Cybercriminals exploit AI tools to breach over 600 FortiGate firewalls across 55 countries in a month-long ca…
Published on: 2026-02-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
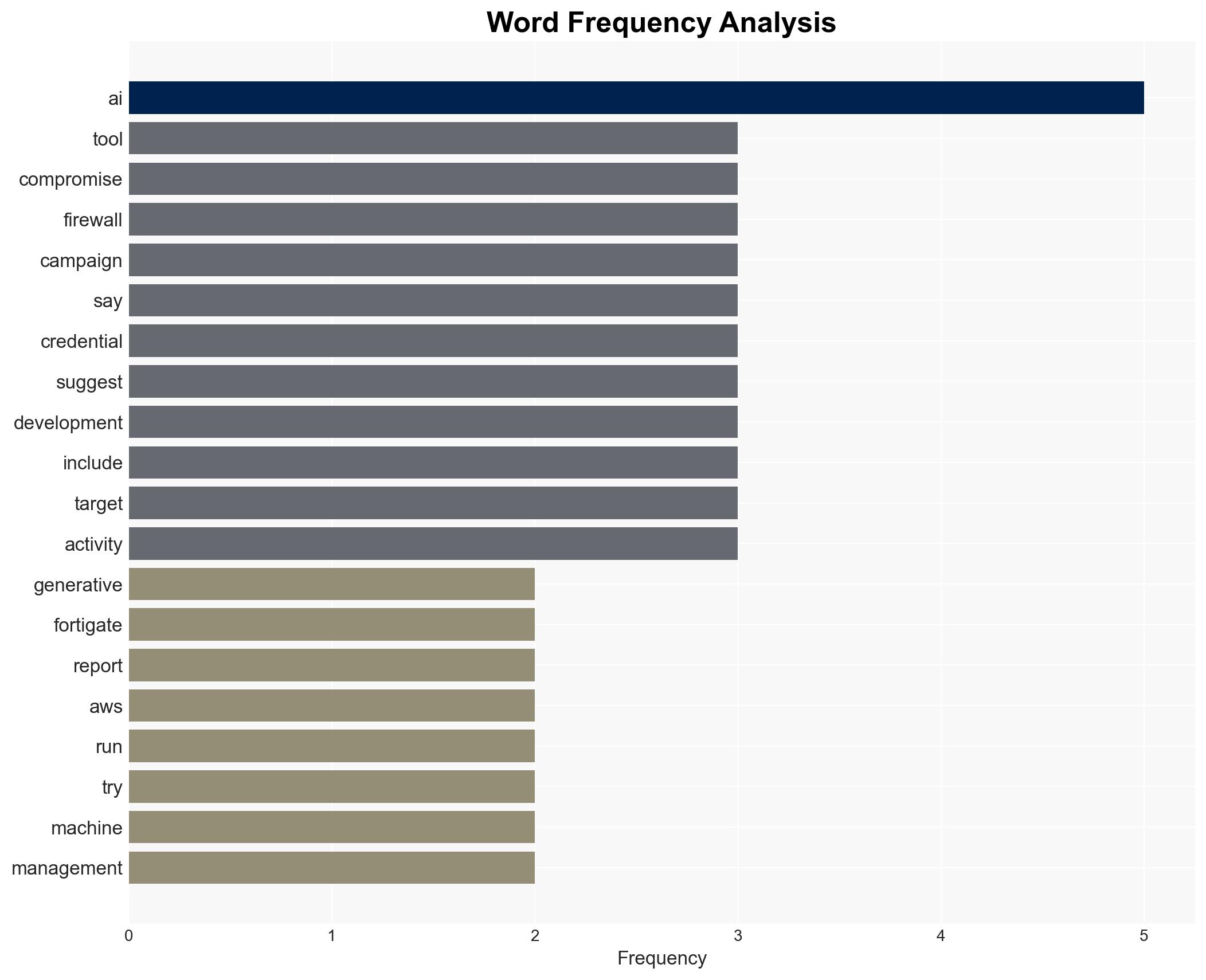
Intelligence Report: AWS says more than 600 FortiGate firewalls hit in AI-augmented campaign
1. BLUF (Bottom Line Up Front)
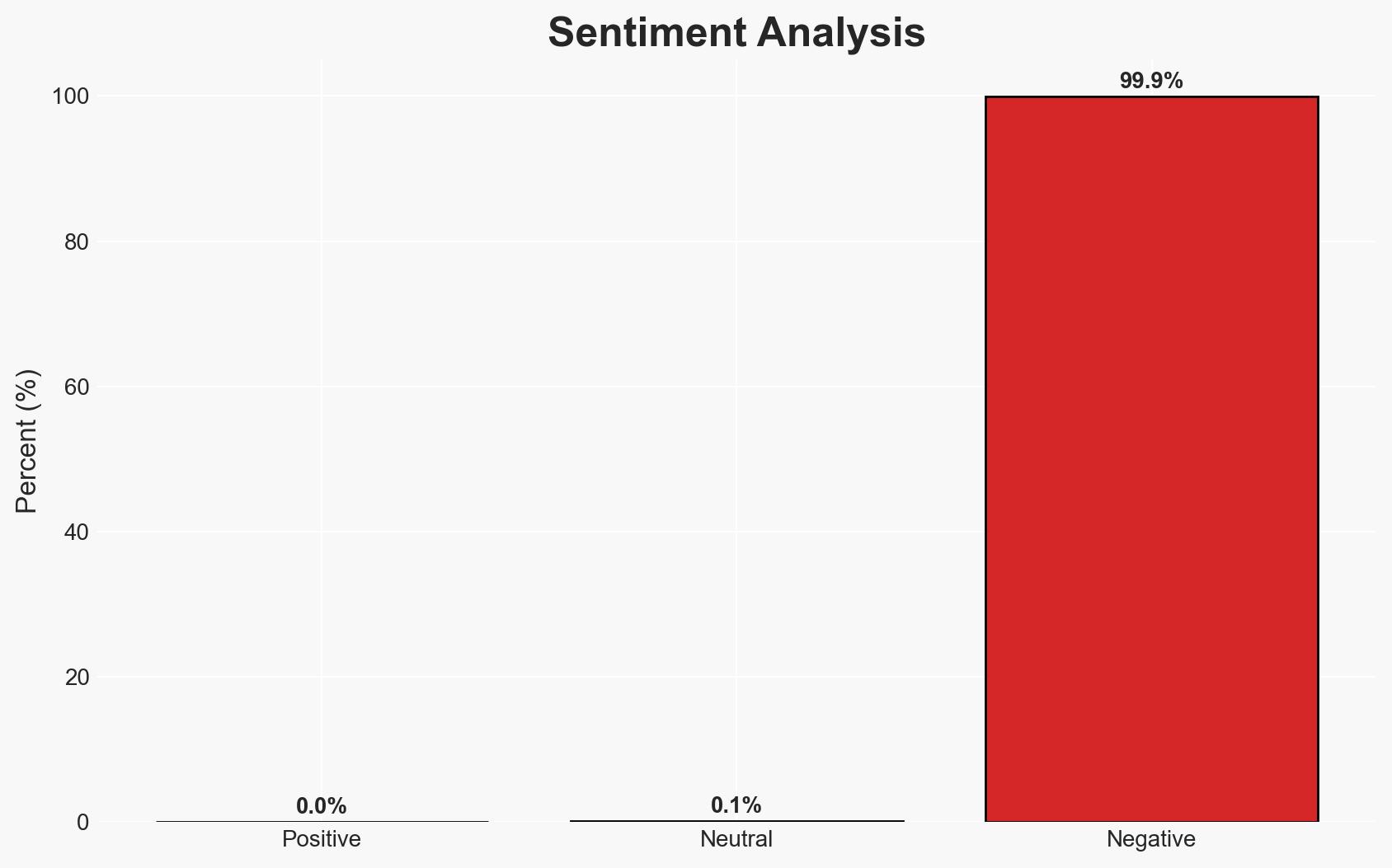
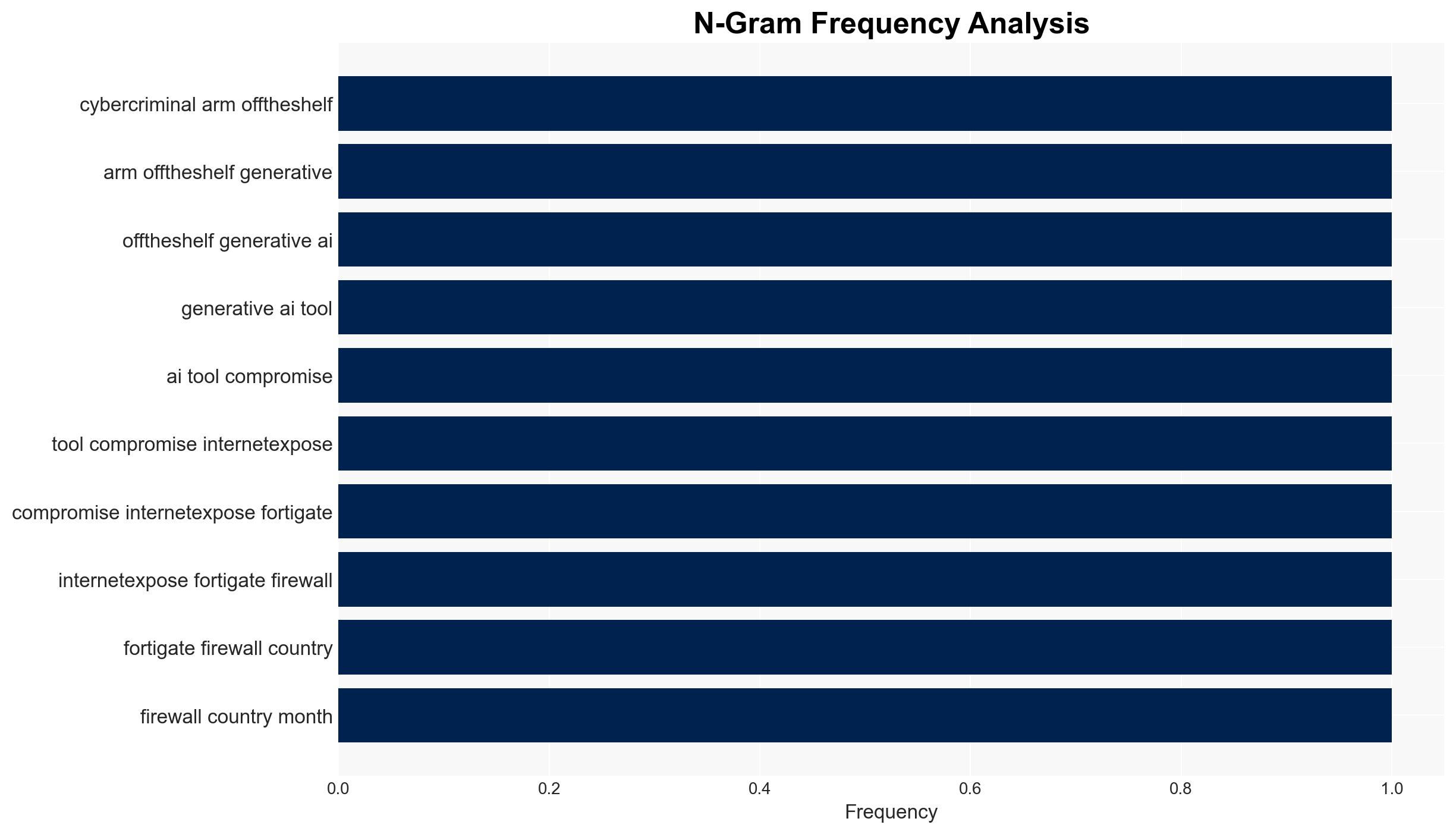
The recent cyber campaign targeting over 600 FortiGate firewalls across 55 countries highlights the growing use of AI tools by cybercriminals, enabling low-skilled actors to execute sophisticated attacks. The operation, attributed to a financially motivated Russian-speaking group, underscores vulnerabilities in network management practices. Moderate confidence is placed in the assessment that AI will increasingly lower the barrier for complex cyber operations, affecting global cybersecurity resilience.
2. Competing Hypotheses
