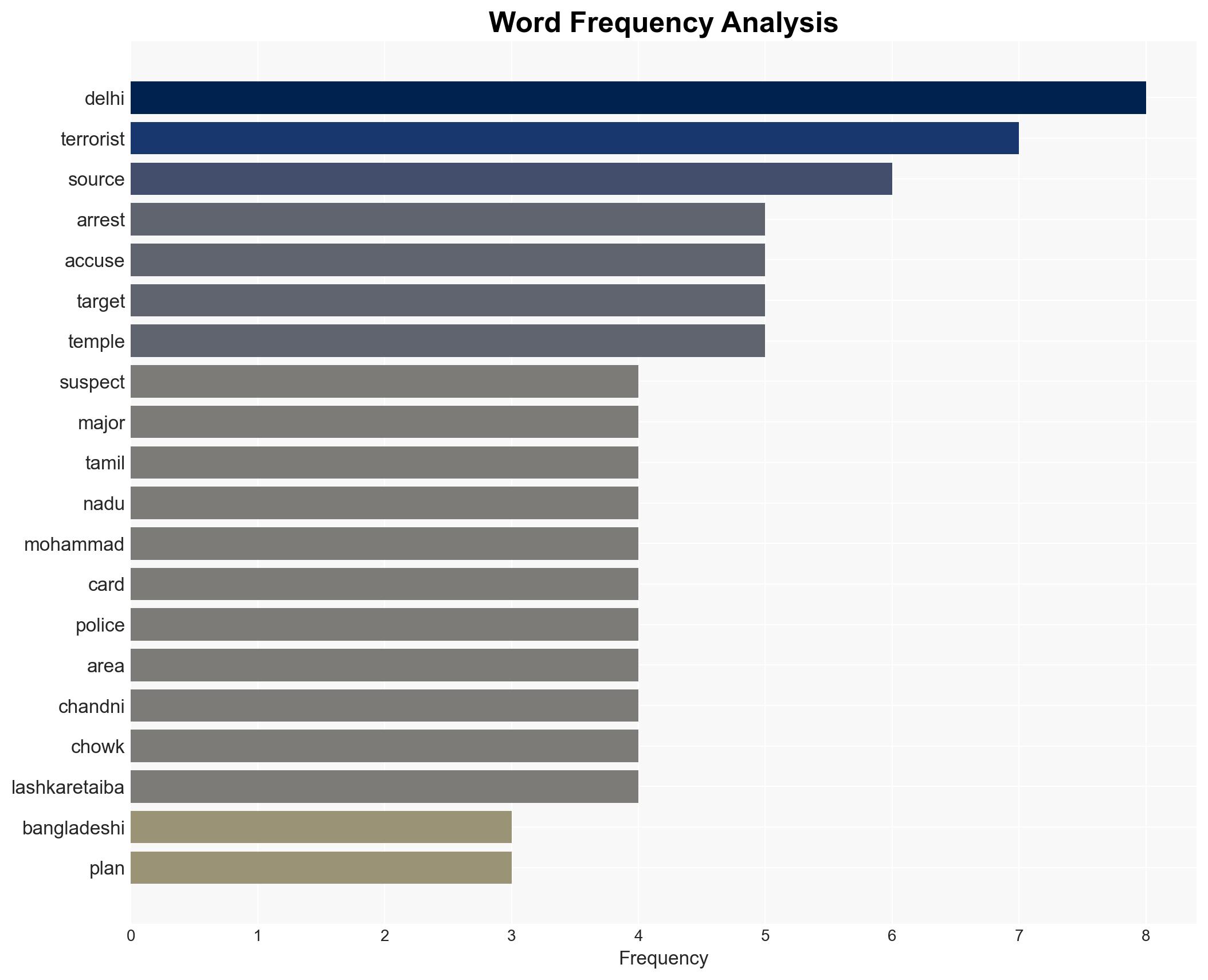
Eight individuals, including a Bangladeshi, detained in Tamil Nadu for alleged ties to ISI and terrorism plots
Published on: 2026-02-22
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Six suspects with Bangladeshi and ISI links arrested in Tamil Nadu
