Escalating Middle East Tensions Ignite Unprecedented Global Cyber Warfare Activities
Published on: 2026-03-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Hybrid Middle East Conflict Triggers Surge in Global Cyber Activity
1. BLUF (Bottom Line Up Front)
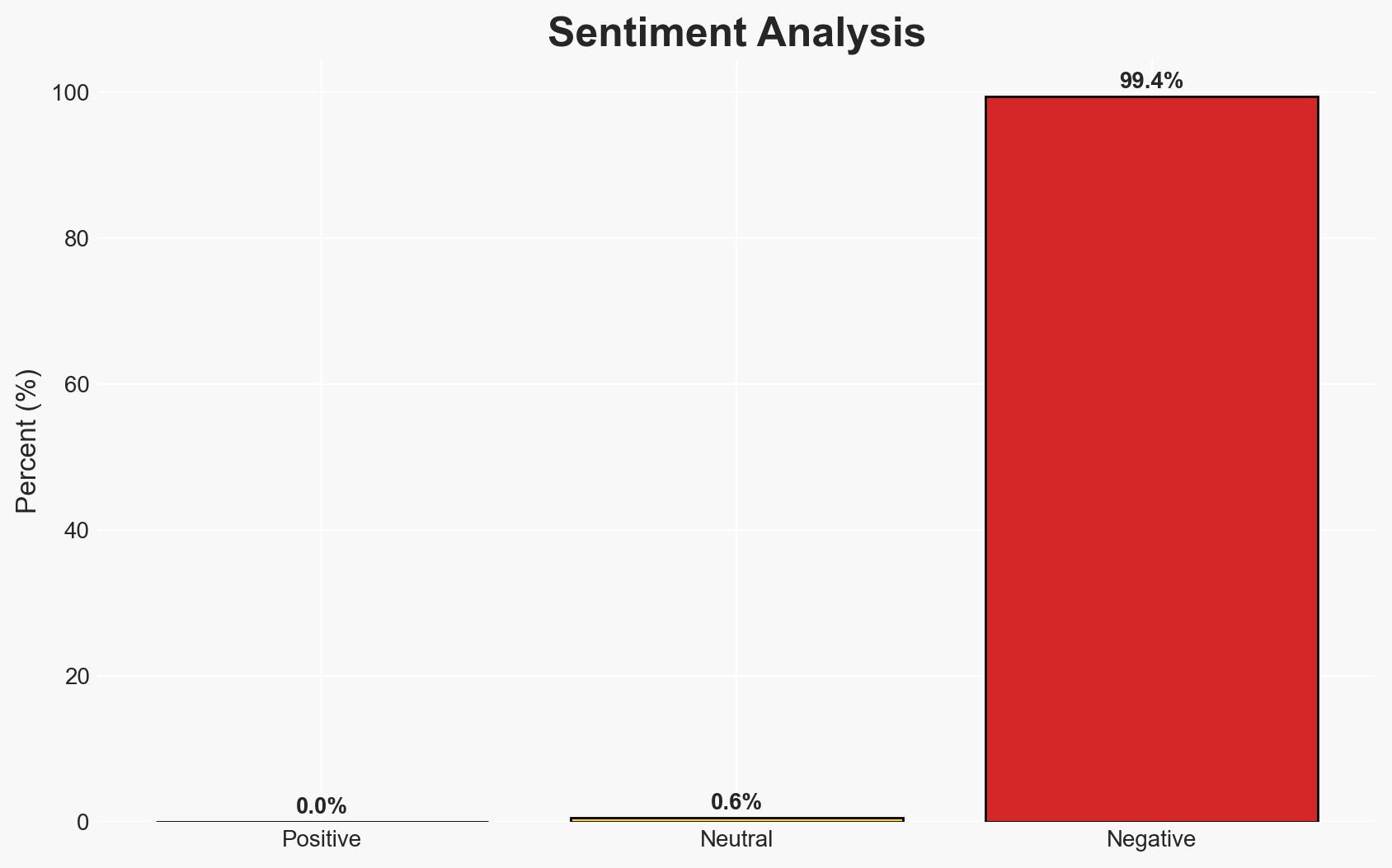
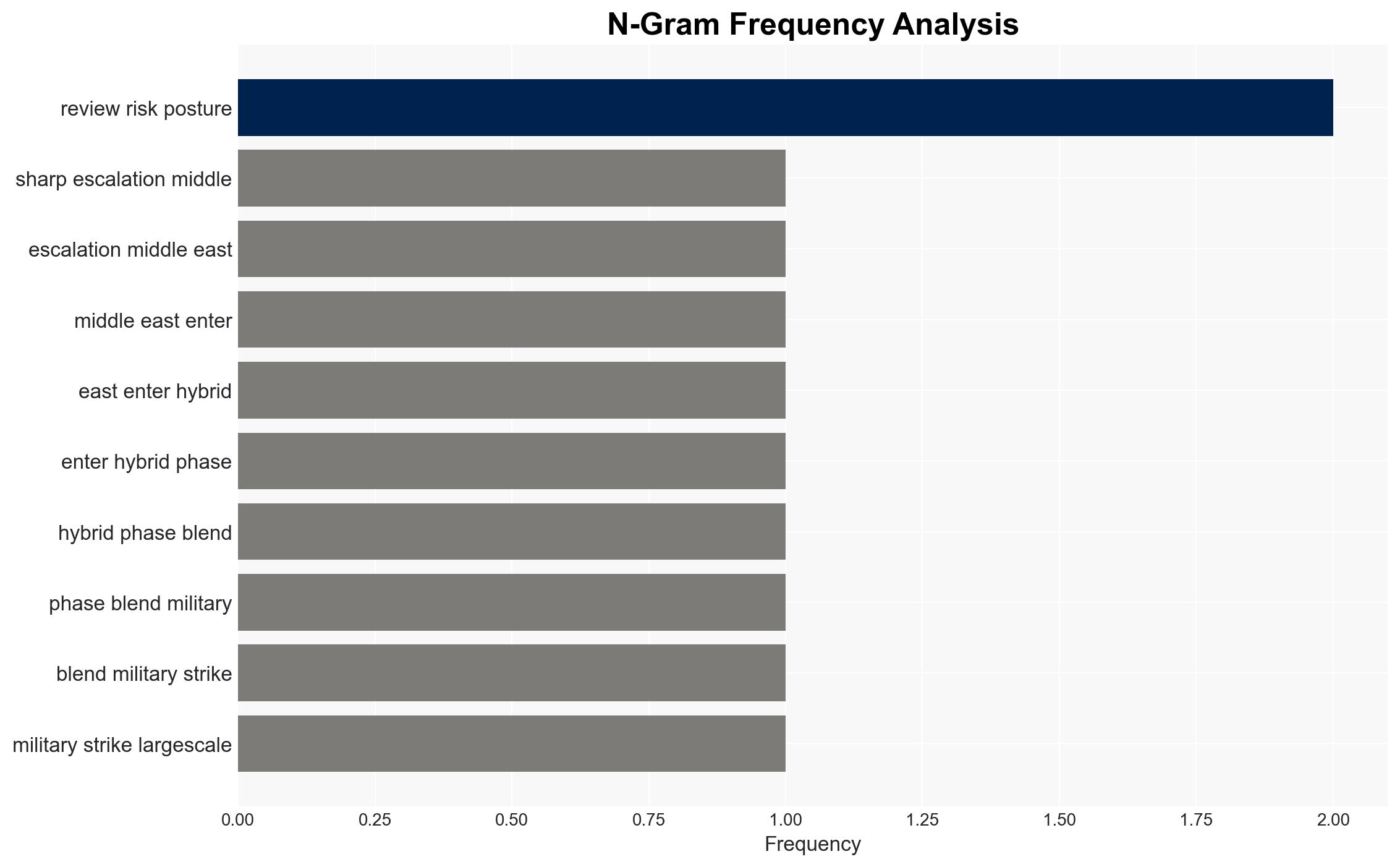
The recent escalation in the Middle East, characterized by joint Israeli-US military and cyber operations against Iran, has heightened global cyber risks. Iran is expected to retaliate through cyber means, potentially impacting international sectors. The situation presents moderate confidence in the likelihood of increased cyber threats and retaliatory actions affecting global cyber infrastructure.
