ELECQ Reports Ransomware Attack Compromising Customer Data, No Financial Information Affected
Published on: 2026-03-09
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
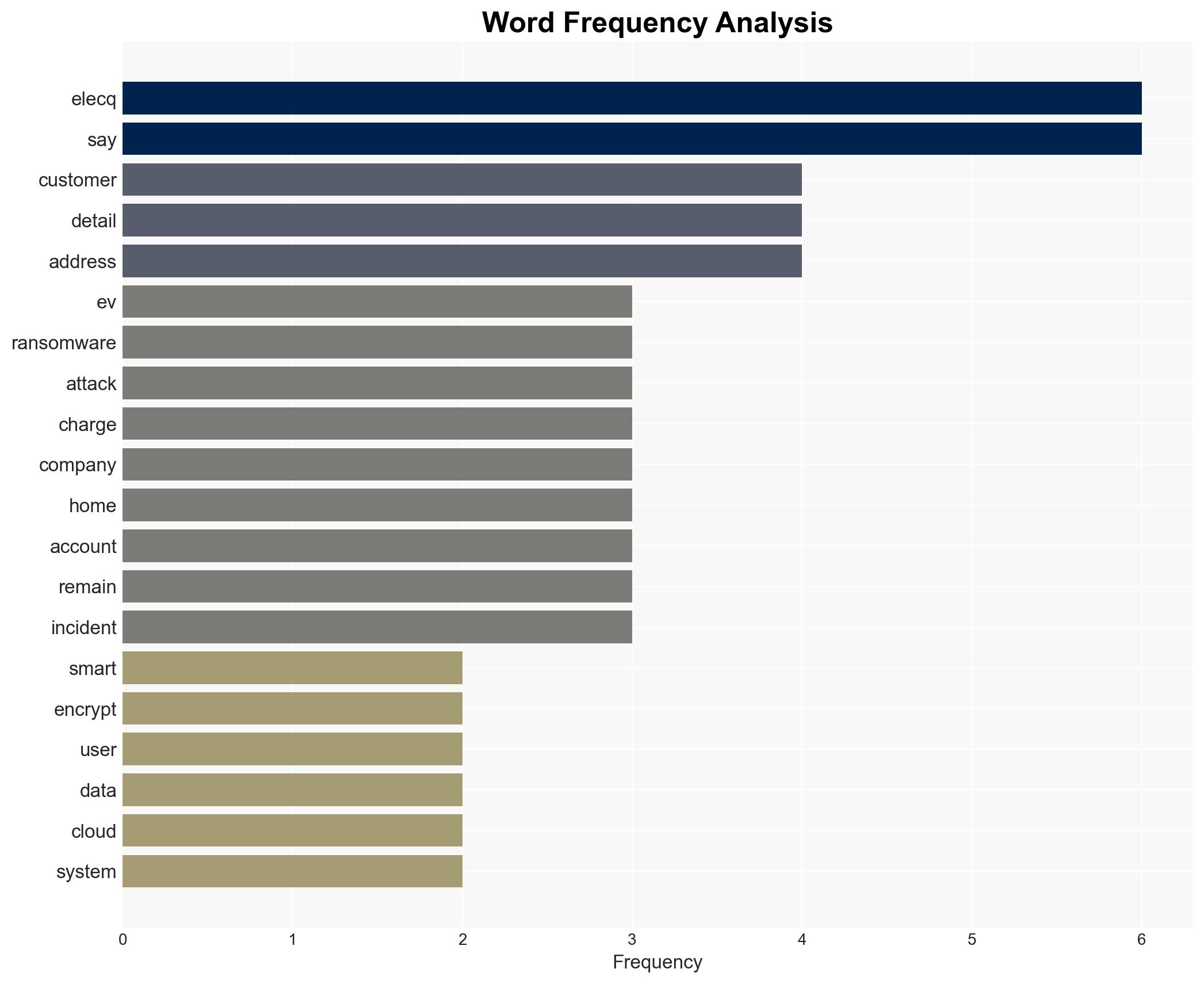
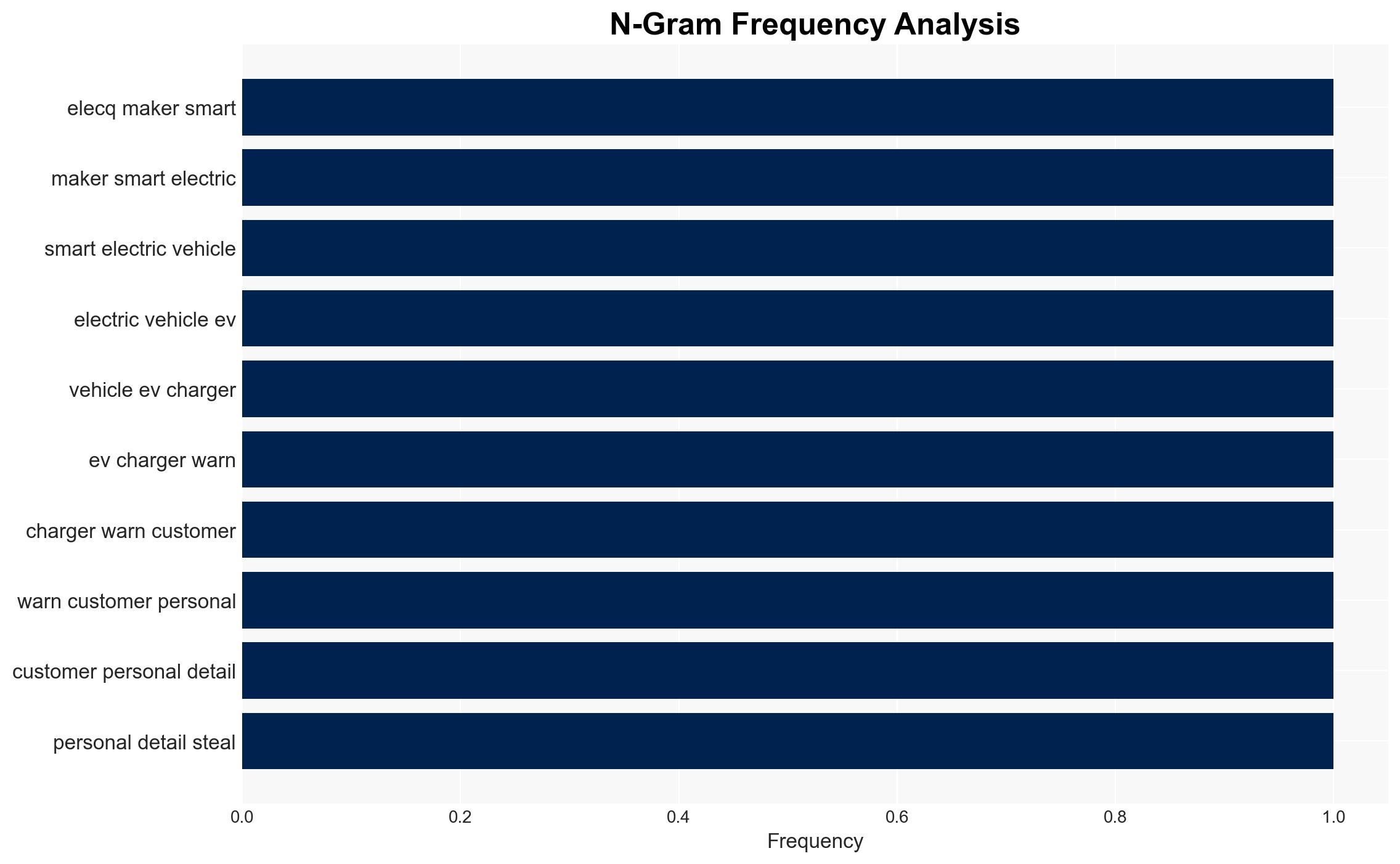
Intelligence Report: EV charger biz ELECQ zapped by ransomware crooks customer contact data stolen
1. BLUF (Bottom Line Up Front)
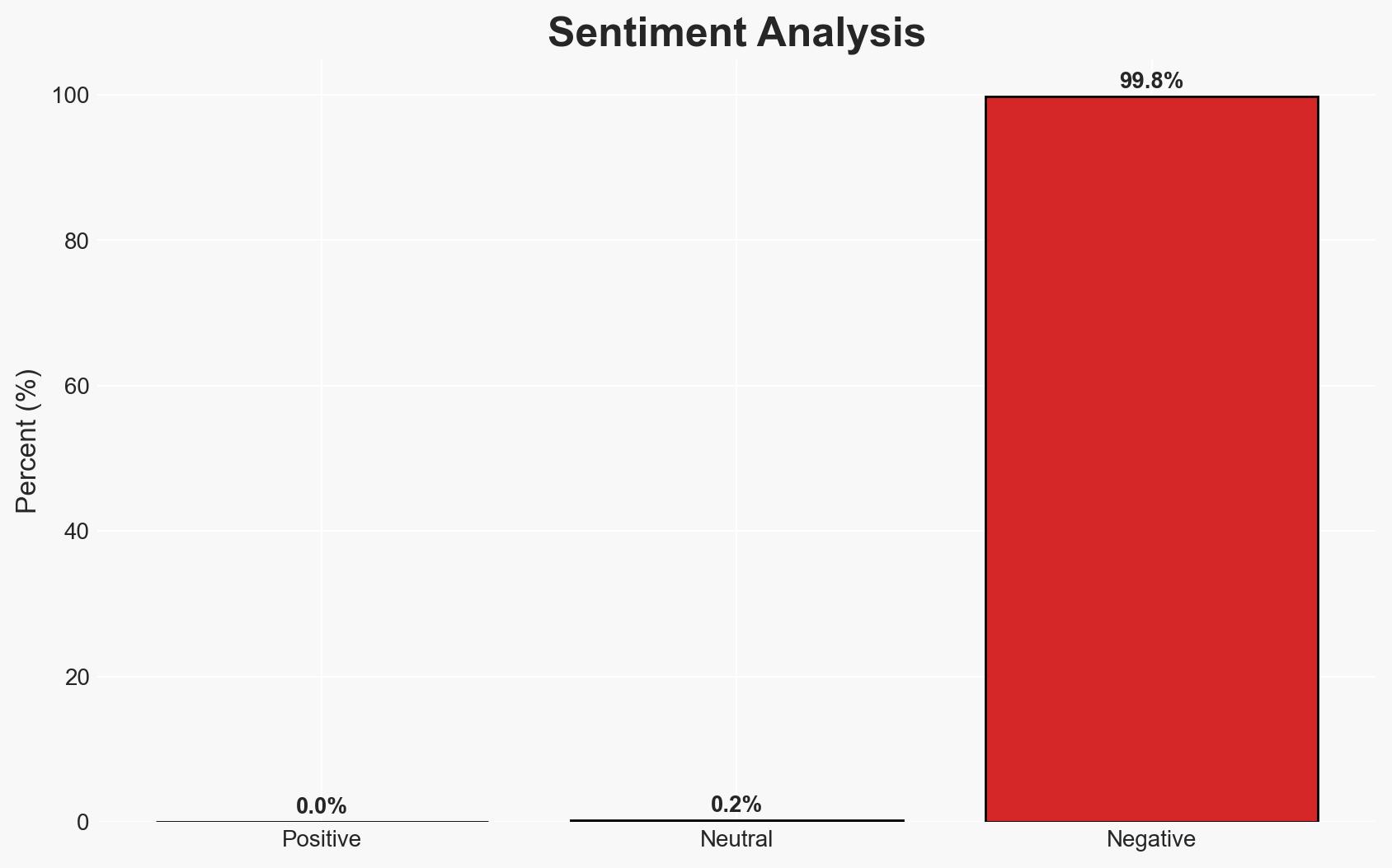
The ransomware attack on ELECQ, a Chinese EV charger manufacturer, resulted in the theft of customer contact data. The incident highlights vulnerabilities in cloud-based infrastructures and poses risks of social engineering attacks. The most likely hypothesis is that the attack was financially motivated, targeting data for potential resale or ransom. Overall confidence in this assessment is moderate due to incomplete information on the attackers and the scale of the breach.
2. Competing Hypotheses
