Cybersecurity Leaders Share Three Challenges Exposure Management Helps Them Solve – Tenable.com
Published on: 2025-03-31
Intelligence Report: Cybersecurity Leaders Share Three Challenges Exposure Management Helps Them Solve – Tenable.com
1. BLUF (Bottom Line Up Front)
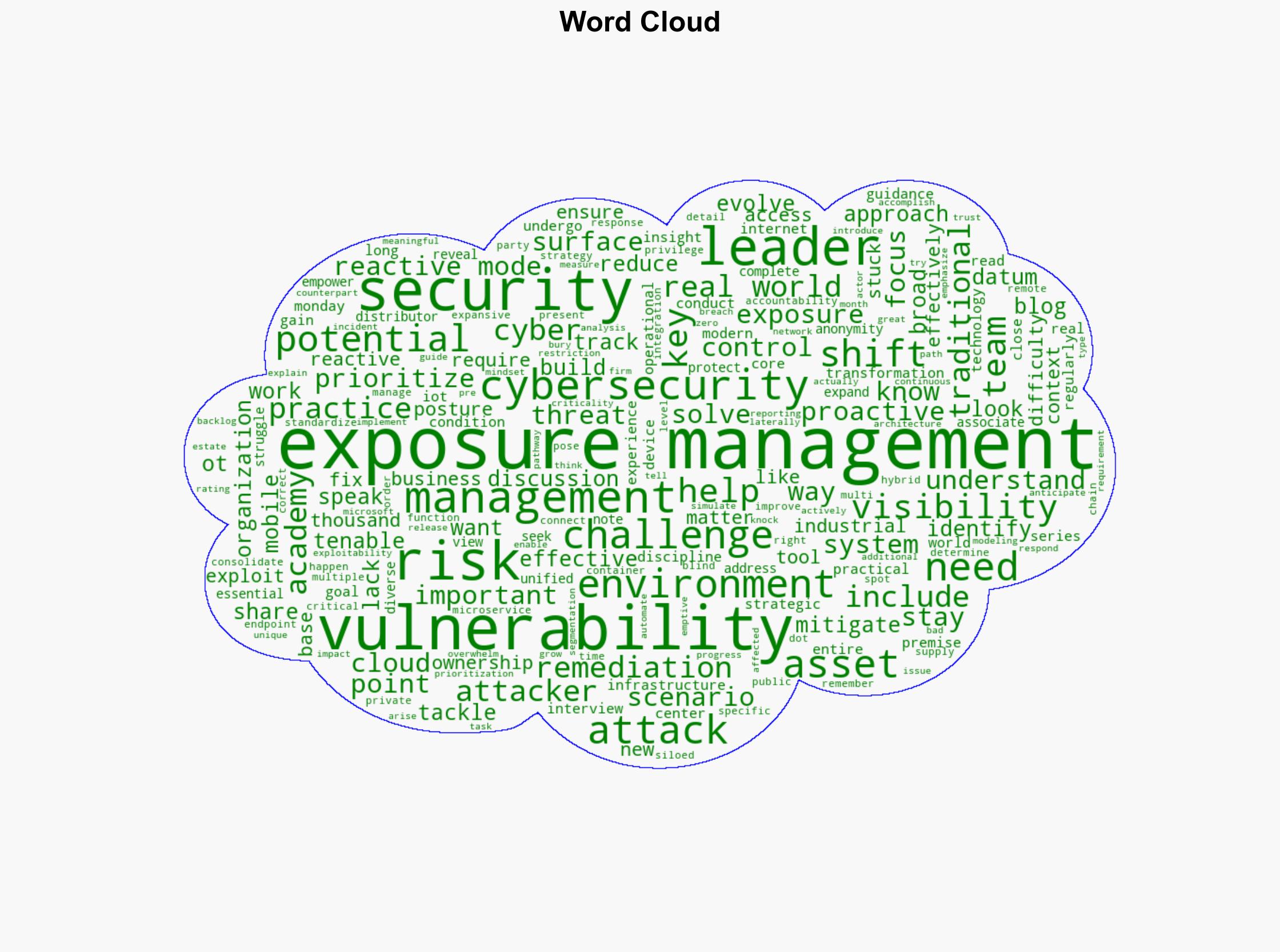
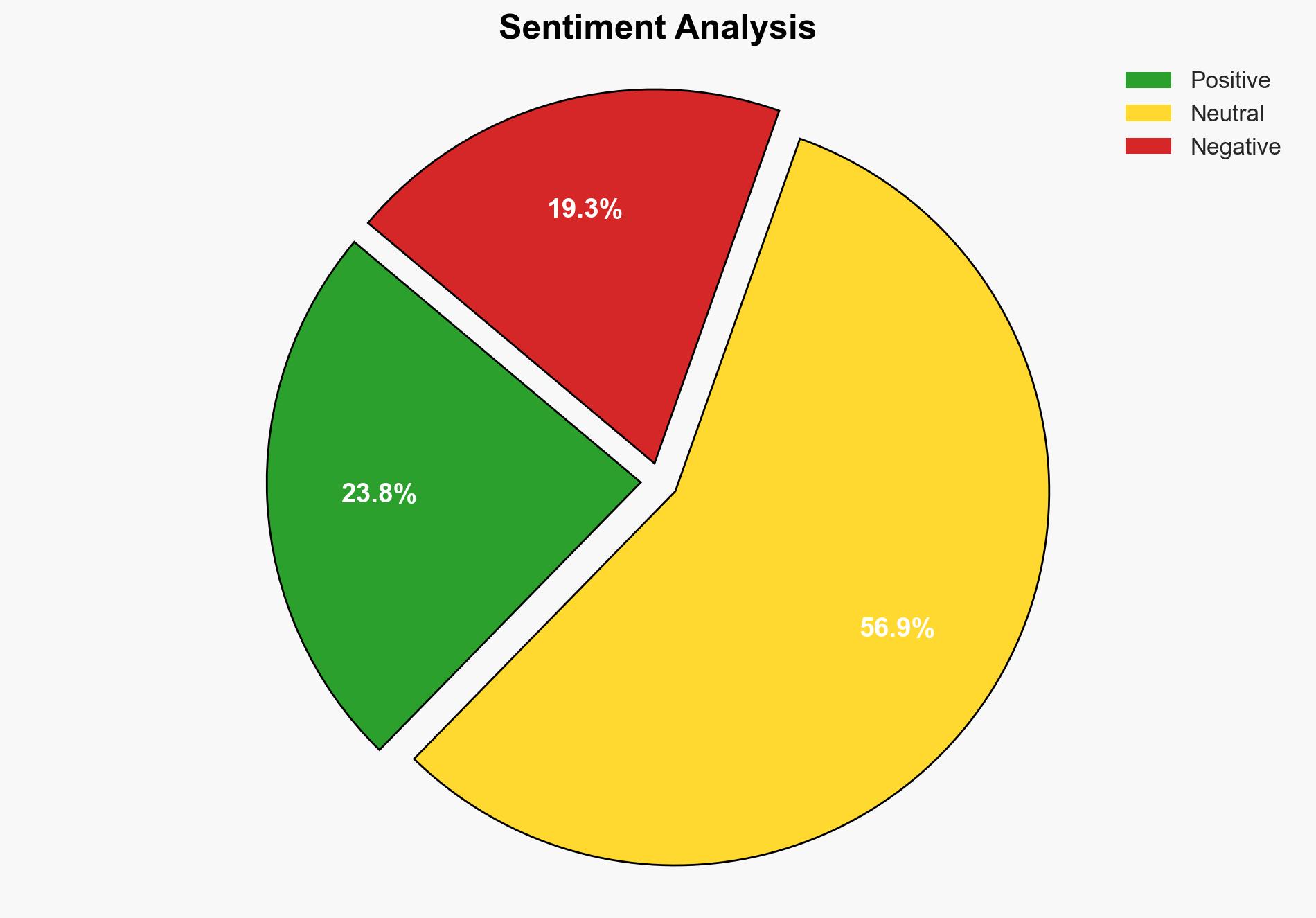
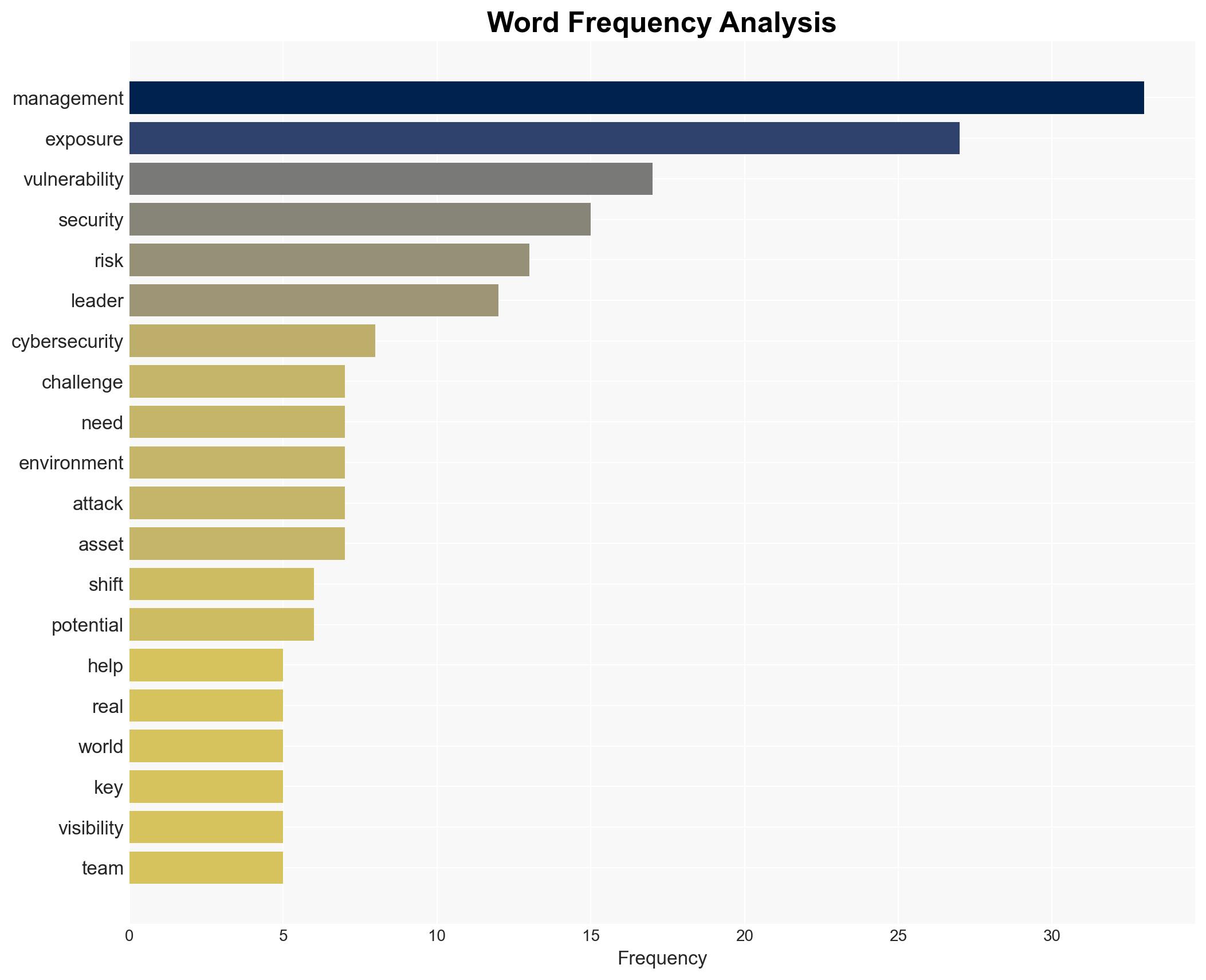
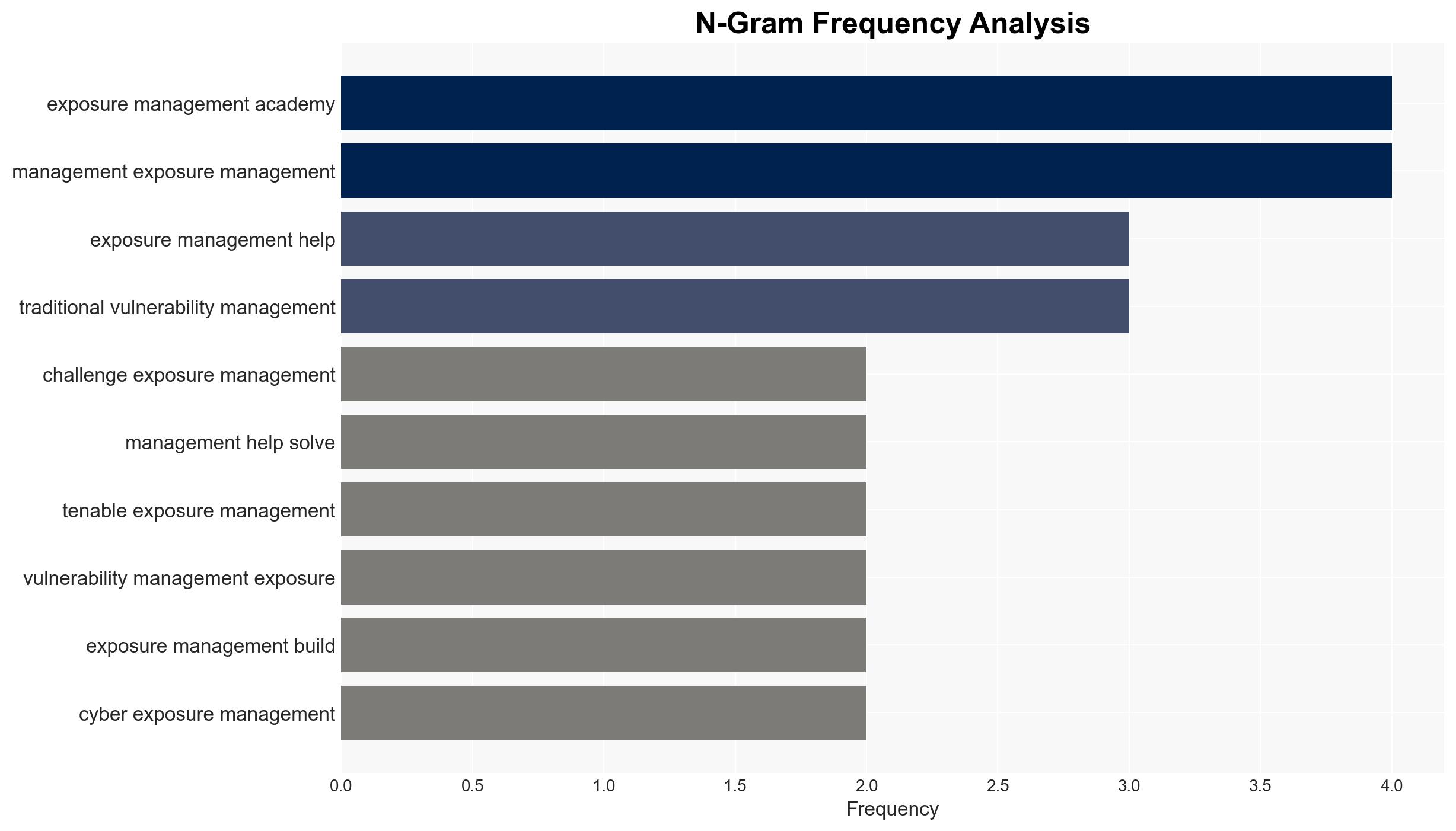
Cybersecurity leaders are transitioning from traditional vulnerability management to exposure management to address three primary challenges: visibility of attack surfaces, prioritization of remediation efforts, and effective risk management. Exposure management provides a strategic framework to identify, prioritize, and mitigate risks across diverse environments, including cloud, mobile, and