Elon Musk’s X might have a mole problem How could someone enumerate all Twitter user IDs unless they were an employee – Windows Central
Published on: 2025-04-02
Intelligence Report: Elon Musk’s X might have a mole problem – Windows Central
1. BLUF (Bottom Line Up Front)
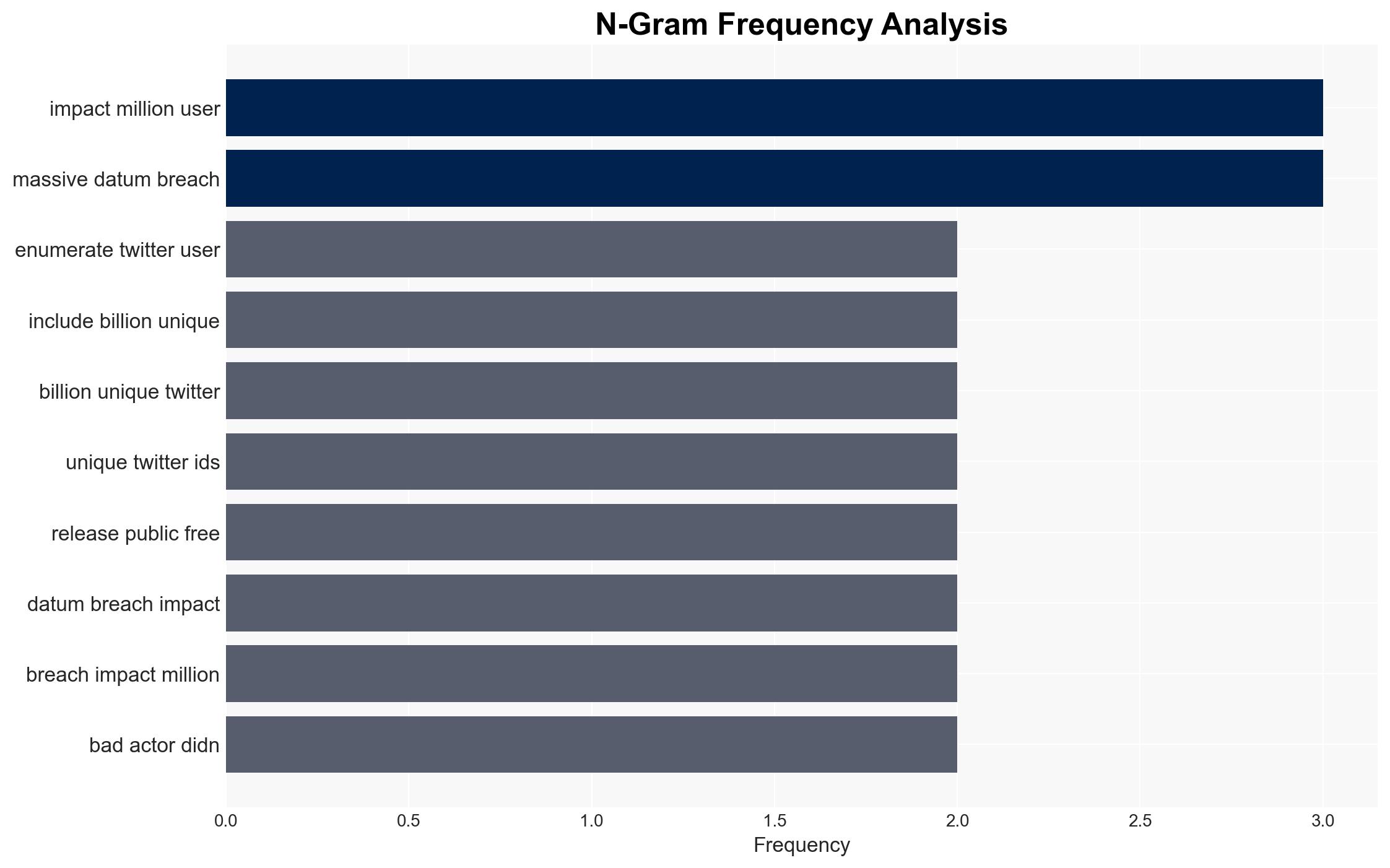
A significant data breach has occurred involving the release of over a billion unique Twitter user IDs, potentially linked to internal actors within the organization. This breach poses substantial security risks, including increased phishing attempts and privacy violations. Immediate action is required to identify the breach source, secure the platform, and mitigate further risks.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