2. Competing Hypotheses
- Hypothesis A: Iran will respond with significant cyber operations targeting US and Israeli interests, leveraging its historical patterns of cyber retaliation. This is supported by past Iranian cyber activities and current increased cyber activity in the Middle East. Key uncertainties include the scale and specific targets of potential attacks.
- Hypothesis B: Iran’s cyber response will be limited, focusing on regional adversaries rather than global targets, due to potential deterrence by US-Israeli capabilities. This is supported by the lack of significant change in the threat level to the UK and other regions. Contradicting evidence includes the historical scope of Iranian cyber operations.
- Assessment: Hypothesis A is currently better supported due to the established pattern of Iranian cyber retaliation and the immediate increase in cyber activity. Indicators that could shift this judgment include a lack of significant cyber incidents in the coming weeks or diplomatic de-escalation efforts.
3. Key Assumptions and Red Flags
- Assumptions: Iran retains the capability and intent to conduct significant cyber operations; US-Israeli actions are perceived as a major provocation by Iran; cyber retaliation is a preferred method for Iran due to asymmetrical advantages.
- Information Gaps: Specific details on the extent of damage to Iran’s digital infrastructure; confirmation of Iran’s cyber operational readiness and specific targets.
- Bias & Deception Risks: Potential overestimation of Iran’s cyber capabilities; reliance on open-source reports which may be subject to misinformation or propaganda.
4. Implications and Strategic Risks
The hybrid conflict in the Middle East could escalate, affecting global cyber stability and international relations. The interplay between military and cyber operations may set precedents for future conflicts.
- Political / Geopolitical: Potential for increased tensions between Iran and Western allies; risk of broader regional instability.
- Security / Counter-Terrorism: Elevated threat levels for US and Israeli assets; potential for increased terrorist activities as a form of retaliation.
- Cyber / Information Space: Increased global cyber threat landscape; potential for widespread cyber disruptions and espionage activities.
- Economic / Social: Disruptions in critical sectors like energy and aviation; potential economic impacts due to cyber disruptions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber activities linked to Iran; strengthen cyber defenses for critical infrastructure; engage in diplomatic efforts to de-escalate tensions.
- Medium-Term Posture (1–12 months): Develop resilience measures against cyber threats; foster international partnerships for cyber threat intelligence sharing; invest in cybersecurity capabilities.
- Scenario Outlook:
- Best: Diplomatic resolution reduces tensions, leading to decreased cyber threats.
- Worst: Escalation leads to widespread cyber attacks impacting global infrastructure.
- Most-Likely: Continued low to moderate level cyber skirmishes targeting regional and global interests.
