Cybersecurity Experts Uncover 1Campaign, a Tool Enabling Hackers to Evade Google Ad Review Systems
Published on: 2026-02-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Hackers Use 1Campaign to Hide Malicious Ads From Google Reviewers
1. BLUF (Bottom Line Up Front)
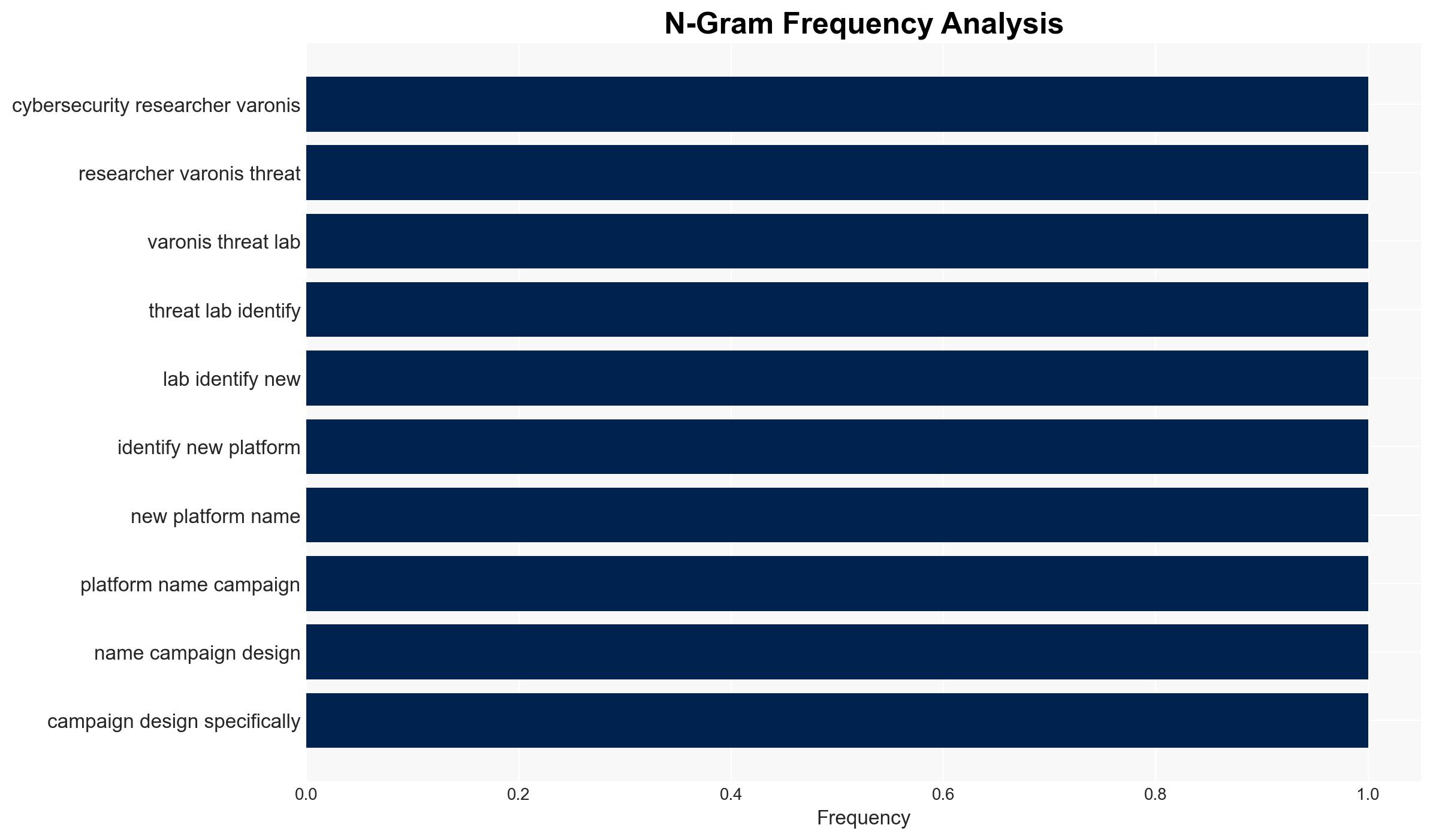
The 1Campaign platform enables cybercriminals to bypass Google’s security systems using cloaking techniques, posing a significant threat to online advertising integrity and user security. This development primarily affects users in the US, UK, Netherlands, China, and Germany. The most likely hypothesis is that 1Campaign will continue to facilitate malvertising attacks, with moderate confidence in this assessment due to the platform’s established presence and sophistication.
2. Competing Hypotheses
- Hypothesis A: 1Campaign is primarily used for financial gain through cryptocurrency theft and phishing. This is supported by the platform’s focus on malvertising and evidence of targeted attacks on financial sites. However, the full scope of its use is unclear, with potential for broader applications.
- Hypothesis B: 1Campaign is a multi-purpose tool used for various cybercriminal activities beyond financial theft, including espionage or data harvesting. While the platform’s capabilities suggest versatility, current evidence predominantly links it to financial scams.