1. BLUF (Bottom Line Up Front)
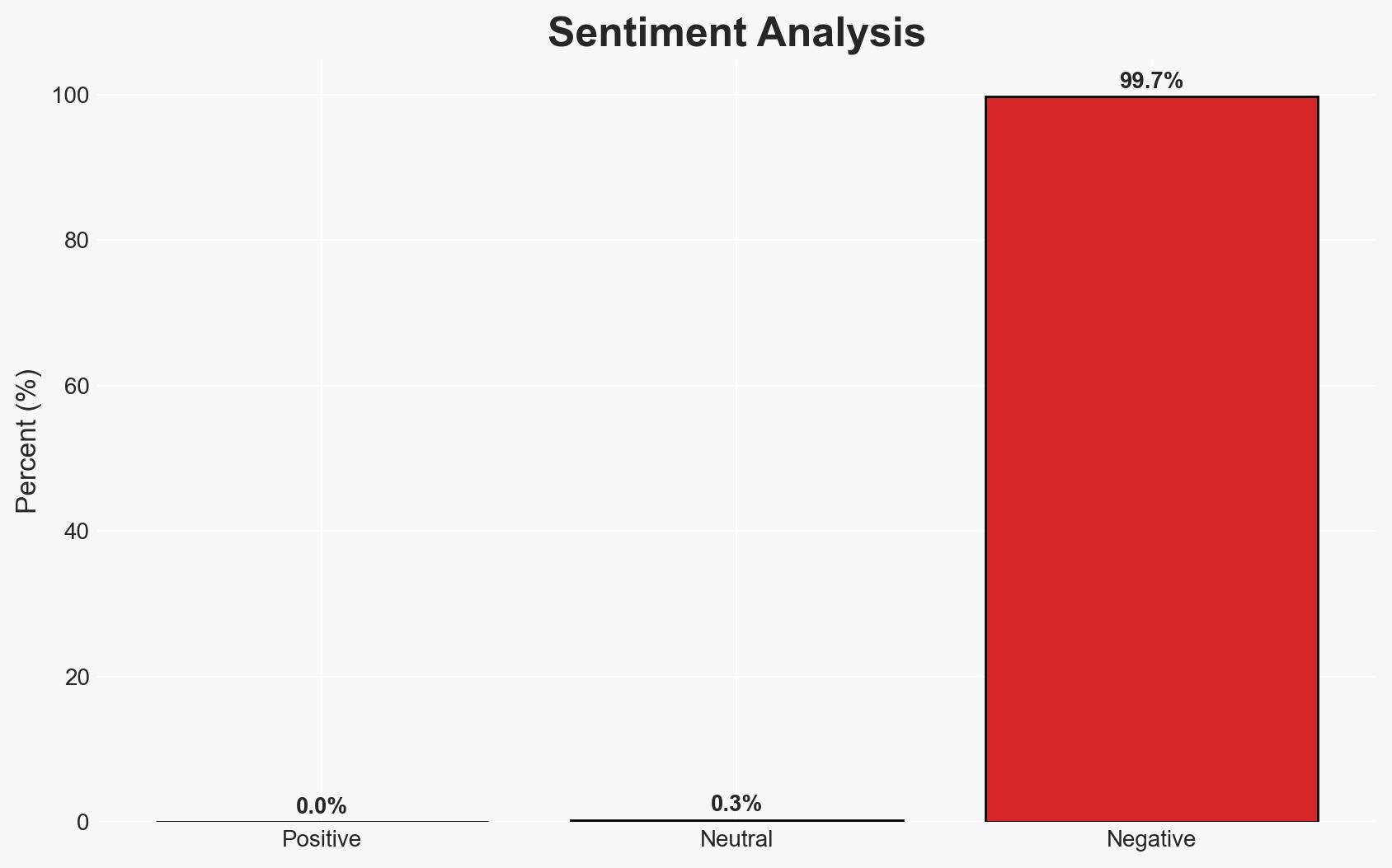
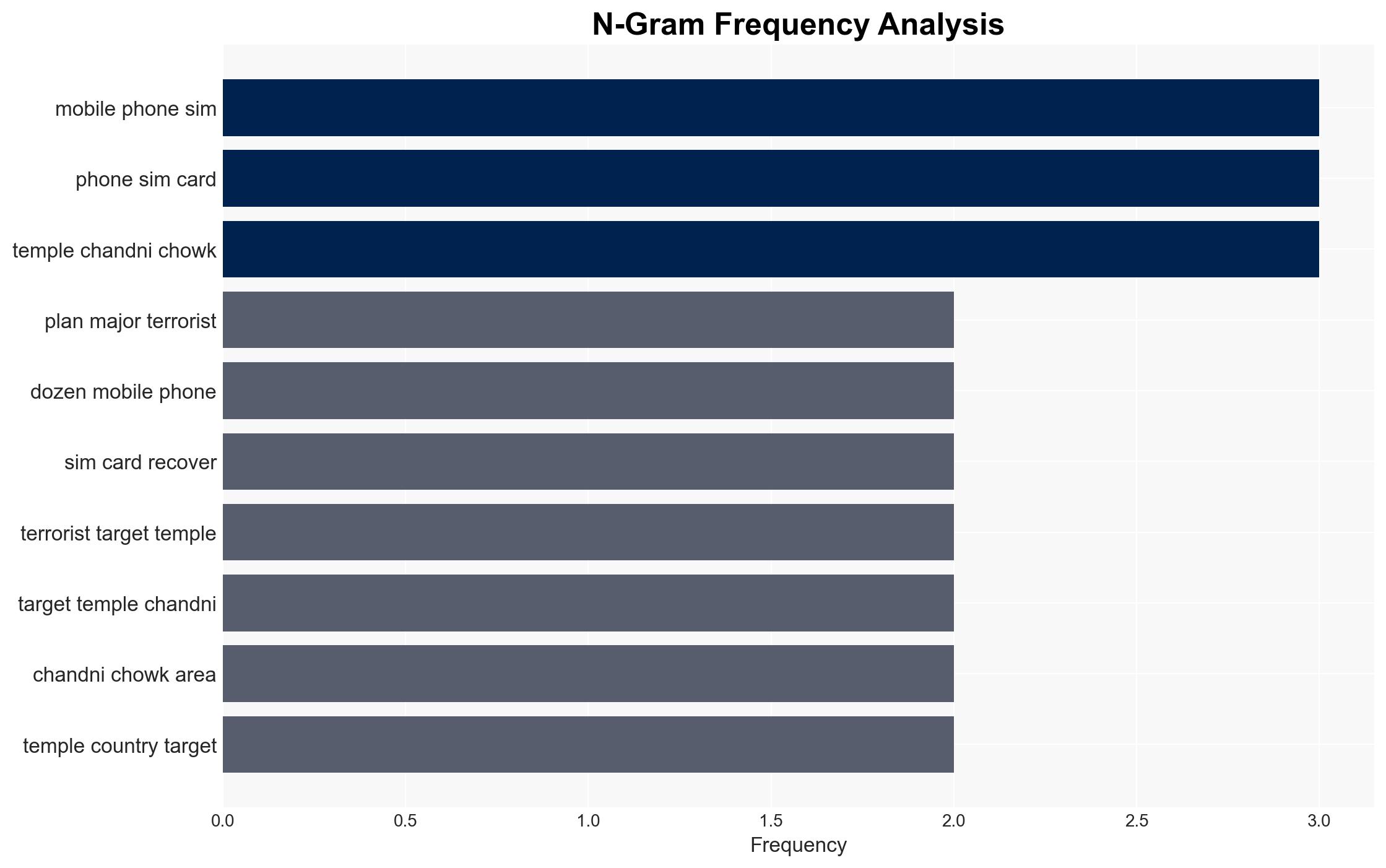
The arrest of eight suspects with alleged links to Bangladeshi terrorist organizations and Pakistan’s ISI in Tamil Nadu highlights a potential cross-border terrorism nexus targeting India. The arrests may have disrupted a planned attack, but the full extent of the network and its capabilities remain uncertain. This development poses a moderate threat to national security, with moderate confidence in the current assessment.