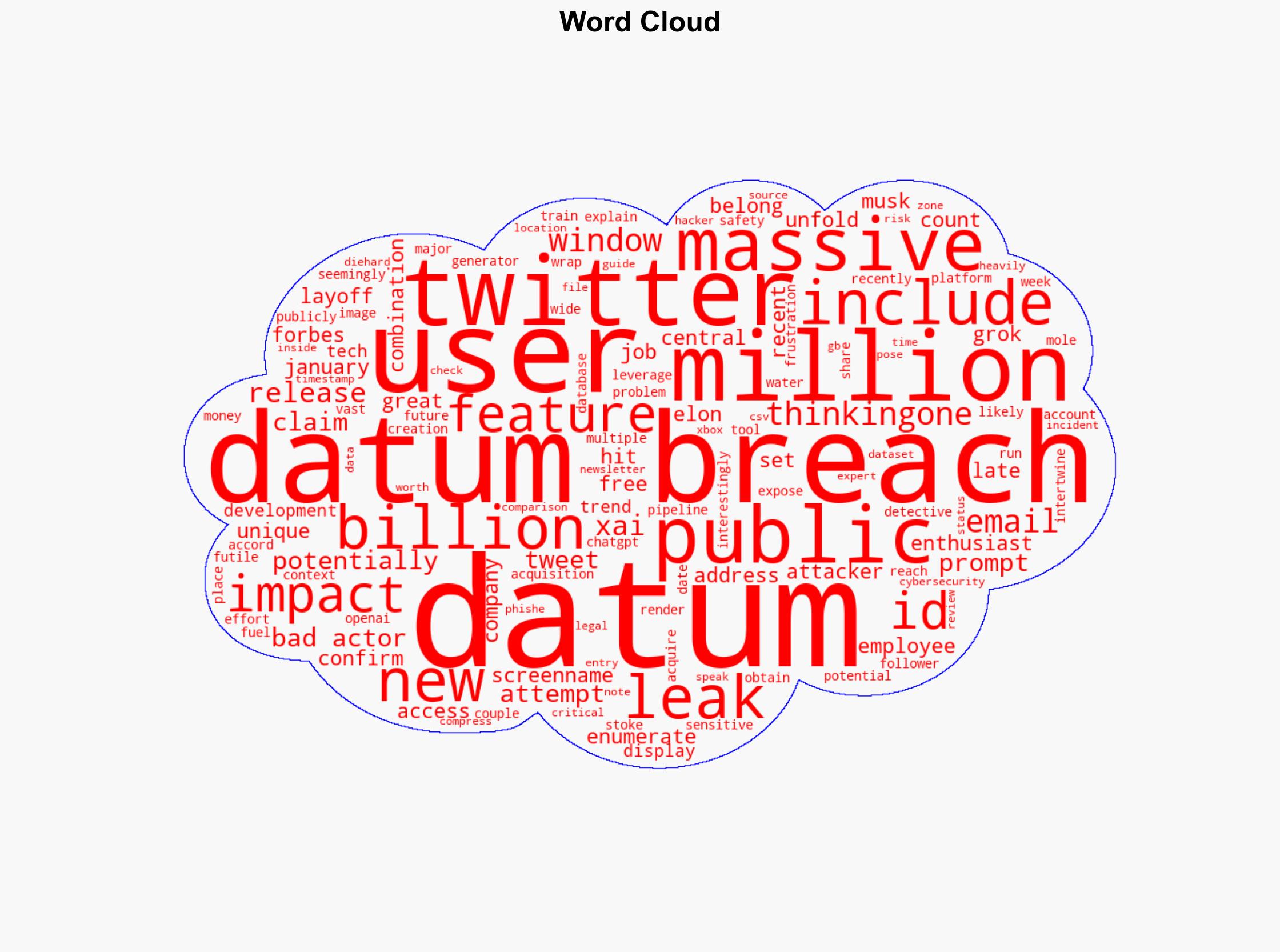
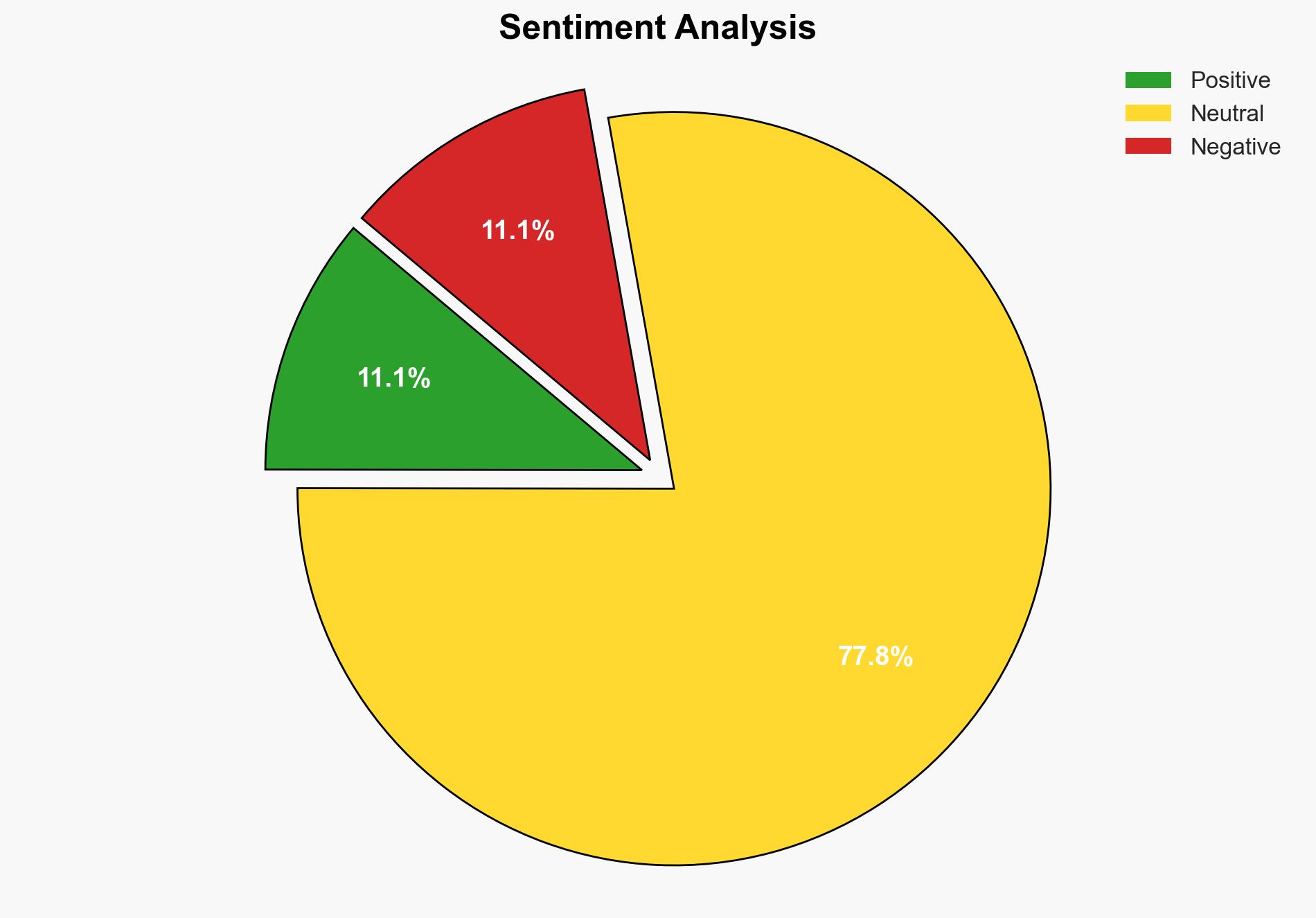
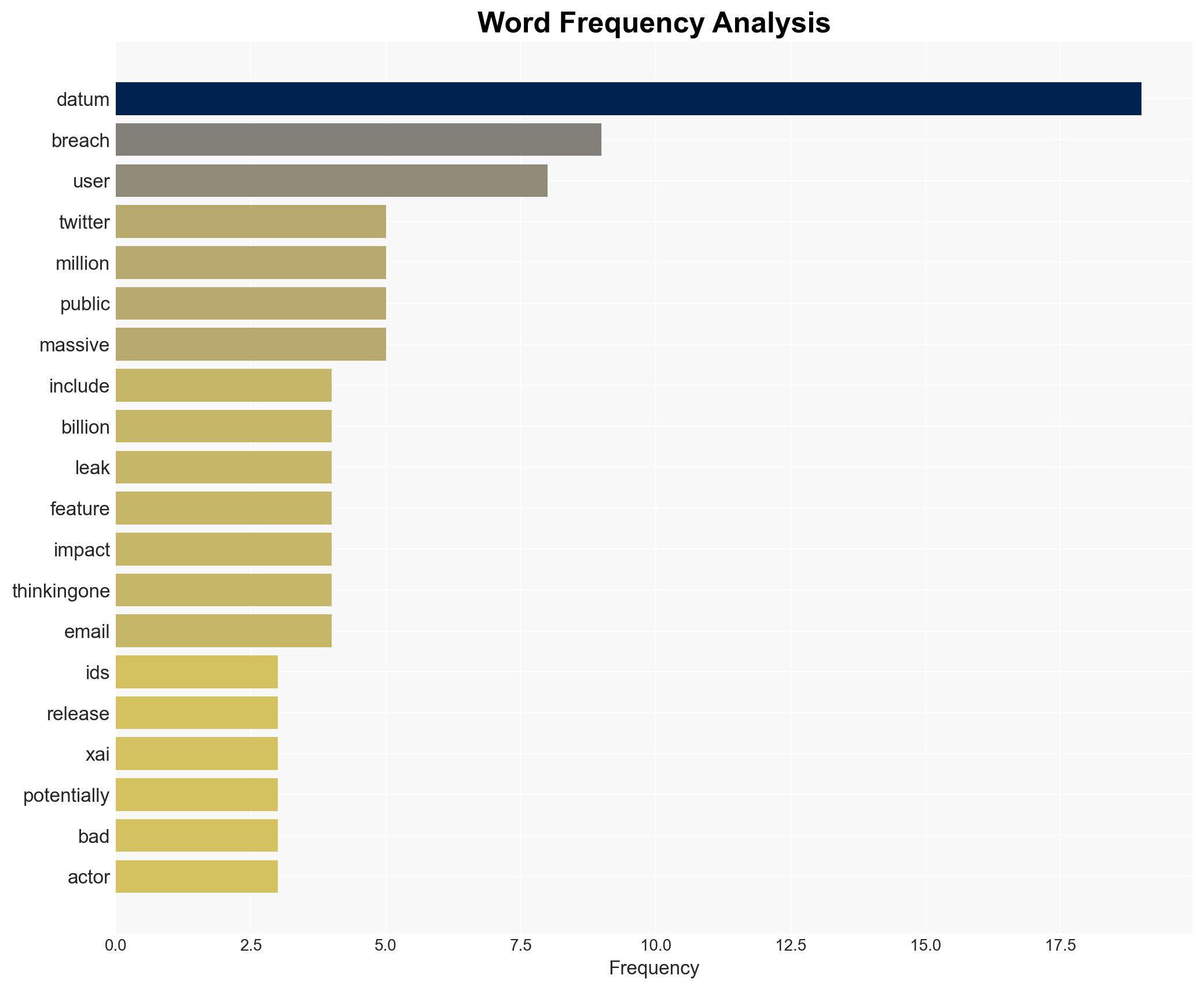
The data breach involved the public release of a dataset containing over a billion unique Twitter user IDs, along with associated user information such as email addresses, usernames, follower counts, and account creation dates. The breach coincided with significant organizational changes, including layoffs, suggesting potential insider involvement. The breach’s scale indicates a sophisticated operation, possibly facilitated by individuals with intimate knowledge of the platform’s infrastructure.
3. Implications and Strategic Risks
The breach poses several strategic risks:
- Increased phishing and cyber-attack risks due to the availability of user data.
- Potential damage to the organization’s reputation, affecting user trust and engagement.
- Legal and regulatory repercussions stemming from data privacy violations.
- Economic impacts due to potential loss of users and advertisers.
The breach could also have broader implications for national security if exploited by malicious actors for targeted attacks.
4. Recommendations and Outlook
Recommendations:
- Conduct a thorough internal investigation to identify and address the source of the breach.
- Enhance cybersecurity measures, including employee access controls and monitoring systems.
- Engage with legal and regulatory bodies to ensure compliance and mitigate potential penalties.
- Implement a comprehensive communication strategy to restore user trust and transparency.
Outlook:
Best-case scenario: The breach source is identified and contained quickly, with minimal impact on user trust and platform integrity.
Worst-case scenario: Continued data leaks lead to significant user attrition, legal challenges, and financial losses.
Most likely outcome: The organization implements corrective measures, stabilizing the situation but facing ongoing scrutiny and trust rebuilding efforts.
5. Key Individuals and Entities
The report highlights the involvement of Elon Musk and references the potential insider threat, emphasizing the need for strategic responses to mitigate risks associated with the breach.