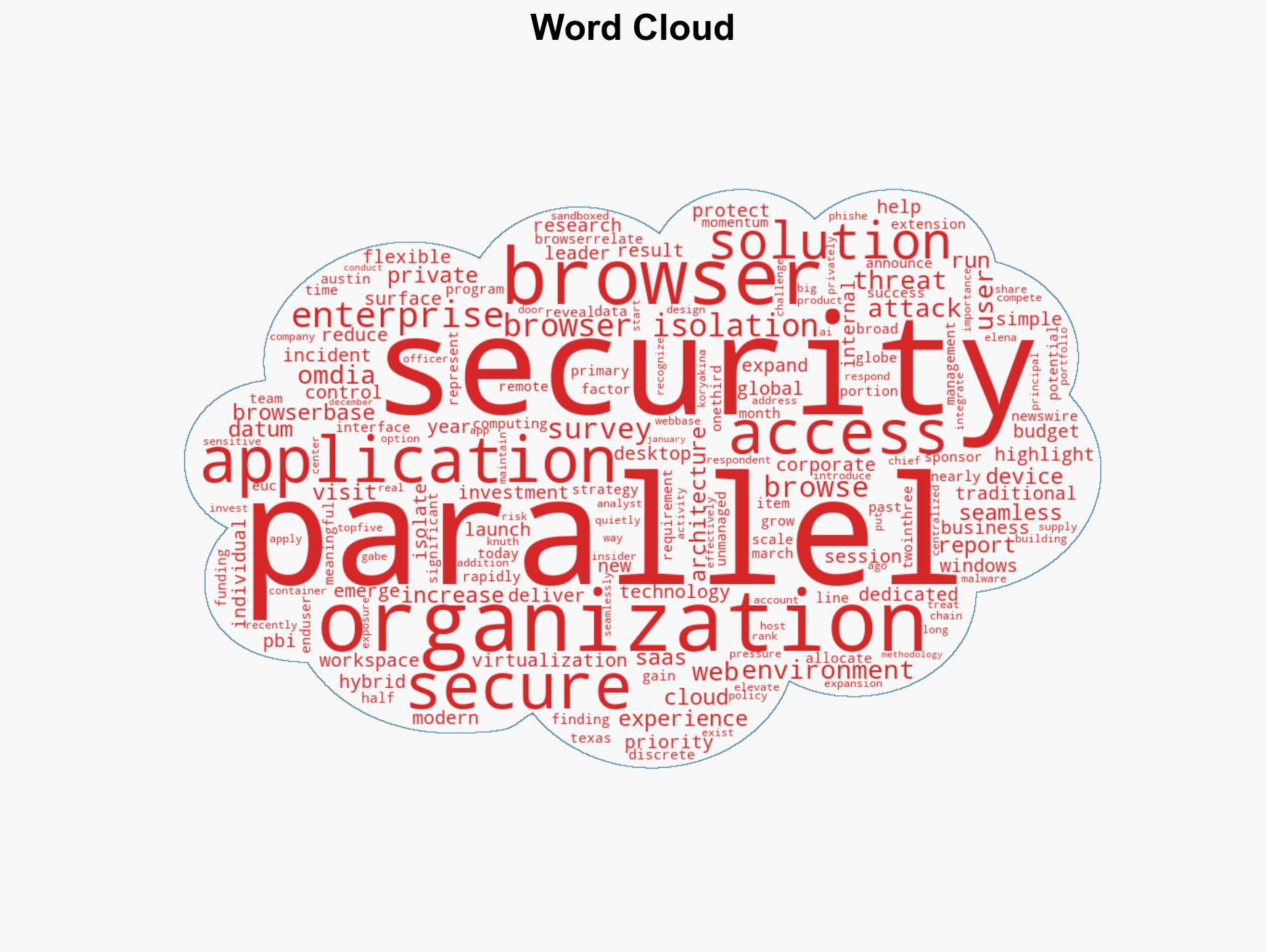
Enterprise Security Spending Rises as Browser Attacks Surge, Omdia Research Reveals
Published on: 2026-03-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Browsers Become Prime Cybercrime Target as 85 of Enterprises Increase Security Spending Omdia Research Finds
1. BLUF (Bottom Line Up Front)
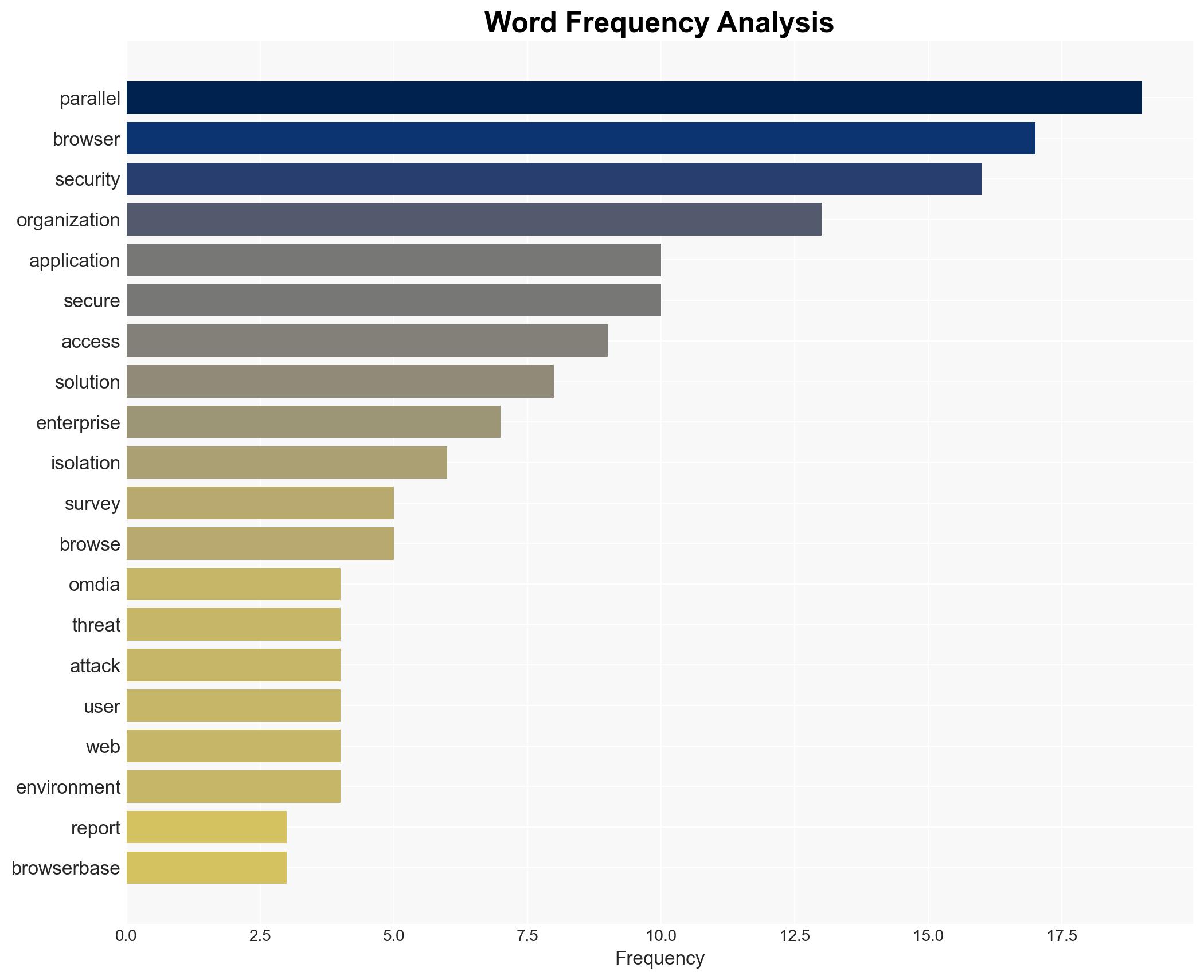
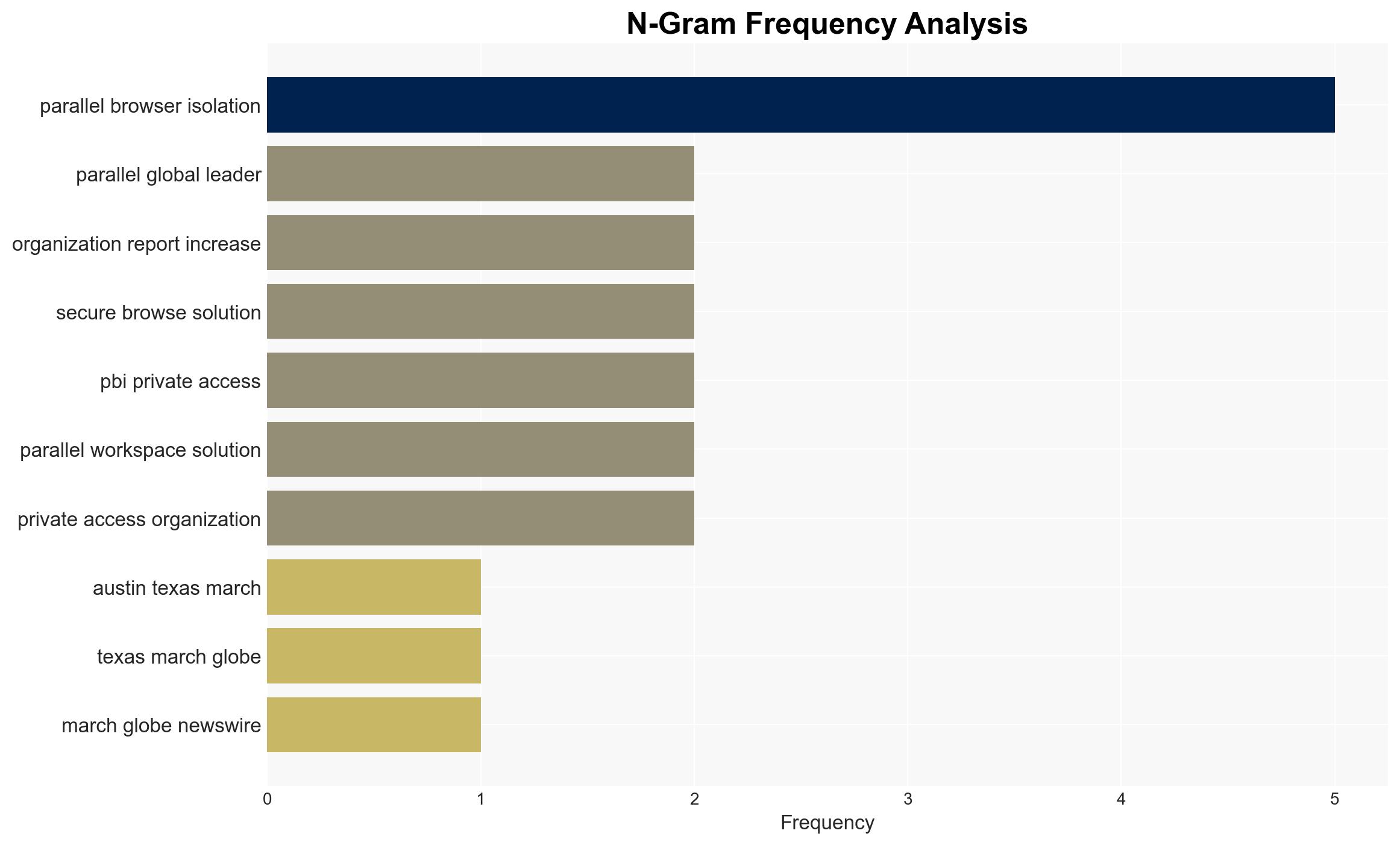
Browser security has emerged as a critical priority for enterprises due to increasing browser-based cyber threats. The majority of organizations are ramping up investments in secure browsing technologies to mitigate these risks. This trend is likely to continue as the browser becomes a primary interface for enterprise applications. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The increase in browser-based attacks is primarily due to the growing use of unmanaged devices accessing corporate applications, expanding the attack surface. This is supported by the reported rise in browser-based threats and the significant investment in browser security. However, the exact contribution of unmanaged devices to the increase in attacks remains uncertain.
- Hypothesis B: The rise in browser-based attacks is largely due to improved detection and reporting mechanisms rather than an actual increase in attacks. While the report highlights increased incidents, it does not explicitly differentiate between actual attack frequency and improved threat visibility.
- Assessment: Hypothesis A is currently better supported due to the correlation between increased use of unmanaged devices and the rise in browser-based threats. Key indicators that could shift this judgment include data on attack vectors and the role of detection improvements.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will continue to prioritize browser security; unmanaged devices significantly contribute to the attack surface; current investments will effectively mitigate browser-based threats.
- Information Gaps: Detailed data on the specific types of browser-based attacks and their origins; effectiveness metrics of current browser security solutions.
