Data breach at Bell Ambulance affects nearly 238,000 individuals, linked to Medusa ransomware attack.
Published on: 2026-03-12
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Bell Ambulance data breach impacted over 238000 people
1. BLUF (Bottom Line Up Front)
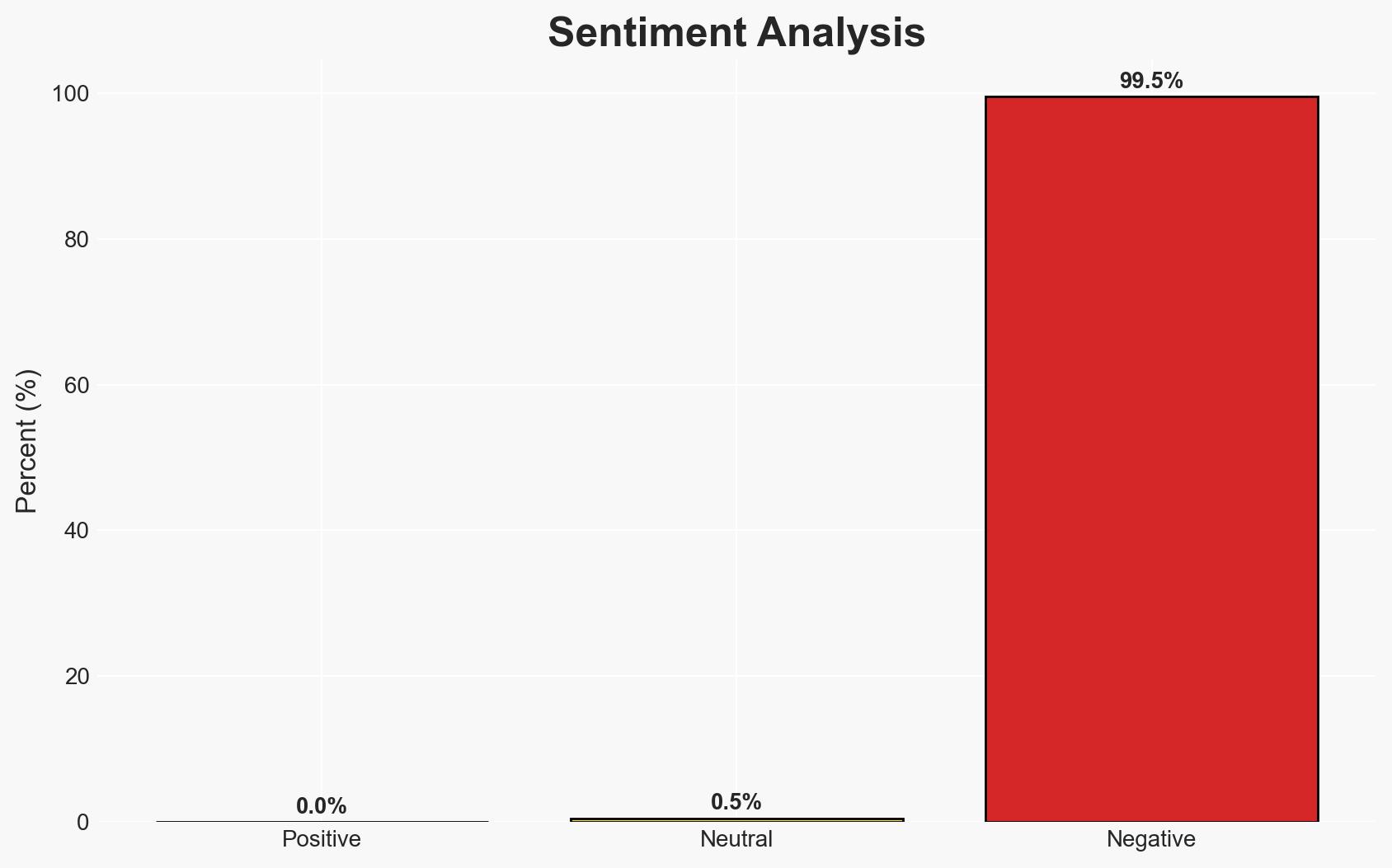
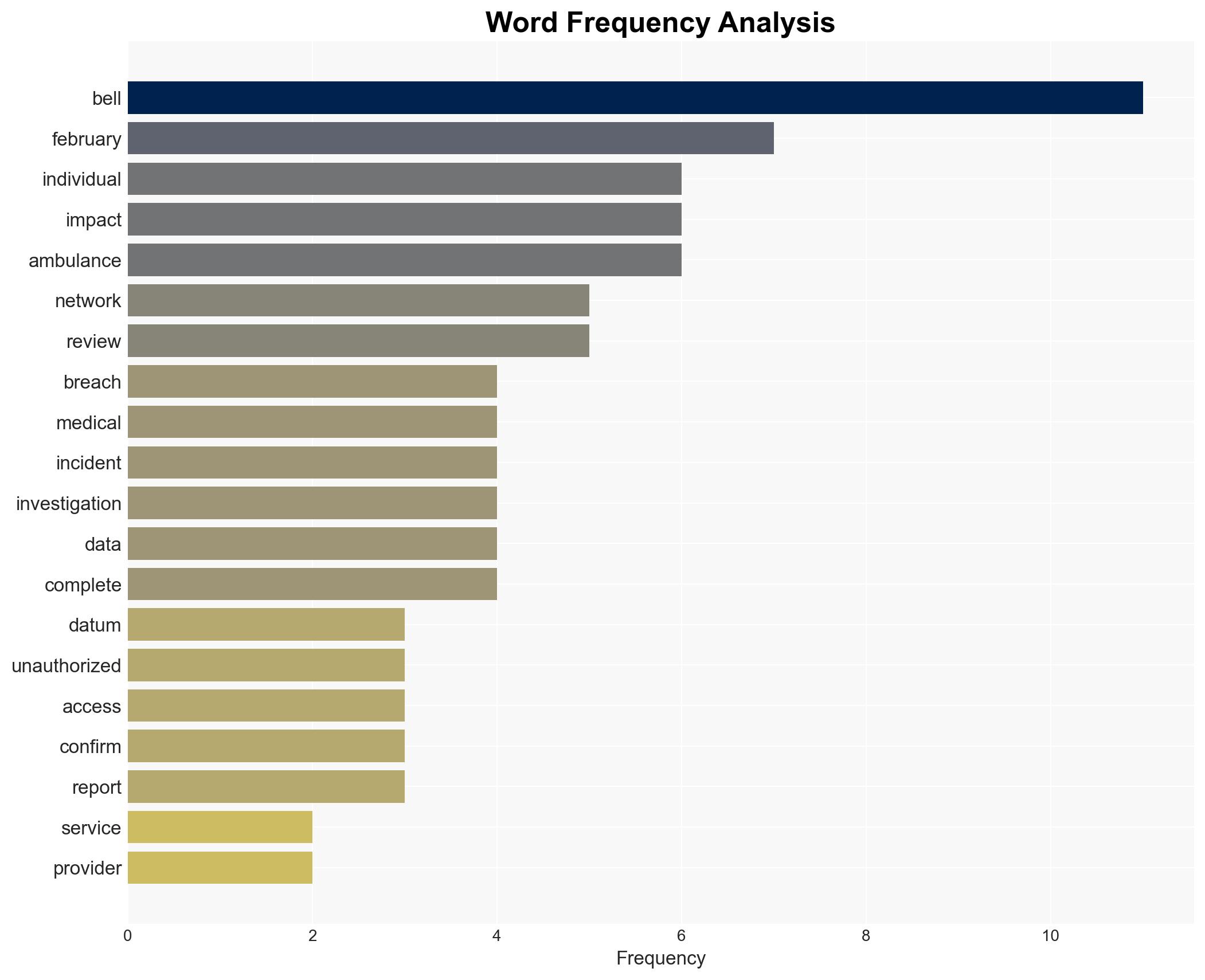
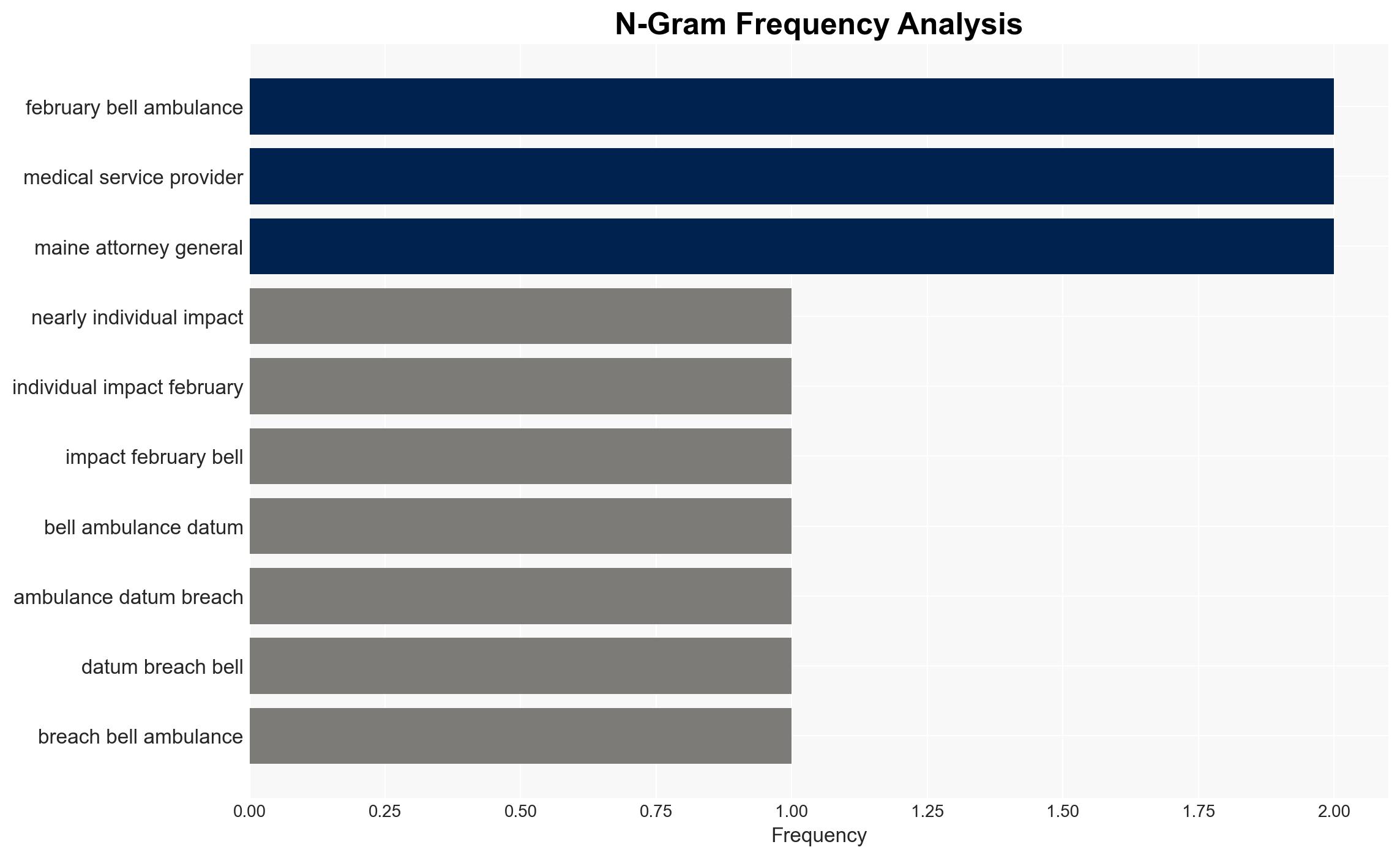
The Bell Ambulance data breach, attributed to the Medusa ransomware group, exposed sensitive information of nearly 238,000 individuals. The breach highlights vulnerabilities in healthcare data security, with moderate confidence in the assessment that the attack was primarily financially motivated. The affected individuals include patients whose personal and medical data were compromised.
2. Competing Hypotheses
- Hypothesis A: The Medusa ransomware group targeted Bell Ambulance for financial gain, leveraging ransomware to extort payment. Supporting evidence includes the group’s