Data breach at Cognizant’s TriZetto Provider Solutions affects over 3.4 million patients’ personal information
Published on: 2026-03-09
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Cognizants TriZetto Provider Solutions data breach impacted over 34 million patients
1. BLUF (Bottom Line Up Front)
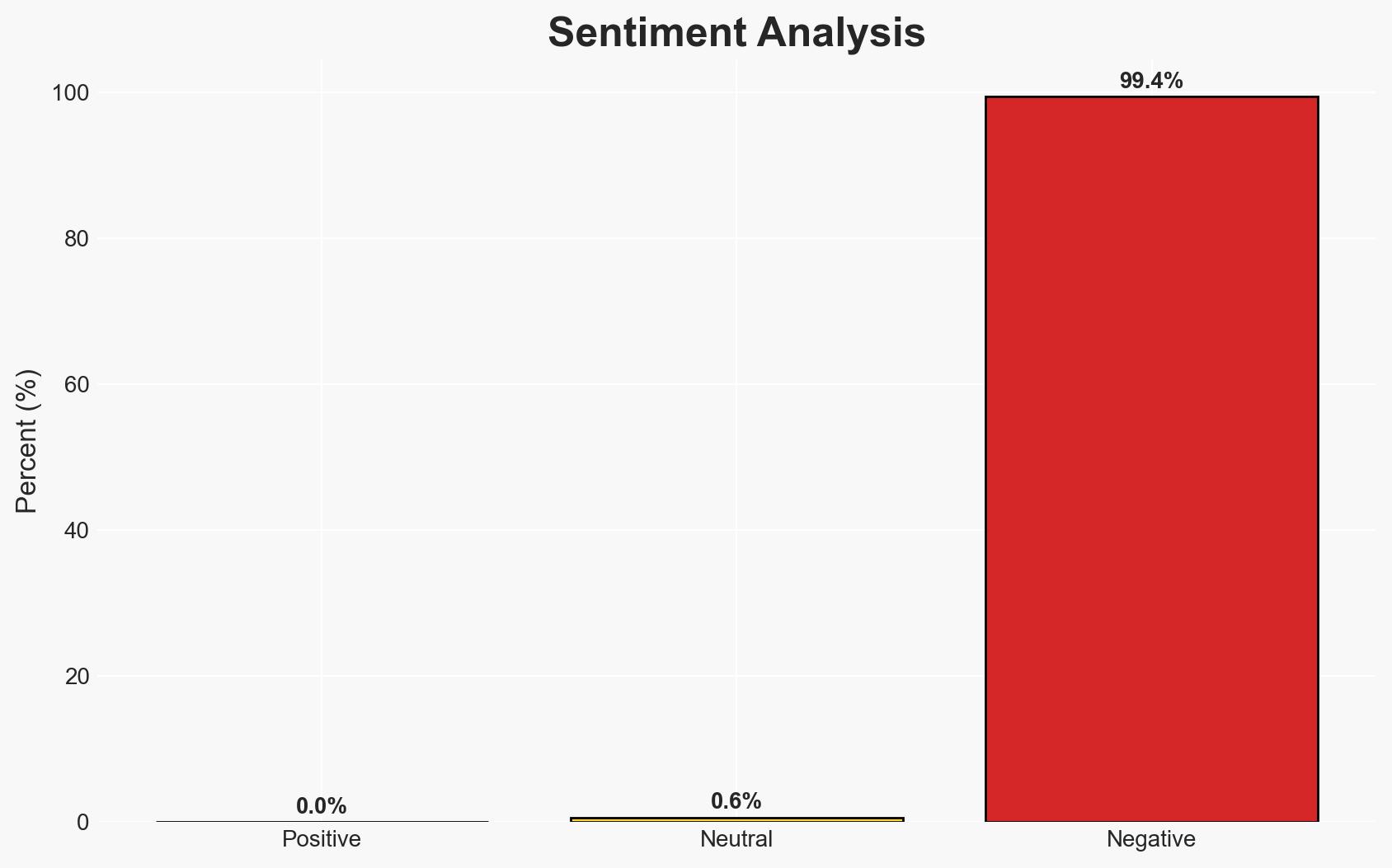
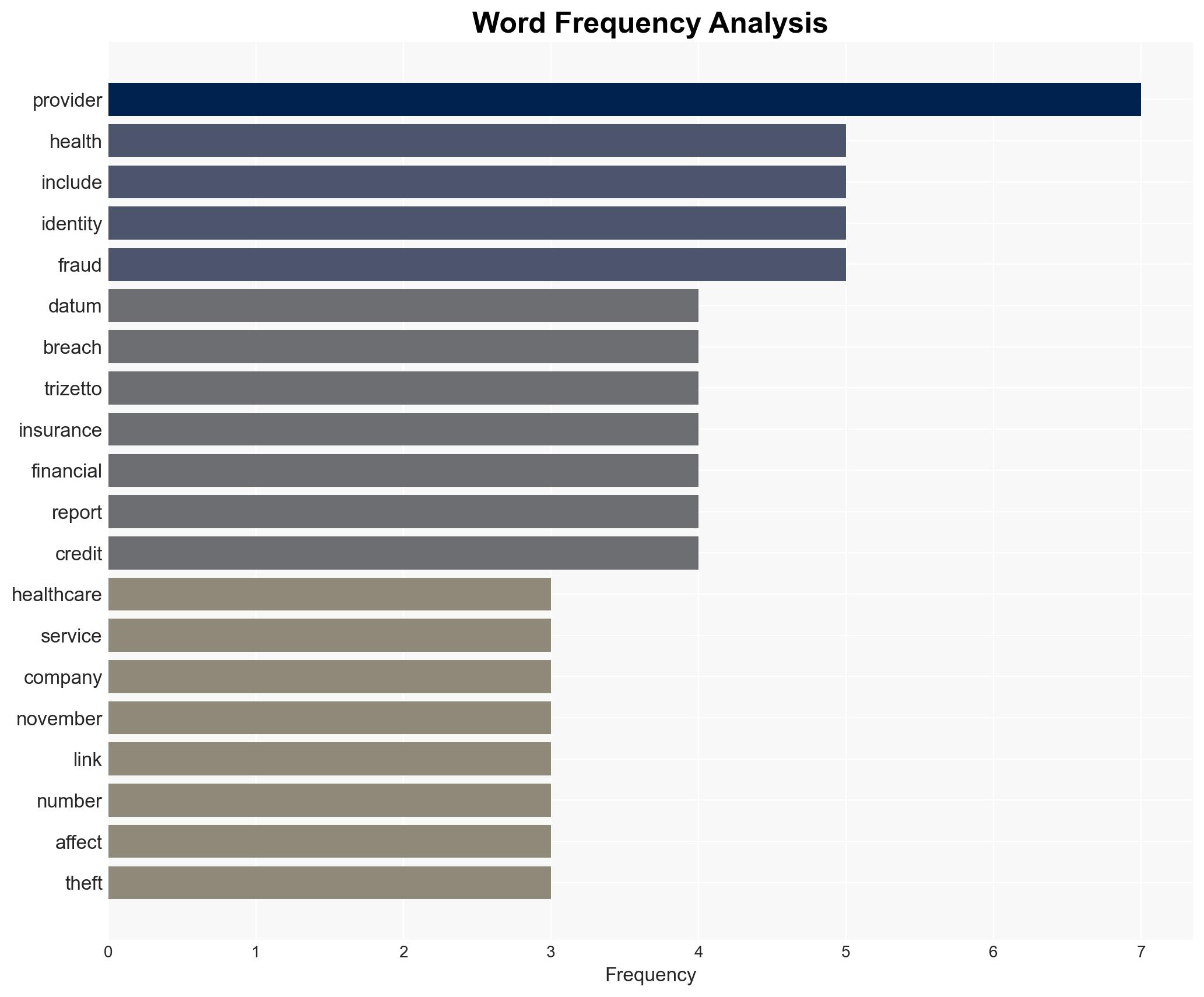
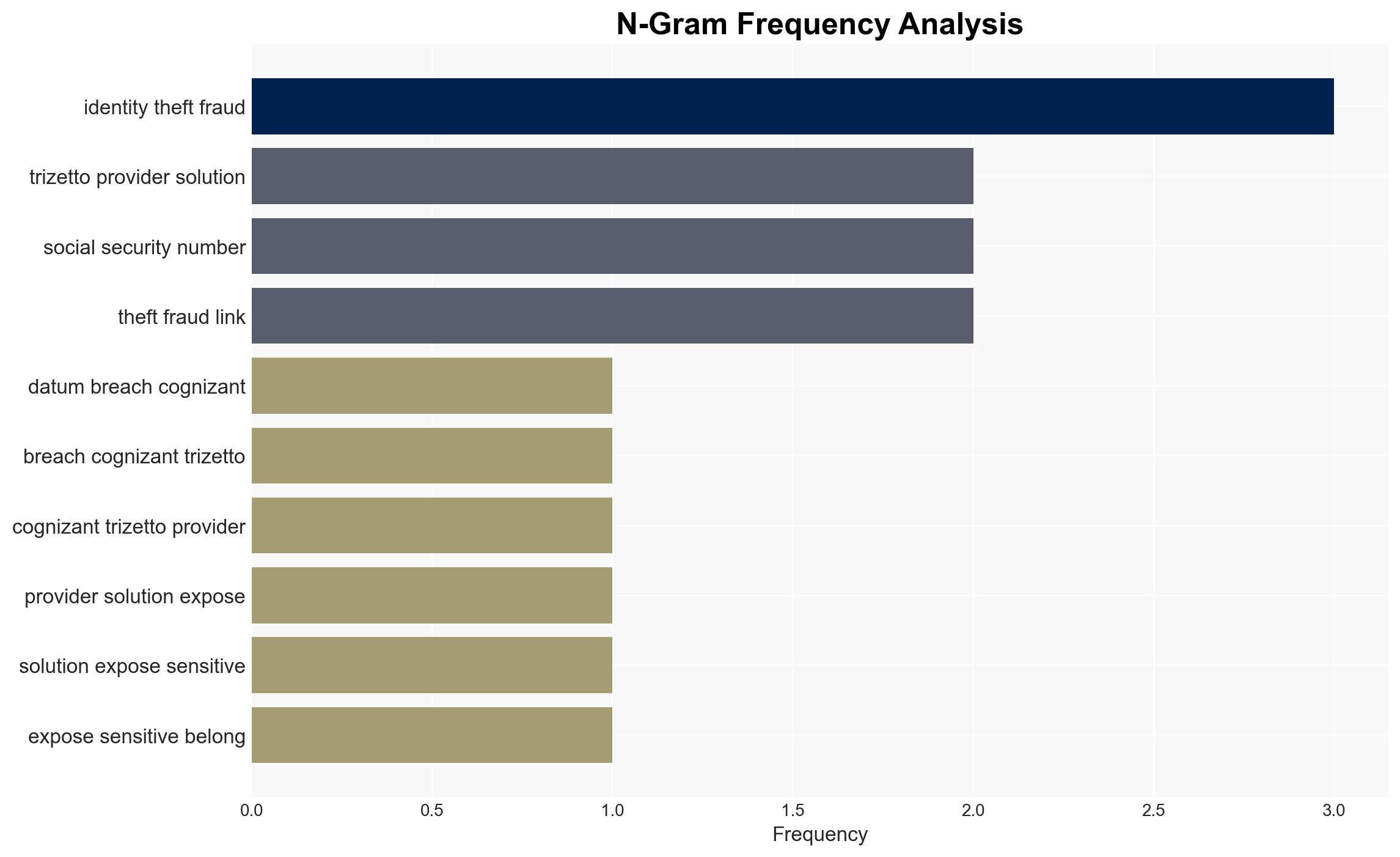
The data breach at Cognizant’s TriZetto Provider Solutions exposed sensitive information of over 34 million patients, with no current evidence of identity theft or fraud. The breach, undetected for nearly a year, highlights significant vulnerabilities in healthcare data security. The most likely hypothesis is an opportunistic cyber intrusion by an unauthorized actor. Overall confidence in this assessment is moderate due to existing information gaps.
2. Competing Hypotheses
- Hypothesis A: The breach was conducted by an opportunistic cybercriminal exploiting vulnerabilities in TriZetto’s systems. This is supported by the lack of a ransomware claim and the extended period of unauthorized access. Uncertainties include the absence of a clear motive or attribution to a known group.
