European Commission Reports Data Compromise in Cloud Infrastructure Following Cyber-Attack
Published on: 2026-03-30
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: European Commission Confirms Cloud Data Breach
1. BLUF (Bottom Line Up Front)
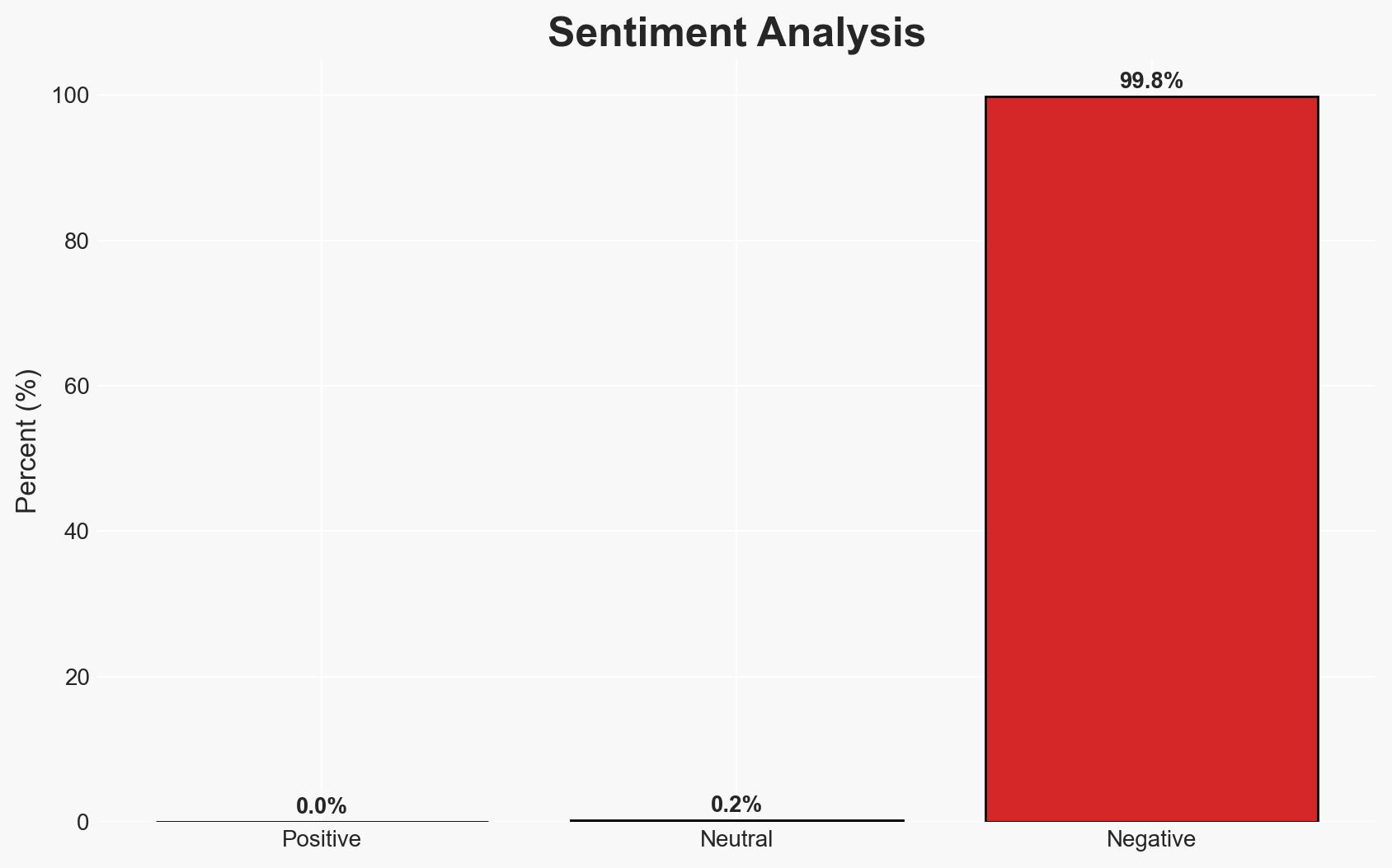
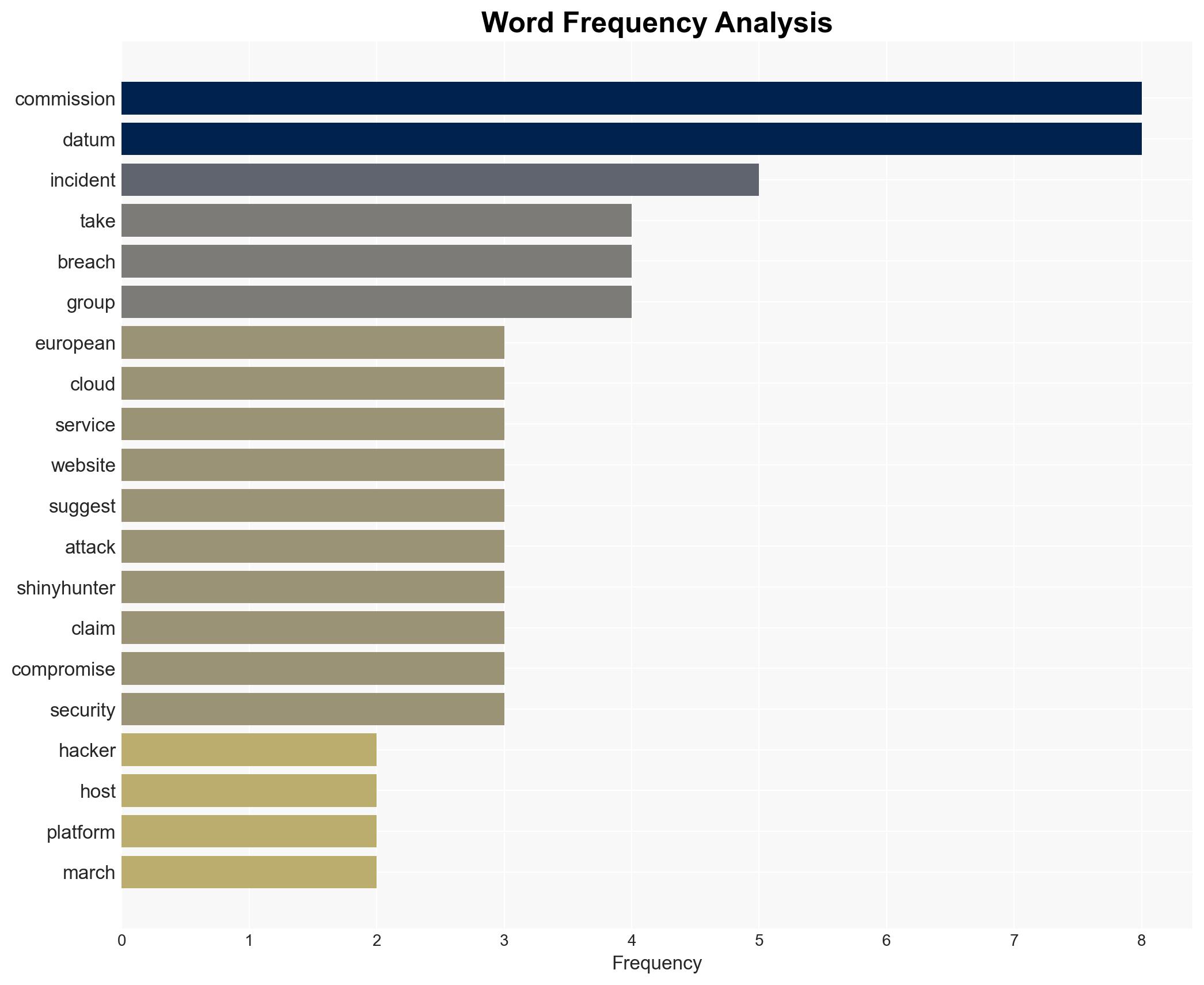
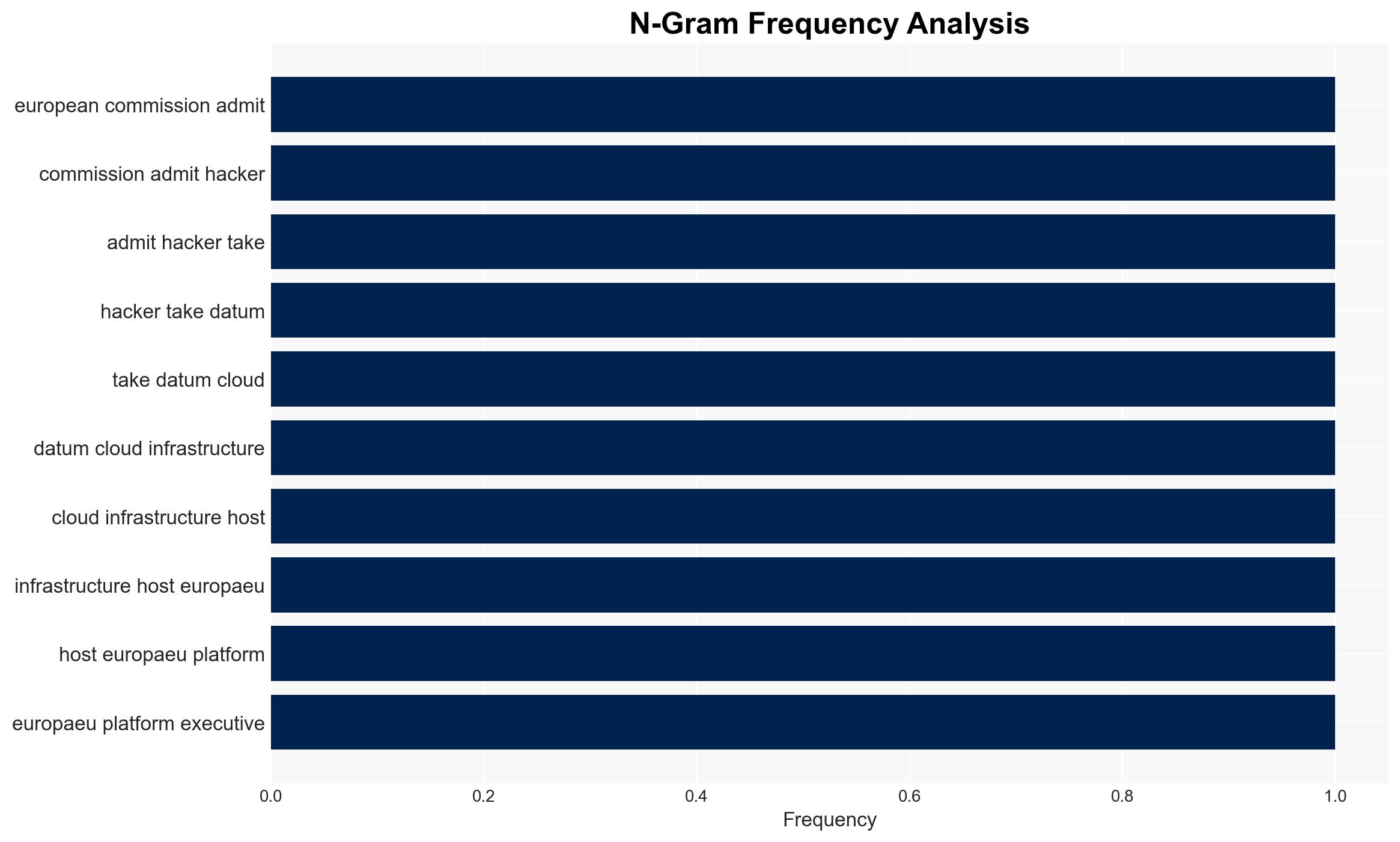
The European Commission has confirmed a data breach involving its cloud infrastructure, potentially exposing sensitive data. The breach, attributed to the hacking group ShinyHunters, may impact EU entities and employees. The incident underscores vulnerabilities in cloud security and raises concerns about potential identity risks and operational disruptions. Overall confidence in this assessment is moderate due to incomplete information on the breach’s full scope and impact.
2. Competing Hypotheses
- Hypothesis A: ShinyHunters exploited vulnerabilities in the European Commission’s AWS cloud environment to extract data. Supporting evidence includes claims by ShinyHunters of accessing extensive data and