2. Competing Hypotheses
- Hypothesis A: The suspects were part of a coordinated effort by ISI and Bangladeshi terrorist groups to conduct a terrorist attack in India. Supporting evidence includes their connections to these organizations and the recovery of communication devices. However, the lack of direct evidence linking them to a specific plot remains a key uncertainty.
- Hypothesis B: The suspects were independently radicalized individuals with no direct operational links to ISI or organized terrorist groups, possibly acting on ideological motivations. This is contradicted by their coordinated activities and use of fake identities, suggesting a more organized effort.
- Assessment: Hypothesis A is currently better supported due to the suspects’ connections to known terrorist organizations and the recovery of multiple communication devices, indicating coordination. Further intelligence could shift this judgment if it reveals a lack of direct operational control by ISI or Bangladeshi groups.
3. Key Assumptions and Red Flags
- Assumptions: The suspects have genuine links to ISI and Bangladeshi terrorist groups; the arrests have disrupted an imminent attack; the recovered devices contain actionable intelligence.
- Information Gaps: The specific objectives and targets of the suspects; the full extent of their network; the level of ISI’s involvement.
- Bias & Deception Risks: Potential over-reliance on initial police reports; possible misinformation from suspects; bias in interpreting communications as indicative of a larger plot.
4. Implications and Strategic Risks
This development could exacerbate regional tensions and influence India’s counter-terrorism posture. The arrests may deter immediate threats but could also provoke retaliatory actions.
- Political / Geopolitical: Potential strain on India-Bangladesh relations; increased scrutiny on Pakistan’s alleged support for terrorism.
- Security / Counter-Terrorism: Heightened alert levels in major cities; potential for increased counter-terrorism operations.
- Cyber / Information Space: Possible increase in propaganda or recruitment efforts online by terrorist organizations.
- Economic / Social: Potential impact on tourism and foreign investment due to perceived security risks.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance surveillance and intelligence-sharing with regional partners; conduct thorough analysis of recovered devices; increase security at potential targets.
- Medium-Term Posture (1–12 months): Strengthen counter-terrorism capabilities; engage in diplomatic efforts to address cross-border terrorism; develop community outreach programs to counter radicalization.
- Scenario Outlook:
- Best: Disruption of network leads to long-term reduction in threat level.
- Worst: Retaliatory attacks occur, escalating regional tensions.
- Most-Likely: Continued low-level threats with sporadic incidents requiring ongoing vigilance.
