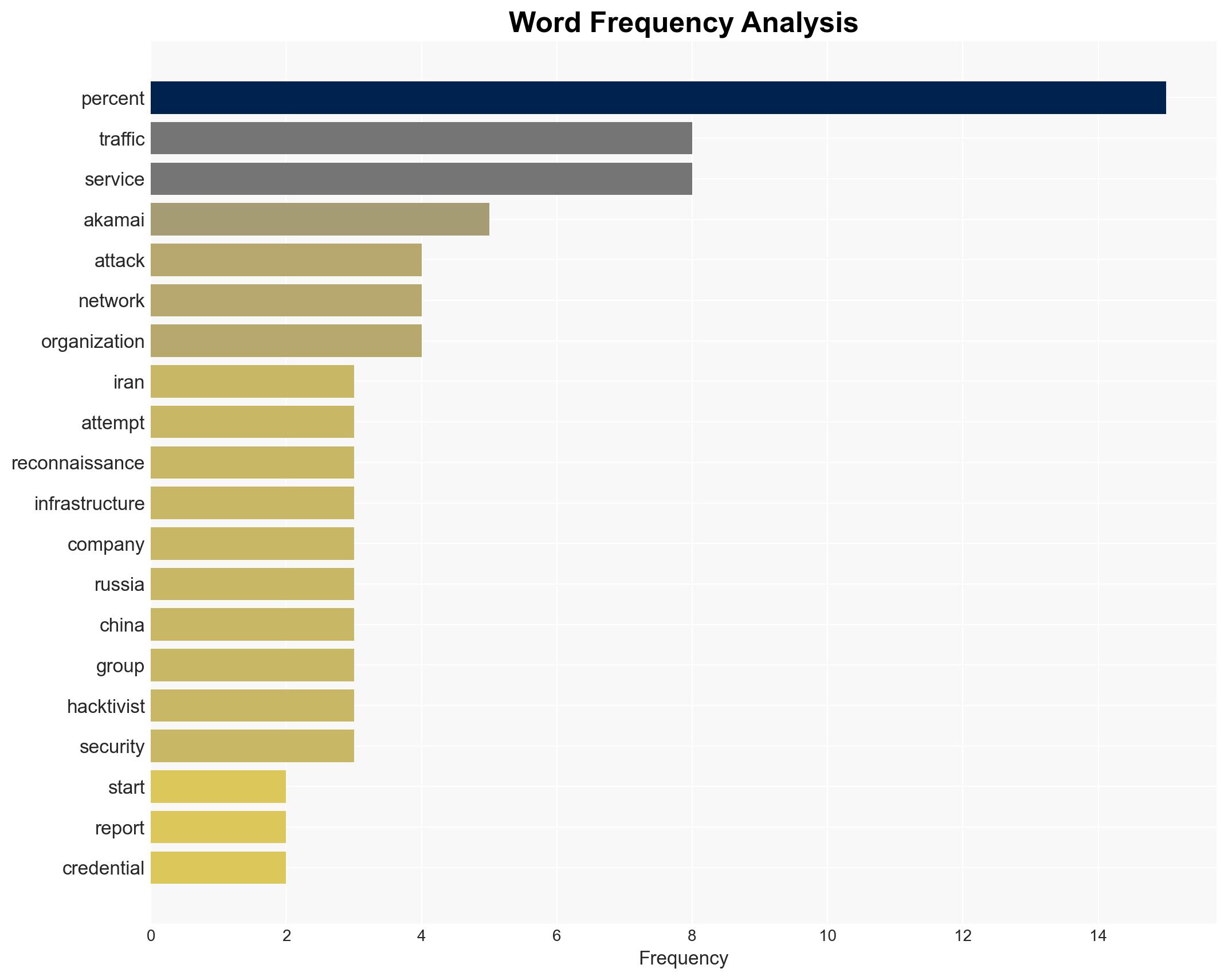
Cybercrime surged by 245% since the onset of the Iran war, with banking and fintech most affected.
