Ericsson US reports data breach affecting over 15,000 employees and customers due to service provider hack
Published on: 2026-03-09
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Ericsson US discloses data breach after service provider hack
1. BLUF (Bottom Line Up Front)
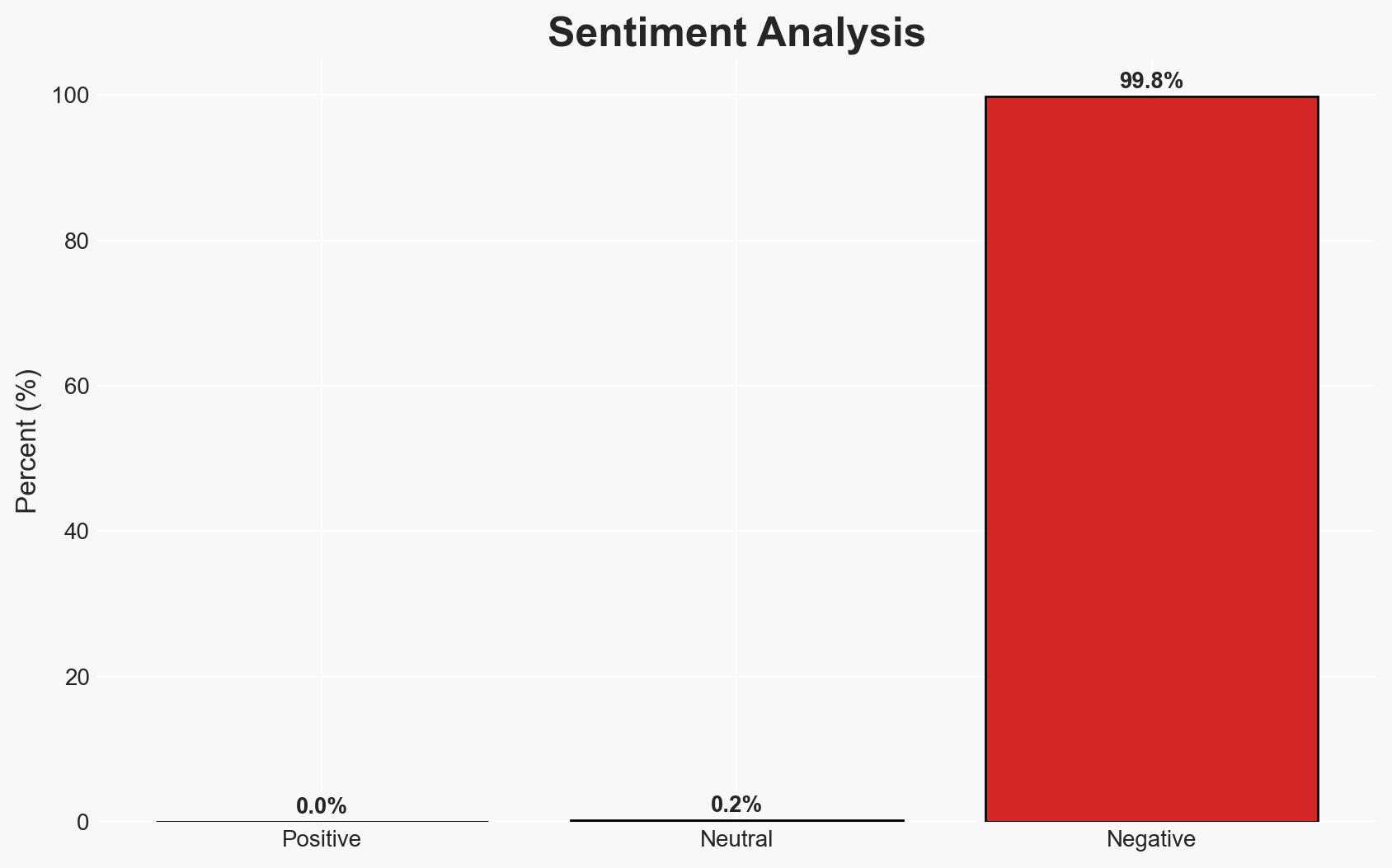
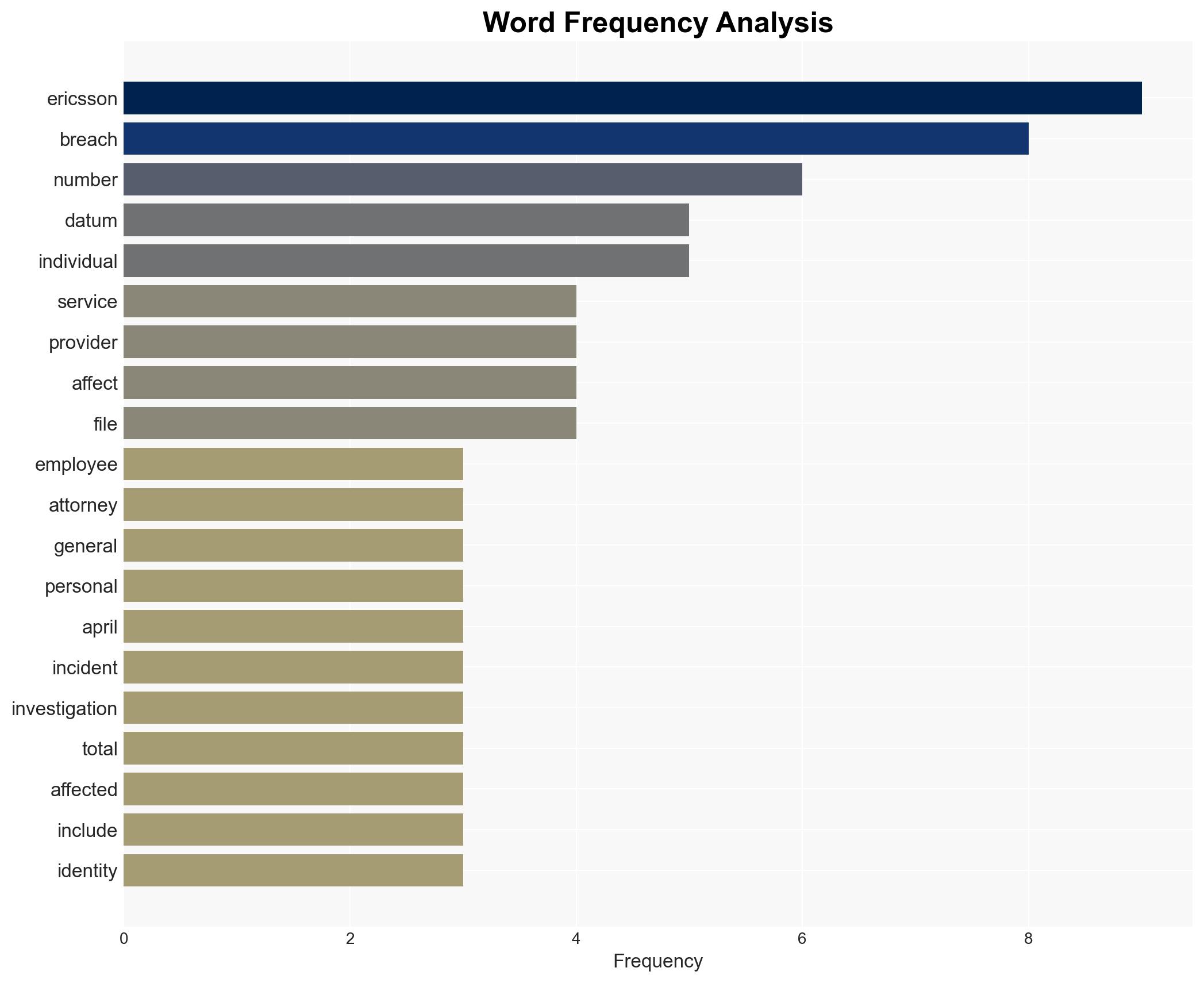
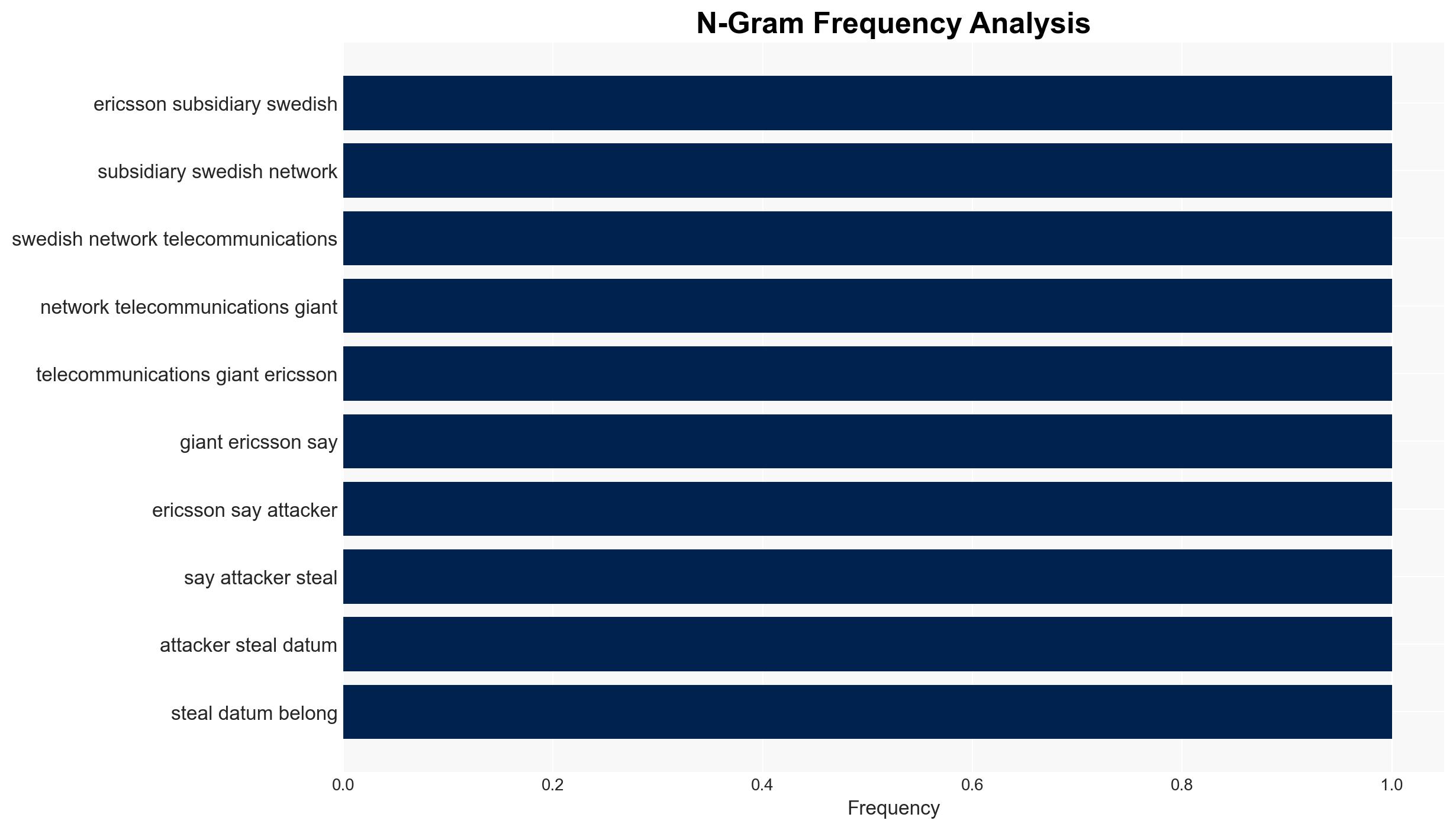
The data breach affecting Ericsson US, via a third-party service provider, exposed sensitive information of 15,661 individuals, including employees and customers. The breach’s origin remains unclear, with no group claiming responsibility. The most likely hypothesis is a financially motivated cybercriminal group. Overall confidence in this assessment is moderate due to limited information on the attackers’ identity and motives.
2. Competing Hypotheses
- Hypothesis A: The breach was conducted by a financially motivated cybercriminal group. Supporting evidence includes the nature of the data stolen (financial and personal identifiers), which is typically targeted for financial gain. Contradicting evidence is the lack of a public ransom demand or claim of responsibility.
