Cybercriminals leverage automation for rapid network breaches; strategies for defense are evolving.
Published on: 2026-03-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Cyberattackers are moving faster to break your network – how to fight back
1. BLUF (Bottom Line Up Front)
The rapid evolution of cyberattack techniques, particularly through automation, significantly reduces the time available for defense, posing increased risks to enterprise networks. The high-tech and financial sectors are especially vulnerable. The most likely hypothesis is that automation will continue to accelerate the pace of cyberattacks, necessitating enhanced defensive measures. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
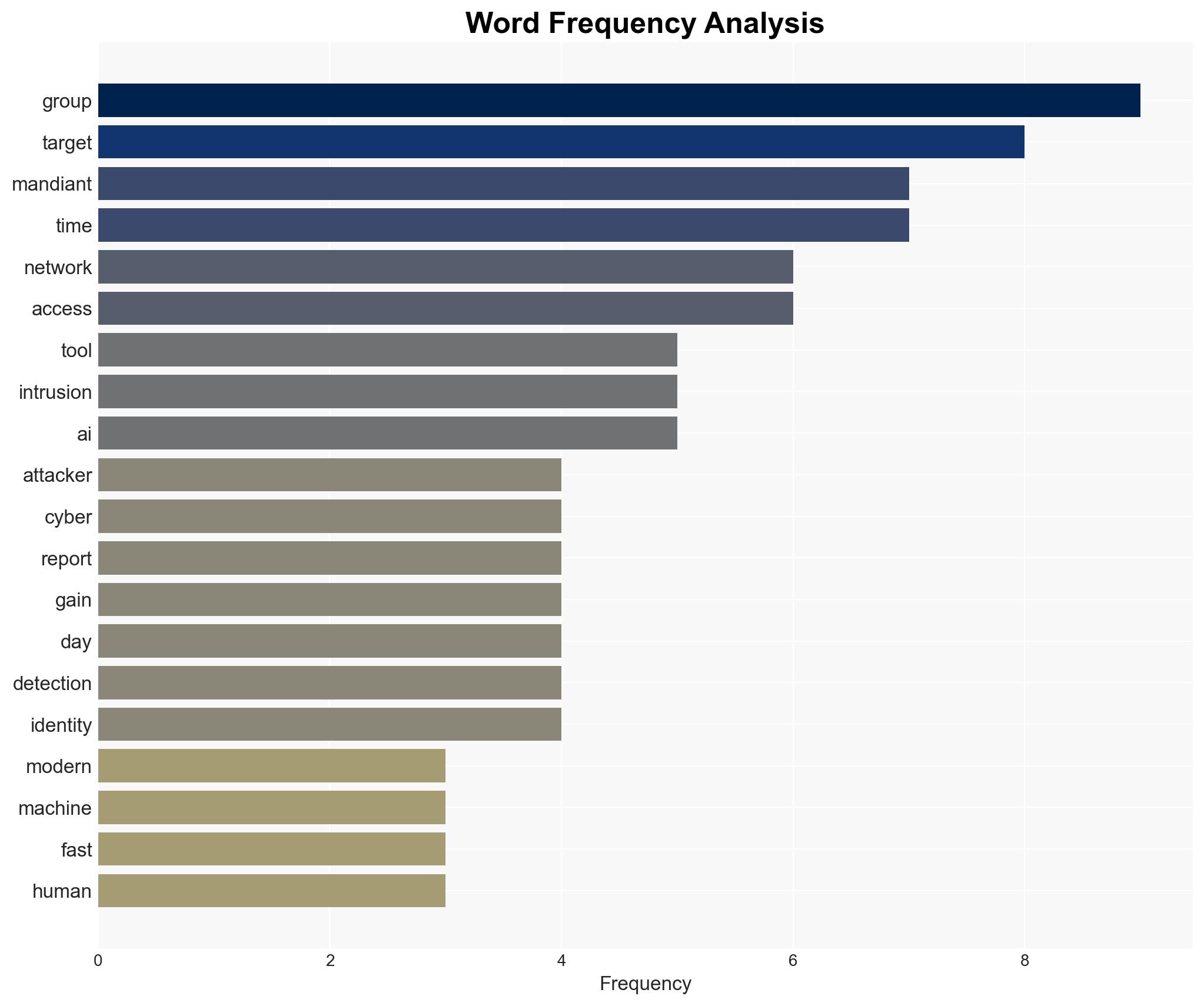
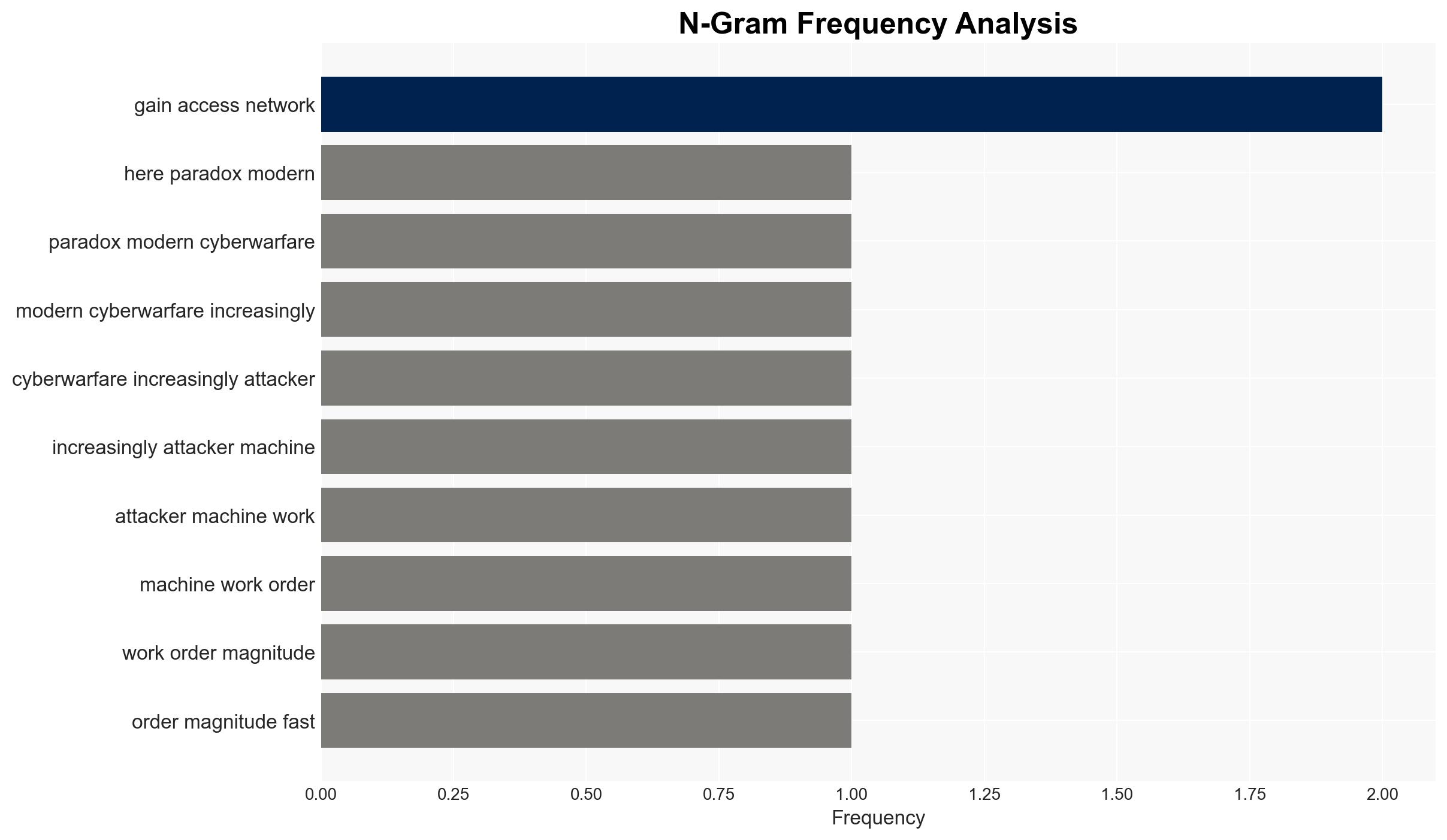
- Hypothesis A: Automation in cyberattacks will continue to reduce the time to compromise networks, increasing the frequency and impact of breaches. This is supported by the reported reduction in “time to hand-off” from hours to seconds and the decreasing time to exploit vulnerabilities.
- Hypothesis B: Defensive automation will effectively counteract the increased speed of cyberattacks, maintaining current levels of network security. This is contradicted by the persistent human element as a weak point and the ongoing success of cybercriminals and espionage groups.
- Assessment: Hypothesis A is currently better supported due to the demonstrated rapid advancements in offensive automation and the continued vulnerabilities in human oversight. Indicators that could shift this judgment include significant breakthroughs in defensive AI or machine learning capabilities.
3. Key Assumptions and Red Flags
- Assumptions: Automation will continue to advance in both offensive and defensive cyber operations; human oversight will remain a critical vulnerability; cybercriminals and espionage groups will persist in exploiting these vulnerabilities.