Published on: 2026-03-16
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Cybercrime has skyrocketed 245 since the start of the Iran war
1. BLUF (Bottom Line Up Front)
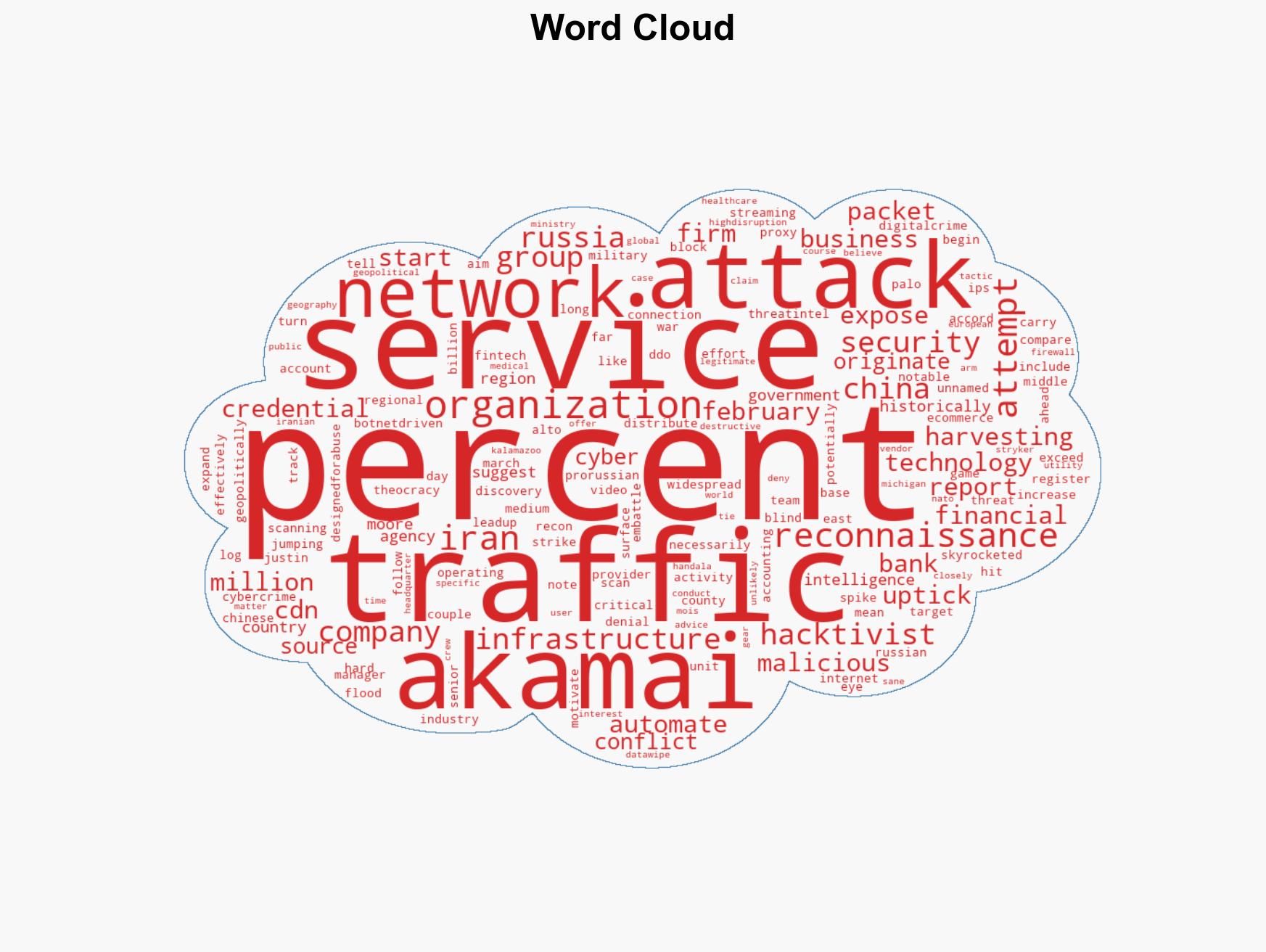
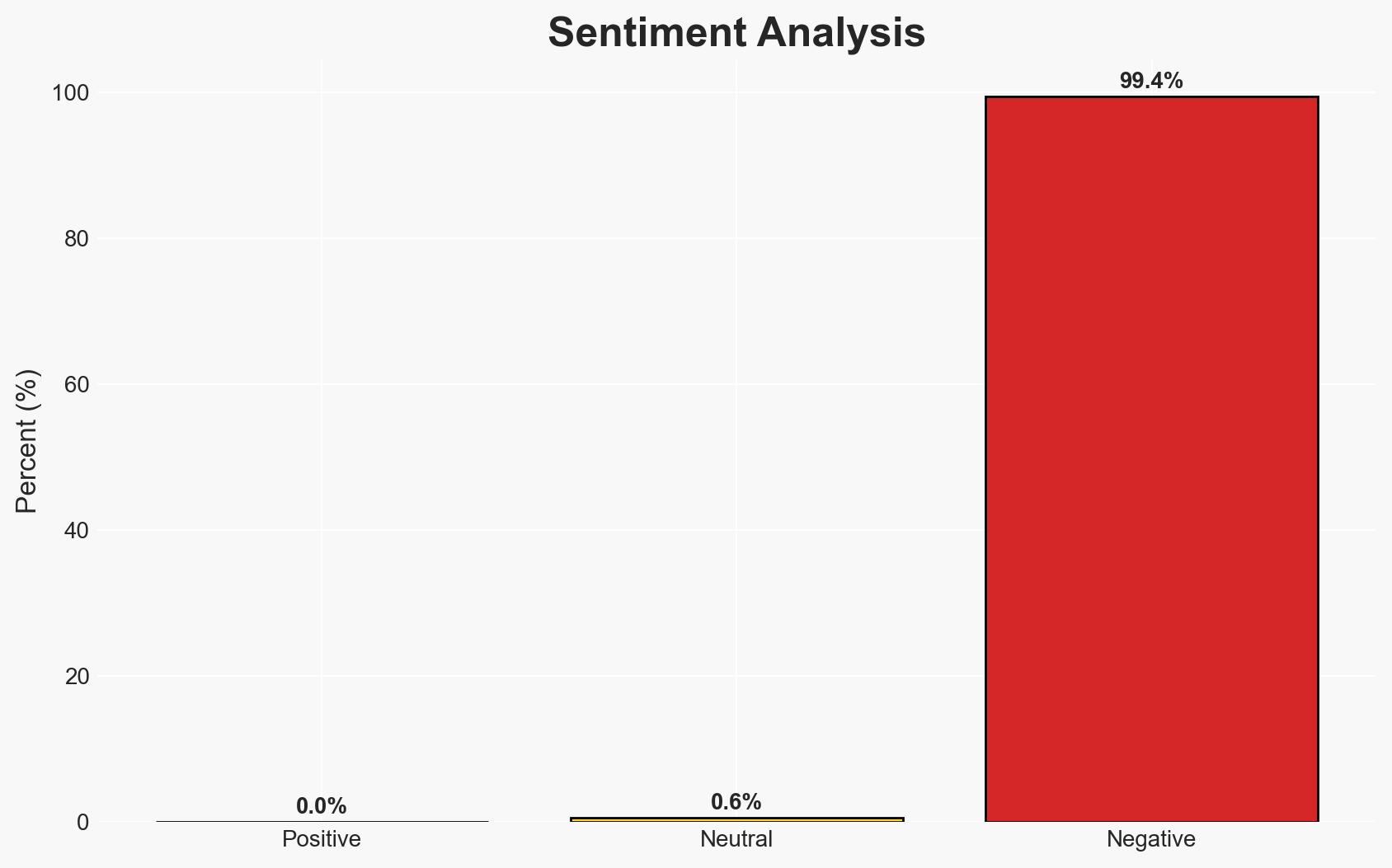
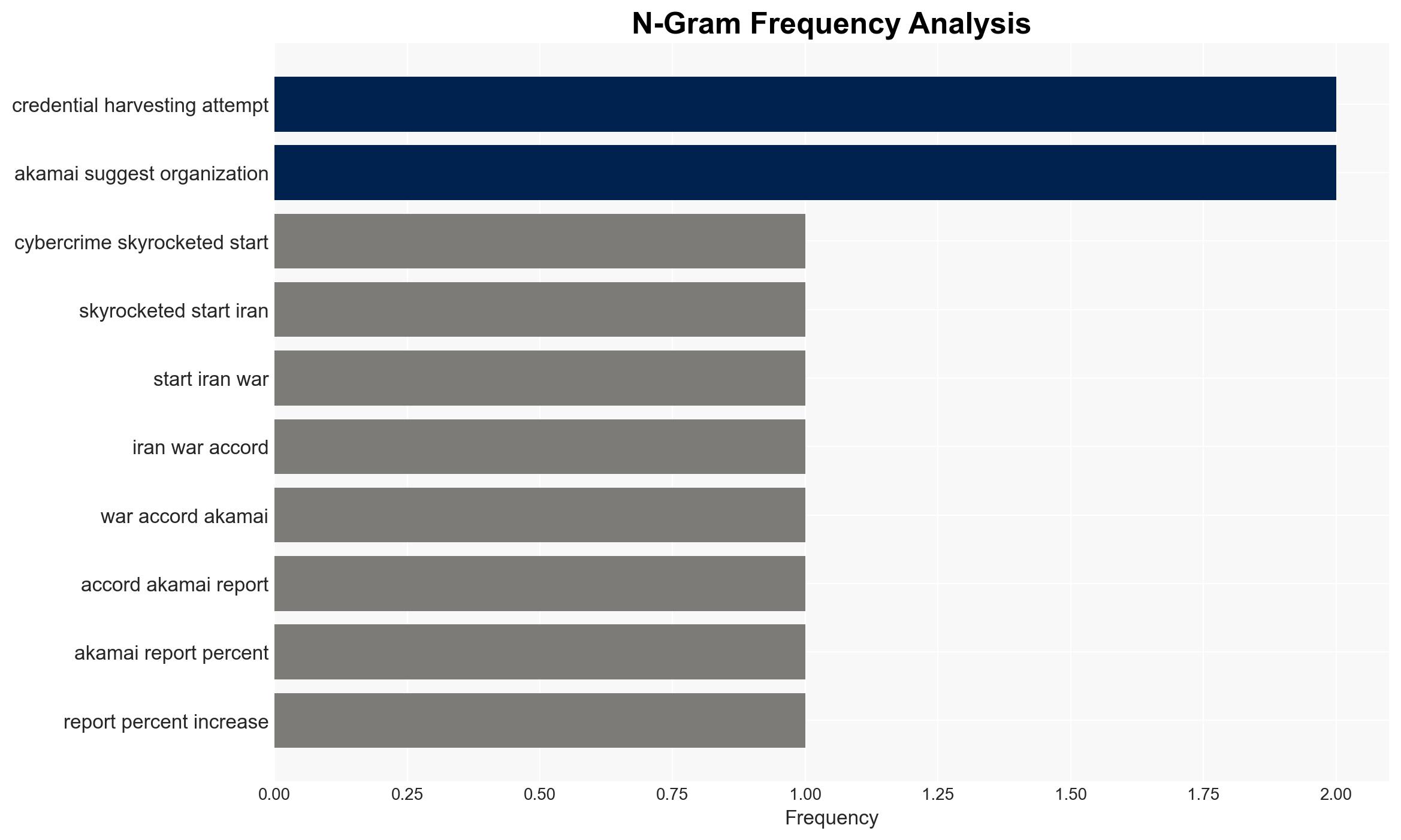
Cybercrime activities have surged by 245% since the onset of the Iran war, with significant impacts on banking, fintech, and other critical sectors. The primary sources of malicious traffic are linked to Russia and China, with geopolitical motivations likely influencing these activities. Overall, I assess with moderate confidence that state-affiliated or state-tolerated actors are leveraging the conflict to expand cyber operations.
2. Competing Hypotheses
- Hypothesis A: The increase in cybercrime is primarily driven by state-affiliated actors from Iran, Russia, and China exploiting the geopolitical situation. Evidence includes the high percentage of traffic from these countries and historical patterns of state-tolerated cyber activities. However, the exact attribution of attacks remains uncertain.
- Hypothesis B: The surge in cybercrime is largely opportunistic, with independent hacktivists and cybercriminals exploiting the chaos of the Iran conflict. This is supported by the diverse range of targeted sectors and the use of proxy services. Contradicting evidence includes the structured nature of some attacks, suggesting more organized efforts.
