Cybersecurity Concerns Rise as Open-Source AI Tools Expand Attack Surfaces and Machine Identities Surge
Published on: 2026-03-30
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: On theCUBE Pod RSAC raises alarms over open-source agents and KubeCons role changes in the wake of AI
1. BLUF (Bottom Line Up Front)
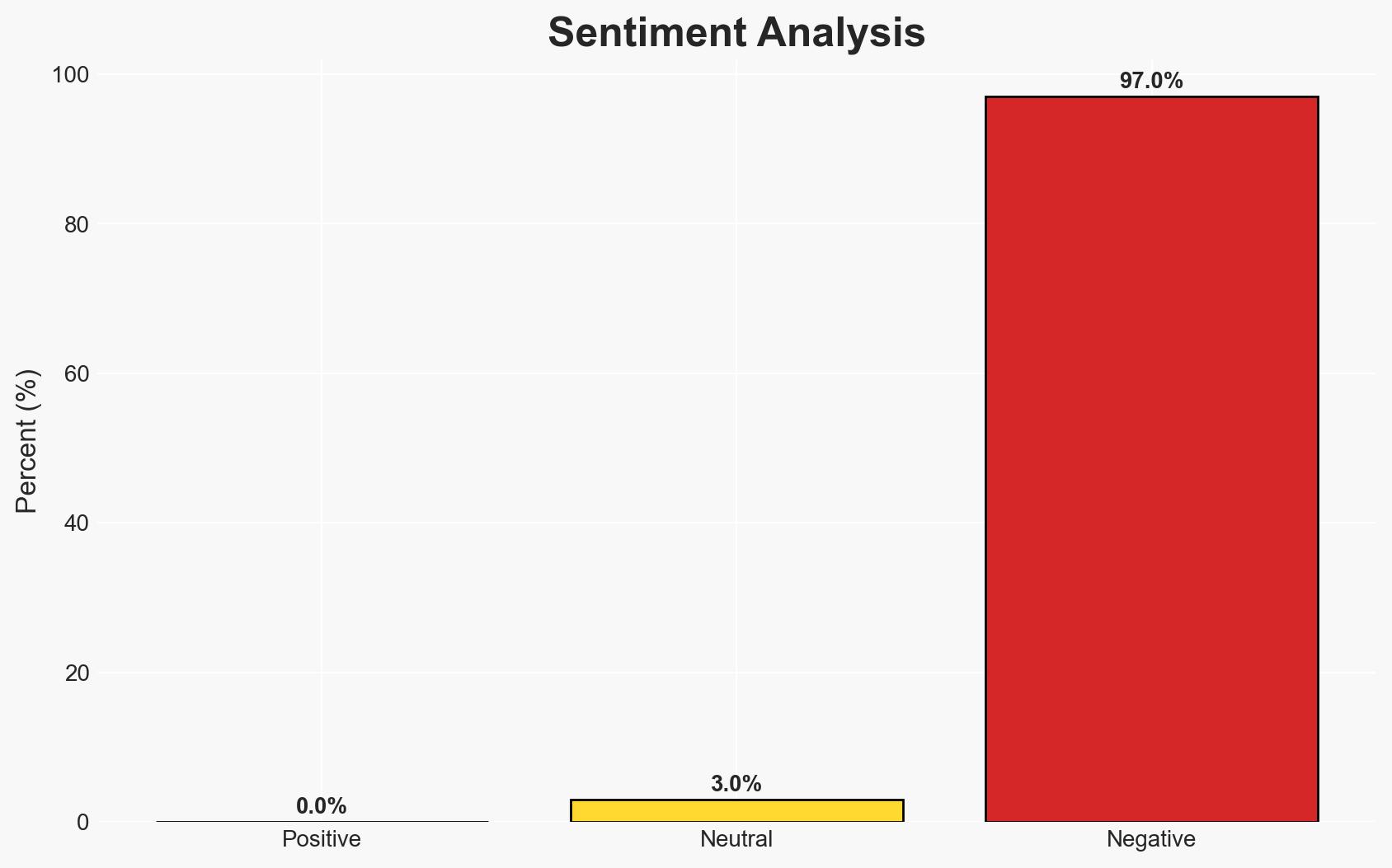
The proliferation of machine identities, driven by open-source AI agents like OpenClaw, presents a significant cybersecurity threat, with the potential to overwhelm current security frameworks. The risk is exacerbated by the rapid adoption of agentic AI, which could lead to increased vulnerabilities. Moderate confidence in this assessment due to the limited scope of available data and potential biases in source reporting.
2. Competing Hypotheses
- Hypothesis A: The rapid increase in machine identities and open-source AI agents will lead to a significant rise in cybersecurity threats, overwhelming existing security measures. Supporting evidence includes the reported outnumbering of human identities by machine identities and the discovery of malware within OpenClaw skills. Key uncertainties include the actual scale of adoption and effectiveness of current countermeasures.