6. Key Individuals and Entities
- Mizanur Rahman
- Mohammad Shabat
- Umar
- Mohammad Litan
- Mohammad Shahid
- Mohammad Ujjal
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
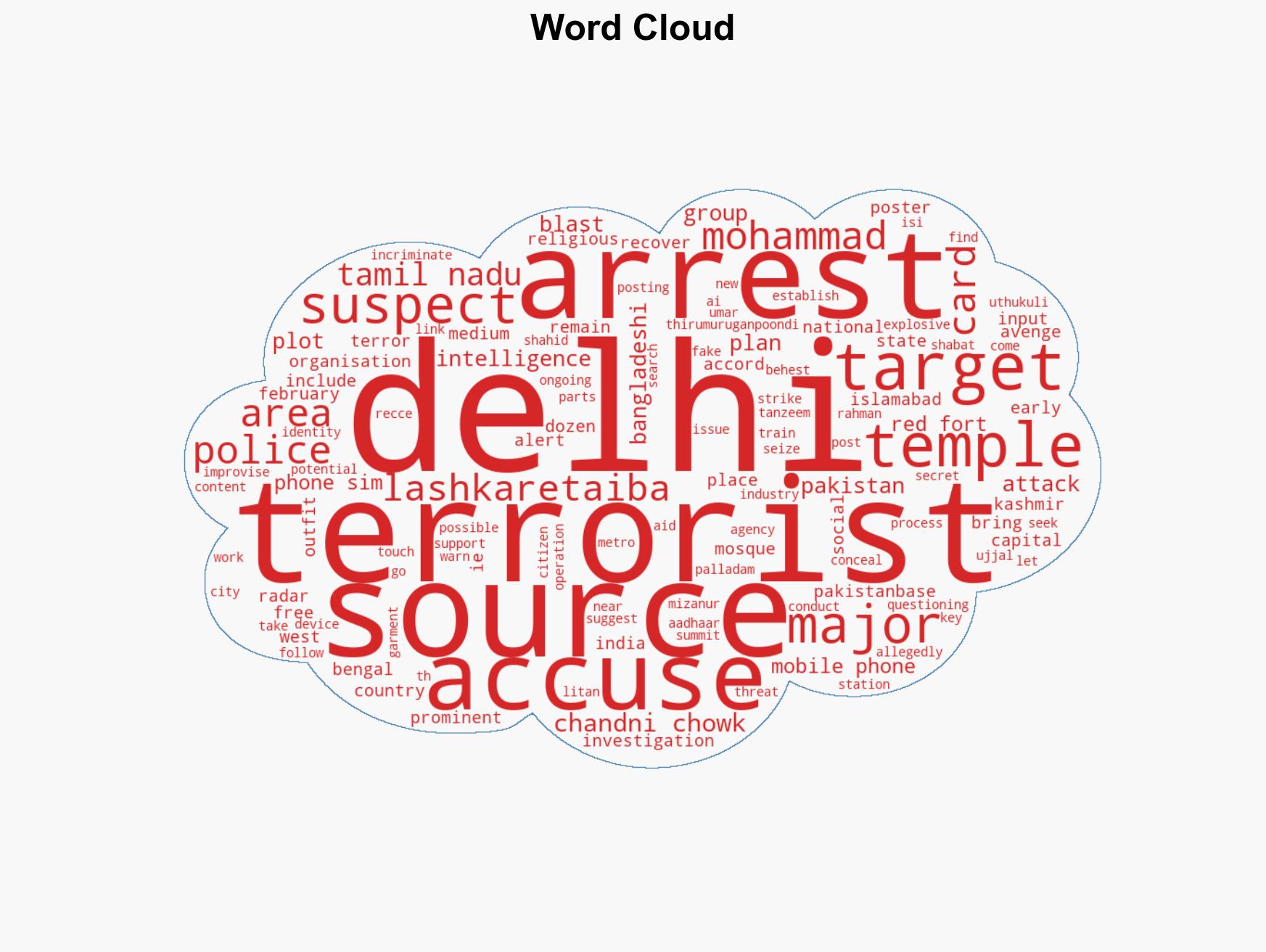
Counter-Terrorism, cross-border terrorism, ISI, Bangladesh, Lashkar-e-Taiba, radicalization, national security
Structured Analytic Techniques Applied
- ACH 2.0: Reconstruct likely threat actor intentions via hypothesis testing and structured refutation.
- Indicators Development: Track radicalization signals and propaganda patterns to anticipate operational planning.
- Narrative Pattern Analysis: Analyze spread/adaptation of ideological narratives for recruitment/incitement signals.
Explore more:
Counter-Terrorism Briefs ·
Daily Summary ·
Support us