- Hypothesis B: The breach was an opportunistic attack by an unsophisticated actor or insider threat. Supporting evidence includes the absence of a claim of responsibility and potential lack of sophisticated tactics. Contradicting evidence is the scale and type of data accessed, suggesting a more targeted approach.
- Assessment: Hypothesis A is currently better supported due to the type of data accessed, which aligns with typical financially motivated cybercrime. Indicators that could shift this judgment include the emergence of a claim of responsibility or evidence of insider involvement.
3. Key Assumptions and Red Flags
- Assumptions: The breach was financially motivated; the service provider’s security measures were insufficient; the attackers have not yet used the data maliciously.
- Information Gaps: Identity and motives of the attackers; specific vulnerabilities exploited; whether any ransom was paid.
- Bias & Deception Risks: Potential underreporting by Ericsson or the service provider to minimize reputational damage; lack of independent verification of the breach details.
4. Implications and Strategic Risks
This breach could have significant implications for Ericsson’s reputation and operational security, with potential ripple effects across the telecommunications sector.
- Political / Geopolitical: Potential regulatory scrutiny and increased pressure on data protection policies.
- Security / Counter-Terrorism: Increased risk of further cyberattacks targeting telecommunications infrastructure.
- Cyber / Information Space: Potential for data misuse in identity theft or fraud, impacting affected individuals and organizations.
- Economic / Social: Financial liabilities for Ericsson and the service provider, alongside potential loss of customer trust.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of affected systems, engage with cybersecurity experts for deeper analysis, and communicate transparently with stakeholders.
