Essential Steps to Take Immediately After a Cyber Hack
Published on: 2026-03-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: The 5 Things You Should Do First If You Get Hacked
1. BLUF (Bottom Line Up Front)
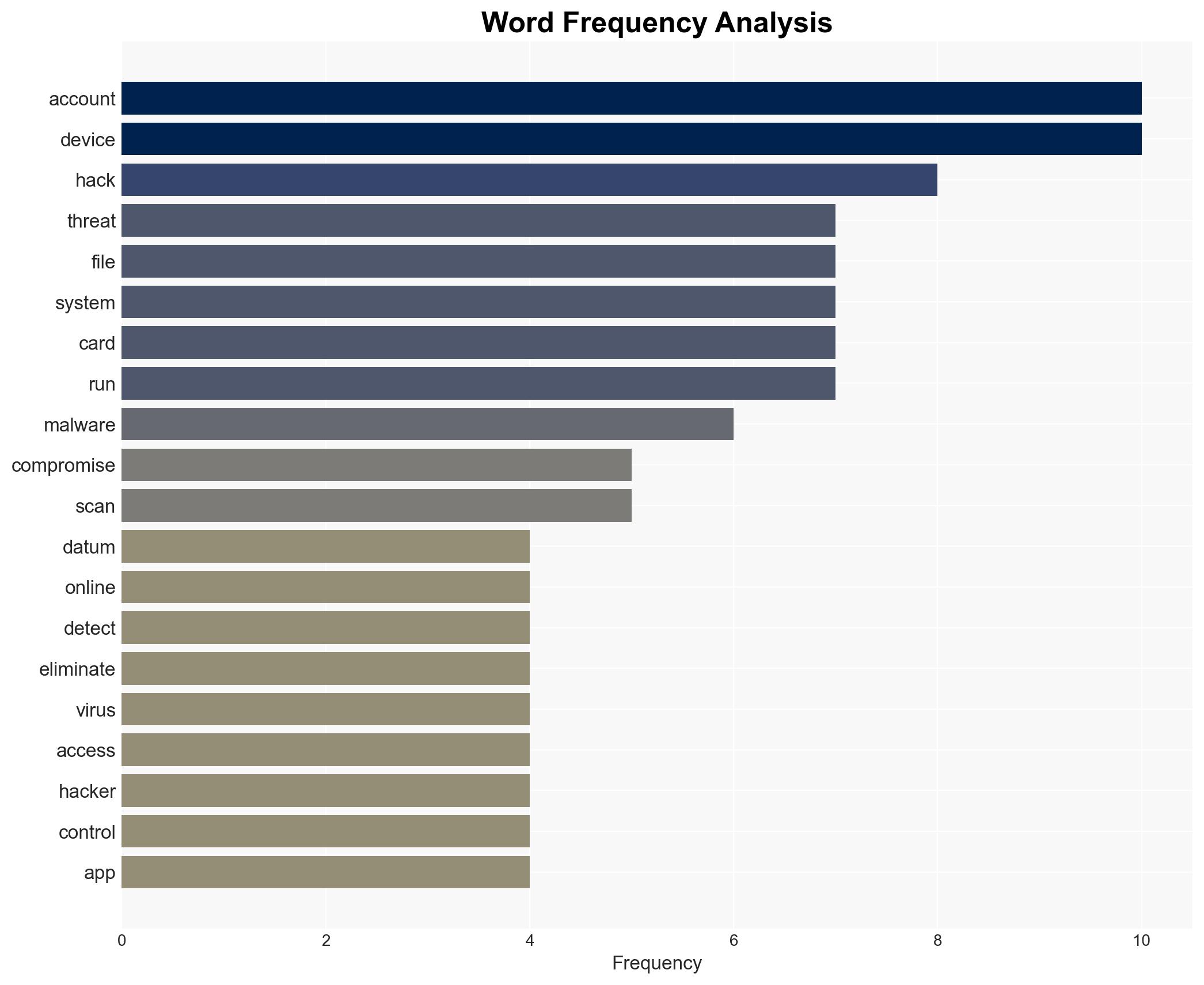
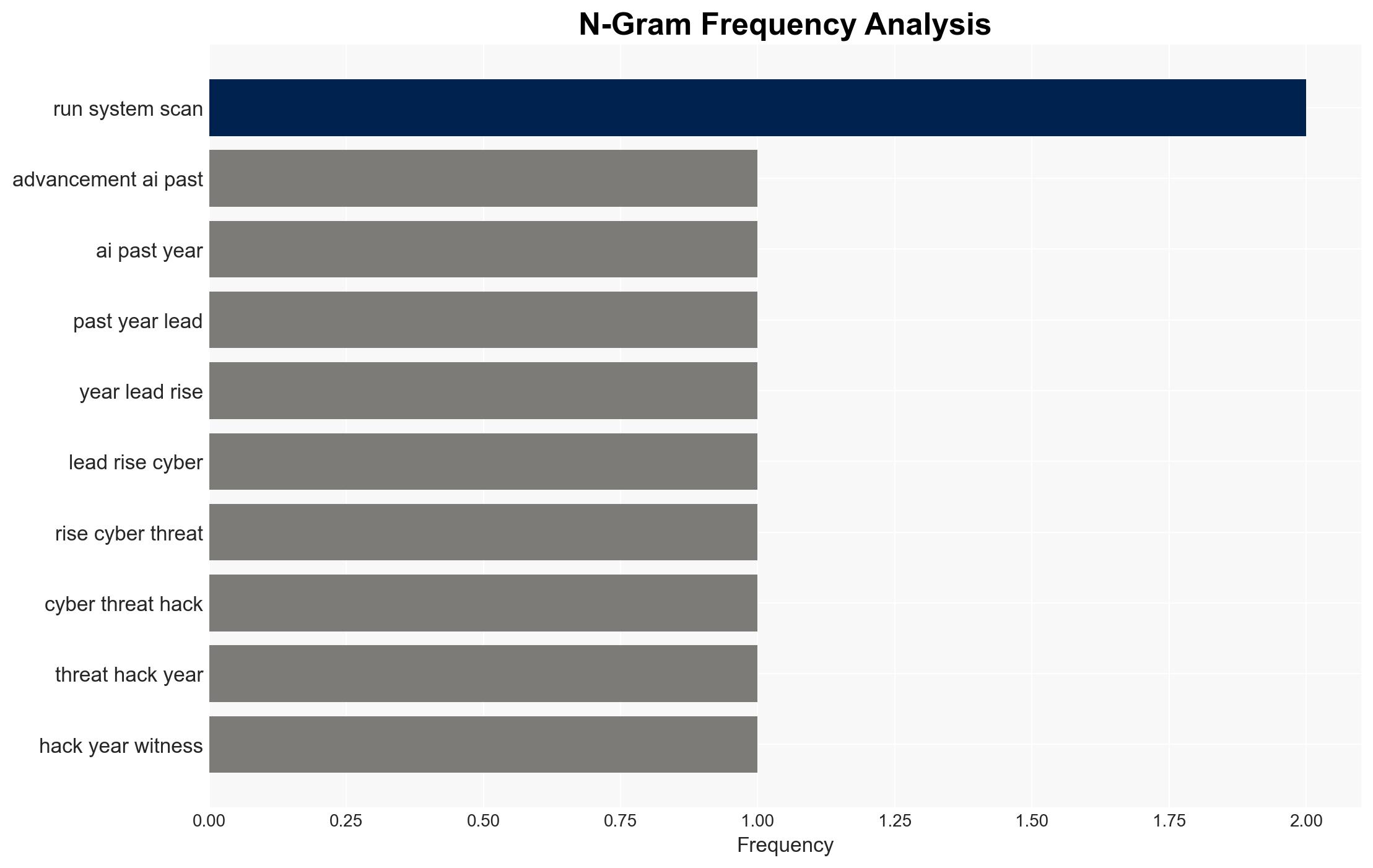
The increasing sophistication of AI has contributed to a surge in cyber threats, with a significant number of attacks targeting both organizations and individuals. The initial response to a cyber breach is critical in mitigating damage. The most likely hypothesis is that cybercriminals are exploiting AI advancements to enhance attack capabilities, affecting a broad range of users. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: Cybercriminals are primarily targeting large organizations and tech giants using AI-enhanced methods. This is supported by the prevalence of massive breaches and the sale of credentials on the dark web. However, the snippet indicates that not all attacks are massive, suggesting a broader target range.