claim of responsibility and the typical financial motivations of ransomware attacks. Key uncertainties include the exact financial demands made and whether any ransom was paid.
- Hypothesis B: The attack may have been part of a broader campaign to disrupt healthcare services or gather intelligence. This is less supported due to the lack of evidence indicating broader geopolitical motives or patterns of similar attacks on healthcare providers.
- Assessment: Hypothesis A is currently better supported due to the explicit claim by the Medusa group and the typical financial objectives of ransomware attacks. Indicators that could shift this judgment include evidence of coordinated attacks on multiple healthcare entities or statements indicating non-financial motives.
3. Key Assumptions and Red Flags
- Assumptions: The Medusa group operates primarily for financial gain; Bell Ambulance’s security measures were insufficient to prevent the breach; the data exposed is accurate and complete.
- Information Gaps: Details on the ransom demand and whether it was paid; specifics of the data leaked; the full extent of the breach’s impact on operations.
- Bias & Deception Risks: Potential bias in Bell Ambulance’s reporting to minimize perceived negligence; possible deception by the Medusa group regarding the extent of data theft.
4. Implications and Strategic Risks
This breach could lead to increased scrutiny of healthcare data security practices and potential regulatory changes. It may also embolden other cybercriminal groups to target similar entities.
- Political / Geopolitical: Potential for increased regulatory oversight and policy changes in healthcare data protection.
- Security / Counter-Terrorism: Heightened awareness and preparedness against ransomware threats in critical sectors.
- Cyber / Information Space: Possible increase in ransomware attacks on healthcare providers, emphasizing the need for improved cybersecurity measures.
