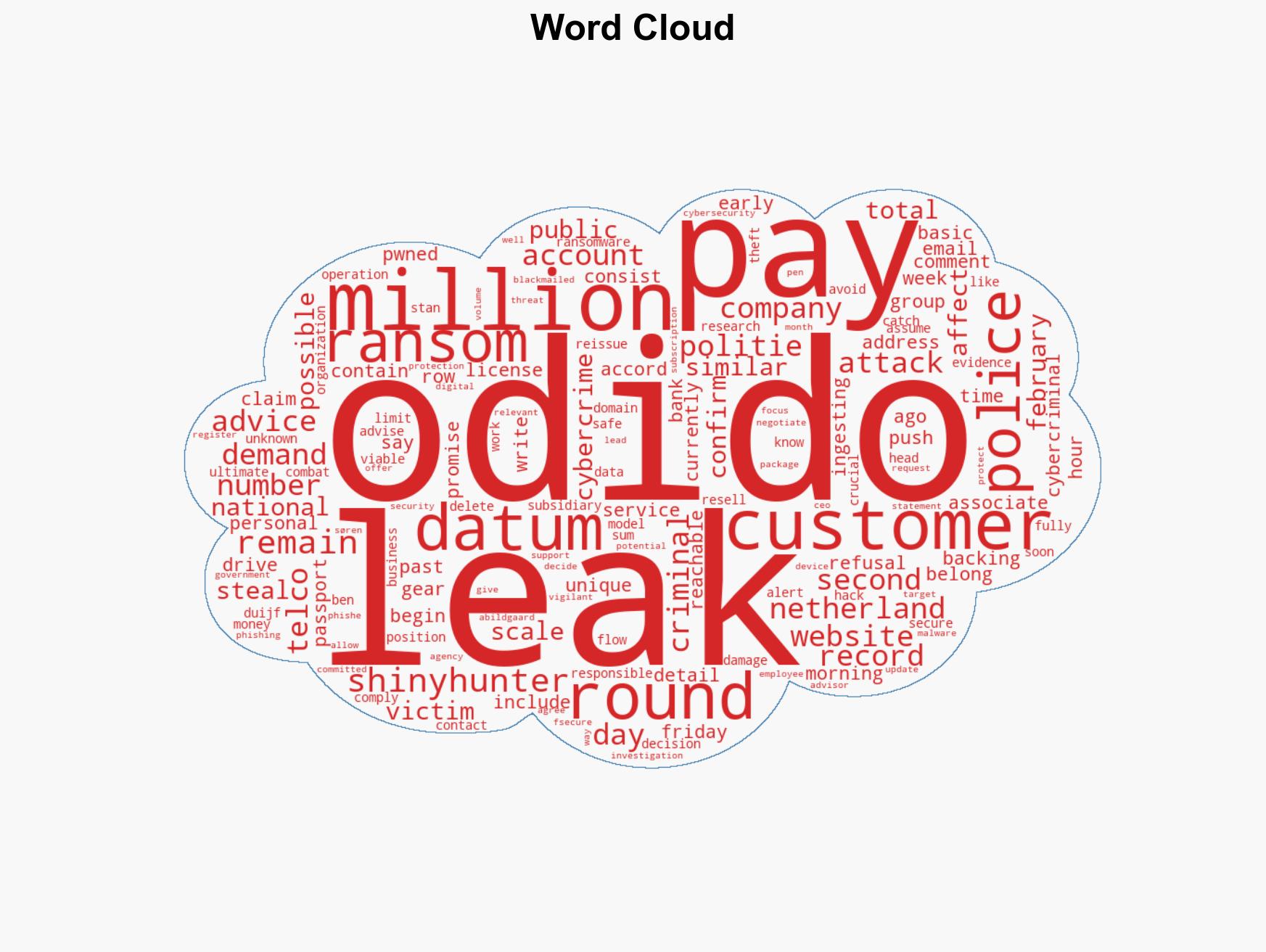
Dutch Police Support Odido’s Stance Against Ransom Amid Ongoing ShinyHunters Data Breach
Published on: 2026-02-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Cops back Dutch telco Odido after second wave of ShinyHunters leaks
1. BLUF (Bottom Line Up Front)
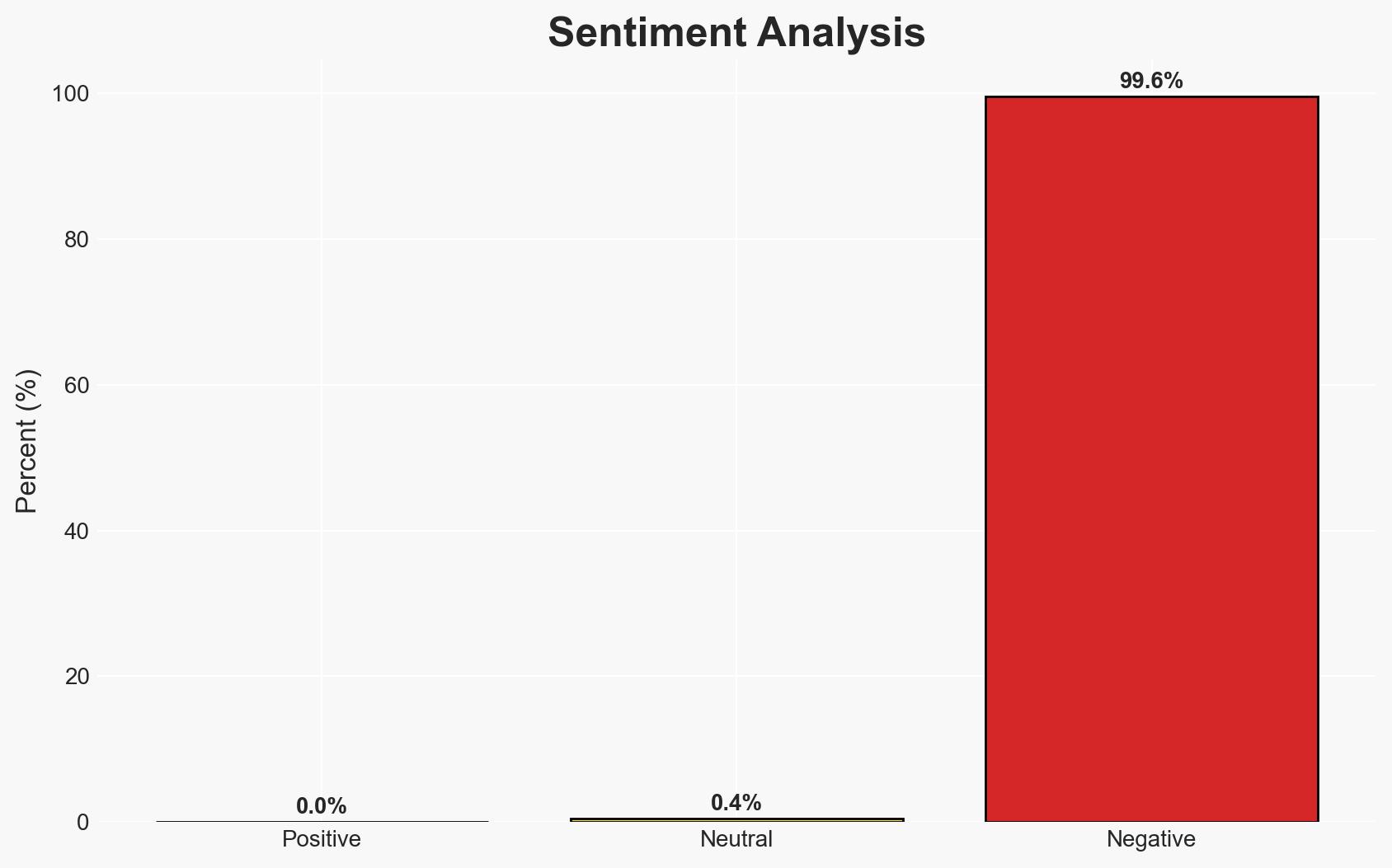
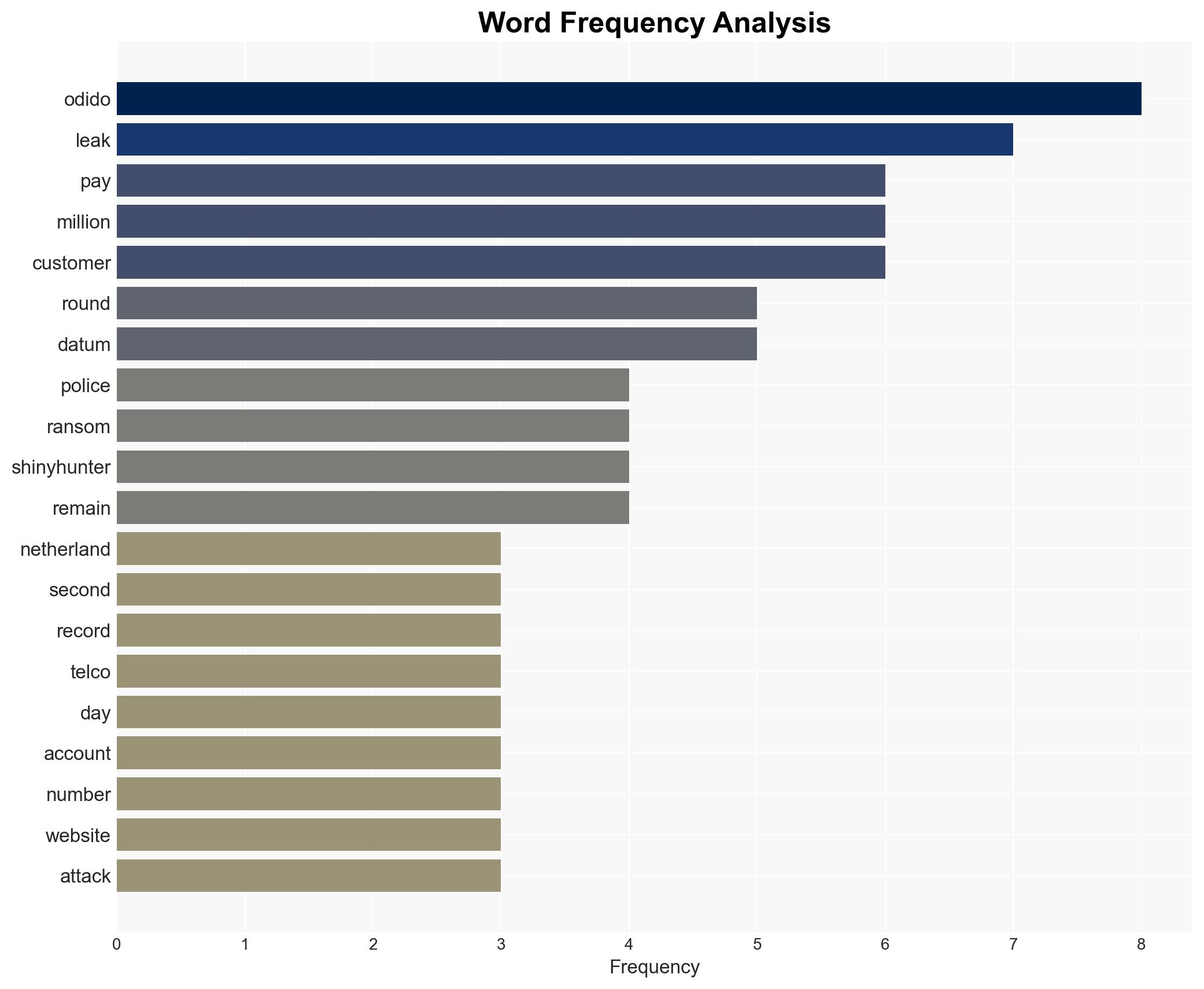
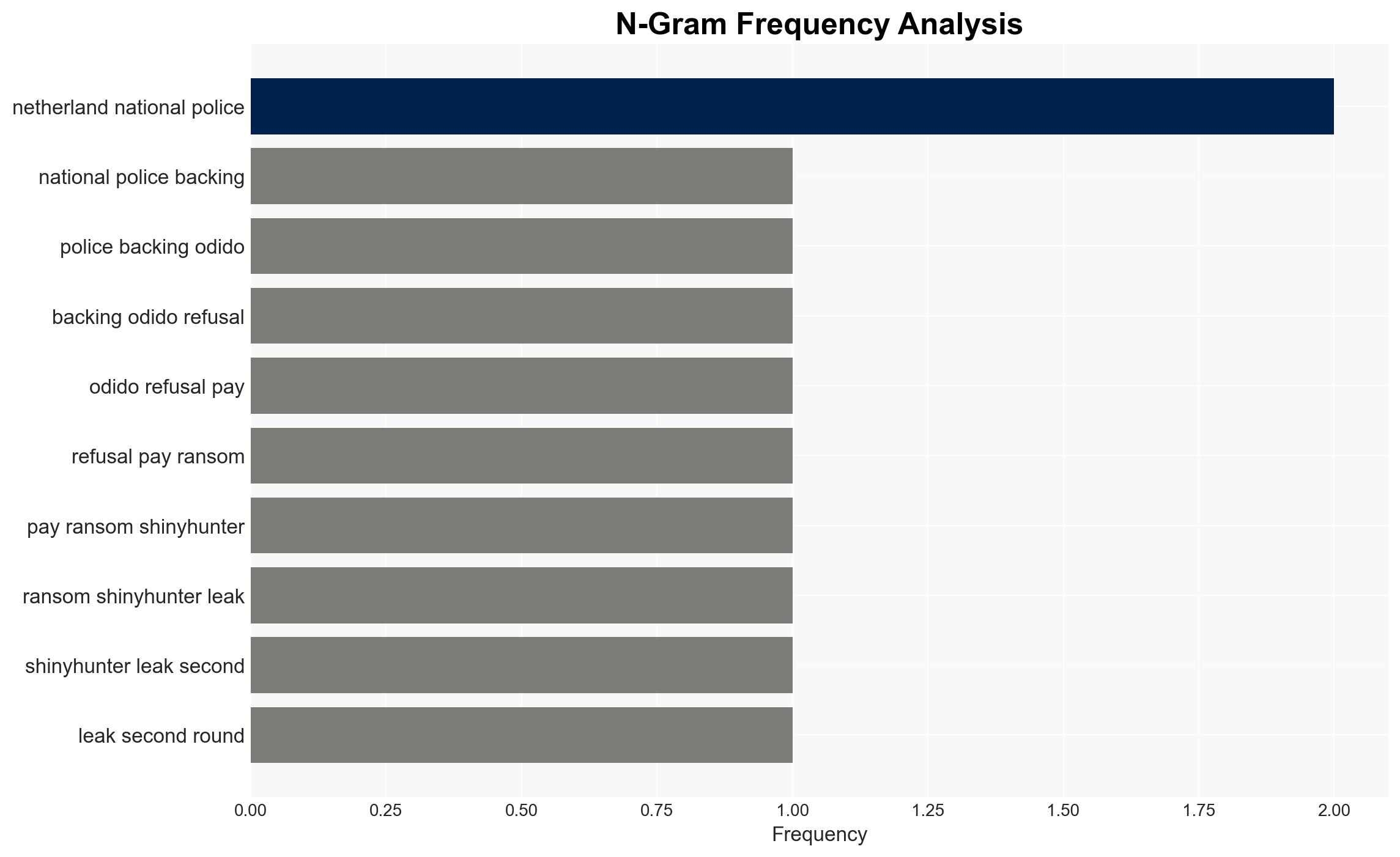
The Netherlands’ national police support Odido’s decision not to pay a ransom following a significant data breach by ShinyHunters. The breach has exposed sensitive data of potentially over 1 million customers, with further leaks anticipated. The decision not to pay is aligned with broader law enforcement advice, though it may lead to continued data exposure. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: ShinyHunters will continue to leak data until a ransom is paid. This is supported by the group’s past behavior and threats of further leaks. However, the refusal to pay by Odido and police backing may deter future ransom demands.
