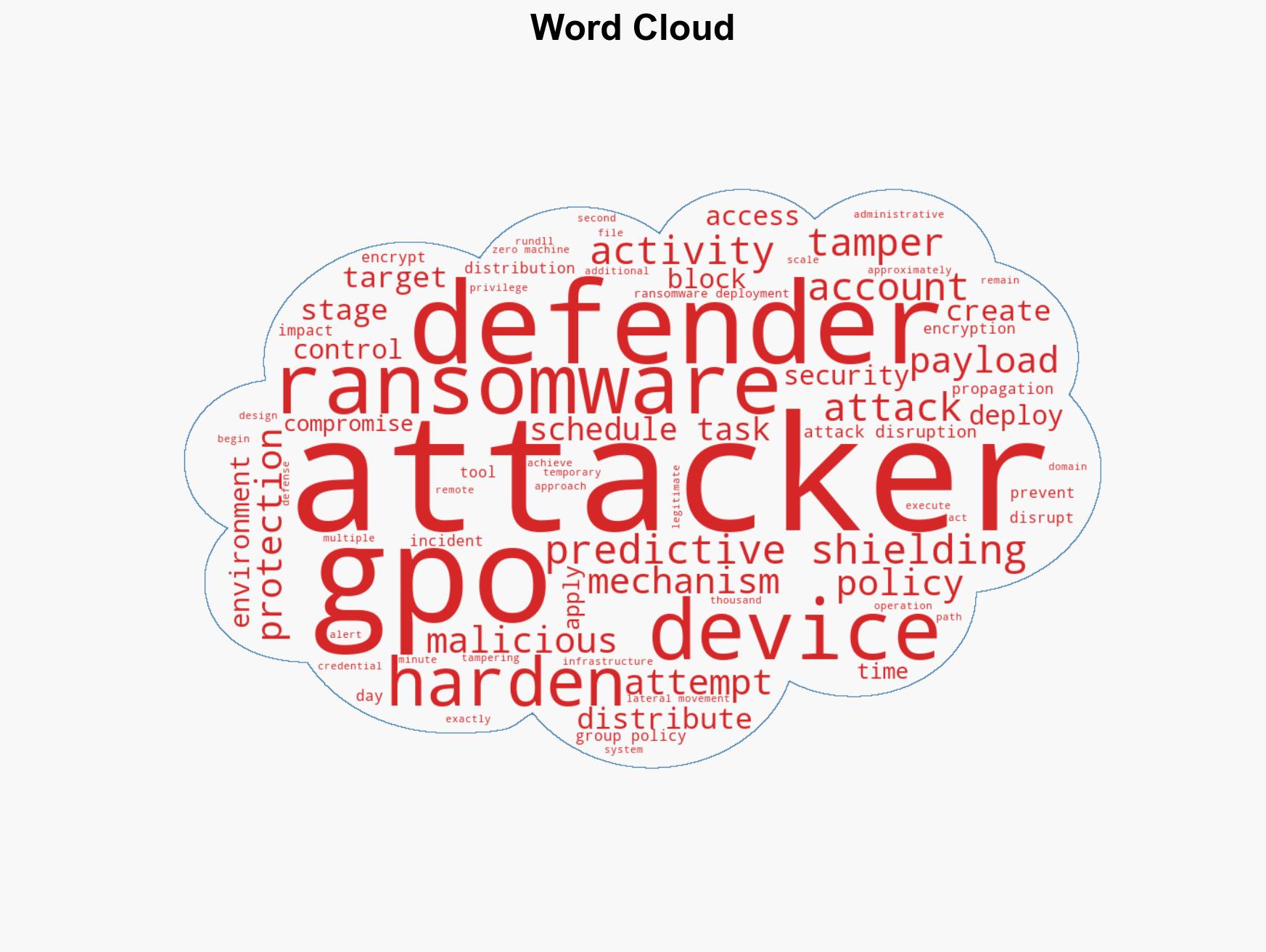
Defender’s Predictive Shielding Thwarts GPO-Based Ransomware Attack on Educational Institution
Published on: 2026-03-23
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Case study How predictive shielding in Defender stopped GPO-based ransomware before it started
1. BLUF (Bottom Line Up Front)
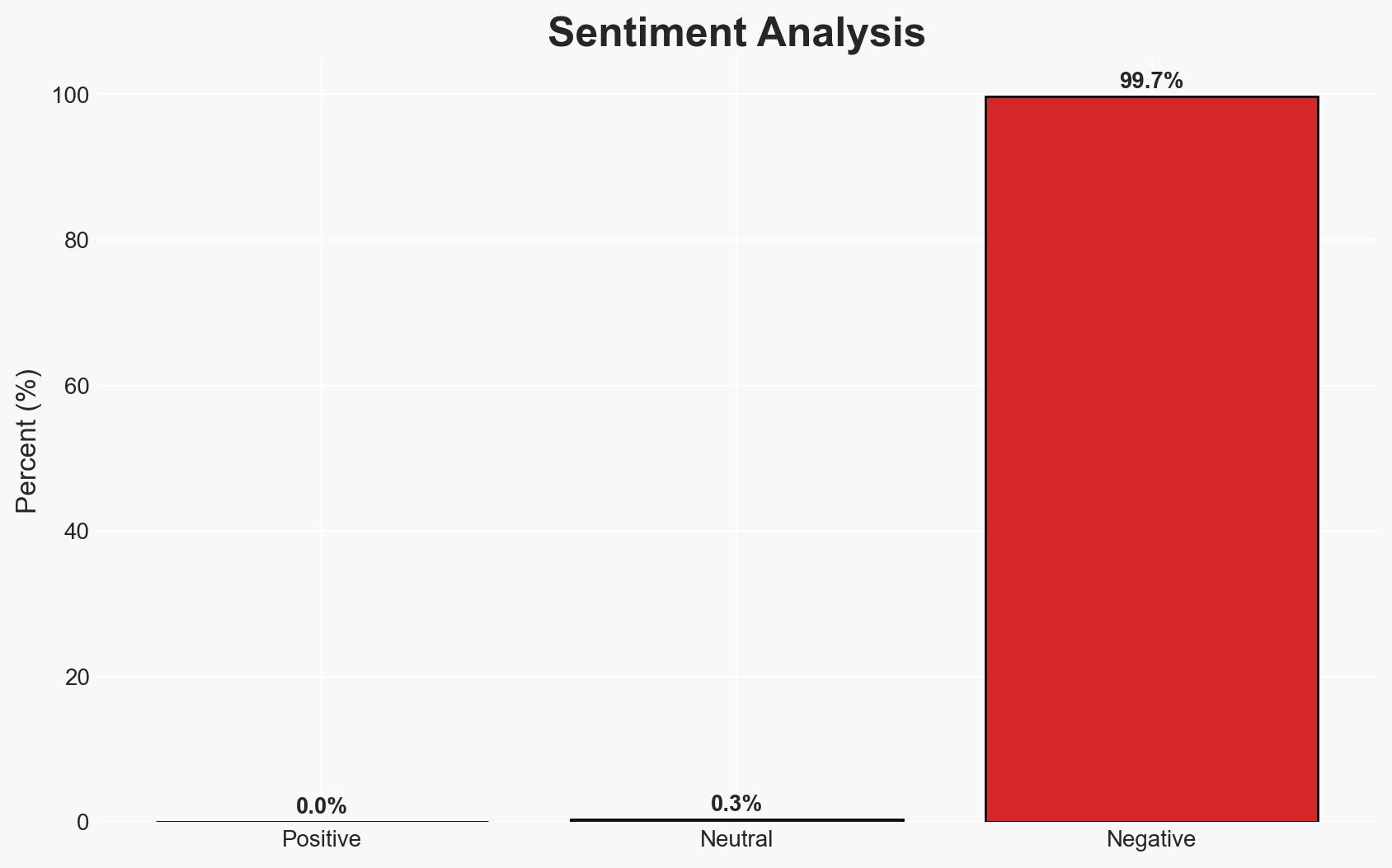
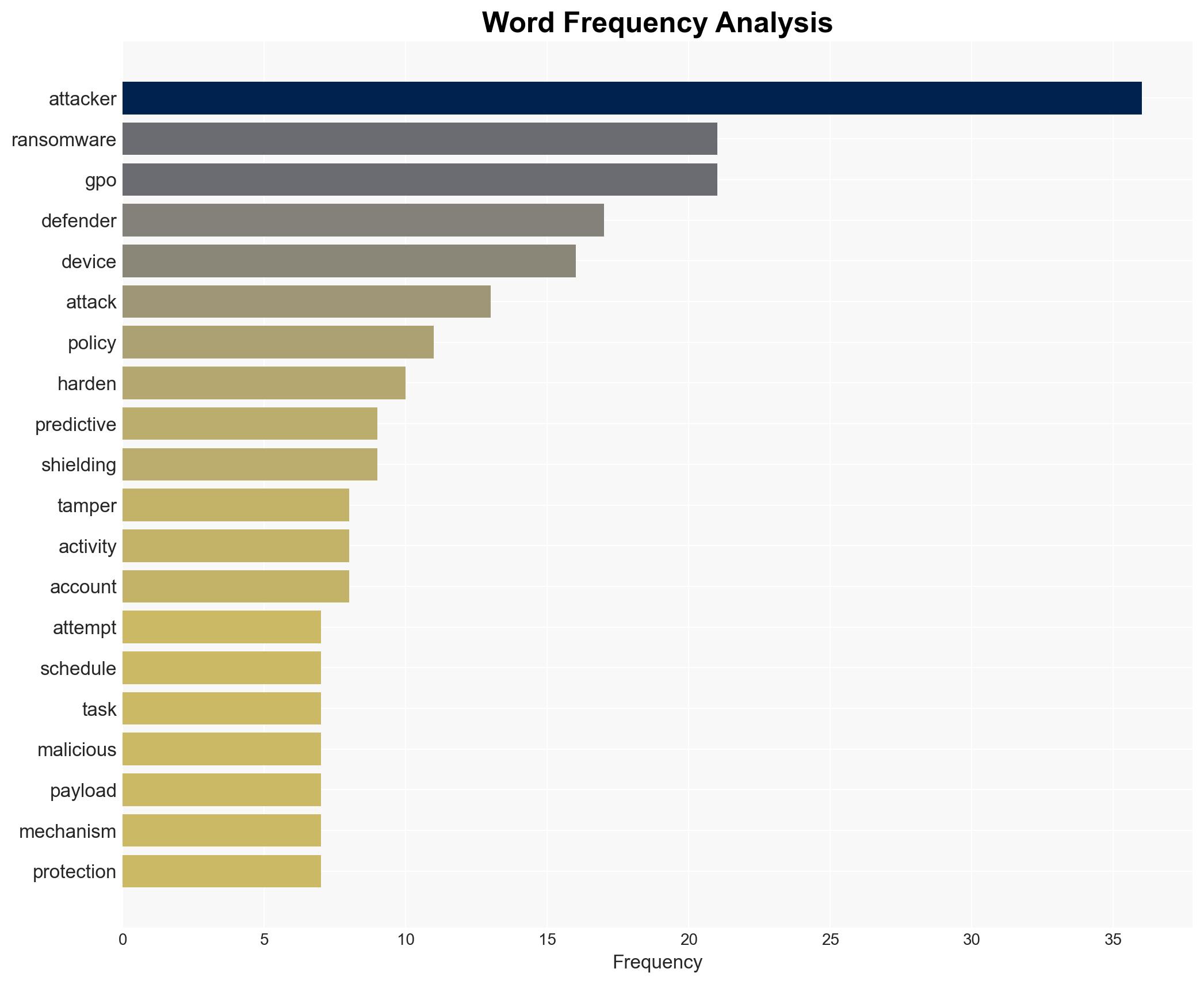
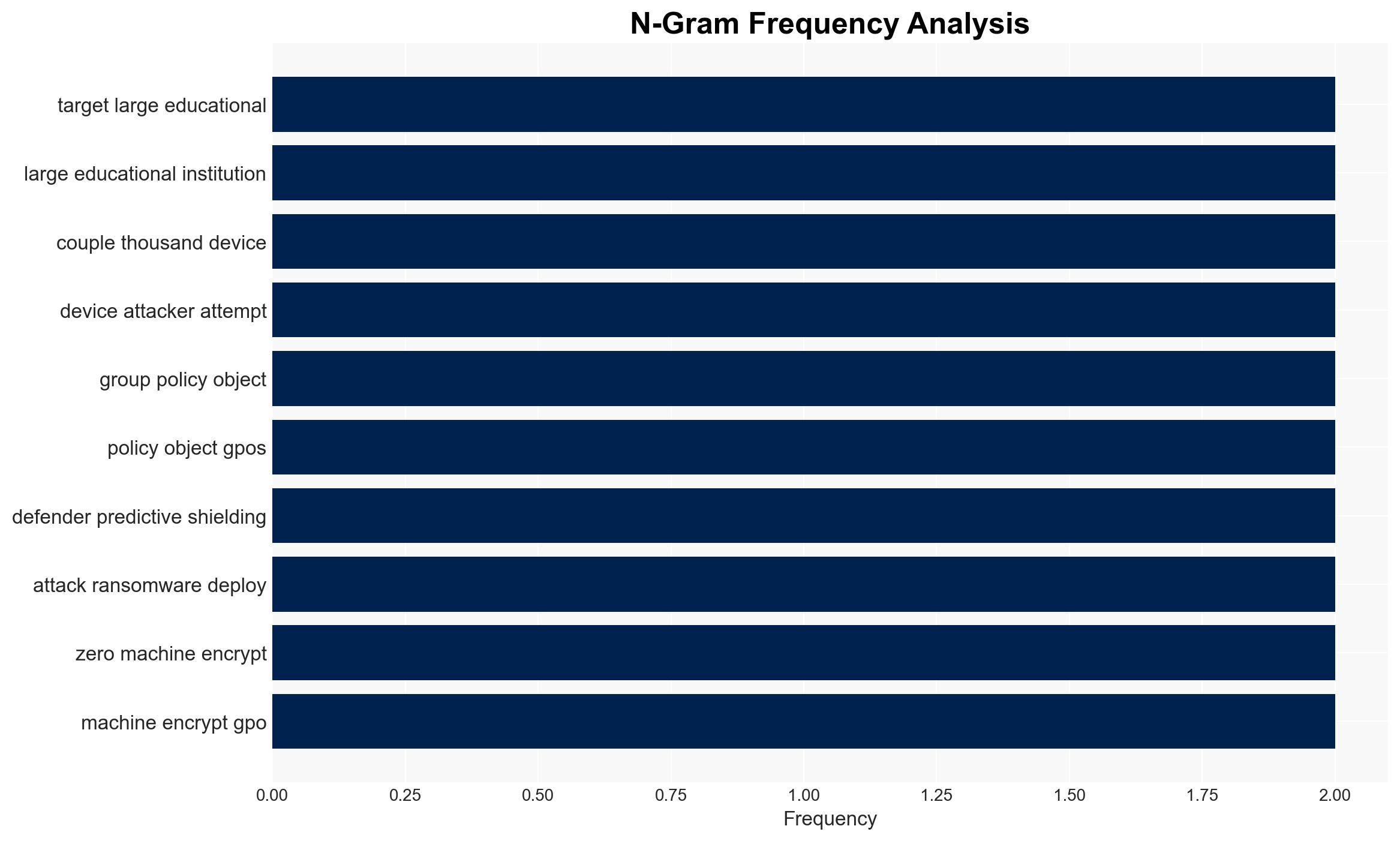
Microsoft Defender successfully thwarted a ransomware attack targeting a large educational institution by detecting and blocking malicious use of Group Policy Objects (GPOs) before ransomware deployment. The incident highlights the evolving sophistication of ransomware operators in exploiting enterprise infrastructure. The assessment is made with moderate confidence due to gaps in initial access vector information.
2. Competing Hypotheses