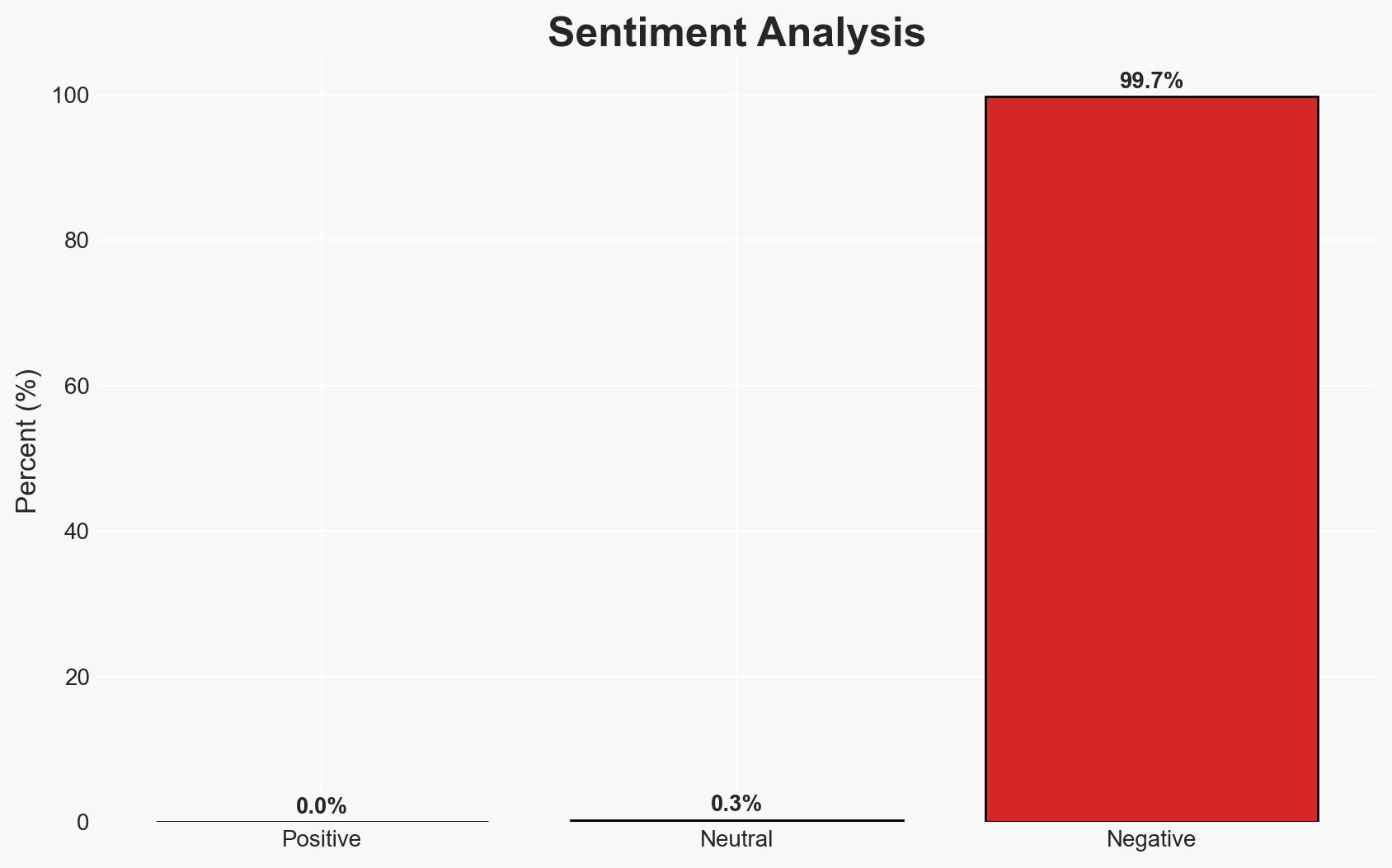
- Hypothesis B: Cybercriminals are increasingly targeting everyday users, exploiting AI to craft more convincing phishing attacks and malware. This is supported by the mention of unsuspecting users being preyed upon and the critical need for immediate action post-breach.
- Assessment: Hypothesis B is currently better supported due to the emphasis on individual users and the detailed guidance on immediate actions to mitigate personal device breaches. Indicators such as increased reports of individual-targeted phishing could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Cybercriminals have access to advanced AI tools; individuals are less prepared to handle cyber threats; financial institutions have mechanisms to reverse unauthorized transactions.
- Information Gaps: Specific data on the proportion of attacks targeting individuals versus organizations; effectiveness of current detection tools for AI-enhanced threats.
- Bias & Deception Risks: Potential bias in focusing on individual-level threats due to lack of comprehensive data on organizational breaches; deception risk from cybercriminals using misinformation to cover tracks.
4. Implications and Strategic Risks
The evolution of AI-driven cyber threats could lead to increased vulnerabilities across both individual and organizational levels, potentially overwhelming current cybersecurity measures.
- Political / Geopolitical: Escalation in cyber warfare tactics could strain international relations and lead to calls for stricter global cybersecurity regulations.
- Security / Counter-Terrorism: Enhanced cyber capabilities may be leveraged by terrorist organizations to disrupt critical infrastructure.
- Cyber / Information Space: Increased sophistication in cyberattacks could lead to more pervasive misinformation campaigns and data breaches.
