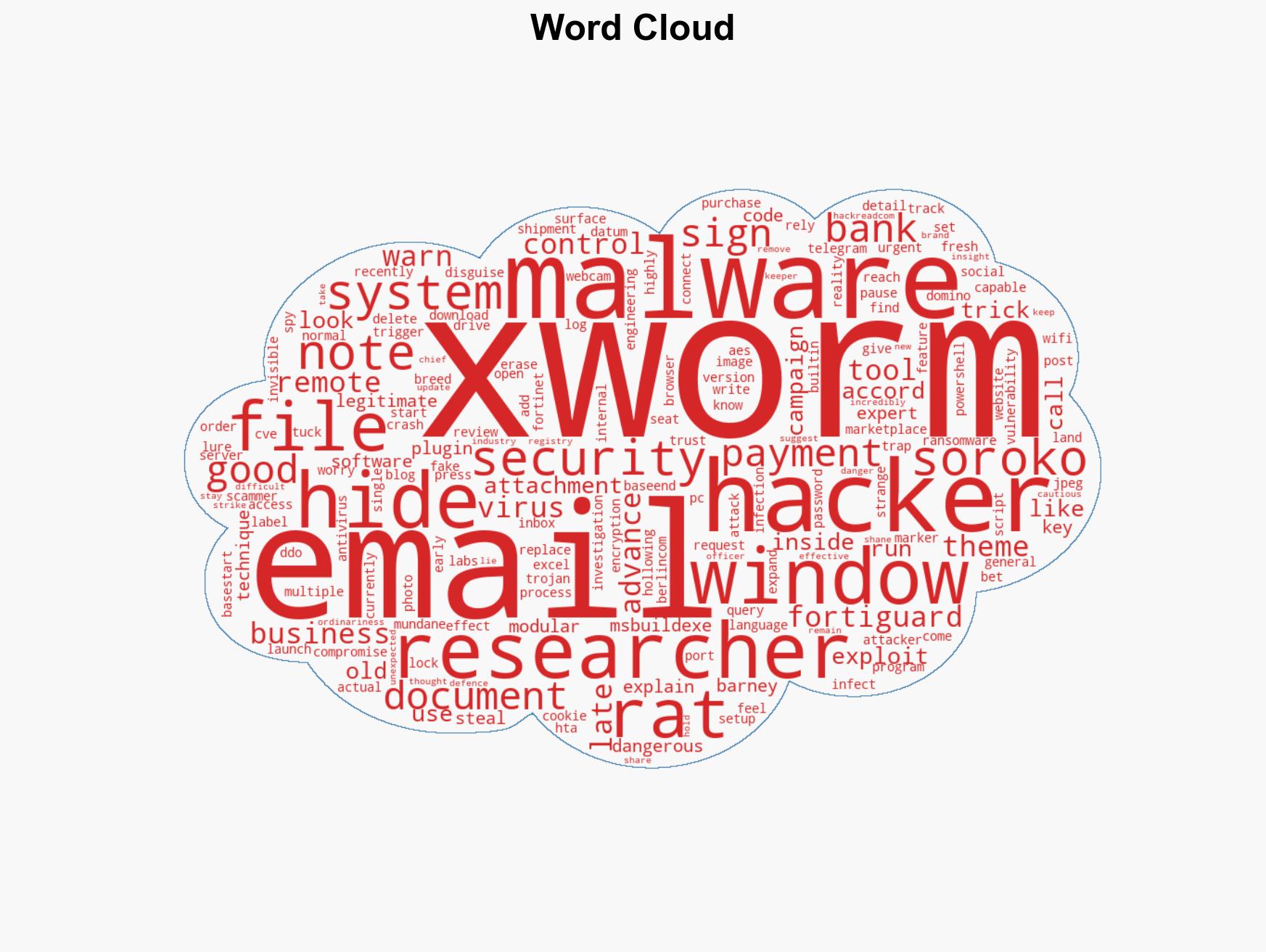
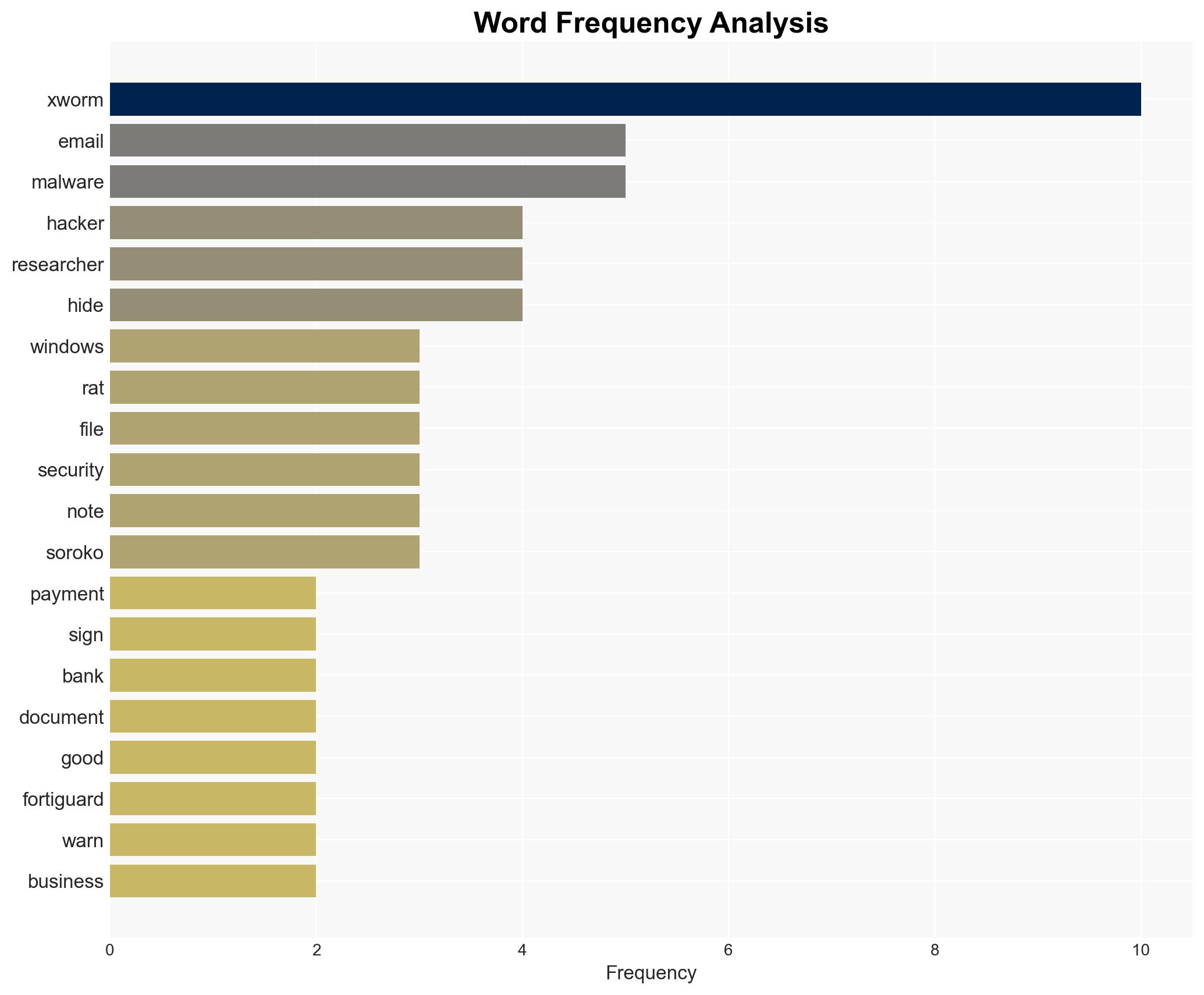
Cybercriminals Leverage Excel Vulnerability to Deploy XWorm 7.2 via Malicious JPEG Attachments
Published on: 2026-02-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Hackers Use Excel Exploit to Hide XWorm 72 in JPEG Files Hijack PCs
1. BLUF (Bottom Line Up Front)
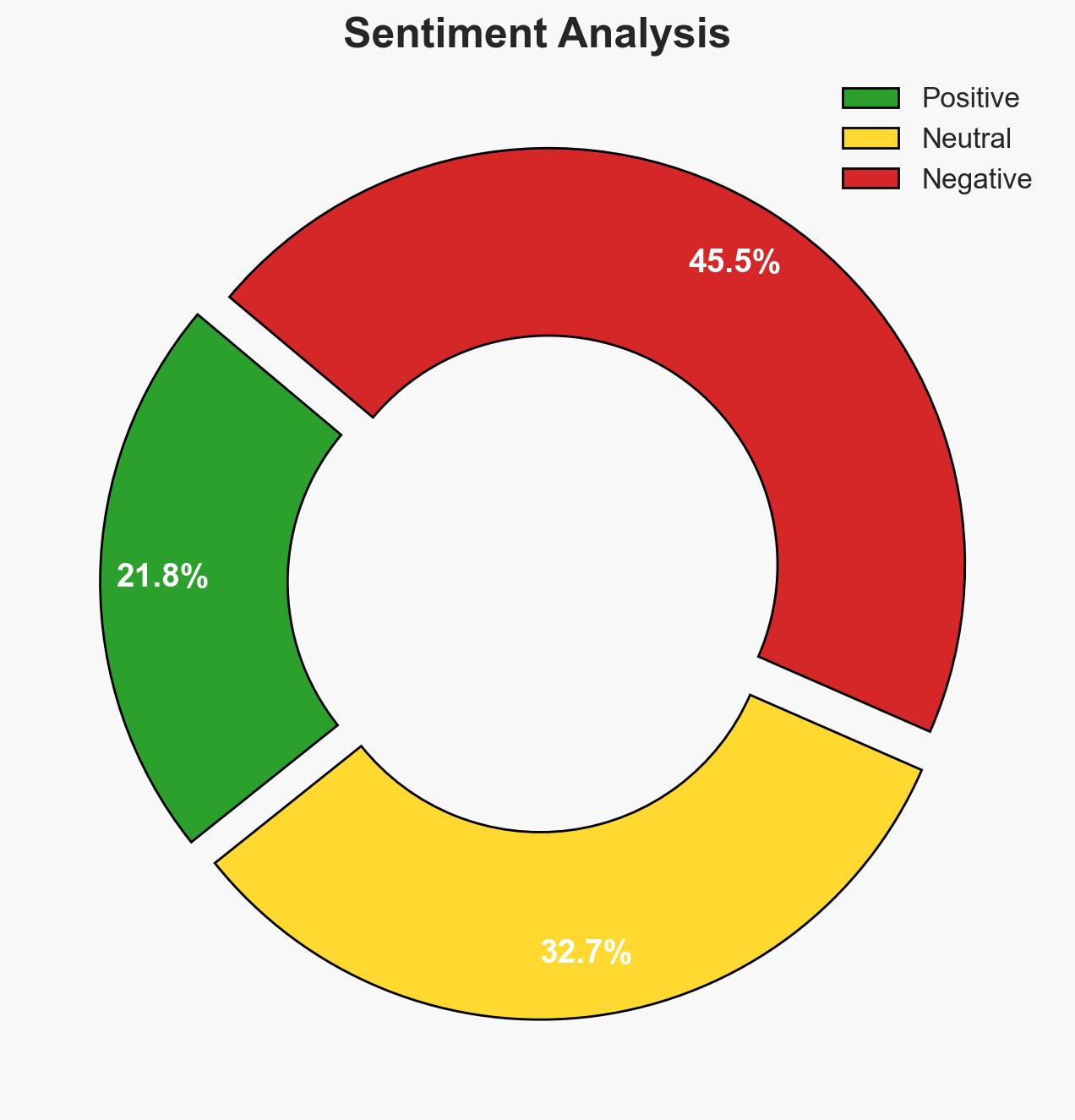
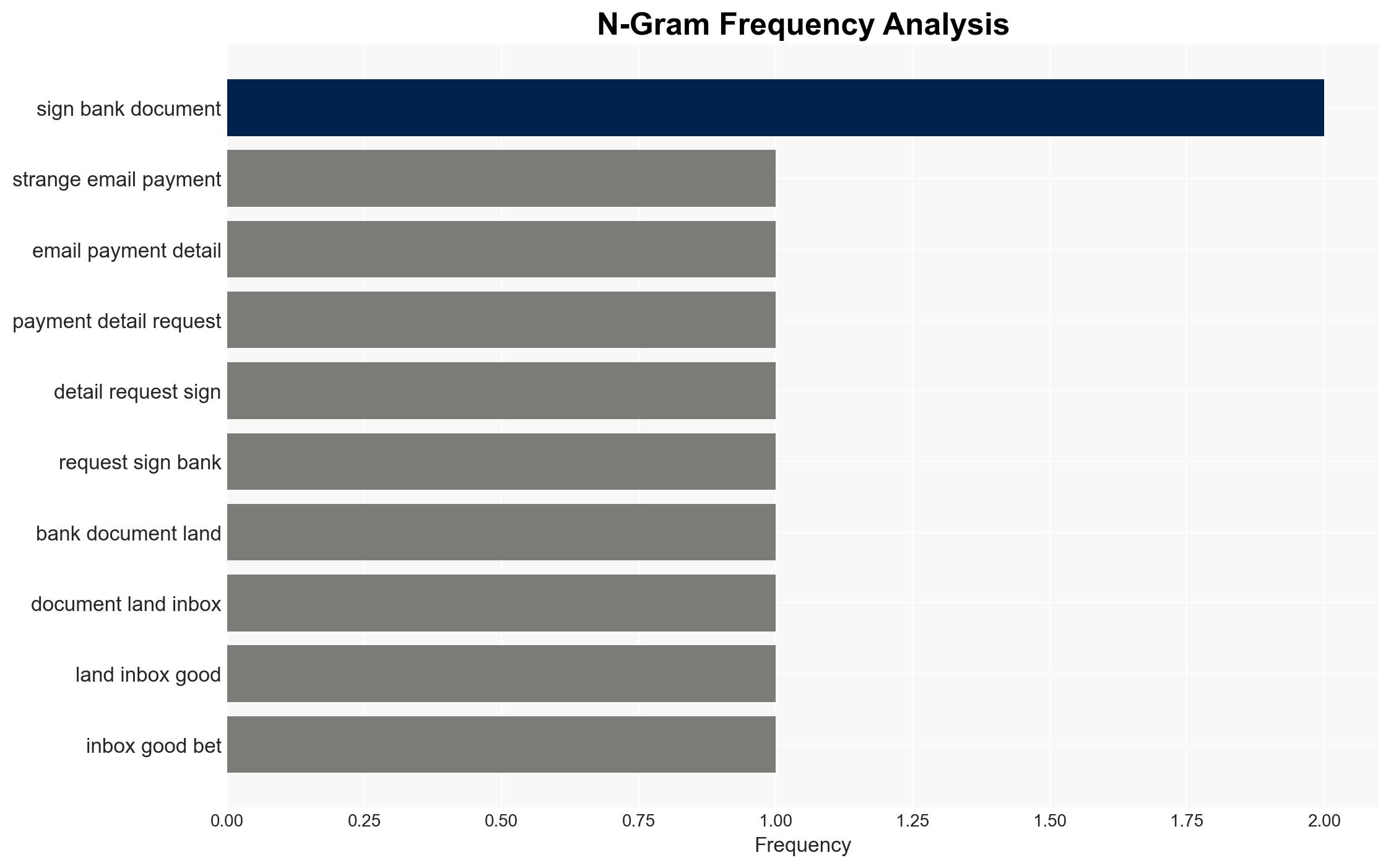
Hackers are exploiting an old Excel vulnerability to deploy XWorm 7.2 malware, using social engineering tactics to target Windows PCs. This campaign poses a significant threat due to its advanced evasion techniques and modular capabilities. The primary affected parties are businesses and individuals receiving fraudulent emails. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The primary goal of the XWorm 7.2 campaign is financial gain through data theft and ransomware. This is supported by the malware’s capabilities to steal credentials and deploy ransomware. However, the lack of specific financial demands in the snippet leaves uncertainty.
- Hypothesis B: The campaign aims to establish a broad network of compromised systems for future strategic cyber operations, such as DDoS attacks or espionage. This is supported by the malware’s modular nature and ability to conduct DDoS attacks. Contradicting evidence includes the immediate financial exploitation capabilities.
- Assessment: Hypothesis A is currently better supported due to the direct financial exploitation capabilities of XWorm 7.2. Indicators such as a shift towards more strategic targets or changes in malware functionality could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The malware’s primary distribution method is through email attachments; XWorm 7.2’s capabilities are accurately reported; the campaign’s reach is global given the multilingual email themes.
- Information Gaps: Specific geographic distribution of the attacks; detailed financial impact data; identification of threat actors behind the campaign.
- Bias & Deception Risks: Potential over-reliance on Fortinet’s analysis; possibility of threat actors using misinformation to mislead investigators.
4. Implications and Strategic Risks
This development could lead to increased cyber threats against businesses and individuals, potentially escalating into broader cyber conflicts if state actors are involved.
- Political / Geopolitical: Potential for increased tensions if linked to state-sponsored actors.
- Security / Counter-Terrorism: Heightened alert for cybersecurity defenses and potential for increased cybercrime.
- Cyber / Information Space: Enhanced focus on patch management and email security protocols.
- Economic / Social: Potential financial losses for affected entities and erosion of trust in digital communications.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase awareness and training on phishing threats; ensure all systems are patched against CVE-2018-0802.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing; enhance incident response capabilities.
- Scenario Outlook: Best: Rapid containment and patching reduce impact. Worst: Widespread infections lead to significant financial and operational disruptions. Most-Likely: Continued sporadic infections with moderate financial impact.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, malware, phishing, remote access trojan, ransomware, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us