- Assessment: Hypothesis A is currently better supported due to the involvement of known state-affiliated groups and the geopolitical context. Indicators that could shift this judgment include evidence of decentralized coordination among non-state actors or shifts in attack patterns.
3. Key Assumptions and Red Flags
- Assumptions: The reported increase is accurately attributed to the Iran conflict; State actors have the capability and intent to exploit the situation; Proxy services are used to obfuscate true attack origins.
- Information Gaps: Detailed attribution of specific attacks; The role of non-state actors in the current surge; The extent of coordination between state and non-state actors.
- Bias & Deception Risks: Potential bias in attributing attacks to state actors without concrete evidence; Deception through the use of proxy services to mislead attribution efforts.
4. Implications and Strategic Risks
The increase in cybercrime activities could exacerbate geopolitical tensions and lead to retaliatory measures in cyberspace. This development may also embolden other state and non-state actors to exploit similar conflicts for cyber operations.
- Political / Geopolitical: Potential escalation in cyber hostilities between involved states, impacting diplomatic relations.
- Security / Counter-Terrorism: Increased threat to critical infrastructure and potential for cyber-enabled terrorism.
- Cyber / Information Space: Expansion of attack surfaces and increased sophistication of cyber operations.
- Economic / Social: Disruption to financial systems and erosion of public trust in digital services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber activities linked to conflict zones; Strengthen defenses of critical infrastructure; Increase intelligence sharing among allies.
- Medium-Term Posture (1–12 months): Develop resilience measures and incident response capabilities; Foster international cooperation to address state-sponsored cyber threats.
- Scenario Outlook:
- Best: De-escalation of cyber activities with increased international cooperation.
- Worst: Escalation into broader cyber conflict affecting global stability.
- Most-Likely: Continued cyber operations with periodic spikes aligned with geopolitical events.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cybercrime, geopolitical conflict, state-sponsored cyber operations, critical infrastructure, cyber defense, hacktivism, proxy services
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us