- Hypothesis A: The campaign was primarily opportunistic, leveraging AI to exploit widespread poor cybersecurity hygiene. Evidence includes the use of common attack vectors and the abandonment of resistant targets. Key uncertainties involve the exact role of AI in decision-making processes.
- Hypothesis B: The campaign was a targeted effort to infiltrate specific high-value networks, using AI to mask intentions. This is less supported due to the broad geographic spread and lack of specific targeting indicators.
- Assessment: Hypothesis A is currently better supported, given the opportunistic nature of the attacks and the emphasis on volume over precision. Indicators that could shift this judgment include evidence of specific targeting or strategic objectives beyond financial gain.
3. Key Assumptions and Red Flags
- Assumptions: AI tools significantly lower the skill threshold for conducting cyber operations; poor cybersecurity hygiene is widespread; the group is financially motivated.
- Information Gaps: Detailed understanding of the AI tools used and their decision-making capabilities; confirmation of the group’s identity and motivations.
- Bias & Deception Risks: Potential overestimation of AI’s role due to novelty bias; reliance on AWS as a single source may introduce confirmation bias.
4. Implications and Strategic Risks
This development could lead to increased adoption of AI in cybercrime, challenging existing cybersecurity frameworks and necessitating new defensive strategies. The ease of executing complex attacks may embolden less skilled actors.
- Political / Geopolitical: Potential for increased tensions if state actors are suspected of similar tactics.
- Security / Counter-Terrorism: Heightened risk of cyber threats to critical infrastructure and national security assets.
- Cyber / Information Space: Accelerated arms race in AI-driven cyber capabilities; potential for misinformation regarding AI’s capabilities.