6. Key Individuals and Entities
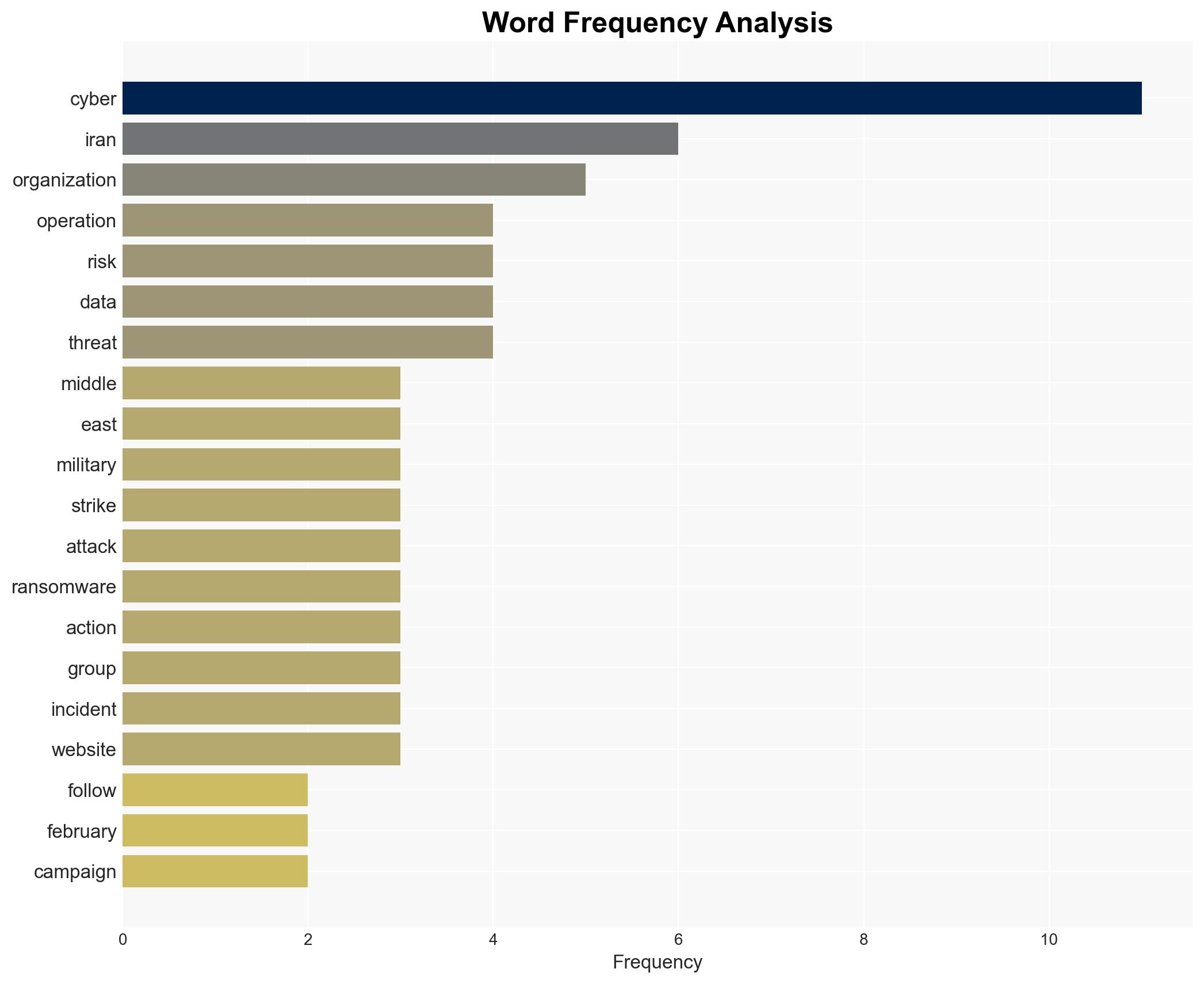
- Cynthia Kaiser, SVP at Halcyon, former FBI cyber executive
- CloudSek (cybersecurity firm)
- Hacktivist group Handala
- Ransomware group Sicarii
- Distributed denial-of-service (DDoS) botnet HydraC2