- Economic / Social: Financial losses from cyberattacks could destabilize economies, while social trust in digital systems may erode.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of AI-driven cyber threats, increase public awareness campaigns on phishing and malware risks, and improve rapid response protocols.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies to improve AI threat detection, invest in cybersecurity training for individuals, and strengthen international cooperation on cybercrime.
- Scenario Outlook:
- Best: Effective countermeasures reduce cyberattack success rates; AI tools aid in threat detection.
- Worst: Cybercriminals outpace defensive measures, leading to widespread breaches and economic damage.
- Most-Likely: Continued rise in AI-driven attacks with gradual improvements in defense capabilities.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
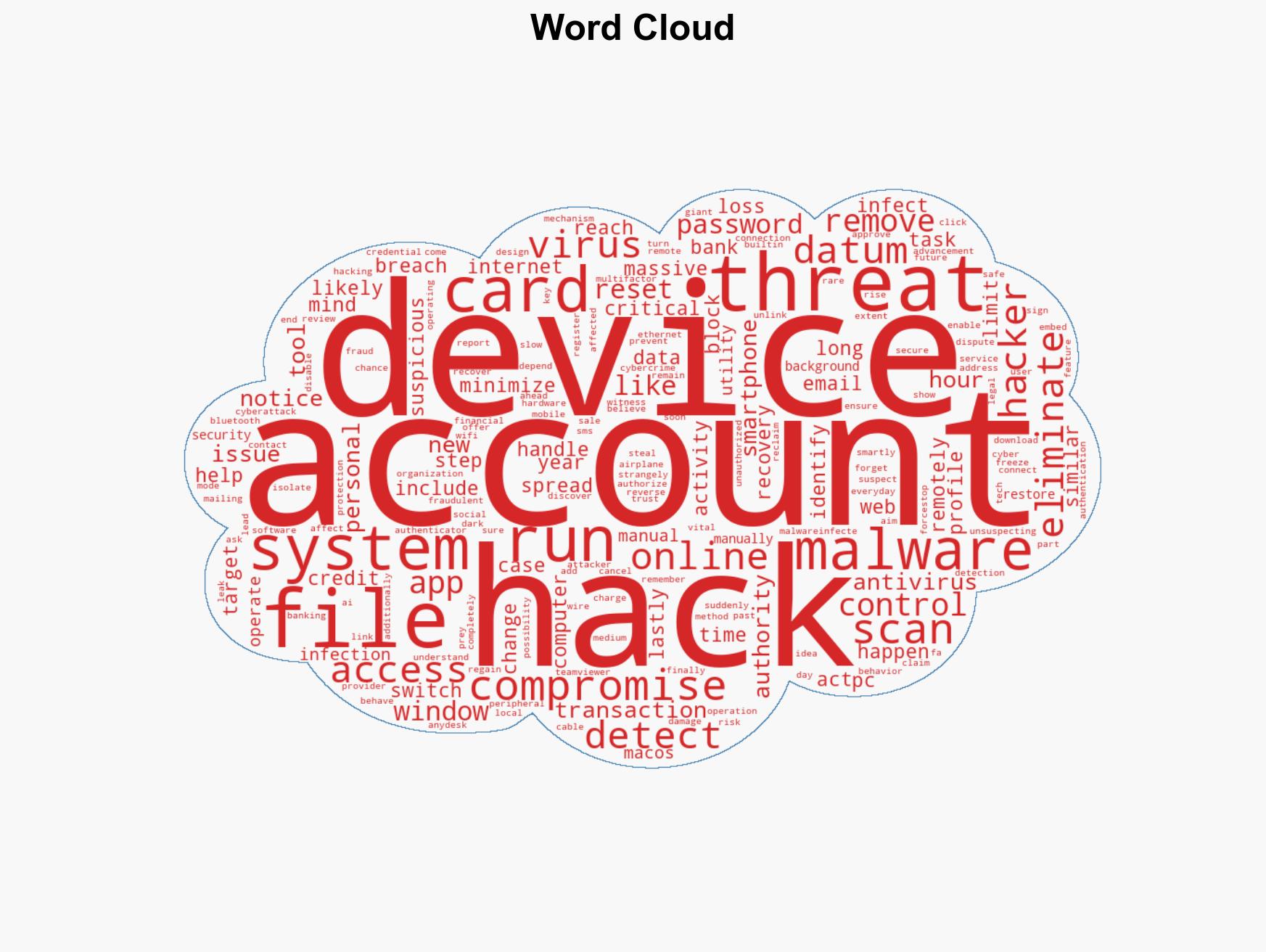
cybersecurity, AI advancements, phishing attacks, malware, individual users, financial institutions, cybercrime
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us