- Hypothesis B: The breach was a targeted attack by a sophisticated actor aiming to collect healthcare data for espionage or strategic purposes. This is less supported due to the lack of sophisticated tactics typically associated with state-sponsored attacks and no evidence of data misuse.
- Assessment: Hypothesis A is currently better supported due to the opportunistic nature of the breach and the absence of sophisticated indicators. Key indicators that could shift this judgment include evidence of data misuse or attribution to a known threat actor.
3. Key Assumptions and Red Flags
- Assumptions: The breach was not financially motivated; the absence of fraud reports indicates limited immediate impact; TriZetto’s security measures were insufficient to prevent the breach.
- Information Gaps: Lack of detailed forensic analysis results; unknown identity of the perpetrator; unclear if data has been sold or used maliciously.
- Bias & Deception Risks: Potential bias in underestimating the sophistication of the attacker; reliance on TriZetto’s internal reporting may obscure external perspectives.
4. Implications and Strategic Risks
This breach underscores vulnerabilities in healthcare data security, potentially prompting regulatory scrutiny and increased cybersecurity investments. The incident could lead to heightened awareness and policy changes within the healthcare sector.
- Political / Geopolitical: Potential for increased regulatory actions and international cooperation on cybersecurity standards.
- Security / Counter-Terrorism: No immediate counter-terrorism implications, but highlights risks of data breaches being exploited by malicious actors.
- Cyber / Information Space: May spur advancements in healthcare cybersecurity practices and technologies.
- Economic / Social: Could impact public trust in healthcare data management and lead to economic costs related to breach mitigation and identity protection services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive forensic analysis to identify the breach vector; enhance monitoring and detection capabilities; engage with law enforcement and intelligence agencies for threat attribution.
