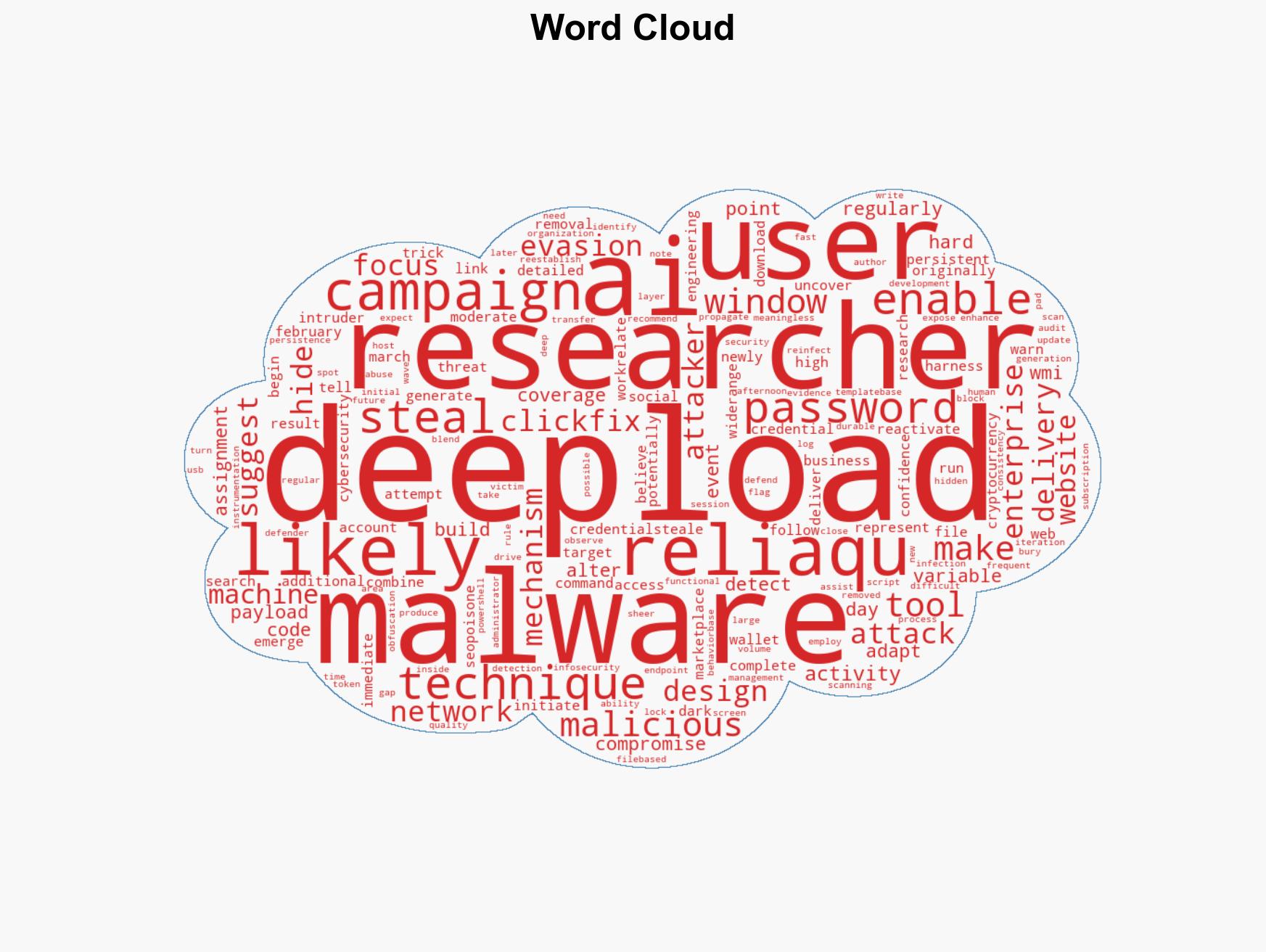
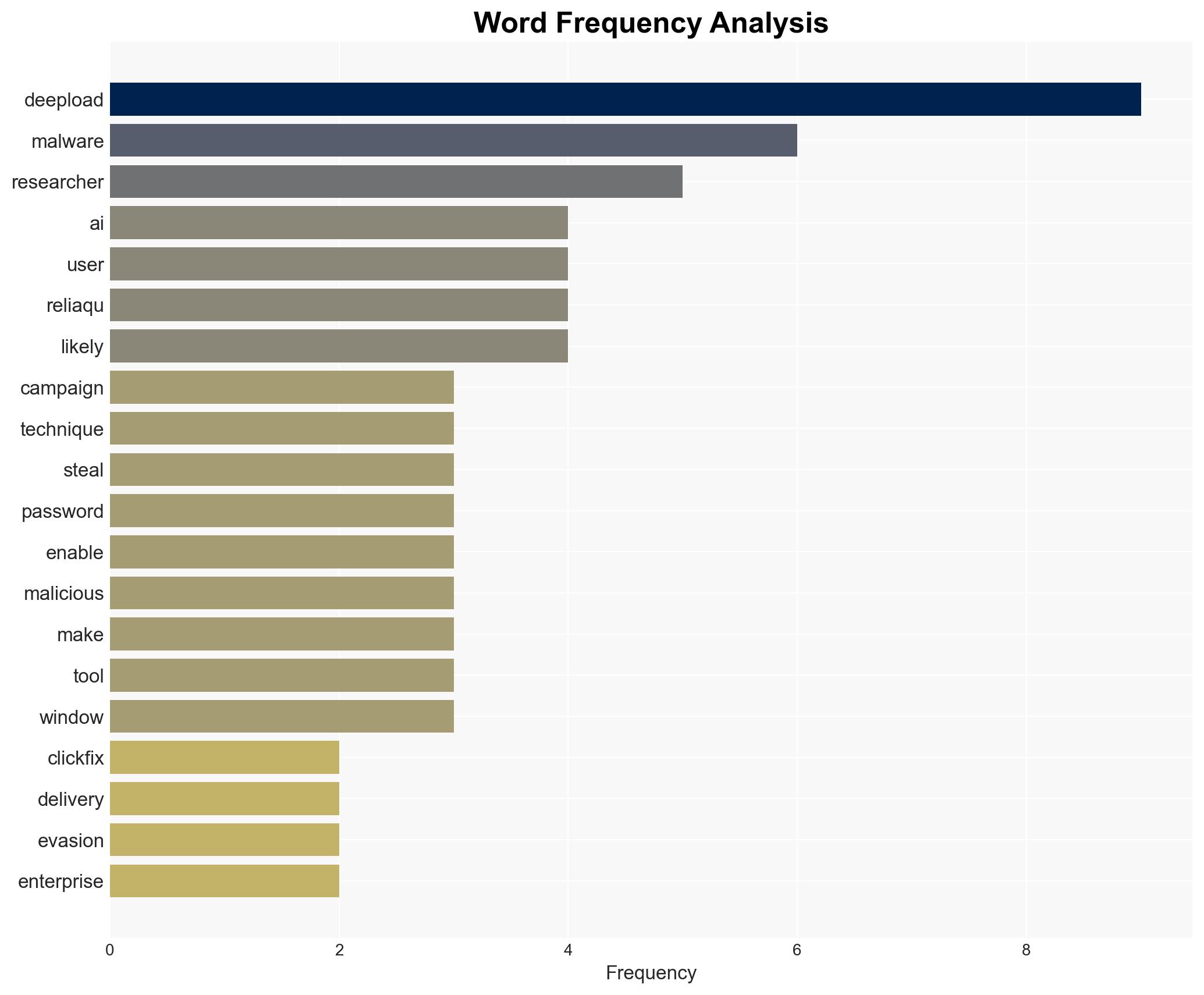
DeepLoad Malware Leverages ClickFix and AI Evasion Tactics to Target Enterprise Credentials
Published on: 2026-03-30
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
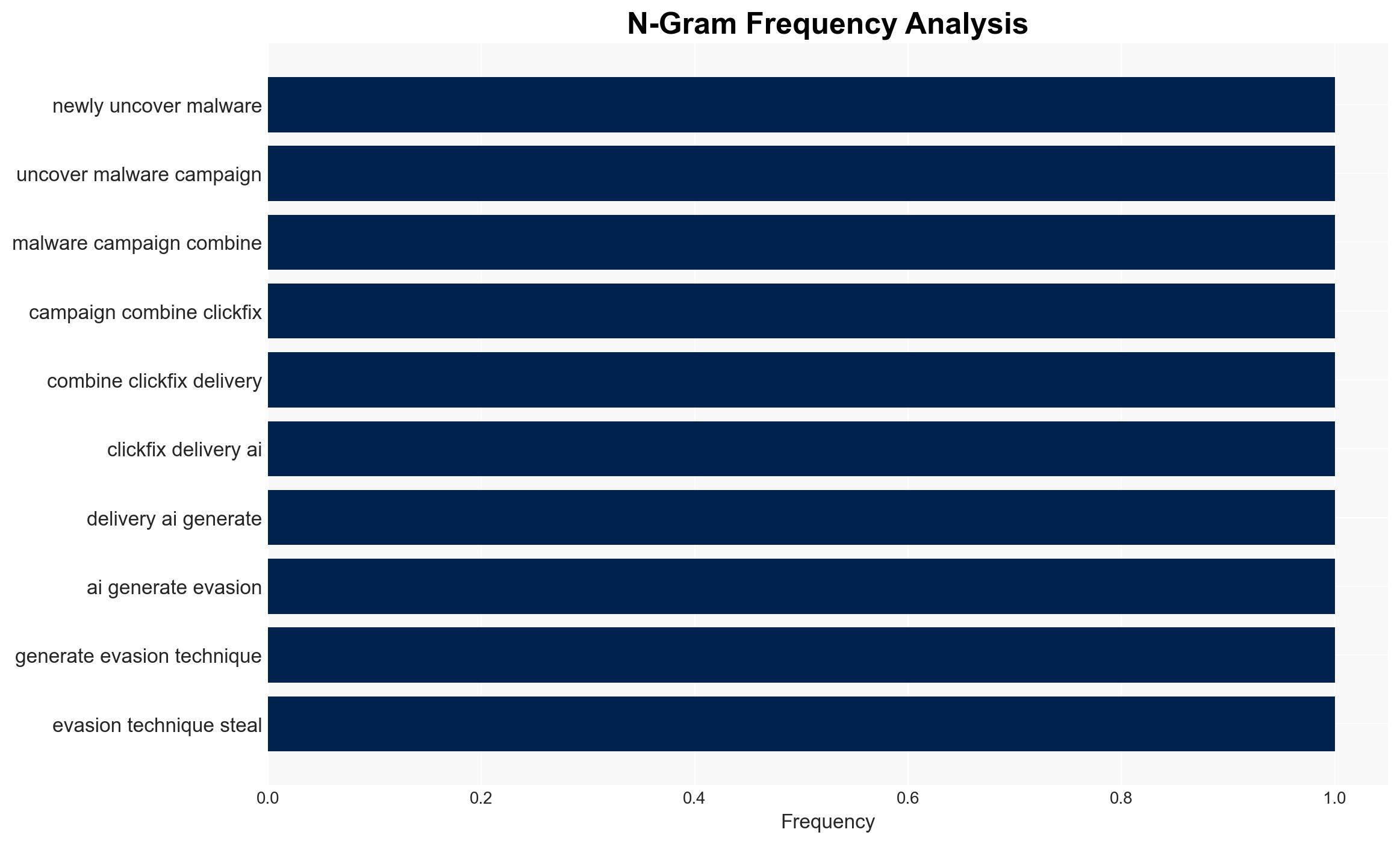
Intelligence Report: DeepLoad Malware Combines ClickFix With AI-Generated Code to Avoid Detection
1. BLUF (Bottom Line Up Front)
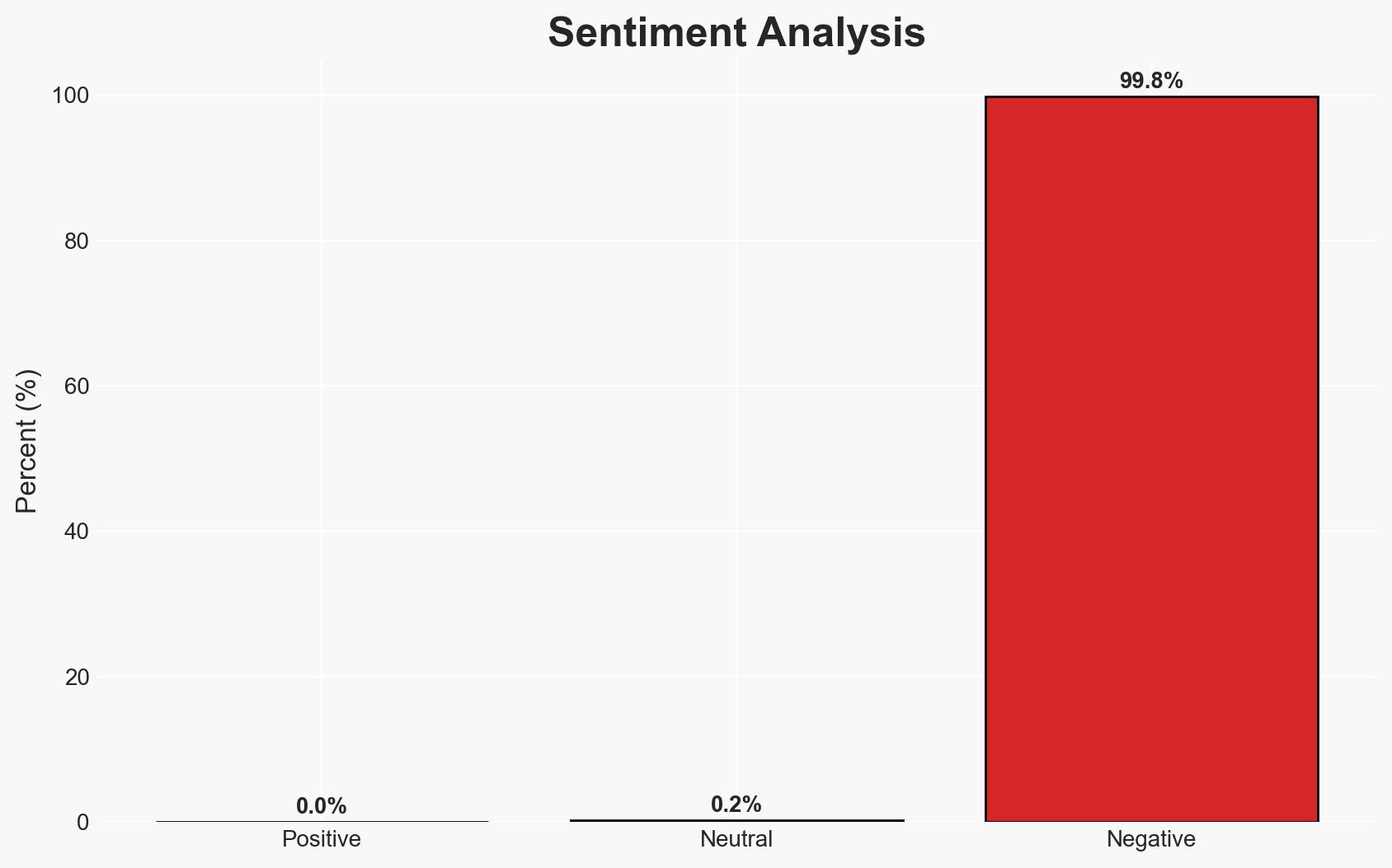
The DeepLoad malware campaign poses an immediate threat to enterprise security by utilizing AI-generated code and social engineering tactics to steal credentials and maintain persistence. The campaign’s ability to evade detection and adapt rapidly suggests a sophisticated threat actor. This assessment is made with moderate confidence due to the evolving nature of the malware and its methods of propagation.
2. Competing Hypotheses
