Data breach at TriZetto exposes sensitive health information of over 3.4 million patients
Published on: 2026-03-06
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Cognizant TriZetto breach exposes health data of 34 million patients
1. BLUF (Bottom Line Up Front)
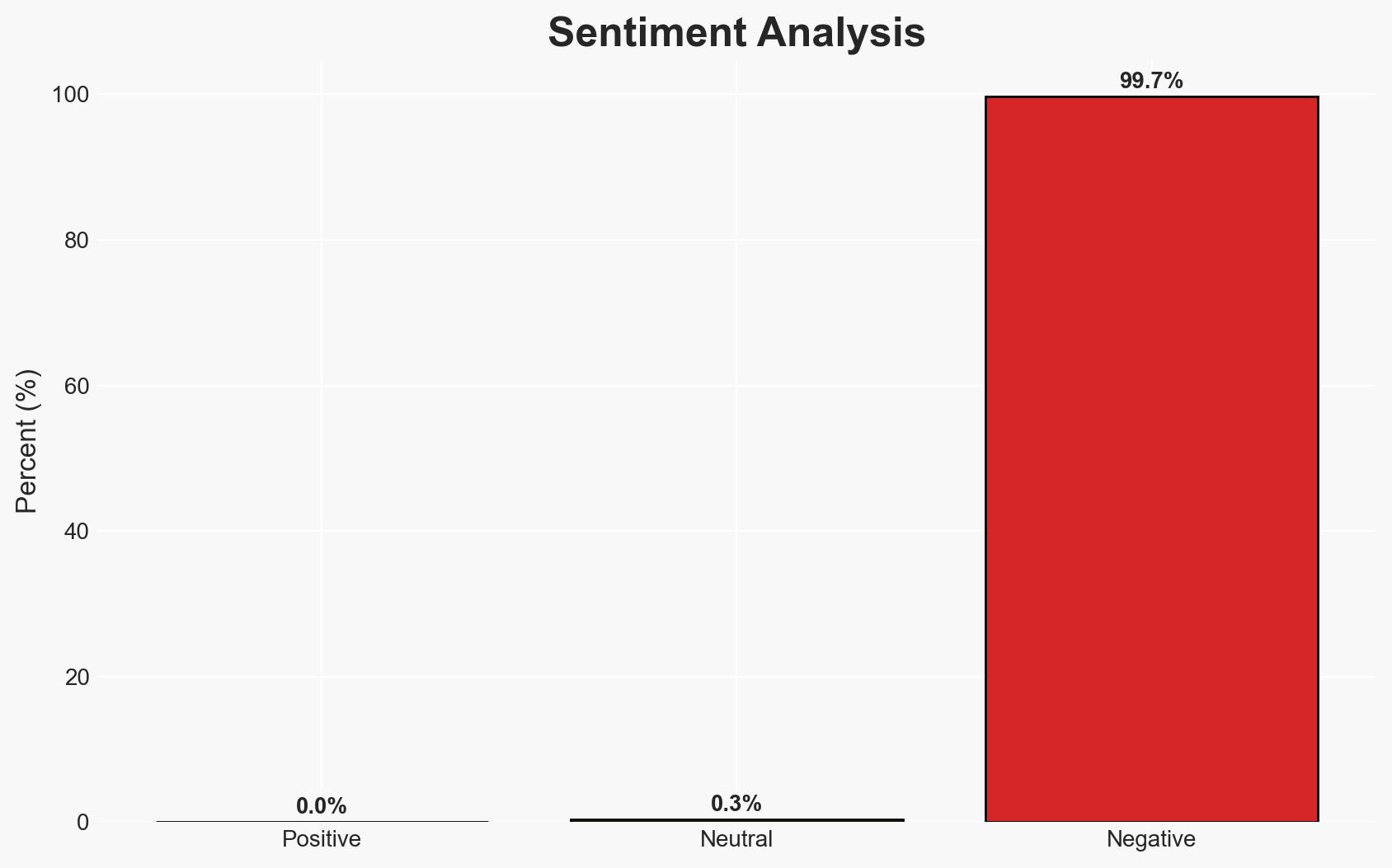
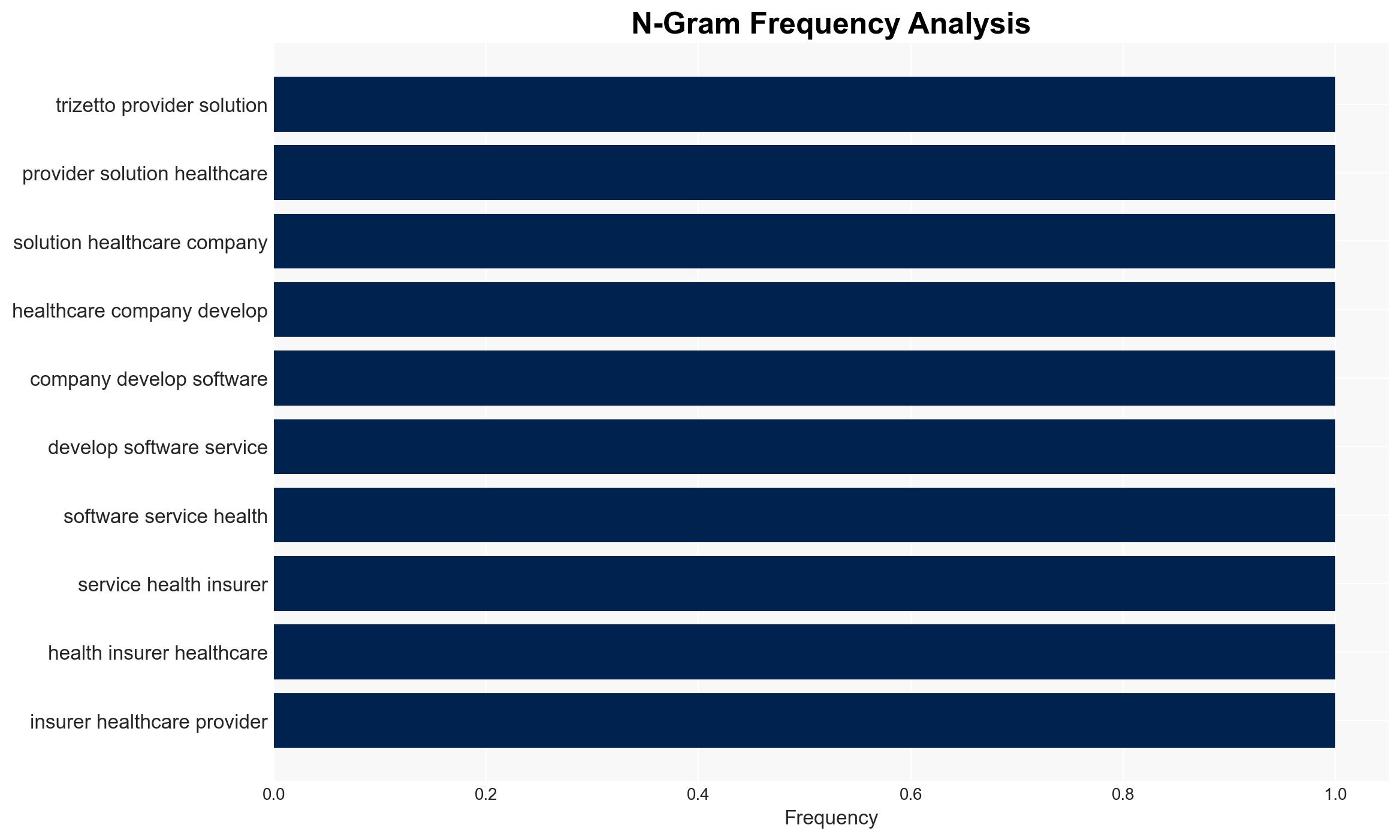
The data breach at TriZetto Provider Solutions has compromised sensitive health information of approximately 3.4 million individuals, with unauthorized access occurring over nearly a year. The breach poses significant risks to affected individuals and highlights vulnerabilities in healthcare IT systems. Currently, there is moderate confidence that the breach was not linked to a ransomware group, given the lack of claims or data leaks. The delay in consumer notification raises concerns about incident response effectiveness.
2. Competing Hypotheses
- Hypothesis A: The breach was conducted by a financially motivated cybercriminal group seeking to exploit healthcare data. This is supported by the type of data accessed and the prolonged period of unauthorized access. However, the absence of financial data and lack of immediate misuse reports contradict this.
- Hypothesis B: The breach was an opportunistic attack by non-affiliated hackers exploiting system vulnerabilities without a clear endgame. This is supported by the lack of claims from known ransomware groups and no data leaks on forums. The delay in notification and lack of immediate financial gain contradict this hypothesis.
- Assessment: Hypothesis B is currently better supported due to the absence of financial data exposure and the lack of claims by ransomware groups. Indicators such as future data leaks or claims could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The breach was not state-sponsored; TriZetto’s cybersecurity measures were inadequate; the delay in notification was not intentional deception.
- Information Gaps: Details on the specific vulnerabilities exploited; the identity and motive of the threat actors; full scope of data accessed.
- Bias & Deception Risks: Potential underreporting by TriZetto to minimize reputational damage; cognitive bias towards assuming financial motivation without evidence.