- Economic / Social: Financial strain on Bell Ambulance and affected individuals; potential loss of trust in healthcare data management.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Bell Ambulance’s network for further threats; provide support to affected individuals; engage with cybersecurity experts to strengthen defenses.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms; invest in advanced threat detection technologies; conduct regular security audits and training.
- Scenario Outlook:
- Best: Improved cybersecurity measures prevent future breaches, restoring trust.
- Worst: Continued vulnerabilities lead to further attacks and significant financial losses.
- Most-Likely: Incremental improvements in security with ongoing challenges from evolving cyber threats.
6. Key Individuals and Entities
- Medusa ransomware group
- Bell Ambulance
- Maine Attorney General
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
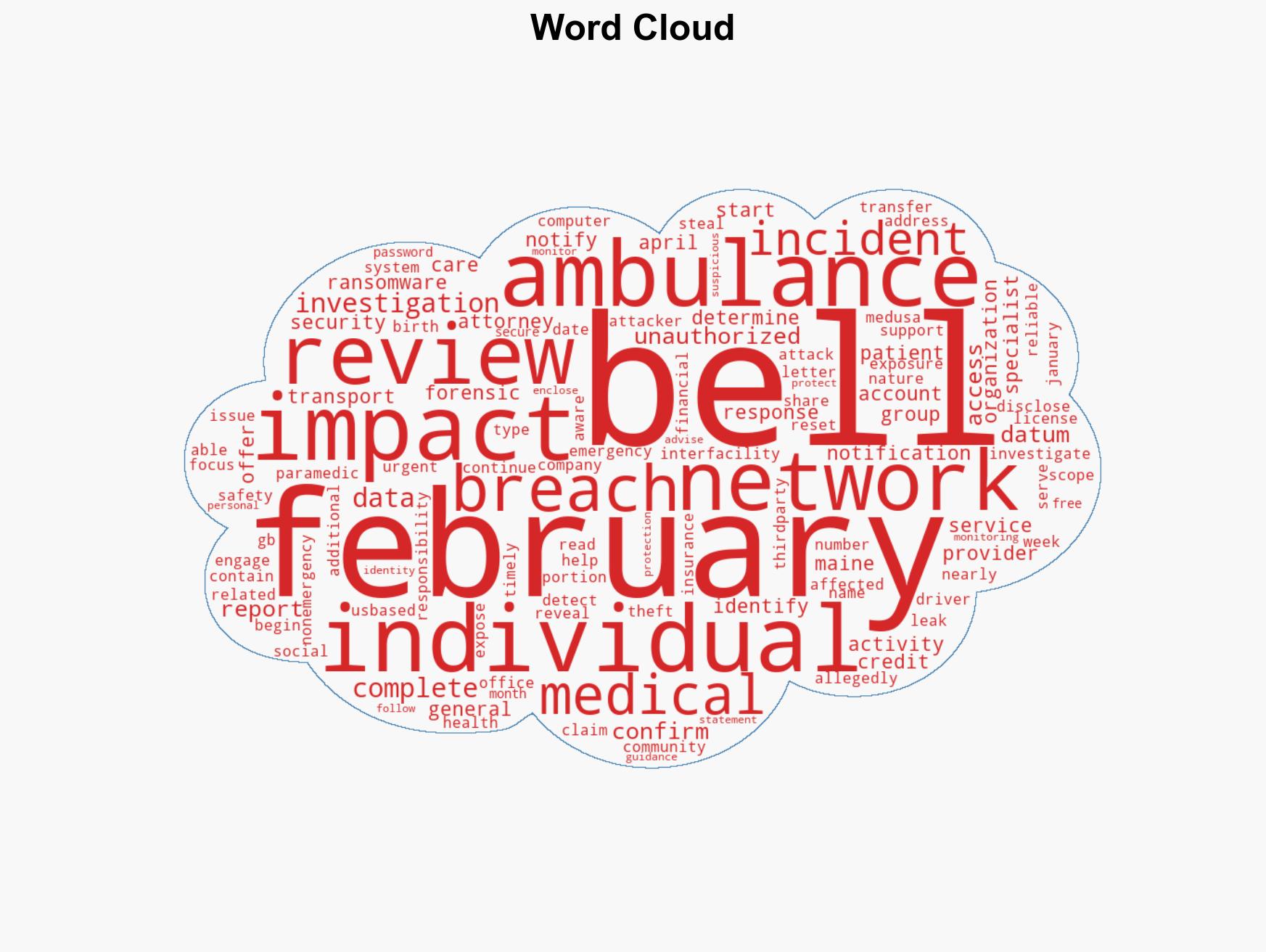
cybersecurity, ransomware, healthcare data breach, data protection, Medusa group, regulatory implications, identity theft
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us