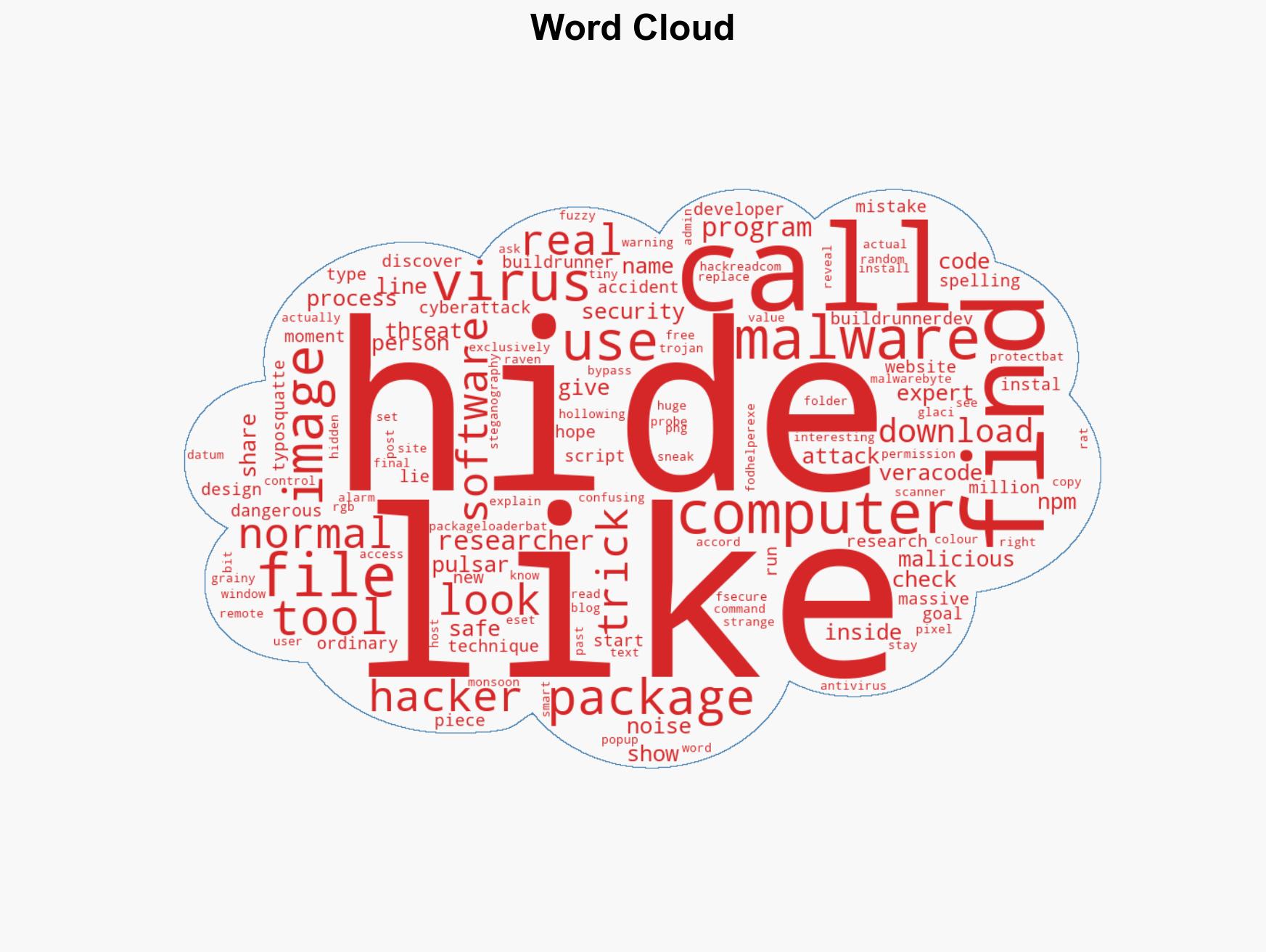
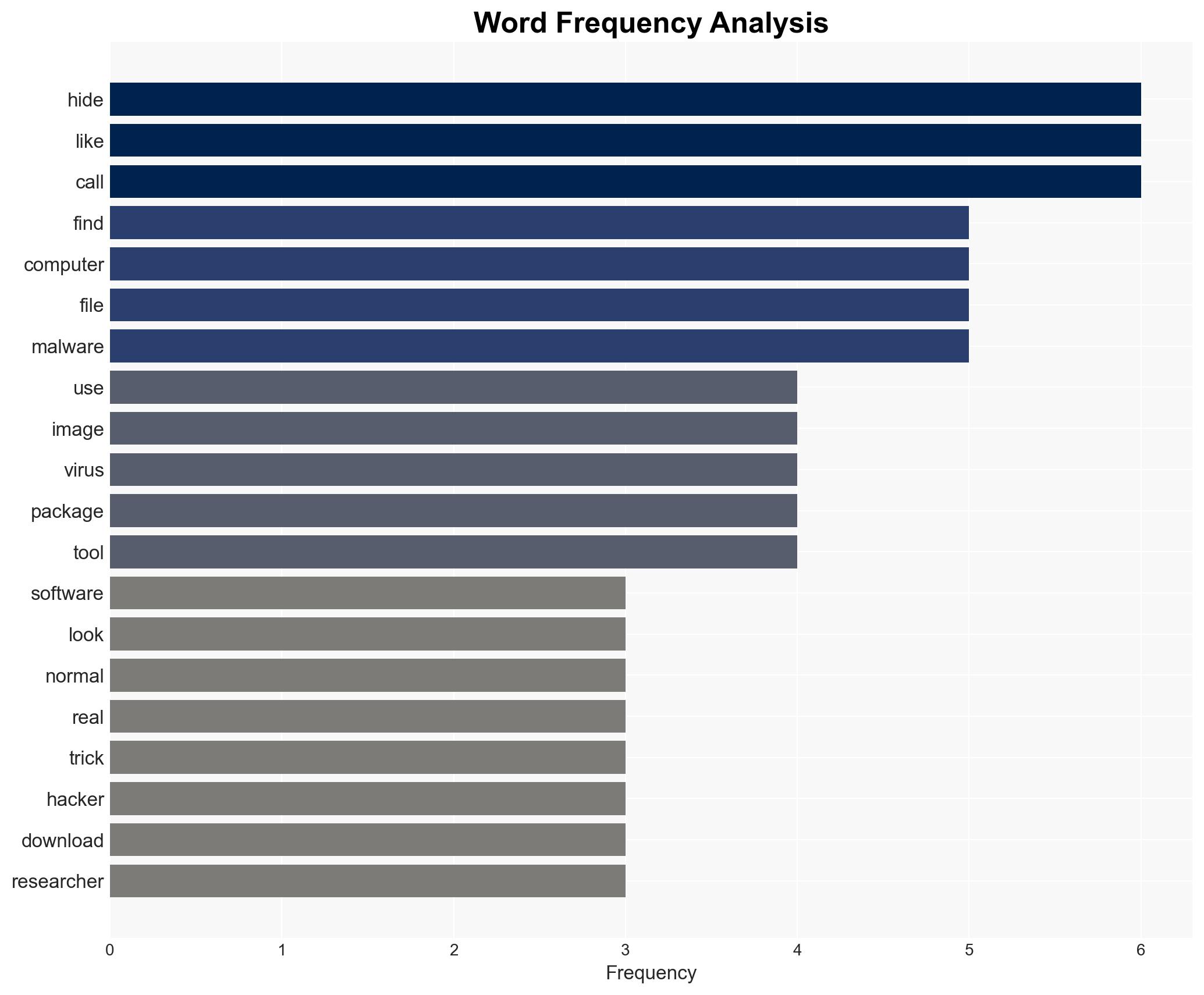
Cyberattackers Conceal Pulsar RAT in PNG Files via Malicious NPM Package Using Typosquatting Tactics
Published on: 2026-02-22
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Hackers Hide Pulsar RAT Inside PNG Images in New NPM Supply Chain Attack
1. BLUF (Bottom Line Up Front)
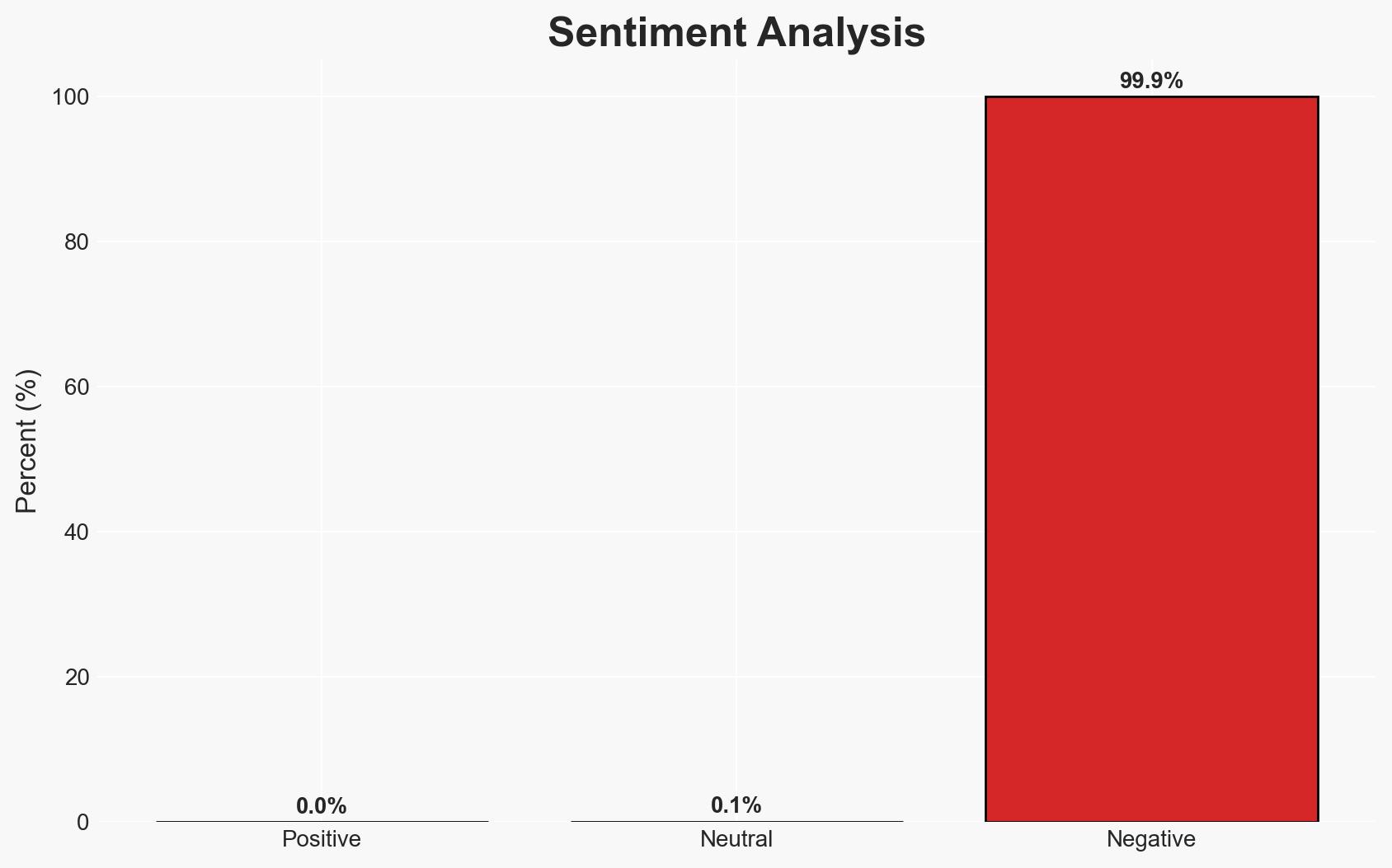
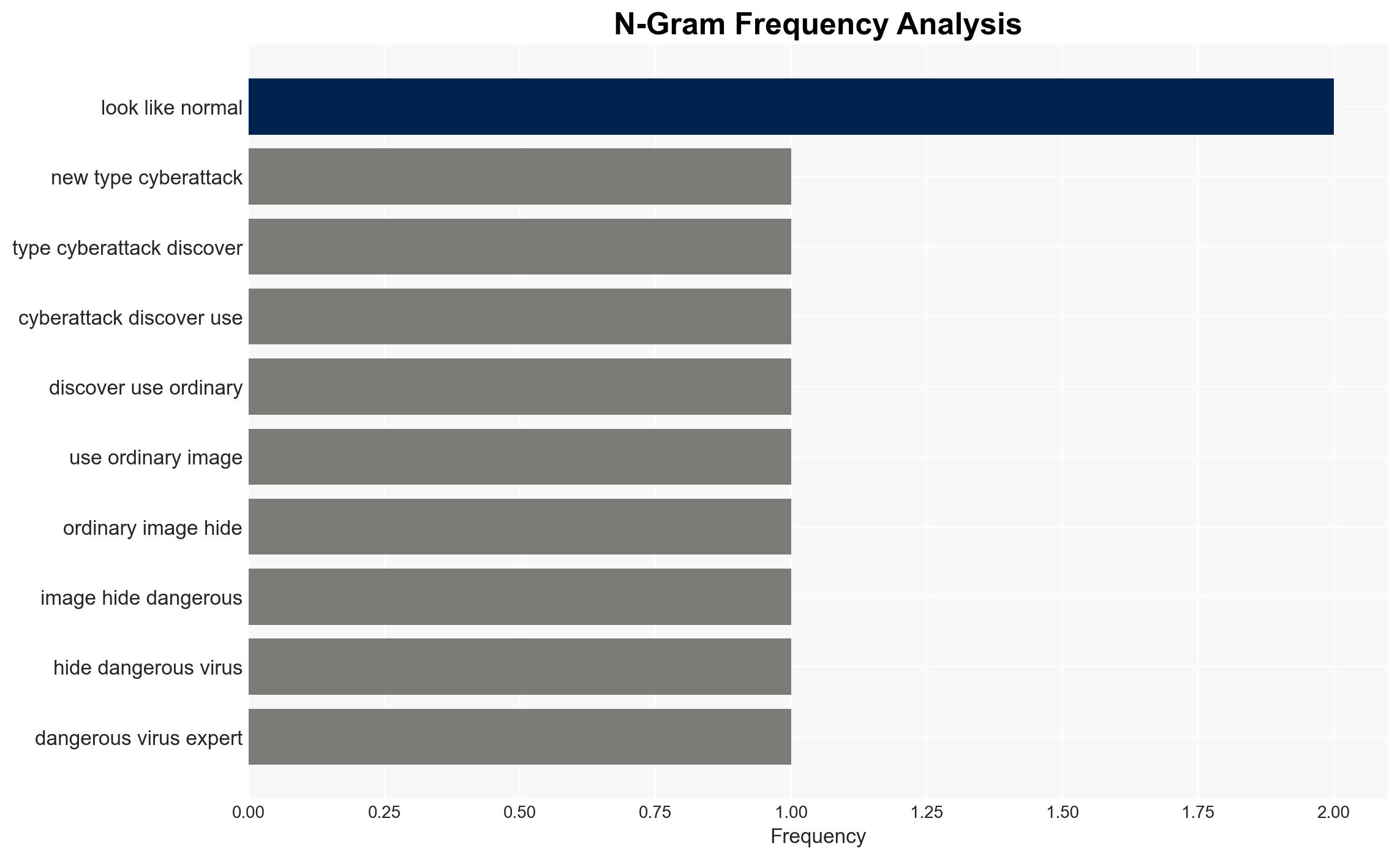
The discovery of a sophisticated cyberattack using steganography to hide the Pulsar RAT within PNG images on NPM represents a significant threat to software developers and potentially broader IT infrastructure. The attack leverages typosquatting and advanced evasion techniques, indicating a high level of sophistication. This assessment is made with moderate confidence due to existing information gaps regarding the attackers’ identity and broader intentions.
2. Competing Hypotheses