- Economic / Social: Increased costs for cybersecurity measures; potential loss of trust in digital infrastructure.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of AI tool usage in cyber operations; promote best practices for network security hygiene.
- Medium-Term Posture (1–12 months): Develop partnerships to share intelligence on AI-driven threats; invest in AI-based defensive technologies.
- Scenario Outlook:
- Best: Improved cybersecurity resilience through AI-enhanced defenses.
- Worst: Proliferation of AI-driven cybercrime overwhelms current defenses.
- Most-Likely: Gradual adaptation to AI threats with intermittent disruptions.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
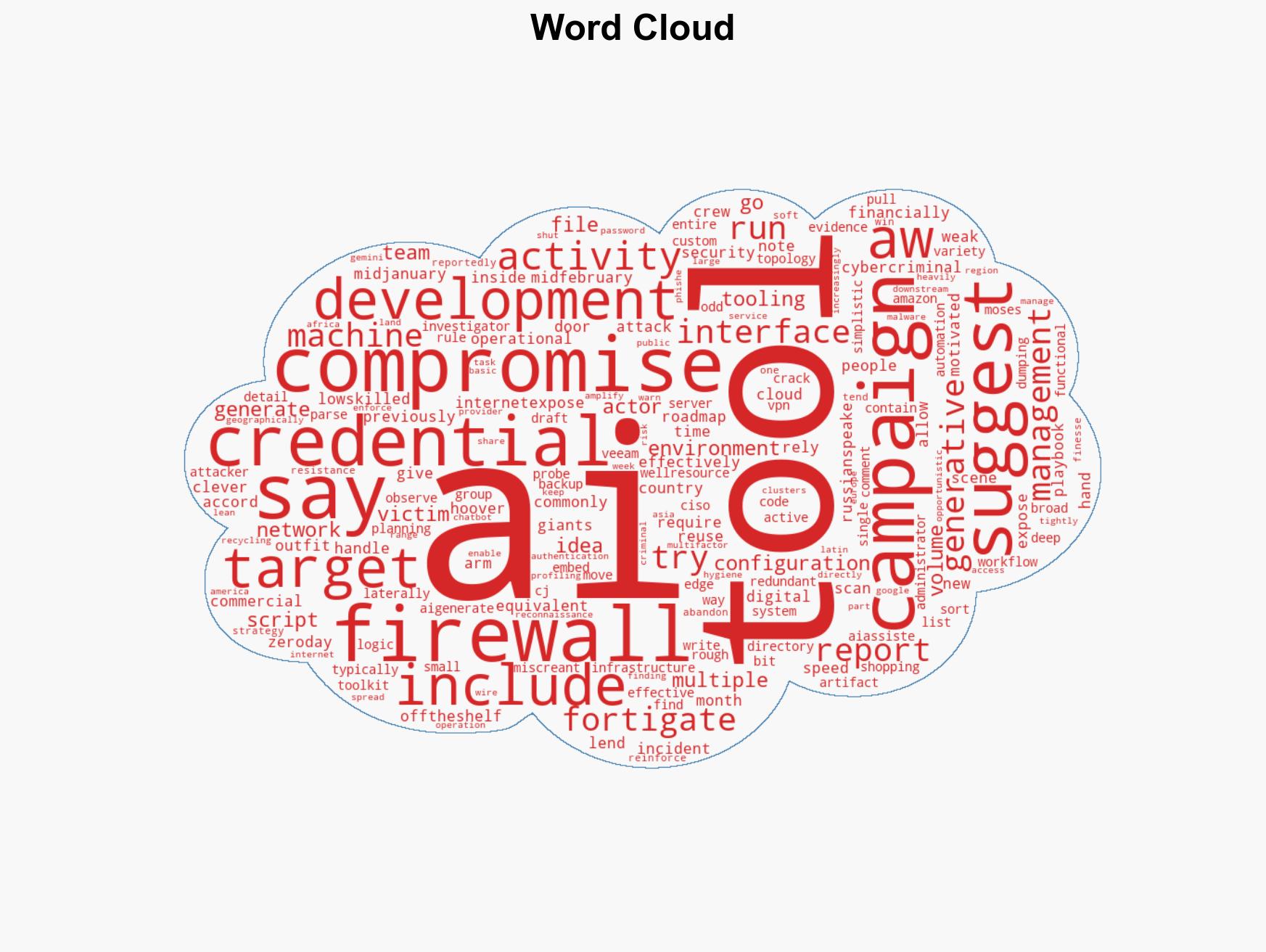
cybersecurity, AI in cybercrime, FortiGate firewalls, cyber hygiene, Russian-speaking cyber actors, network vulnerabilities, global cyber threats
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us