- Hypothesis B: The cybersecurity community will adapt to the challenges posed by machine identities and agentic AI, mitigating potential threats through innovation and enhanced security protocols. This hypothesis is less supported due to the current lack of comprehensive solutions and the high level of concern expressed by cybersecurity experts.
- Assessment: Hypothesis A is currently better supported due to the immediate concerns raised by experts and the lack of effective countermeasures. Indicators that could shift this judgment include the development of robust security frameworks and successful mitigation of identified vulnerabilities.
3. Key Assumptions and Red Flags
- Assumptions: The number of machine identities will continue to grow exponentially; current security frameworks are inadequate to handle the new threats; open-source AI agents will remain a key vector for cyber threats.
- Information Gaps: Detailed data on the effectiveness of current security measures against machine identity threats; comprehensive analysis of the malware discovered within OpenClaw skills.
- Bias & Deception Risks: Potential bias in source reporting due to vested interests in promoting cybersecurity solutions; risk of underestimating the adaptability of cybersecurity measures.
4. Implications and Strategic Risks
The unchecked growth of machine identities and agentic AI could lead to significant disruptions in cybersecurity, with potential spillover effects in various domains.
- Political / Geopolitical: Increased cyber threats could strain international relations, particularly if state actors are implicated in exploiting vulnerabilities.
- Security / Counter-Terrorism: Enhanced capabilities for cyber-terrorism and espionage, potentially leading to increased state and non-state actor activity.
- Cyber / Information Space: Greater complexity in managing digital identities and securing communications, with potential for widespread data breaches.
- Economic / Social: Potential economic disruptions due to increased cybersecurity costs and loss of trust in digital systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive review of current cybersecurity measures; prioritize the development of machine identity management protocols.