- Hypothesis A: The attack is primarily aimed at gaining unauthorized access to individual developers’ systems to exfiltrate data or conduct espionage. Supporting evidence includes the use of typosquatting and steganography, which are typically employed for targeted attacks. However, the lack of specific targeting information limits this hypothesis.
- Hypothesis B: The attack is part of a broader campaign to compromise software supply chains, potentially affecting multiple organizations. This is supported by the use of NPM, a widely used platform, suggesting an intent to infiltrate through a common entry point. Contradicting evidence includes the absence of widespread reports of compromised organizations.
- Assessment: Hypothesis B is currently better supported due to the attack’s deployment on a major platform like NPM, indicating a potential supply chain compromise. Key indicators that could shift this judgment include evidence of targeted espionage or data exfiltration activities.
3. Key Assumptions and Red Flags
- Assumptions: The attackers have the capability to exploit vulnerabilities in widely used platforms; the use of steganography is intentional to evade detection; the attack is not yet widespread.
- Information Gaps: The identity and motivations of the attackers; the full extent of the attack’s impact; potential connections to known threat actors.
- Bias & Deception Risks: Potential bias in source reporting due to limited visibility into the attackers’ operations; risk of deception through false flag operations or misattribution.
4. Implications and Strategic Risks
This development could lead to increased scrutiny of software supply chains and heightened security measures among developers and organizations. The use of sophisticated techniques may inspire similar attacks, escalating the threat landscape.
- Political / Geopolitical: Potential for increased tensions if state-sponsored actors are implicated, leading to diplomatic or economic repercussions.
- Security / Counter-Terrorism: Heightened alert for similar cyber threats targeting critical infrastructure or government systems.
- Cyber / Information Space: Increased focus on securing software development environments and enhancing detection capabilities for steganographic techniques.
- Economic / Social: Potential economic impact if major software platforms are compromised, affecting business operations and consumer trust.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of NPM and similar platforms for malicious packages; conduct awareness campaigns for developers on typosquatting and steganography risks.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for threat intelligence sharing; invest in advanced detection tools for steganography.
- Scenario Outlook: Best: Attack is contained with minimal impact; Worst: Widespread supply chain compromise; Most-Likely: Increased vigilance and minor disruptions in software development processes.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, supply chain attack, steganography, typosquatting, remote access trojan, software development, threat intelligence
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us