- Hypothesis B: ShinyHunters may cease leaks due to law enforcement pressure or diminishing returns. This is less supported given their current trajectory and lack of immediate deterrents, but increased police involvement could shift this.
- Assessment: Hypothesis A is currently better supported due to ShinyHunters’ ongoing actions and threats. Key indicators that could shift this include increased law enforcement actions or changes in the group’s operational capacity.
3. Key Assumptions and Red Flags
- Assumptions: ShinyHunters has the capacity to continue leaks; Odido’s refusal to pay aligns with long-term strategic interests; law enforcement support will deter future attacks.
- Information Gaps: The total volume of data stolen and the full scope of ShinyHunters’ capabilities remain unclear.
- Bias & Deception Risks: Potential bias in police statements aiming to discourage ransom payments; possibility of ShinyHunters exaggerating their capabilities or data volume.
4. Implications and Strategic Risks
The ongoing data leaks could exacerbate tensions between private sector entities and cybercriminal groups, influencing future ransom negotiations and law enforcement strategies.
- Political / Geopolitical: Increased pressure on Dutch and EU cyber policies; potential for international cooperation on cybercrime.
- Security / Counter-Terrorism: Elevated risk of targeted phishing and identity theft; potential for increased cybercrime activity.
- Cyber / Information Space: Potential for heightened cyber defense measures and information sharing among telcos.
- Economic / Social: Possible loss of consumer trust in Odido; broader economic impacts if similar attacks occur across the sector.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of ShinyHunters’ activities; increase public awareness on phishing risks; strengthen data protection measures.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms; invest in advanced threat detection capabilities; engage in policy advocacy for stronger cybercrime deterrents.
- Scenario Outlook:
- Best: ShinyHunters ceases operations under law enforcement pressure.
- Worst: Continued leaks lead to severe reputational and financial damage for Odido.
- Most-Likely: Ongoing leaks with gradual law enforcement progress in disrupting ShinyHunters.
6. Key Individuals and Entities
- Odido (Dutch telecommunications company)
- ShinyHunters (cybercriminal group)
- Politie (Netherlands’ national police)
- Stan Duijf (Head of operations, Politie)
- Søren Abildgaard (CEO, Odido Netherlands)
7. Thematic Tags
cybersecurity, ransomware, data breach, law enforcement, telecommunications, cybercrime, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us