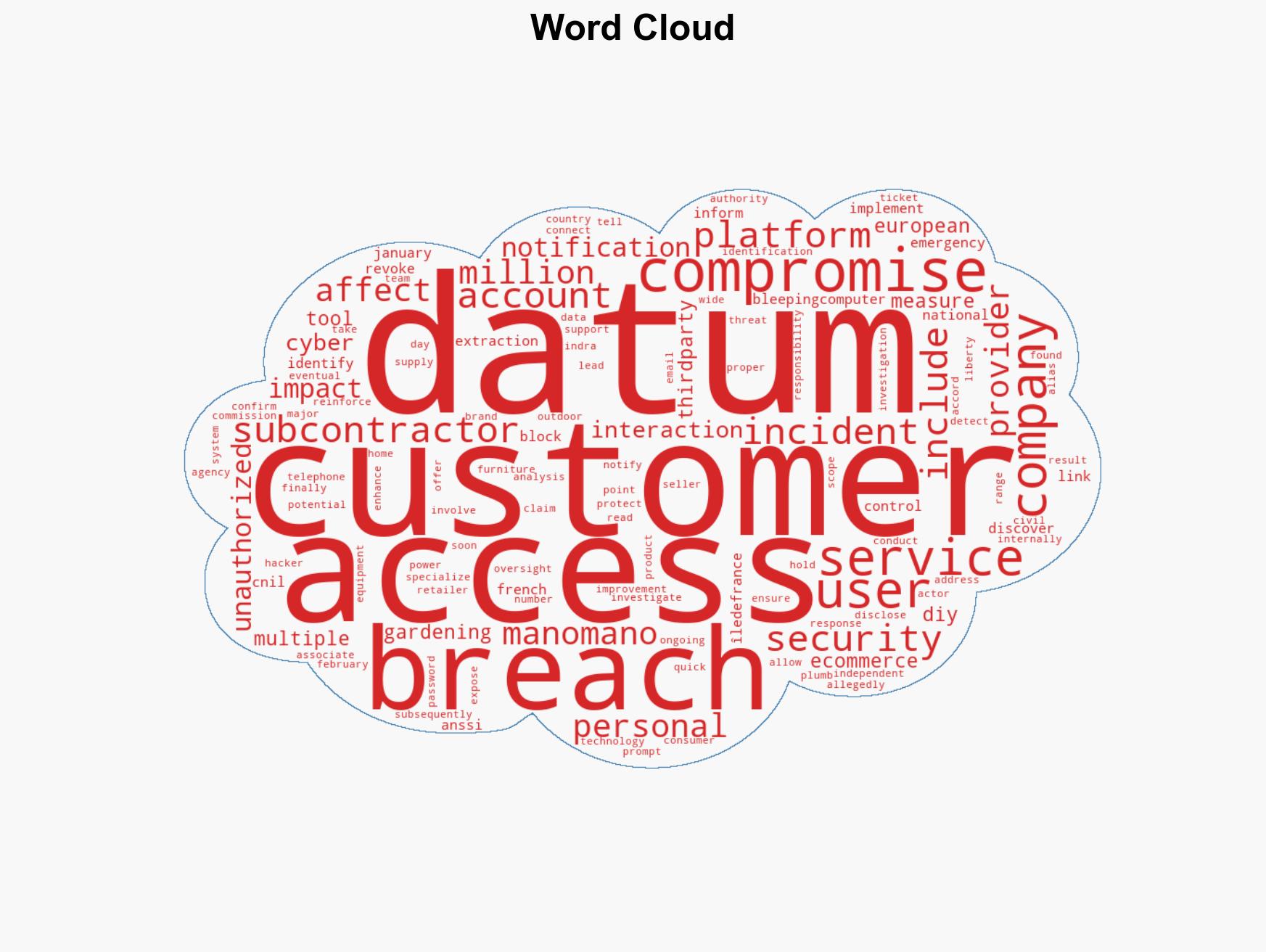
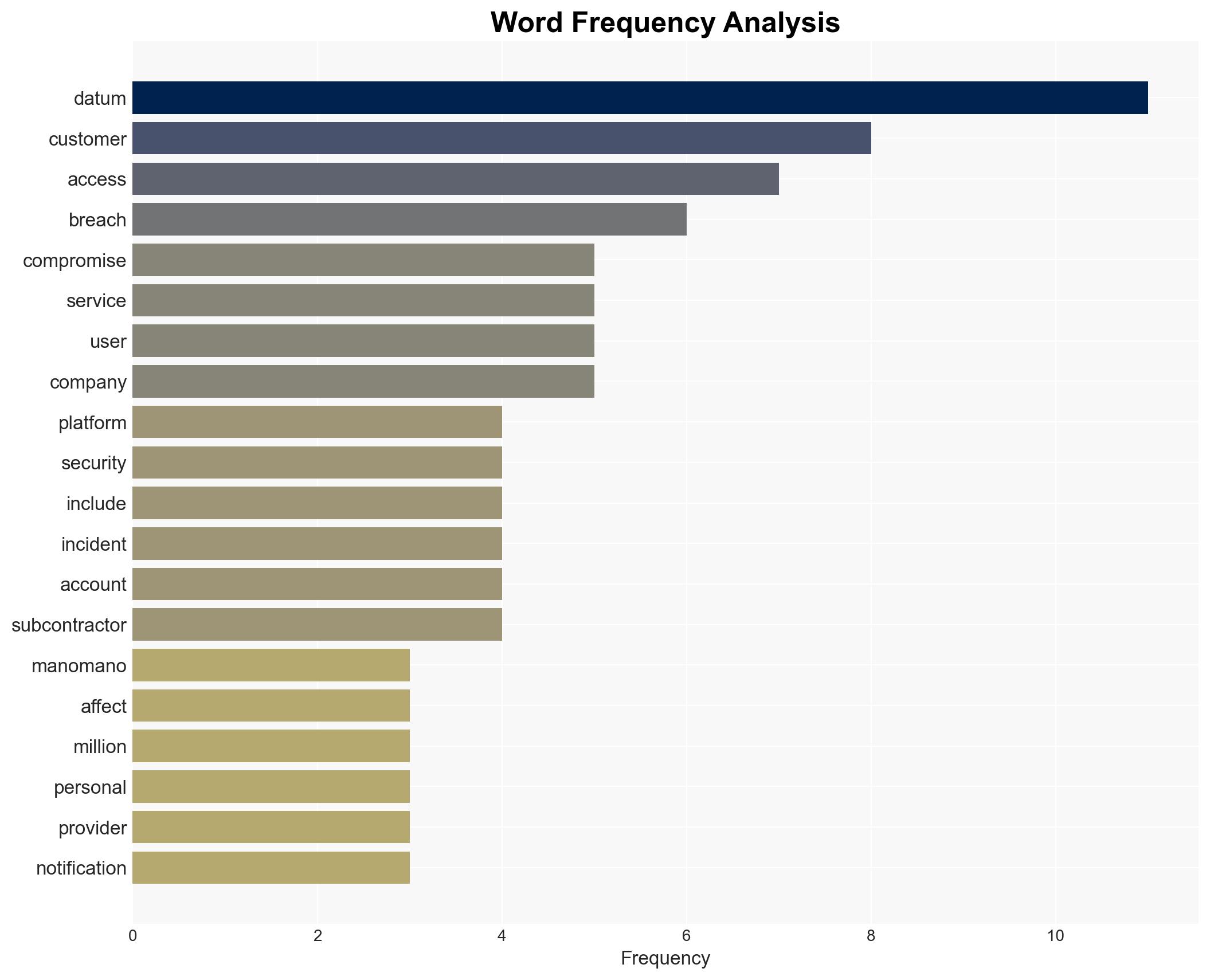
Data breach at ManoMano affects 38 million customer accounts through compromised third-party service provider
Published on: 2026-02-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: ManoMano data breach impacted 38 Million customer accounts
1. BLUF (Bottom Line Up Front)
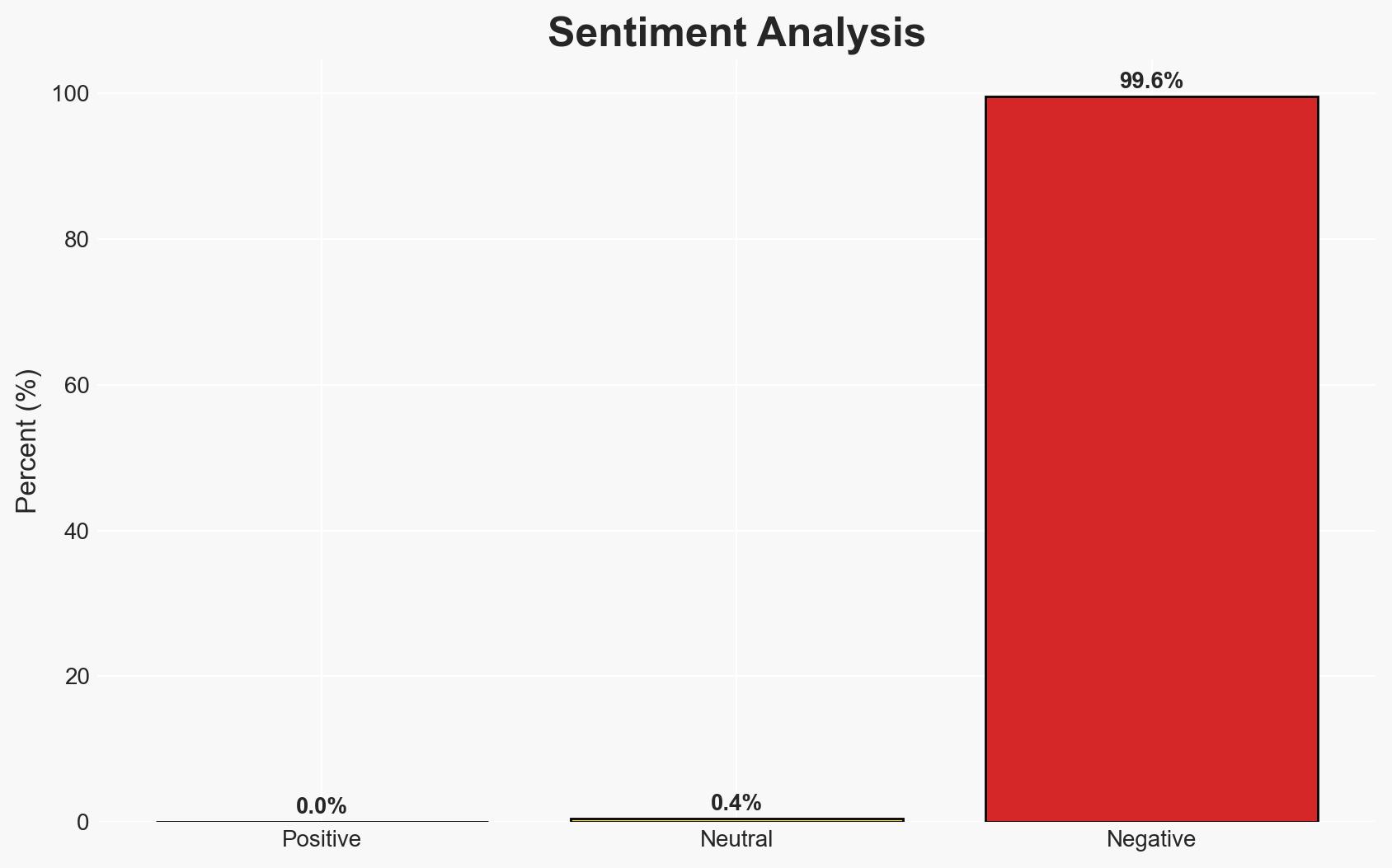
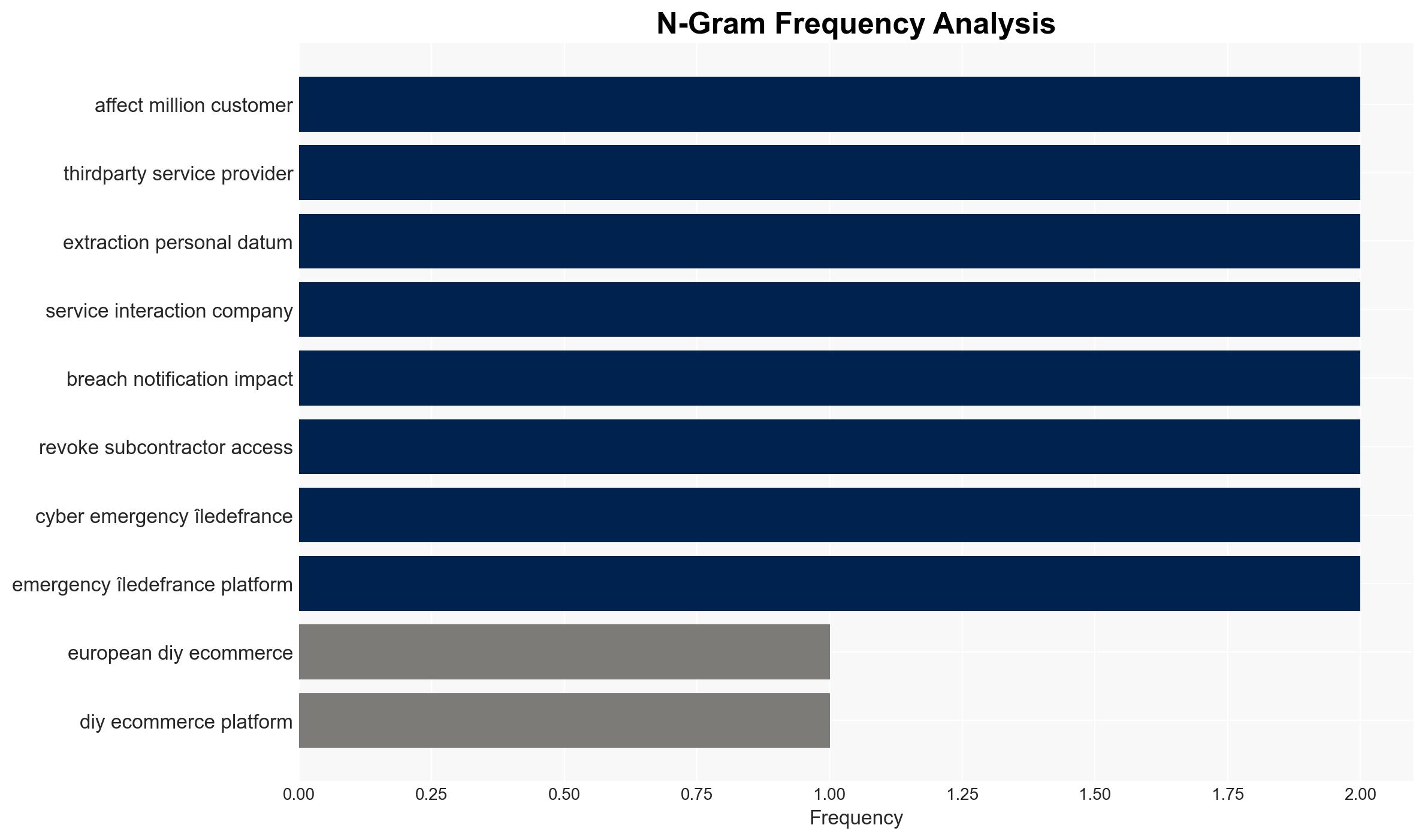
The ManoMano data breach, impacting 38 million customer accounts, was facilitated through a compromised third-party service provider. The breach exposed personal data but not passwords. The incident highlights vulnerabilities in third-party access controls. Current evidence moderately supports the hypothesis that the breach was opportunistic rather than targeted. The confidence level in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The breach was an opportunistic attack exploiting vulnerabilities in third-party service providers. Supporting evidence includes the lack of password compromise and the immediate containment measures taken by ManoMano. Key uncertainties include the full scope of data accessed and the motivations of the threat actor.