- Information Gaps: Detailed data on the effectiveness of current defensive automation technologies; insights into the strategic objectives of major cyber threat actors.
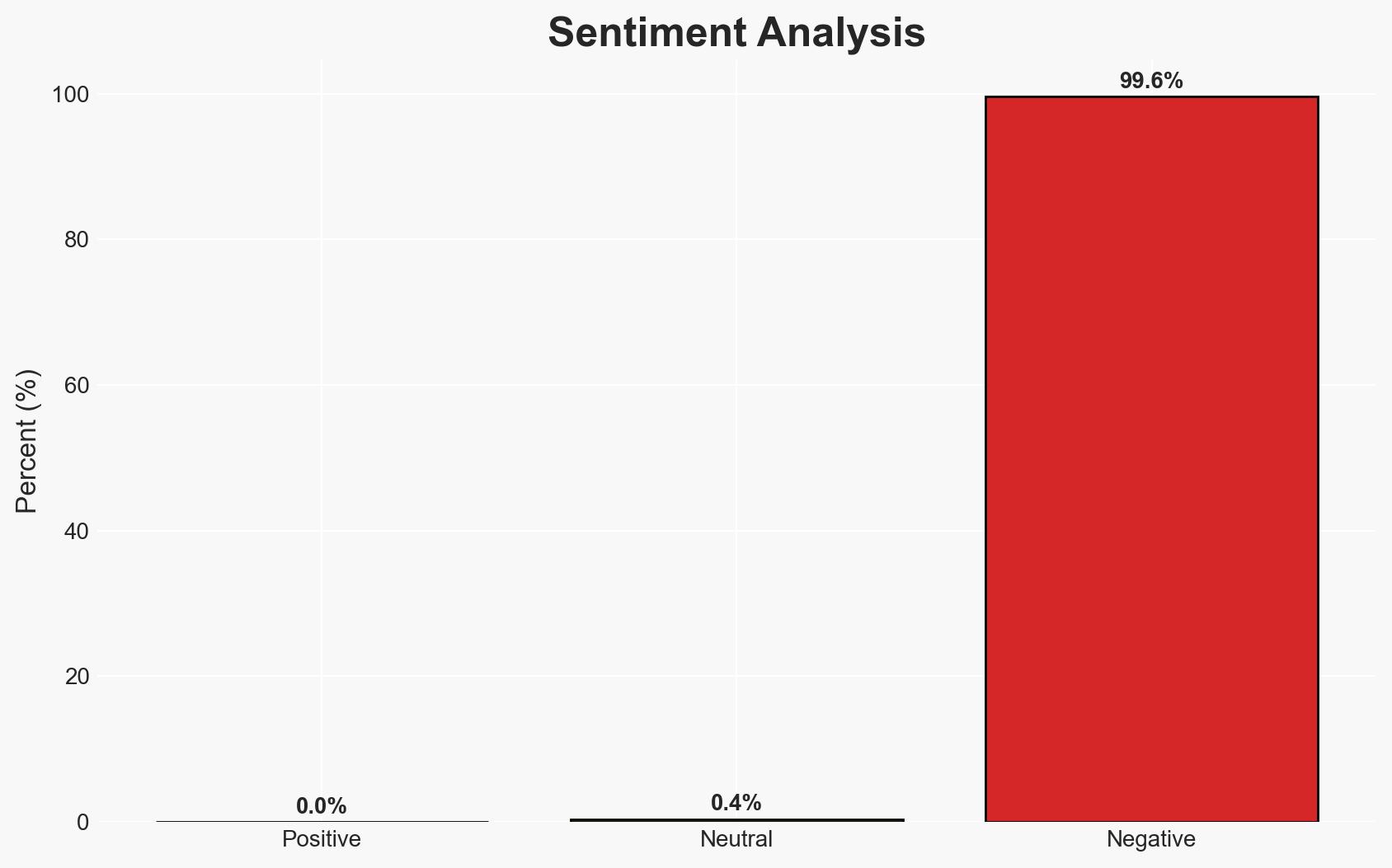
- Bias & Deception Risks: Potential bias in Mandiant’s reporting due to vested interests in promoting cybersecurity solutions; possible deception by threat actors in masking their true capabilities or intentions.
4. Implications and Strategic Risks
The acceleration of cyberattack capabilities through automation could lead to more frequent and severe breaches, impacting critical infrastructure and economic stability.
- Political / Geopolitical: Increased cyber tensions between nation-states, potential for retaliatory cyber operations.
- Security / Counter-Terrorism: Heightened threat environment, requiring enhanced vigilance and response strategies.
- Cyber / Information Space: Greater emphasis on developing advanced defensive technologies and improving cyber hygiene practices.