- Hypothesis A: The attacker’s primary objective was to deploy ransomware across the institution using GPOs as a means to disable security controls and propagate the attack. This is supported by the methodical progression through the network and the use of GPOs, but contradicted by the lack of successful encryption.
- Hypothesis B: The attack was a reconnaissance operation aimed at testing the institution’s defenses and gathering intelligence for future attacks. This is supported by the detailed reconnaissance activities and credential access but lacks direct evidence of intent to deploy ransomware.
- Assessment: Hypothesis A is currently better supported due to the observed use of GPOs for ransomware propagation, a common tactic among modern ransomware operators. Indicators such as the creation of scheduled tasks for ransomware distribution could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The attacker had prior knowledge of the institution’s infrastructure; the use of GPOs was intended for large-scale ransomware deployment; Microsoft Defender’s detection capabilities are representative of its general performance.
- Information Gaps: The initial access vector and method of obtaining Domain Admin privileges remain unknown; the identity and motivations of the attackers are unclear.
- Bias & Deception Risks: Potential bias in assuming the attack was primarily ransomware-focused; reliance on Microsoft Defender’s reporting may overlook other security tool perspectives.
4. Implications and Strategic Risks
This development underscores the need for enhanced security measures against sophisticated ransomware tactics, particularly in educational institutions. The incident could prompt broader adoption of predictive shielding technologies.
- Political / Geopolitical: Increased pressure on educational institutions to enhance cybersecurity may lead to policy changes and funding allocations.
- Security / Counter-Terrorism: The incident highlights vulnerabilities in administrative mechanisms, potentially prompting similar attacks on other sectors.
- Cyber / Information Space: Demonstrates the importance of advanced threat detection and response capabilities in combating evolving cyber threats.
- Economic / Social: Successful ransomware attacks could disrupt educational services, affecting students and staff, and leading to financial losses.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a thorough investigation to identify the initial access vector; enhance monitoring of GPO activities; review and update access controls.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for advanced threat intelligence sharing; invest in training for IT staff on emerging ransomware tactics.
- Scenario Outlook: Best: Enhanced defenses prevent future attacks; Worst: Attackers succeed in a future attempt, causing significant disruption; Most-Likely: Continued attempts with varying degrees of success, prompting ongoing security enhancements.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, ransomware, predictive shielding, educational institutions, Group Policy Objects, threat detection, network security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us