- Assessment: Hypothesis A is currently better supported due to the direct evidence of financial targeting and the platform’s design to exploit Google Ads. Indicators such as shifts in target profiles or new functionalities could support Hypothesis B.
3. Key Assumptions and Red Flags
- Assumptions: 1) The platform’s primary goal is financial gain. 2) Google’s security measures are insufficient against current cloaking techniques. 3) The developer, DuppyMeister, is actively maintaining and updating the platform.
- Information Gaps: Details on the full range of 1Campaign’s capabilities and the identity and motivations of its developer.
- Bias & Deception Risks: Potential bias in source reporting due to reliance on cybersecurity firm analysis; deception risk from cloaking techniques that may obscure true intent.
4. Implications and Strategic Risks
The continued operation of 1Campaign could lead to increased financial losses and erosion of trust in online advertising platforms, potentially prompting stricter regulatory measures.
- Political / Geopolitical: Potential for international tensions if state actors are implicated or if attacks are perceived as originating from specific countries.
- Security / Counter-Terrorism: Increased cyber threat landscape complexity, requiring enhanced monitoring and response capabilities.
- Cyber / Information Space: Potential for widespread misinformation campaigns using similar techniques, complicating digital trust and verification processes.
- Economic / Social: Economic impact on affected businesses and potential loss of consumer confidence in digital platforms.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Google Ads for cloaking techniques, collaborate with cybersecurity firms for intelligence sharing, and raise public awareness about malvertising risks.
- Medium-Term Posture (1–12 months): Develop and implement stricter ad verification processes, invest in advanced detection technologies, and foster international cooperation to address cross-border cyber threats.
- Scenario Outlook: Best: 1Campaign is dismantled through coordinated international efforts. Worst: Platform evolves, increasing attack sophistication. Most-Likely: Continued use with gradual improvements in detection and mitigation.
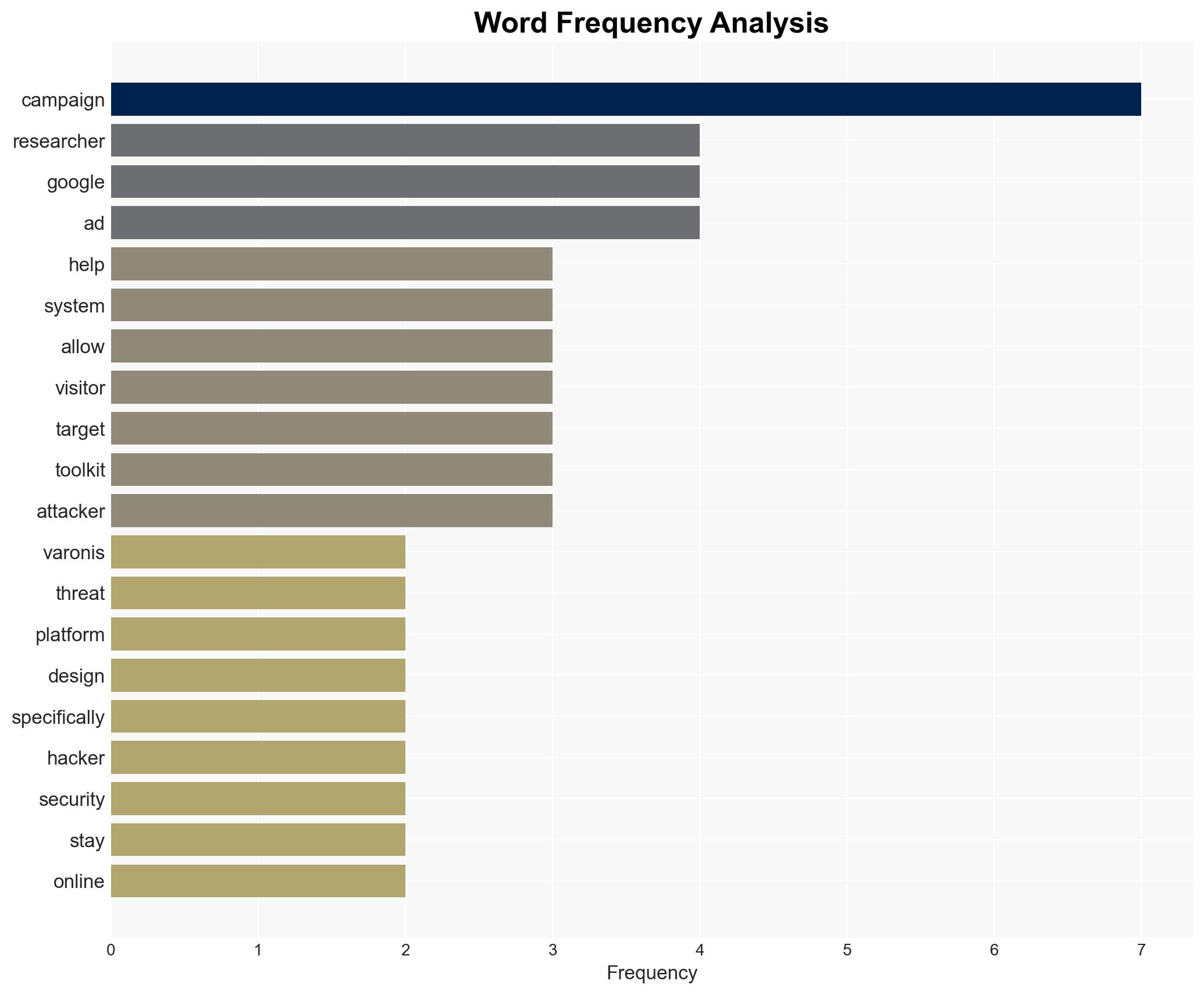
6. Key Individuals and Entities
- DuppyMeister (Developer of 1Campaign)
- Varonis Threat Labs (Cybersecurity researchers)
- Google (Target of cloaking techniques)
- Daniel Kelley (Researcher involved in the study)
7. Thematic Tags
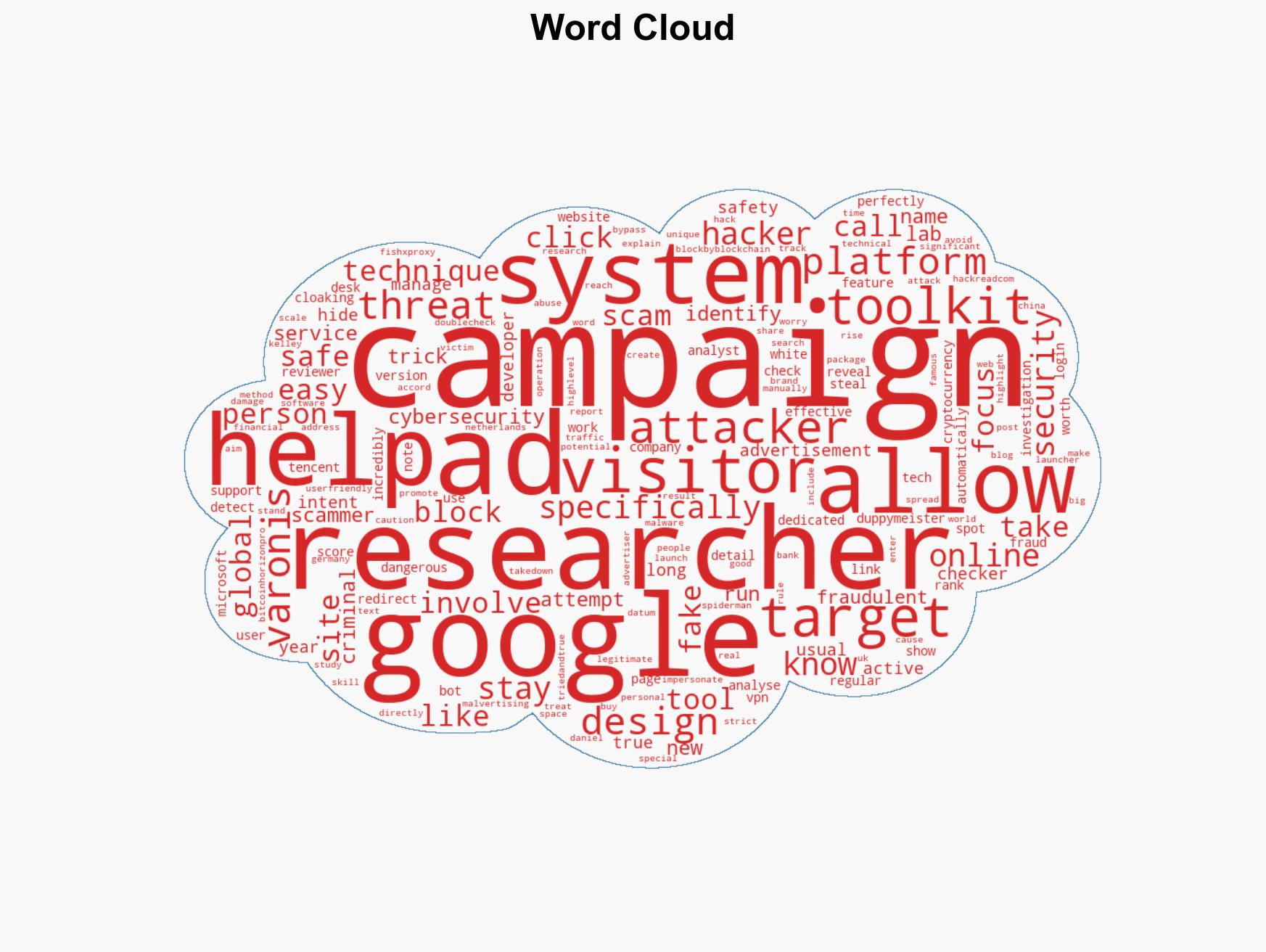
cybersecurity, malvertising, cloaking techniques, online fraud, Google Ads, financial scams, cybercrime tools
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us