- Hypothesis A: The ransomware attack was financially motivated, aiming to steal and potentially sell customer data. This is supported by the theft of personal information and the typical objectives of ransomware groups. However, the absence of a reported ransom demand introduces uncertainty.
- Hypothesis B: The attack was a state-sponsored operation intended to gather intelligence on EV infrastructure. This is less supported due to the lack of evidence indicating state involvement or strategic data targeting beyond standard personal information.
- Assessment: Hypothesis A is currently better supported due to the nature of the data stolen and common ransomware tactics. Indicators such as a ransom demand or further data leaks could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The attackers are financially motivated; ELECQ’s incident response measures are effective; the breach is limited to personal contact data.
- Information Gaps: The identity of the attackers, the total number of affected individuals, and whether a ransom was demanded or paid.
- Bias & Deception Risks: Potential underreporting by ELECQ to minimize reputational damage; reliance on company-provided information without independent verification.
4. Implications and Strategic Risks
This incident could lead to increased scrutiny of cybersecurity practices in the EV sector and influence regulatory policies. The breach may also encourage similar attacks on other tech companies.
- Political / Geopolitical: Potential diplomatic tensions if state involvement is suspected or if data of foreign nationals is compromised.
- Security / Counter-Terrorism: Increased risk of social engineering attacks using the stolen data.
- Cyber / Information Space: Highlighting vulnerabilities in cloud-based systems and the need for enhanced security protocols.
