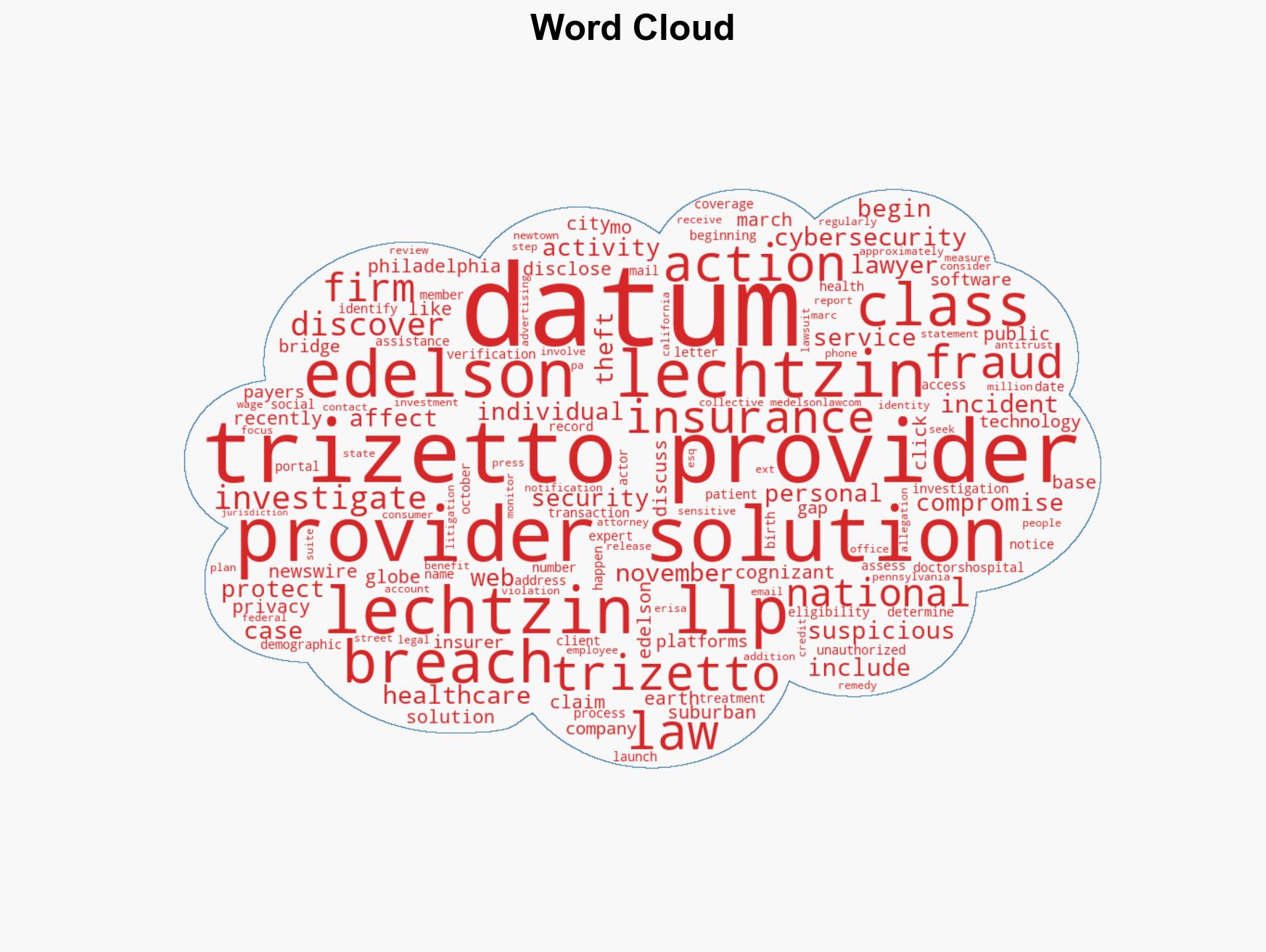
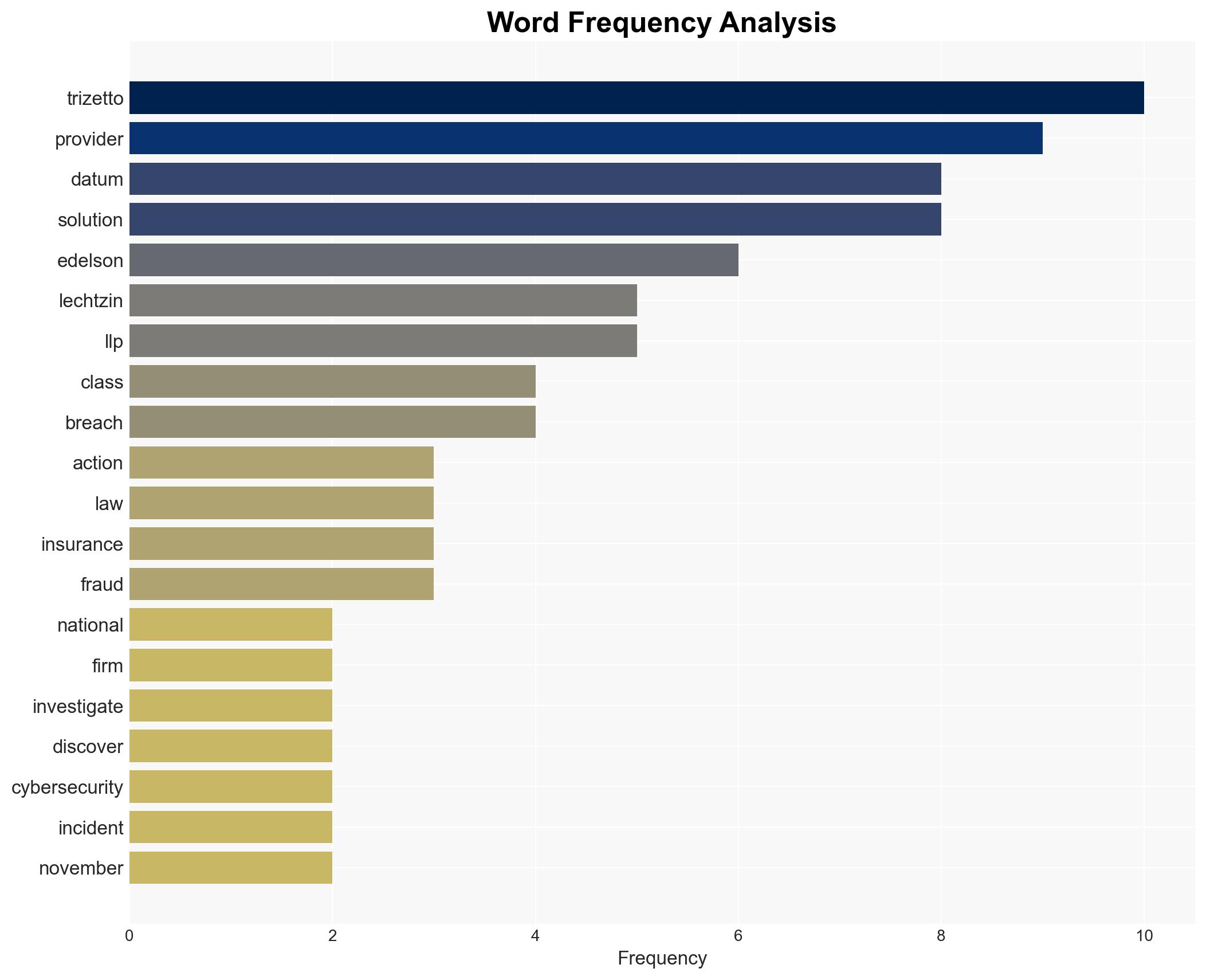
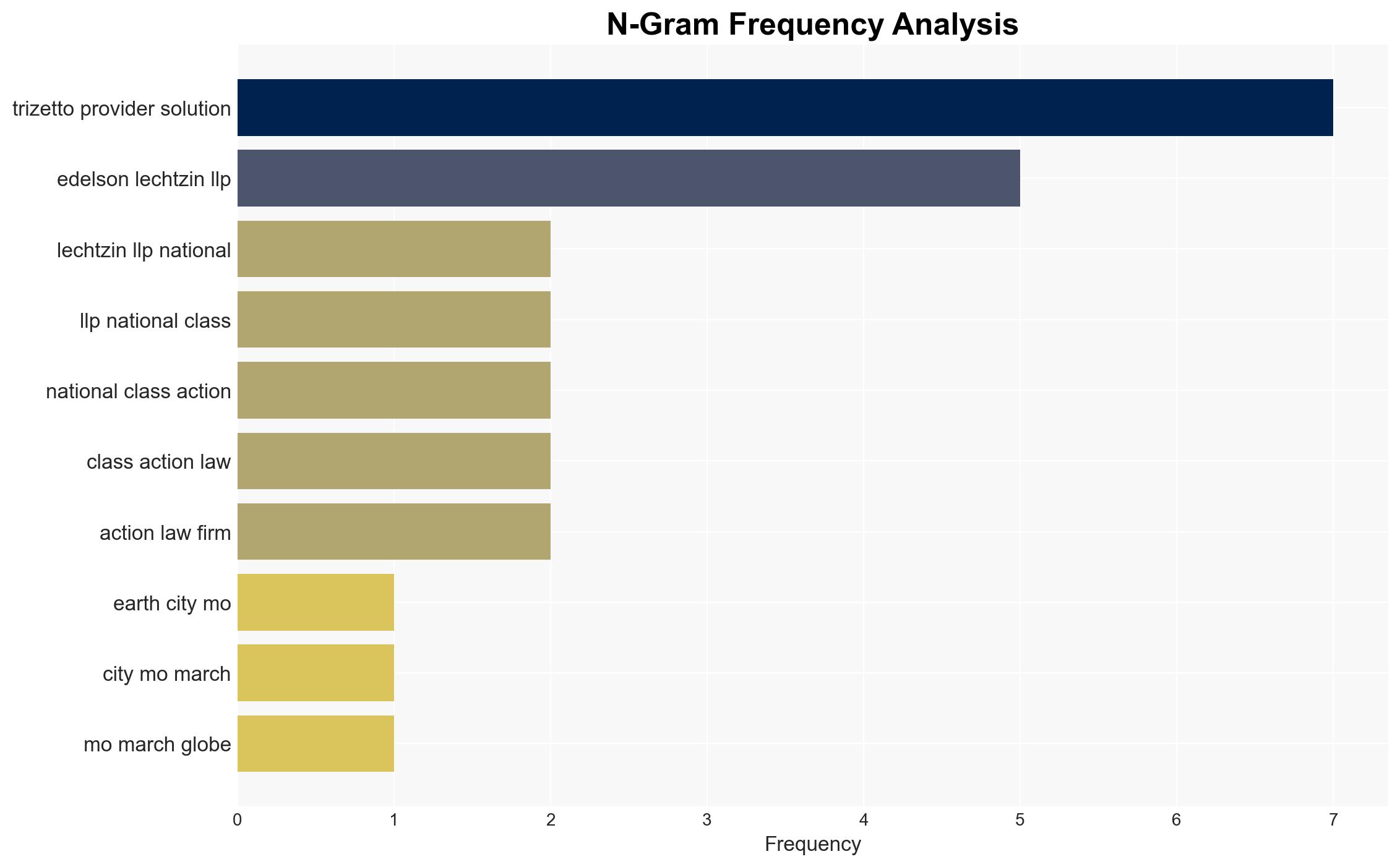
Edelson Lechtzin LLP Investigates TriZetto Provider Solutions Data Breach Affecting Personal Information
Published on: 2026-03-08
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: DATA BREACH ALERT Edelson Lechtzin LLP is Investigating Claims on Behalf of Persons Affected by the TriZetto Provider Solutions TPS Data Breach
1. BLUF (Bottom Line Up Front)
The TriZetto Provider Solutions data breach, affecting approximately 3.4 million individuals, exposed sensitive personal and health information. The breach, active since November 2024, was disclosed in March 2026, suggesting a significant delay in detection and response. The most likely hypothesis is that the breach resulted from sophisticated cyber intrusion tactics. Overall confidence in this assessment is moderate due to limited details on the breach’s technical aspects.
2. Competing Hypotheses
- Hypothesis A: The data breach was a result of a targeted cyber attack by a sophisticated threat actor. Supporting evidence includes the prolonged unauthorized access and the nature of the data targeted. Key uncertainties involve the identity and motives of the threat actor.