- Medium-Term Posture (1–12 months): Invest in research and development for advanced security solutions; establish partnerships with tech companies to enhance threat intelligence sharing.
- Scenario Outlook:
- Best: Rapid development of effective security solutions mitigates threats.
- Worst: Widespread cyber-attacks lead to significant economic and social disruptions.
- Most-Likely: Gradual adaptation to new threats with intermittent security breaches.
6. Key Individuals and Entities
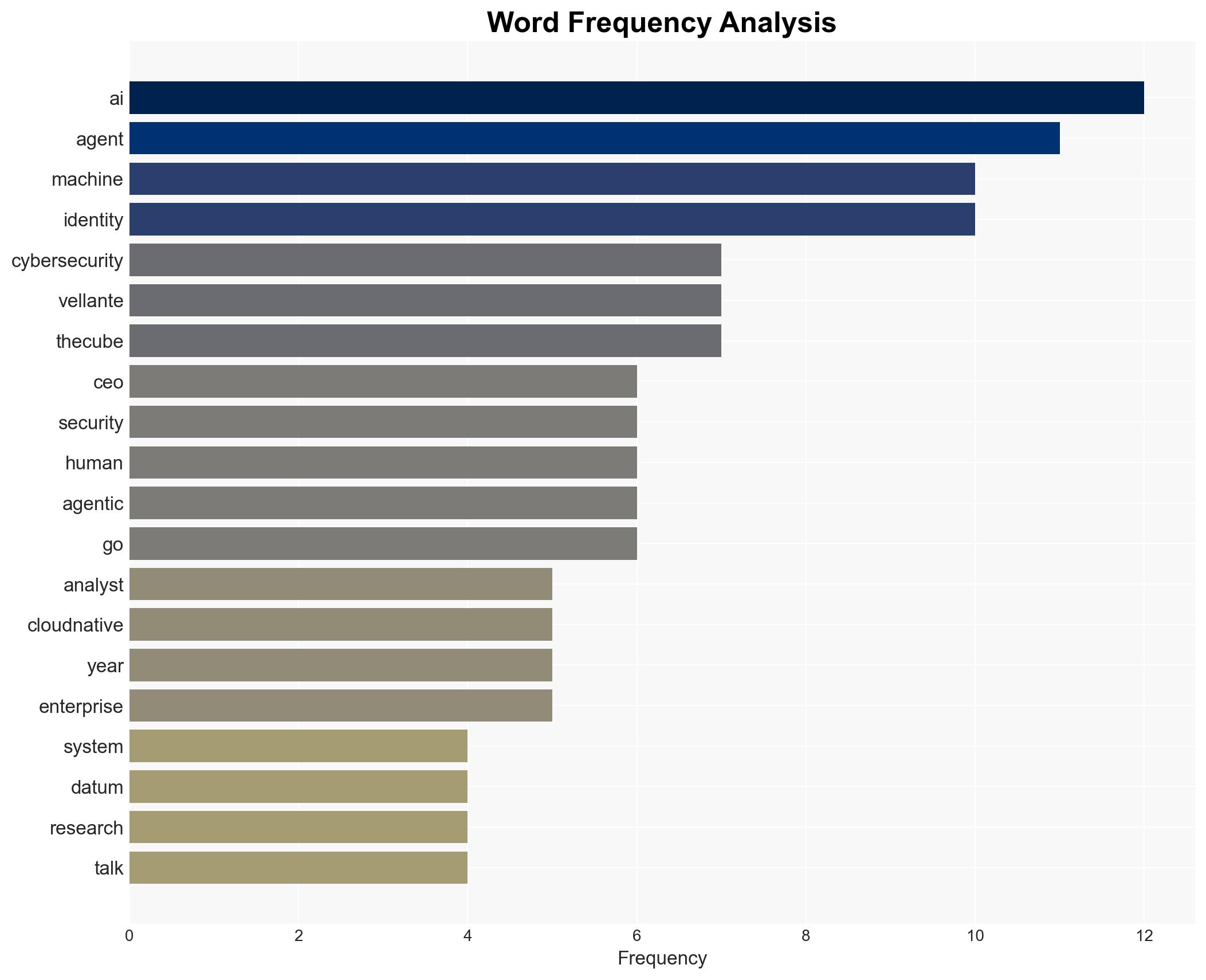
- Jensen Huang, Nvidia Corp. CEO
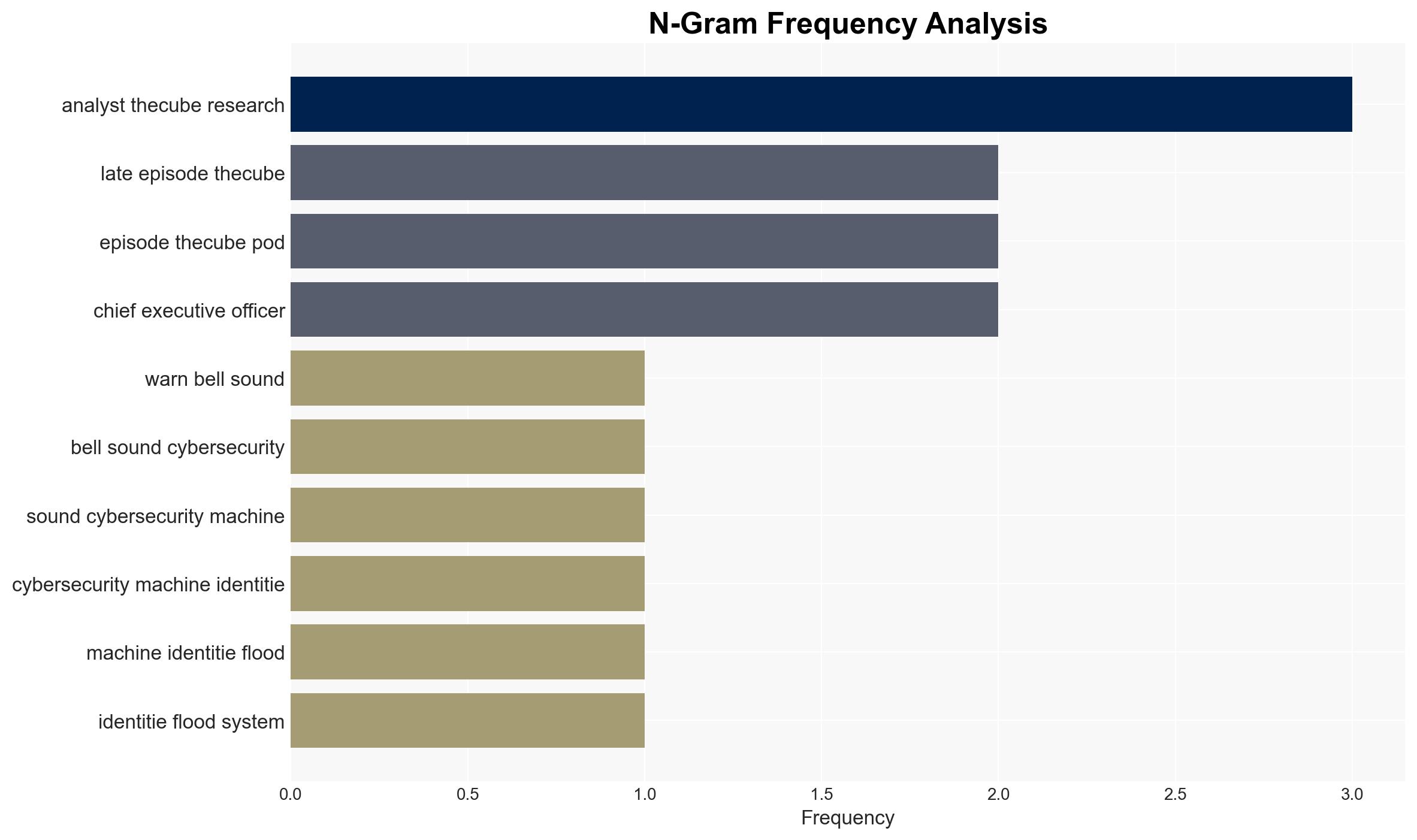
- Dave Vellante, Chief Analyst for theCUBE Research
- John Furrier, Executive Analyst for theCUBE Research
- Google (as a corporate entity)
7. Thematic Tags
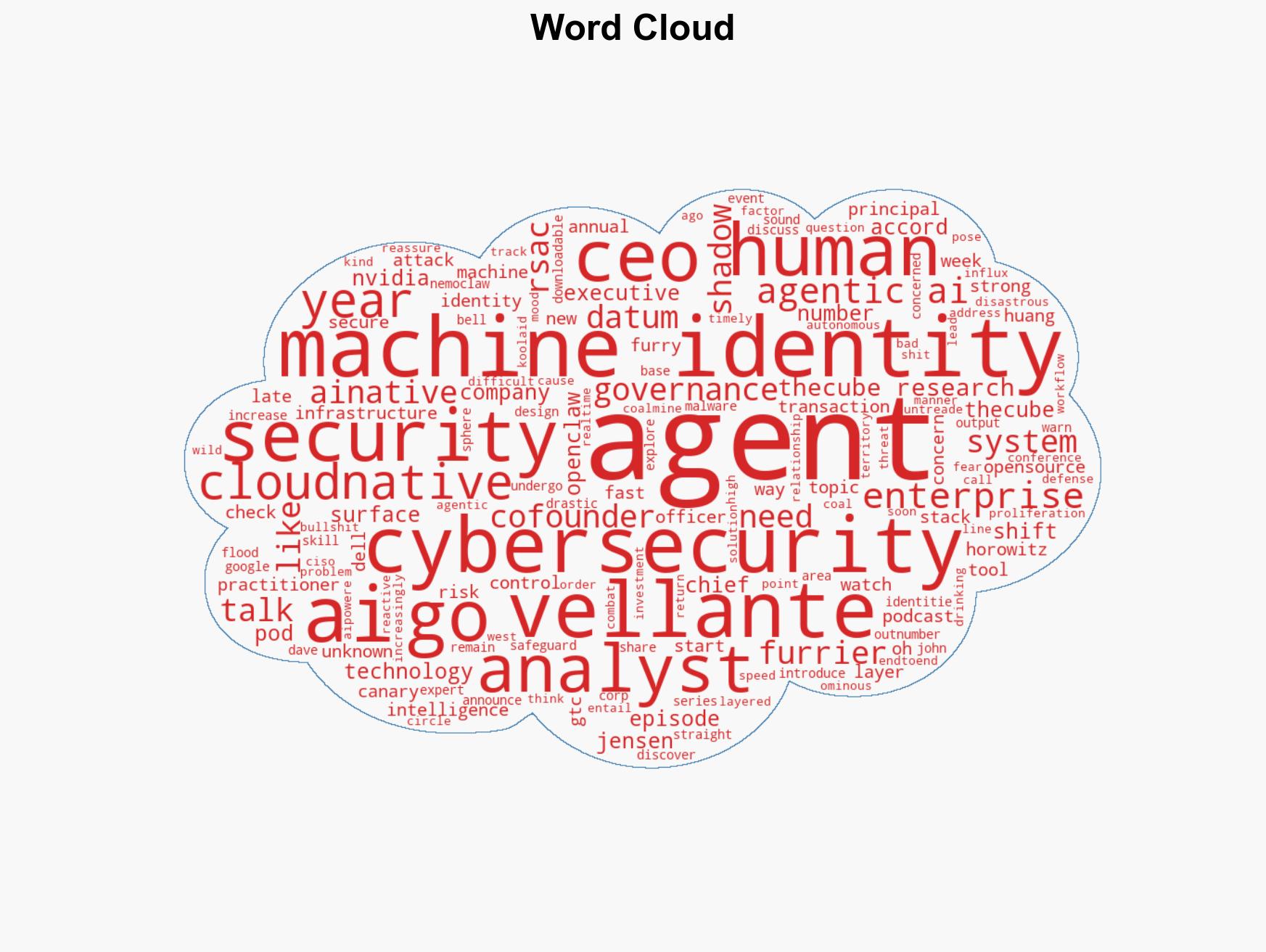
cybersecurity, machine identities, open-source AI, agentic AI, cyber threats, malware, digital security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us