- Economic / Social: Possible erosion of consumer trust in smart EV technology and impact on ELECQ’s market position.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of ELECQ’s networks, advise customers on protective measures against phishing, and verify ELECQ’s security enhancements.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing, and invest in cybersecurity training and infrastructure upgrades.
- Scenario Outlook:
- Best: No further data leaks and improved cybersecurity practices industry-wide.
- Worst: Additional breaches occur, leading to significant financial and reputational damage.
- Most-Likely: ELECQ strengthens its security, but similar attacks occur in the sector, prompting regulatory action.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
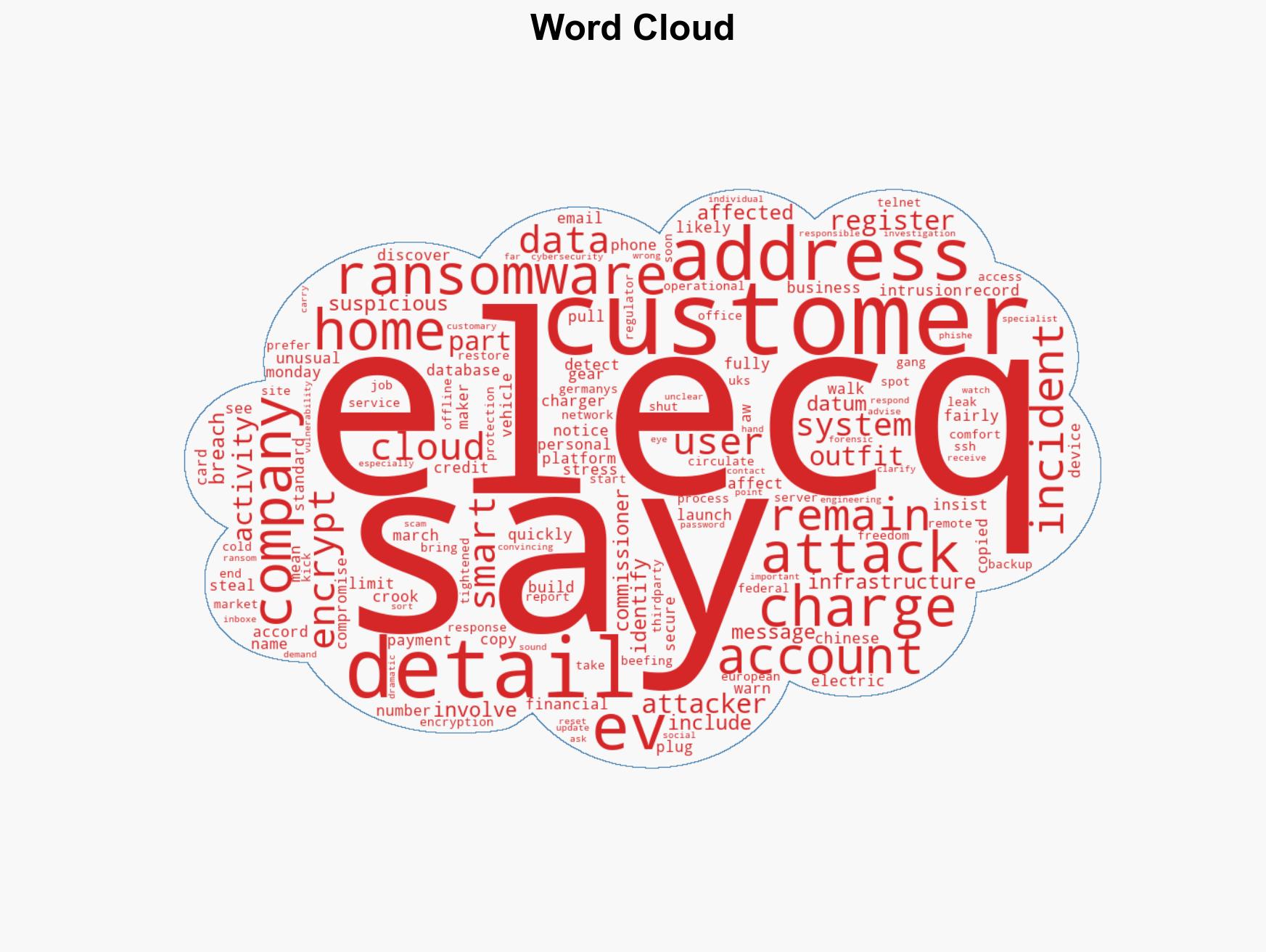
cybersecurity, ransomware, data breach, electric vehicles, cloud security, social engineering, regulatory impact
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us