screenshots of compromised information. Contradicting evidence includes AWS’s statement that its services were not compromised, creating uncertainty about the exact breach vector.
- Hypothesis B: The breach resulted from a phishing campaign targeting Commission employees, leveraging social engineering tactics. This is supported by ShinyHunters’ known use of vishing and impersonation techniques. However, there is no direct evidence linking this method to the current breach.
- Assessment: Hypothesis A is currently better supported due to the direct claims and evidence presented by ShinyHunters. However, further investigation into the breach vector and methods could shift this judgment, especially if new evidence of phishing emerges.
3. Key Assumptions and Red Flags
- Assumptions: The breach was limited to cloud-hosted data; ShinyHunters’ claims are partially accurate; AWS infrastructure was not directly compromised.
- Information Gaps: Full scope of data compromised; exact method of breach; potential involvement of other threat actors.
- Bias & Deception Risks: Potential exaggeration or misinformation by ShinyHunters; reliance on unverified social media sources; confirmation bias towards cloud vulnerabilities.
4. Implications and Strategic Risks
The breach could lead to increased scrutiny of EU cybersecurity practices and influence future policy decisions. It may also embolden other threat actors to target EU institutions.
- Political / Geopolitical: Potential diplomatic tensions if sensitive data involves international partners; increased pressure on EU cybersecurity policy.
- Security / Counter-Terrorism: Heightened threat landscape for EU entities; possible exploitation of stolen data for spear-phishing or identity theft.
- Cyber / Information Space: Increased focus on cloud security measures; potential for misinformation campaigns leveraging leaked data.
- Economic / Social: Potential financial impact on affected entities; erosion of trust in EU digital infrastructure.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive forensic analysis; enhance monitoring of affected systems; notify potentially impacted individuals and entities.