- Hypothesis A: DeepLoad is primarily targeting enterprises for credential theft, leveraging AI to enhance its evasion capabilities. This is supported by the malware’s focus on enterprise credentials and its sophisticated obfuscation techniques. However, the initial focus on cryptocurrency wallets suggests a potential shift in targeting strategy.
- Hypothesis B: DeepLoad’s primary objective remains cryptocurrency theft, with enterprise credential theft being a secondary target to facilitate broader financial gains. The initial emergence on dark web marketplaces focused on cryptocurrency supports this, but the expanded targeting of enterprise credentials contradicts it.
- Assessment: Hypothesis A is currently better supported due to the malware’s advanced evasion techniques and the explicit targeting of enterprise credentials. Indicators such as changes in targeting patterns or new functionalities could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The attackers have access to AI tools for code generation; the malware is primarily distributed via compromised websites or SEO-poisoned results; enterprises are the main targets.
- Information Gaps: Specific attribution of the threat actor; detailed understanding of the AI tools used; comprehensive list of affected enterprises.
- Bias & Deception Risks: Potential overestimation of AI’s role due to lack of direct evidence; reliance on cybersecurity firm reports may introduce confirmation bias.
4. Implications and Strategic Risks
The evolution of DeepLoad malware could significantly impact enterprise security landscapes, necessitating rapid adaptation in defense strategies. Its use of AI for evasion may set a precedent for future cyber threats.
- Political / Geopolitical: Potential for state-sponsored actors to adopt similar techniques, escalating cyber tensions.
- Security / Counter-Terrorism: Increased difficulty in detecting and mitigating threats, potentially leading to more successful cyber intrusions.
- Cyber / Information Space: Accelerated arms race in malware sophistication, challenging existing cybersecurity frameworks.
- Economic / Social: Potential financial losses for affected enterprises, impacting economic stability and trust in digital security.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring for AI-generated code patterns, update security protocols to detect ClickFix techniques, and conduct employee awareness training on social engineering risks.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for intelligence sharing, invest in AI-driven detection tools, and establish protocols for rapid response to malware updates.
- Scenario Outlook:
- Best: Rapid adaptation by enterprises mitigates threat impact.
- Worst: Widespread breaches lead to significant economic and reputational damage.
- Most-Likely: Continued evolution of malware with periodic successful intrusions.
6. Key Individuals and Entities
- ReliaQuest (Cybersecurity Research Firm)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, malware, AI-generated code, enterprise security, credential theft, social engineering, cyber threat
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us