- Medium-Term Posture (1–12 months): Strengthen cybersecurity frameworks and incident response plans; invest in employee training and awareness; develop partnerships with cybersecurity firms for ongoing threat intelligence.
- Scenario Outlook:
- Best: No further data misuse is detected, and security measures prevent future breaches.
- Worst: Data is sold on the dark web, leading to widespread identity theft and regulatory penalties.
- Most-Likely: Increased cybersecurity measures mitigate immediate risks, but ongoing vigilance is required.
6. Key Individuals and Entities
- TriZetto Provider Solutions
- Cognizant
- Kroll (identity protection and fraud remediation firm)
- Maine Attorney General Office
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
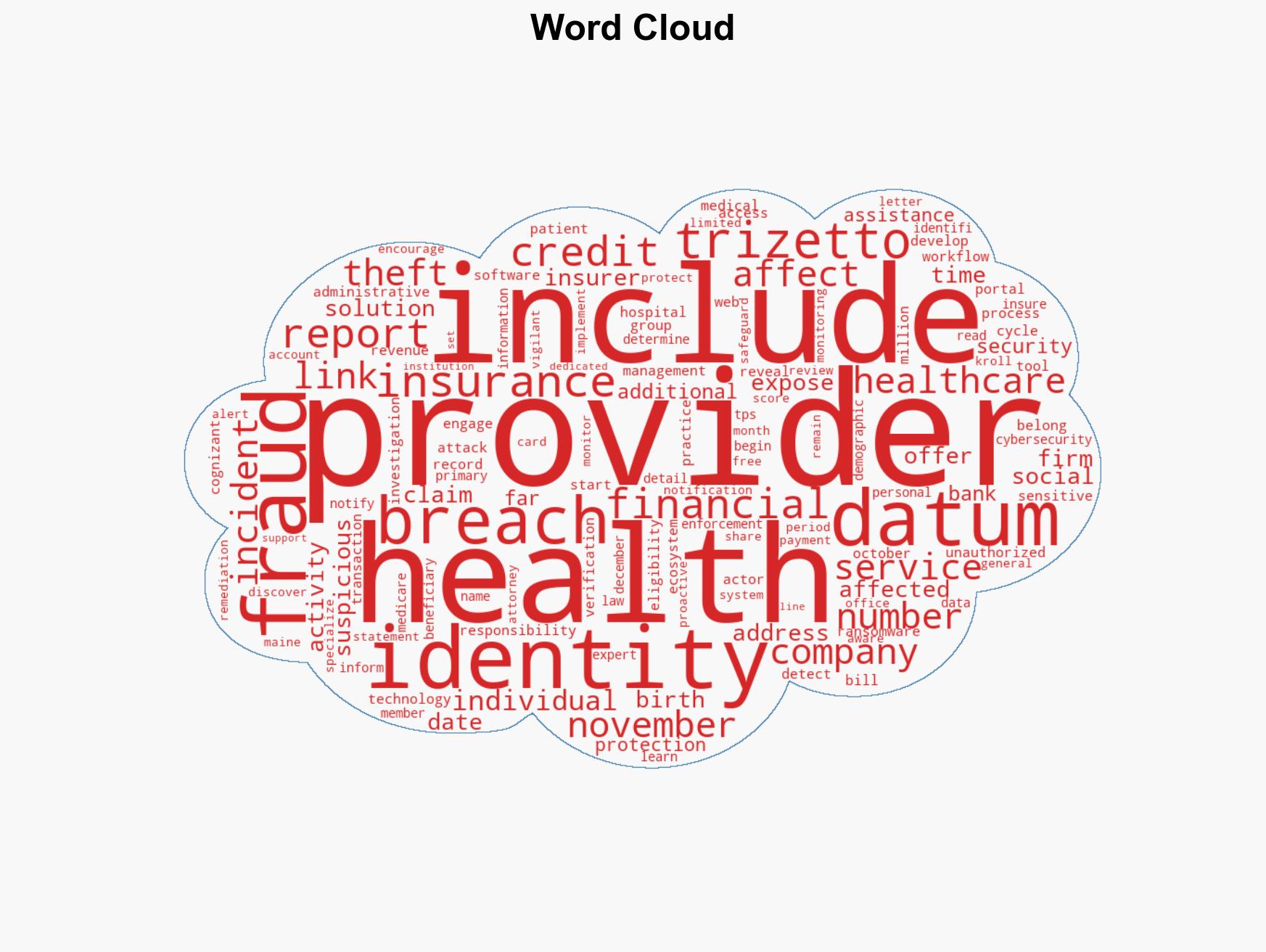
cybersecurity, data breach, healthcare cybersecurity, identity protection, cyber intrusion, regulatory implications, information security, patient data
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us