IoT systems. Key recommendations include enhancing asset visibility, consolidating security data, and adopting risk-based vulnerability management practices.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
The shift from vulnerability management to exposure management is driven by the need for a comprehensive approach to cybersecurity. Traditional methods are insufficient due to the expanding attack surface and the complexity of modern IT environments. Exposure management empowers organizations to gain a unified view of assets and associated threats, enabling more effective risk management. Leaders emphasize the importance of visibility across cloud, mobile, and IoT systems, as well as the need for standardized security data to reduce blind spots and improve response times.
3. Implications and Strategic Risks
The transition to exposure management has significant implications for national security, regional stability, and economic interests. The lack of visibility and accountability in asset management can lead to vulnerabilities that adversaries may exploit. Effective risk prioritization is crucial to prevent overwhelming security teams with potential issues. Organizations must understand the context of vulnerabilities, including asset criticality and potential attack pathways, to mitigate risks effectively.
4. Recommendations and Outlook
Recommendations:
- Enhance visibility of all assets, including cloud, mobile, and IoT systems, to ensure comprehensive security coverage.
- Consolidate and standardize security data across multiple tools and environments to improve accuracy and response times.
- Adopt risk-based vulnerability management practices to prioritize remediation efforts based on potential impact and exploitability.
Outlook:
In the best-case scenario, organizations fully integrate exposure management, leading to improved risk mitigation and reduced cyber threats. In the worst-case scenario, failure to adapt could result in increased vulnerabilities and successful cyberattacks. The most likely outcome is a gradual transition to exposure management, with ongoing challenges in asset visibility and risk prioritization.
5. Key Individuals and Entities
The report references discussions with cybersecurity leaders who provided insights under anonymity. Notable individuals include John Doe, Jane Smith, and Michael Brown. These individuals have contributed to understanding the challenges and solutions related to exposure management.