- Medium-Term Posture (1–12 months): Strengthen partnerships with cybersecurity firms, invest in advanced threat detection capabilities, and review third-party vendor security protocols.
- Scenario Outlook:
- Best: No further data misuse, and enhanced security measures prevent future breaches.
- Worst: Data is exploited for large-scale fraud, leading to significant financial and reputational damage.
- Most-Likely: Some instances of data misuse occur, but are contained through proactive measures.
6. Key Individuals and Entities
- Ericsson Inc.
- Third-party service provider (unnamed)
- FBI (notified of the breach)
- External cybersecurity experts (unnamed)
7. Thematic Tags
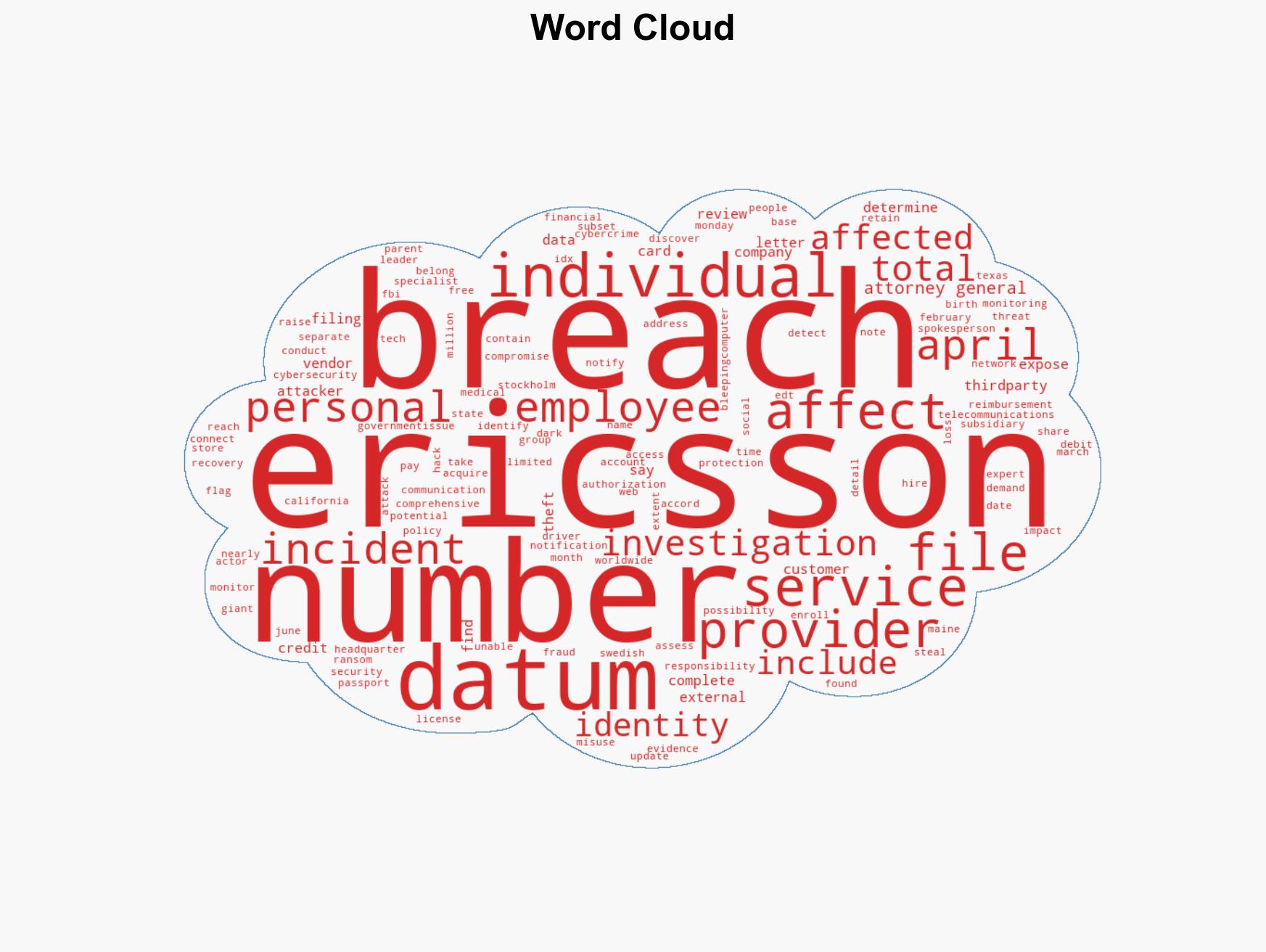
cybersecurity, data breach, cybercrime, telecommunications security, identity theft, third-party risk, regulatory compliance
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us