EU Imposes Sanctions on Chinese and Iranian Entities for Cyber Threats to Critical Infrastructure
Published on: 2026-03-17
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Europe sanctions Chinese and Iranian firms for cyberattacks
1. BLUF (Bottom Line Up Front)
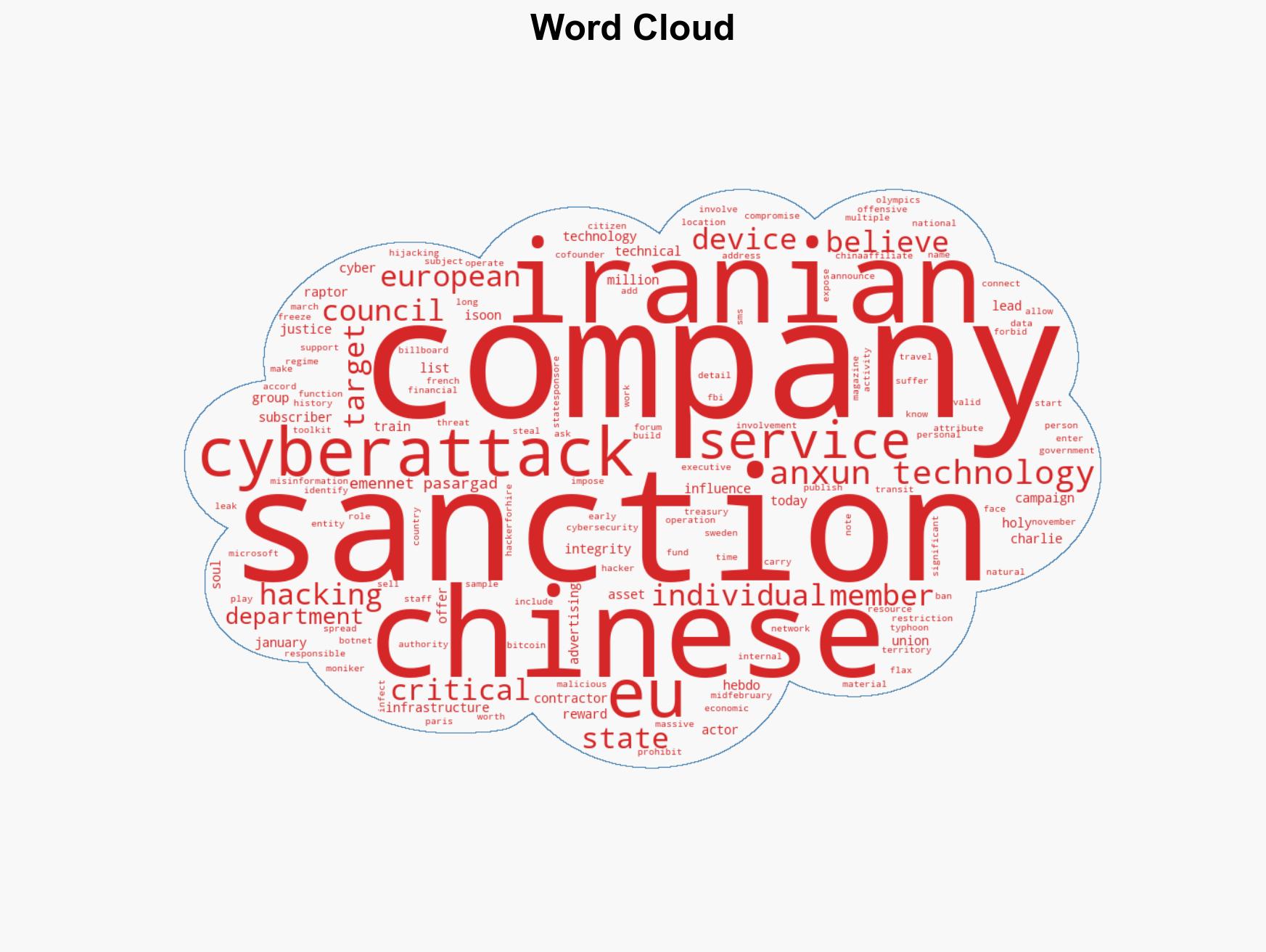
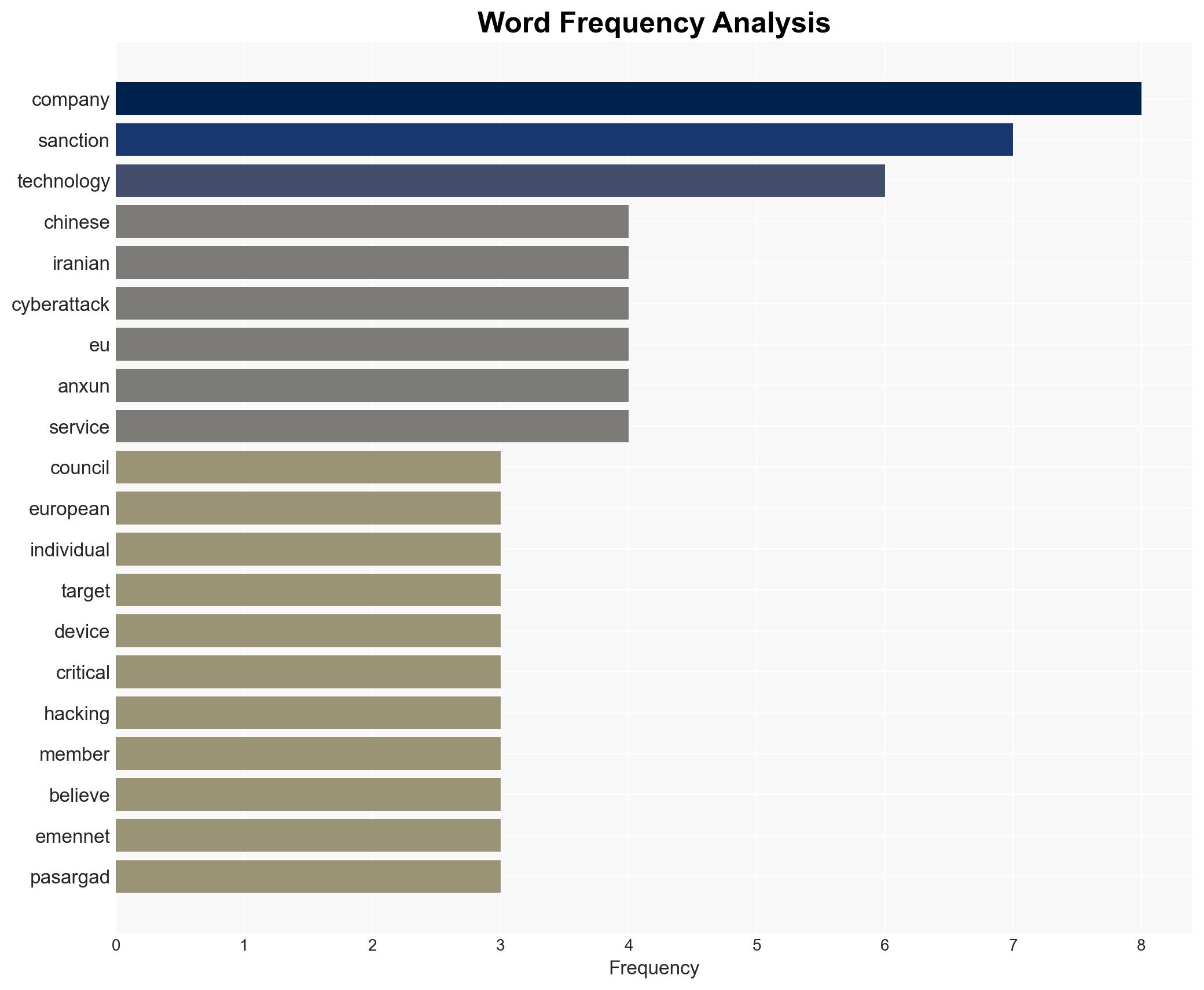
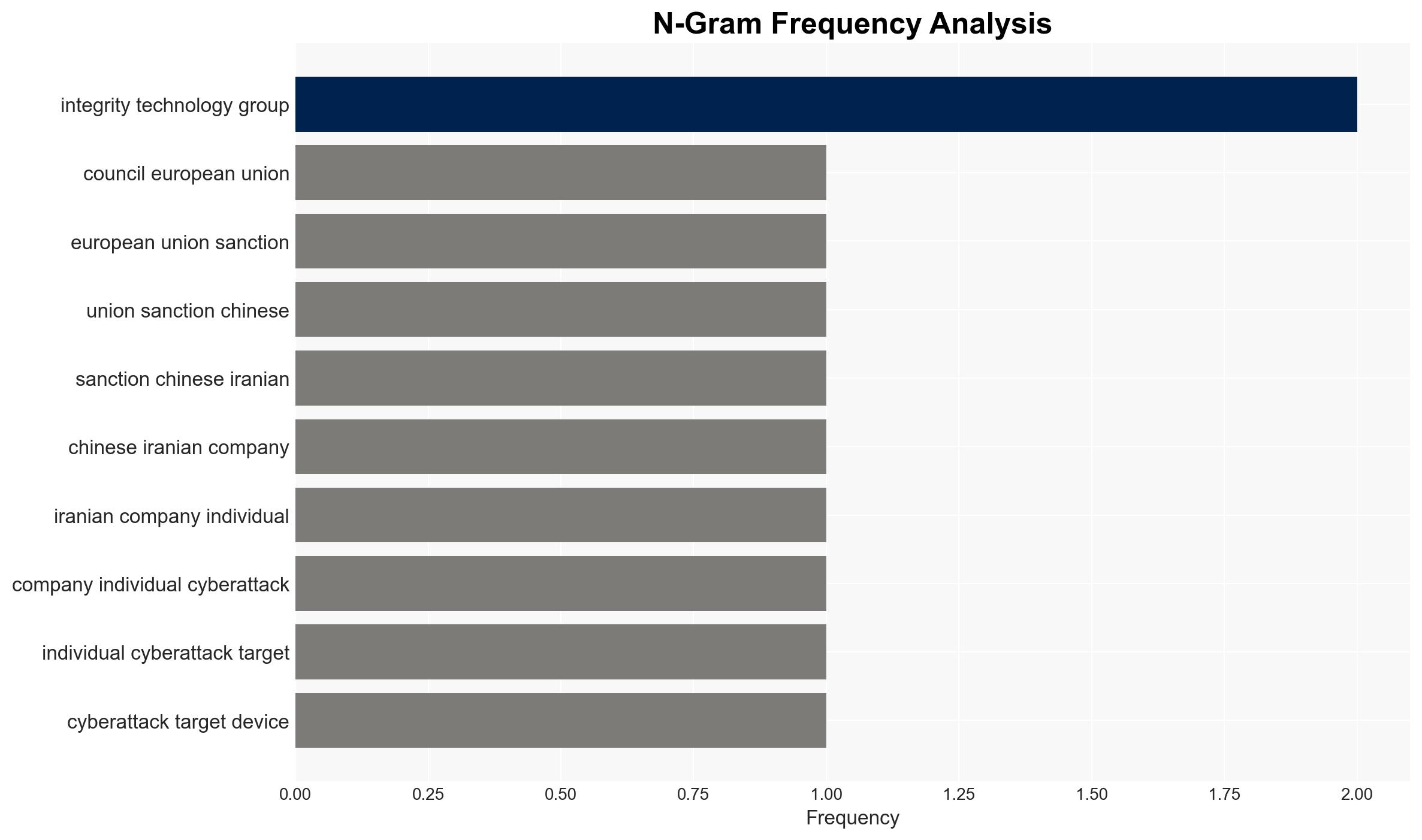
The European Union has imposed sanctions on Chinese and Iranian entities for cyberattacks against critical infrastructure and influence operations. The sanctions target three companies and two individuals linked to significant cyber threats. This action reflects heightened EU vigilance against state-affiliated cyber aggression, with moderate confidence in the attribution of these activities to state-sponsored actors.
2. Competing Hypotheses
- Hypothesis A: The sanctioned entities are state-sponsored actors conducting cyber operations on behalf of their respective governments. This is supported by the entities’ history of cyber activities and connections to government-affiliated operations, as well as previous sanctions by the U.S. However, direct evidence linking state directives to specific attacks remains limited.