- Economic / Social: Potential for significant economic losses and erosion of public trust in digital systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of network activities, conduct vulnerability assessments, and update incident response plans.
- Medium-Term Posture (1–12 months): Invest in advanced defensive automation technologies, foster public-private partnerships for threat intelligence sharing, and conduct regular cybersecurity training.
- Scenario Outlook:
- Best Case: Defensive technologies outpace offensive advancements, reducing breach frequency.
- Worst Case: Offensive automation overwhelms defenses, leading to widespread breaches.
- Most Likely: Continued arms race between offensive and defensive capabilities, with incremental improvements on both sides.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
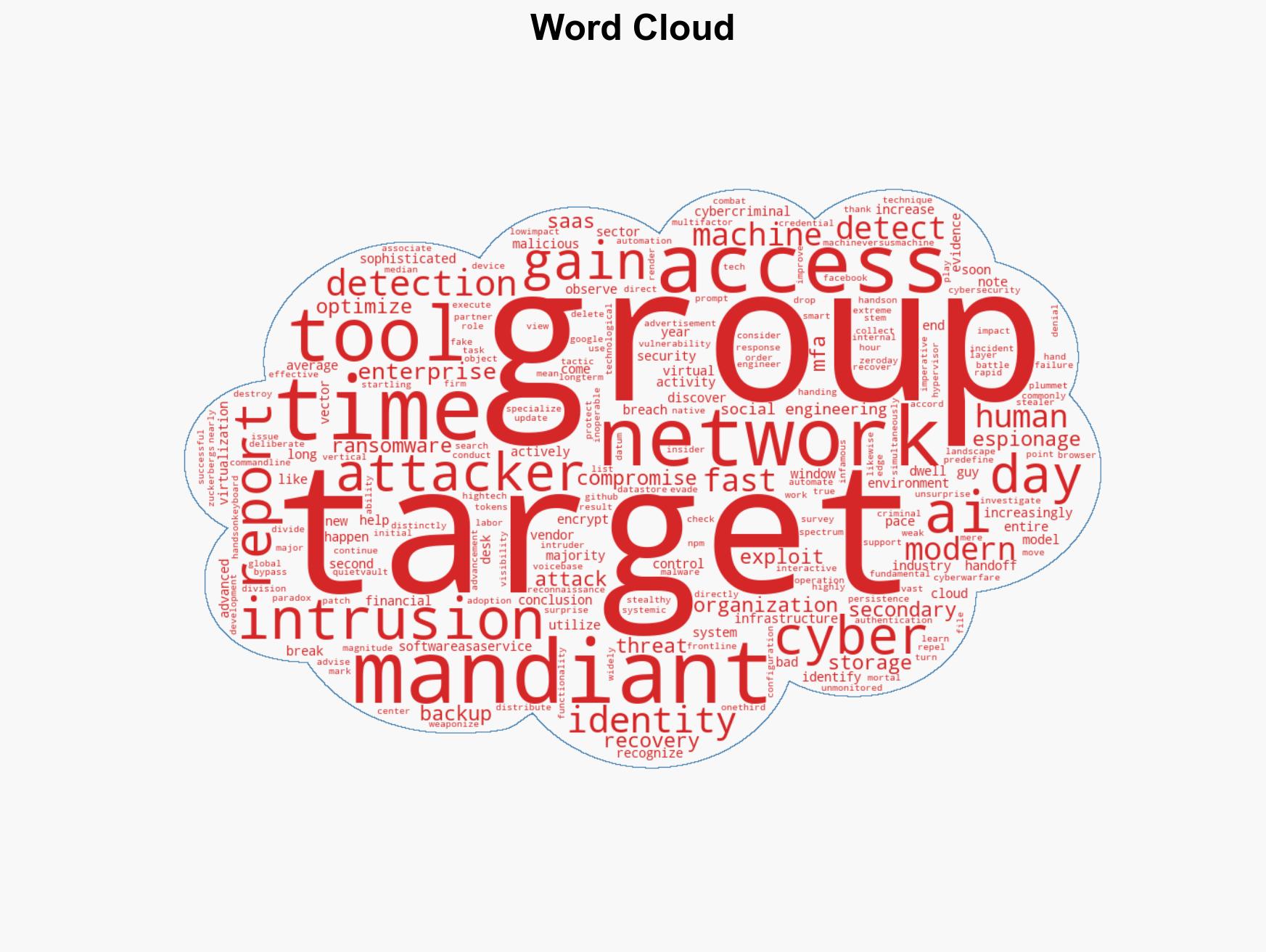
cybersecurity, automation, cyber-espionage, ransomware, enterprise networks, threat intelligence, vulnerability management
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us