4. Implications and Strategic Risks
This breach underscores vulnerabilities in healthcare IT systems, potentially prompting regulatory scrutiny and increased cybersecurity investments. The incident could erode trust in digital health solutions and impact patient-provider relationships.
- Political / Geopolitical: Potential for increased regulatory actions and international scrutiny on data protection practices.
- Security / Counter-Terrorism: Heightened awareness and potential for similar attacks on healthcare infrastructure.
- Cyber / Information Space: Increased focus on healthcare cybersecurity; potential for copycat attacks exploiting similar vulnerabilities.
- Economic / Social: Financial liabilities for TriZetto; potential loss of consumer trust and reputational damage.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive security audit; enhance monitoring of affected systems; engage with law enforcement for ongoing investigation.
- Medium-Term Posture (1–12 months): Strengthen cybersecurity frameworks; foster partnerships with cybersecurity firms; implement regular employee training on data protection.
- Scenario Outlook:
- Best: No further data misuse or breaches; improved cybersecurity measures restore trust.
- Worst: Additional breaches occur, leading to significant financial and reputational damage.
- Most-Likely: Incremental improvements in cybersecurity with periodic attempts at exploitation by cybercriminals.
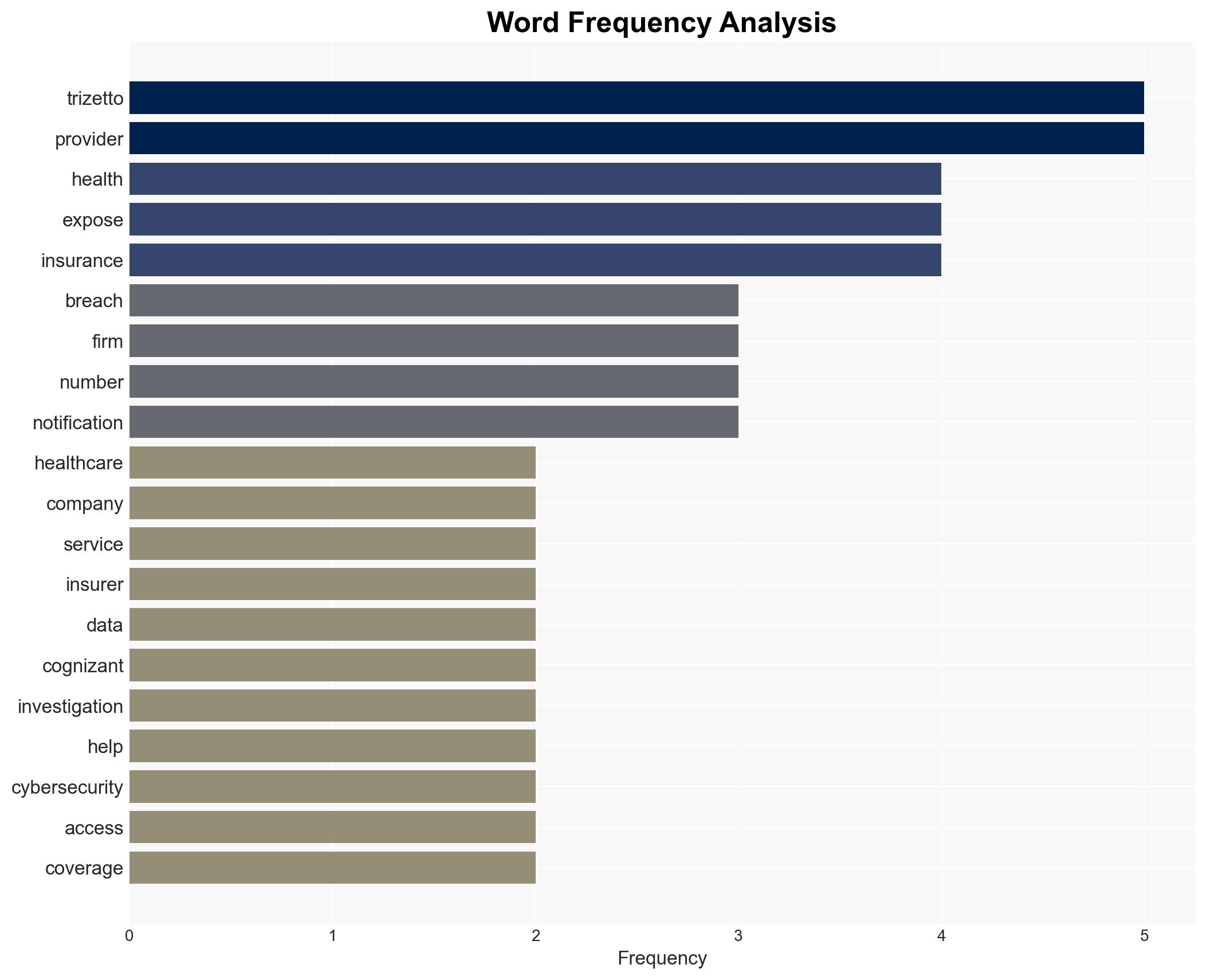
6. Key Individuals and Entities
- TriZetto Provider Solutions
- Cognizant
- Maine’s Attorney General
- Kroll
- BleepingComputer
- Clorox
7. Thematic Tags
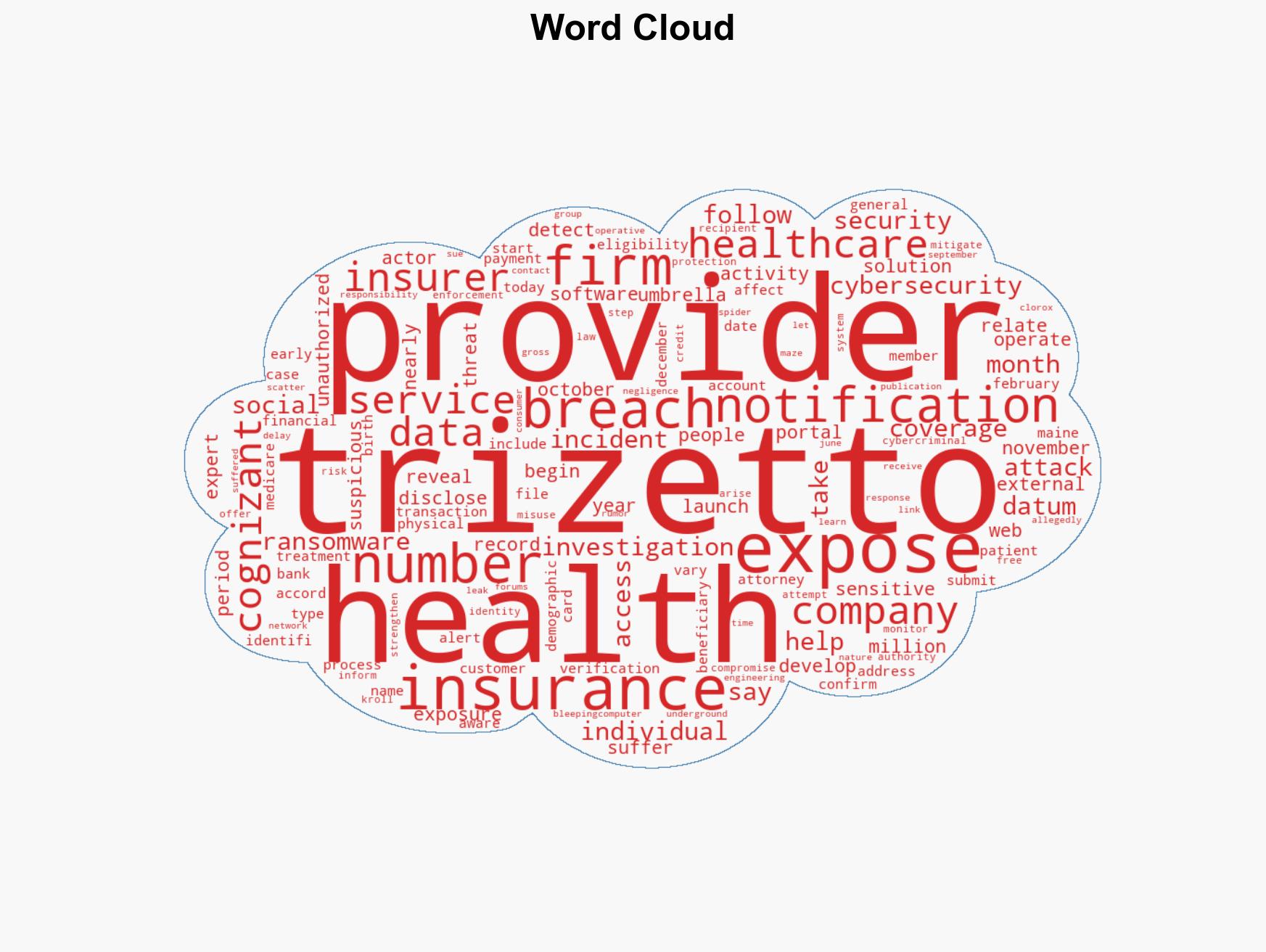
cybersecurity, data breach, healthcare IT, information security, regulatory compliance, identity protection, cybercrime
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us