- Hypothesis B: The breach was a targeted attack specifically aimed at ManoMano for strategic or economic gain. This is supported by the claim of responsibility by the threat actor “Indra.” However, the lack of specific demands or further actions by the actor contradicts this hypothesis.
- Assessment: Hypothesis A is currently better supported due to the nature of the breach and the immediate response by ManoMano. Indicators that could shift this judgment include new evidence of targeted reconnaissance or demands by the threat actor.
3. Key Assumptions and Red Flags
- Assumptions: The breach was detected promptly; the threat actor’s claims are genuine; ManoMano’s internal security measures are robust post-breach.
- Information Gaps: The identity and motivations of the threat actor “Indra”; the specific vulnerabilities exploited; the full extent of data compromised.
- Bias & Deception Risks: Potential bias in relying on ManoMano’s internal reports; the threat actor’s claims may be exaggerated or false.
4. Implications and Strategic Risks
This data breach could lead to increased scrutiny on third-party service providers and their security practices. It may also prompt regulatory actions and affect consumer trust in e-commerce platforms.
- Political / Geopolitical: Potential regulatory responses from European authorities could impact cross-border data handling practices.
- Security / Counter-Terrorism: Increased focus on securing supply chains and third-party services in cybersecurity frameworks.
- Cyber / Information Space: Potential for increased cyber-attacks targeting third-party providers; heightened awareness of supply chain vulnerabilities.
- Economic / Social: Potential loss of consumer confidence in ManoMano and similar platforms; possible financial liabilities due to regulatory fines or lawsuits.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive audit of third-party service providers; enhance monitoring of customer data access; engage with cybersecurity experts for vulnerability assessments.
- Medium-Term Posture (1–12 months): Develop stronger partnerships with cybersecurity firms; invest in advanced threat detection technologies; implement regular security training for staff and partners.
- Scenario Outlook:
- Best: Enhanced security measures prevent future breaches, restoring consumer trust.
- Worst: Further breaches occur, leading to significant financial and reputational damage.
- Most-Likely: Incremental improvements in security posture with ongoing regulatory scrutiny.
6. Key Individuals and Entities
- ManoMano
- Indra (alleged threat actor)
- CNIL (French National Commission for Information Technology and Civil Liberties)
- ANSSI (French National Agency for the Security of Information Systems)
- Cyber Emergency Île-de-France platform
7. Thematic Tags
cybersecurity, data breach, cyber security, e-commerce, third-party risk, regulatory compliance, consumer trust, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us