- Hypothesis B: The entities operate independently or as private contractors without direct state sponsorship, motivated by financial gain or other non-state objectives. While this could explain the commercial nature of some activities, the consistency with state objectives and historical patterns of behavior suggests otherwise.
- Assessment: Hypothesis A is currently better supported due to the alignment of the entities’ actions with state interests and previous attributions by credible sources. Indicators such as further leaks or disclosures could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The sanctioned entities have ongoing operational capabilities; state sponsorship is inferred from past behavior; EU sanctions will impact the entities’ operations.
- Information Gaps: Direct evidence of state directives; comprehensive understanding of the entities’ full operational scope and partnerships.
- Bias & Deception Risks: Potential bias in attributing state sponsorship without direct evidence; risk of misinformation from adversarial sources aiming to obfuscate true affiliations.
4. Implications and Strategic Risks
This development could lead to increased geopolitical tensions and a recalibration of cyber defense strategies within the EU. The sanctions may deter similar future activities or provoke retaliatory cyber actions.
- Political / Geopolitical: Potential escalation in EU-China/Iran relations; increased diplomatic efforts to address cyber threats.
- Security / Counter-Terrorism: Heightened alert for retaliatory cyberattacks; potential shifts in threat actor tactics.
- Cyber / Information Space: Increased focus on securing critical infrastructure; potential for enhanced cyber collaboration among EU states.
- Economic / Social: Possible impacts on trade relations; public perception of cybersecurity threats may influence policy and investment.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of sanctioned entities; strengthen cyber defenses of critical infrastructure; engage in diplomatic dialogue to mitigate escalation.
- Medium-Term Posture (1–12 months): Develop resilience measures; foster international partnerships for cyber threat intelligence sharing; invest in cybersecurity capabilities.
- Scenario Outlook: Best: De-escalation and improved cyber cooperation. Worst: Escalation leading to broader cyber conflict. Most-Likely: Continued low-level cyber skirmishes with diplomatic engagement.
6. Key Individuals and Entities
- Integrity Technology Group
- Anxun Information Technology (i-Soon)
- Emennet Pasargad
- Co-founders of Anxun Information Technology
- Holy Souls (pseudonym)
7. Thematic Tags
cybersecurity, sanctions, cyberattacks, state-sponsored actors, EU security, critical infrastructure, cyber defense, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us