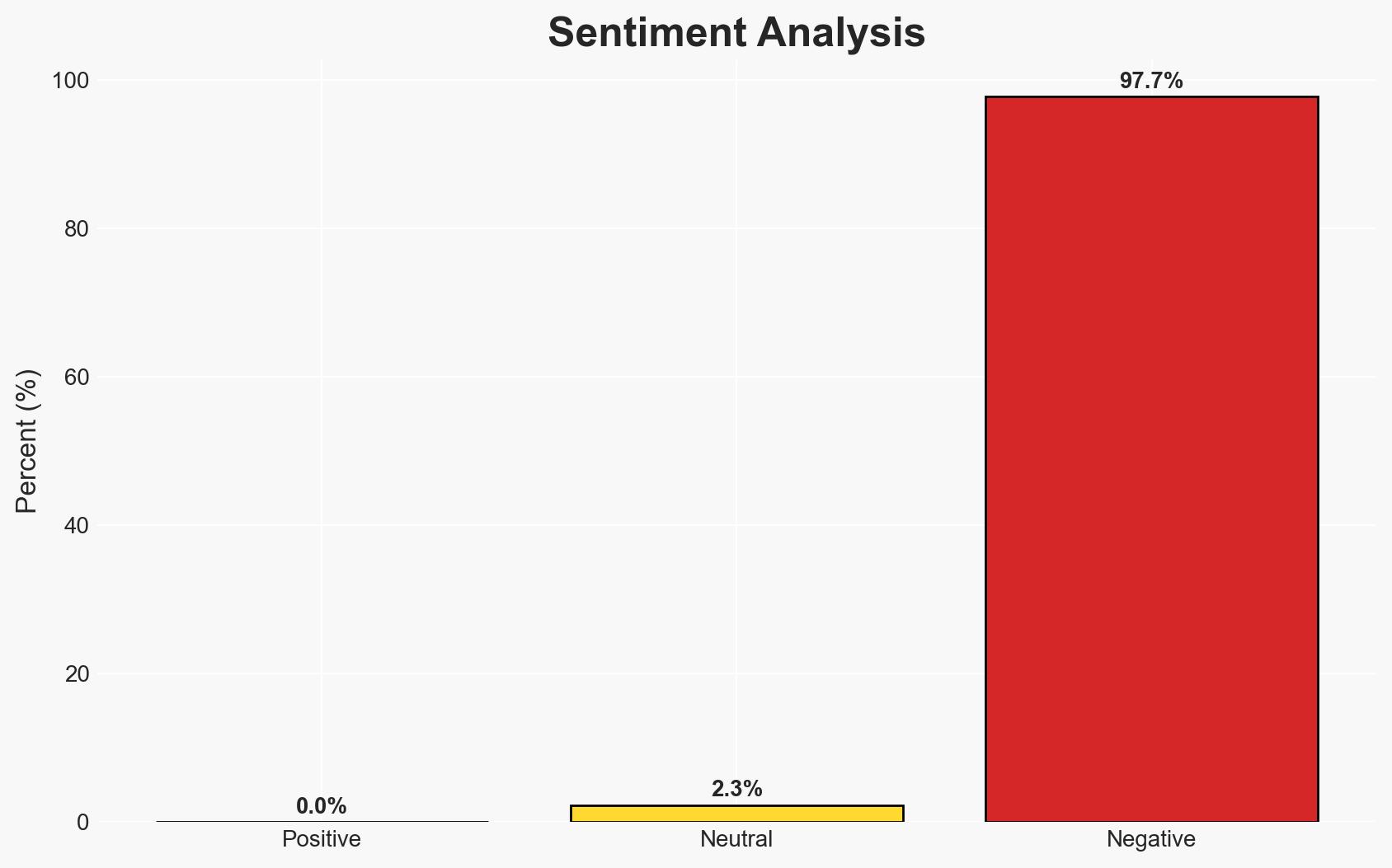
- Bias & Deception Risks: Potential bias in the report due to sponsorship by Parallels; reliance on self-reported data from enterprises may lead to over or underestimation of threat levels.
4. Implications and Strategic Risks
The growing focus on browser security may lead to shifts in enterprise security strategies and budgets, potentially impacting other areas of cybersecurity investment.
- Political / Geopolitical: Increased browser security could reduce vulnerabilities exploited by state-sponsored actors, potentially altering cyber espionage dynamics.
- Security / Counter-Terrorism: Enhanced browser security may decrease the success rate of cyber-attacks, including those by terrorist organizations.
- Cyber / Information Space: The emphasis on browser security could drive innovation in secure browsing technologies and influence cyber defense strategies.
- Economic / Social: Increased security spending may strain budgets, particularly for smaller enterprises, potentially affecting economic stability and competitiveness.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor developments in browser security technologies; assess organizational exposure to browser-based threats.
- Medium-Term Posture (1–12 months): Develop partnerships with technology providers for secure browsing solutions; enhance training programs for employees on secure browsing practices.
- Scenario Outlook:
- Best: Effective implementation of browser security solutions significantly reduces cyber threats.
- Worst: Browser security investments fail to keep pace with evolving threats, leading to increased incidents.
- Most-Likely: Gradual improvement in security posture with ongoing adjustments to address emerging threats.
6. Key Individuals and Entities
- Gabe Knuth, Principal Analyst at Omdia
- Elena Koryakina, Chief Product and Technology Officer at Parallels
- Parallels
- Omdia
7. Thematic Tags
cybersecurity, browser security, enterprise IT, cyber threats, unmanaged devices, secure browsing, cyber defense
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us