- Hypothesis B: The breach was due to internal negligence or misconfiguration, allowing unauthorized access. While possible, this is less supported given the duration and complexity of the breach. Evidence contradicting this includes the engagement of cybersecurity experts, suggesting external intrusion.
- Assessment: Hypothesis A is currently better supported due to the breach’s complexity and the sensitive nature of the data accessed. Indicators that could shift this judgment include new evidence of internal vulnerabilities or insider involvement.
3. Key Assumptions and Red Flags
- Assumptions: The breach was externally initiated; TriZetto’s cybersecurity measures were insufficient; the data accessed is valuable for identity theft.
- Information Gaps: Specific technical details of the breach, identity of the threat actor, and the exact timeline of unauthorized access.
- Bias & Deception Risks: Potential bias in reporting from involved legal parties; lack of independent verification of breach details; possible underreporting of breach impact by TriZetto.
4. Implications and Strategic Risks
This data breach could lead to significant legal, financial, and reputational repercussions for TriZetto and its parent company, Cognizant Technology Solutions. The exposure of sensitive data may increase identity theft and fraud risks for affected individuals.
- Political / Geopolitical: Limited direct geopolitical impact, but potential for increased regulatory scrutiny on data protection practices.
- Security / Counter-Terrorism: Heightened risk environment for healthcare data security; potential exploitation by cybercriminals.
- Cyber / Information Space: Increased focus on cybersecurity measures and potential for further cyber incidents targeting healthcare data.
- Economic / Social: Financial liabilities for TriZetto; potential loss of consumer trust and increased demand for robust data protection measures.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of affected individuals’ data, conduct a thorough forensic investigation, and improve immediate cybersecurity measures.
- Medium-Term Posture (1–12 months): Develop stronger partnerships with cybersecurity firms, invest in advanced threat detection technologies, and conduct regular security audits.
- Scenario Outlook:
- Best: Rapid containment and remediation with minimal legal and financial fallout.
- Worst: Prolonged legal battles, significant financial penalties, and loss of client trust.
- Most-Likely: Moderate legal challenges and financial impacts, with gradual recovery of reputation.
6. Key Individuals and Entities
- TriZetto Provider Solutions
- Cognizant Technology Solutions
- Edelson Lechtzin LLP
- Marc Edelson, Esq.
7. Thematic Tags
cybersecurity, data breach, healthcare data, identity theft, legal action, information security, privacy protection
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us