- UK’s National Cyber Security Centre (NCSC)
7. Thematic Tags
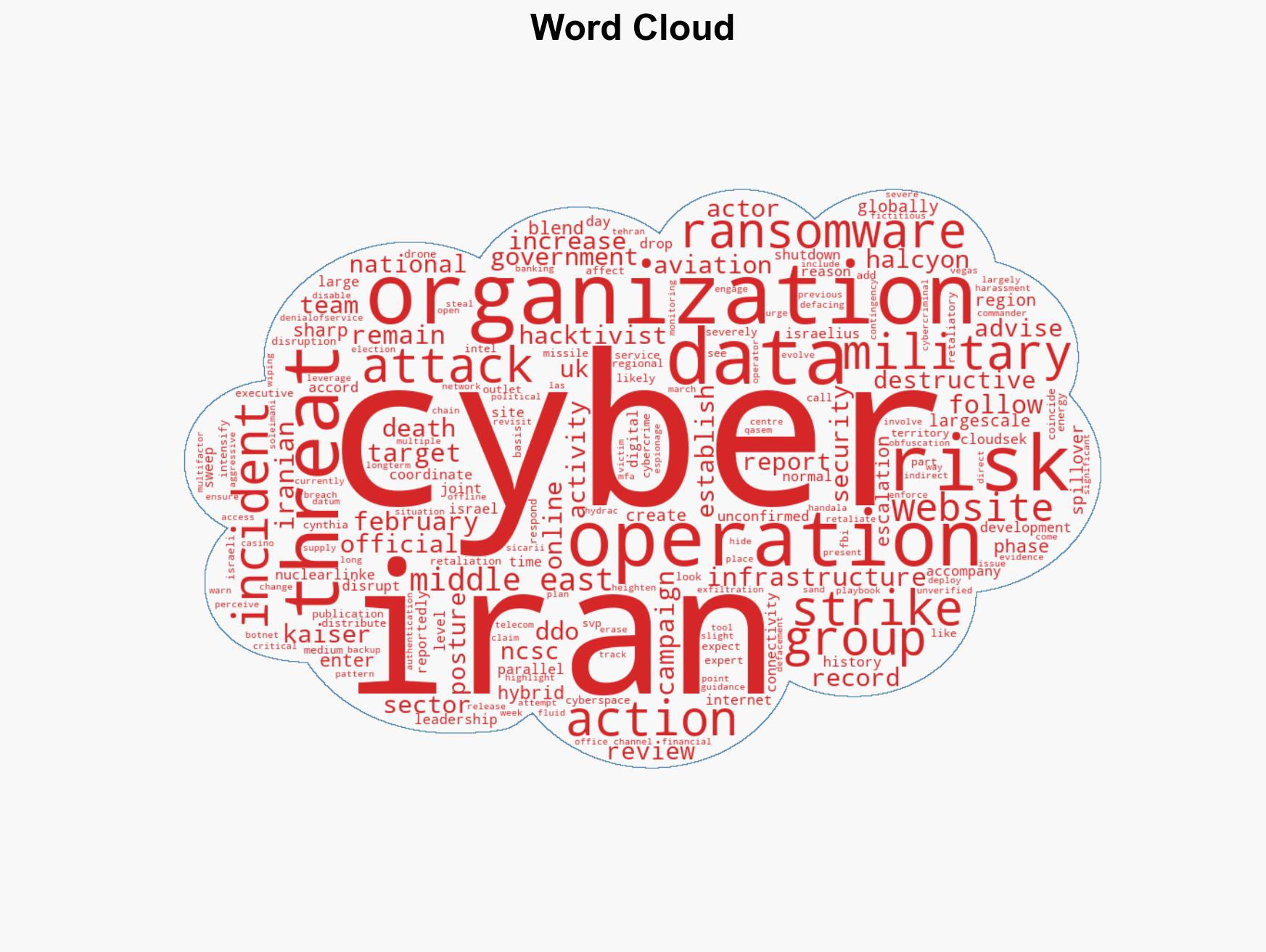
cybersecurity, cyber warfare, Middle East conflict, Iran-Israel tensions, cyber retaliation, global cybersecurity, hybrid warfare, geopolitical risks
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us