- Medium-Term Posture (1–12 months): Strengthen cloud security protocols; develop partnerships with cybersecurity firms; conduct regular security audits and training.
- Scenario Outlook:
- Best: Breach contained with minimal data misuse; improved cybersecurity measures prevent future incidents.
- Worst: Data exploited for extensive phishing campaigns; significant political and economic fallout.
- Most-Likely: Limited data misuse; gradual implementation of enhanced security measures.
6. Key Individuals and Entities
- European Commission
- ShinyHunters
- Amazon Web Services (AWS)
- European Union entities (unspecified)
- Nick Tausek, Swimlane
7. Thematic Tags
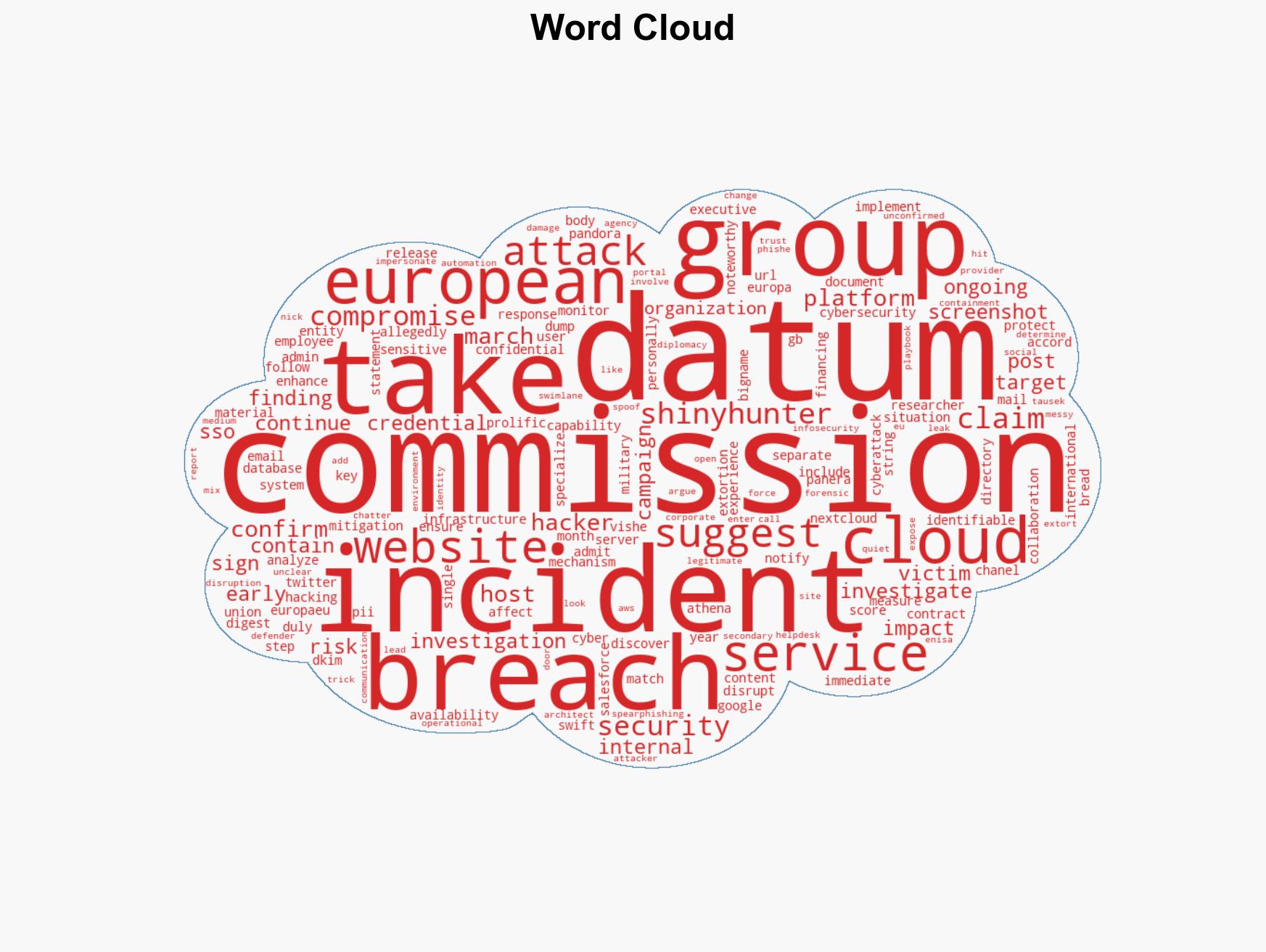
cybersecurity, data breach, cloud infrastructure, European Union, ShinyHunters, phishing, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us