Evolving Cyber Threats Demand Immediate Readiness from Critical Infrastructure Leaders
Published on: 2026-03-31
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: The threat to critical infrastructure has changed Has your readiness
1. BLUF (Bottom Line Up Front)
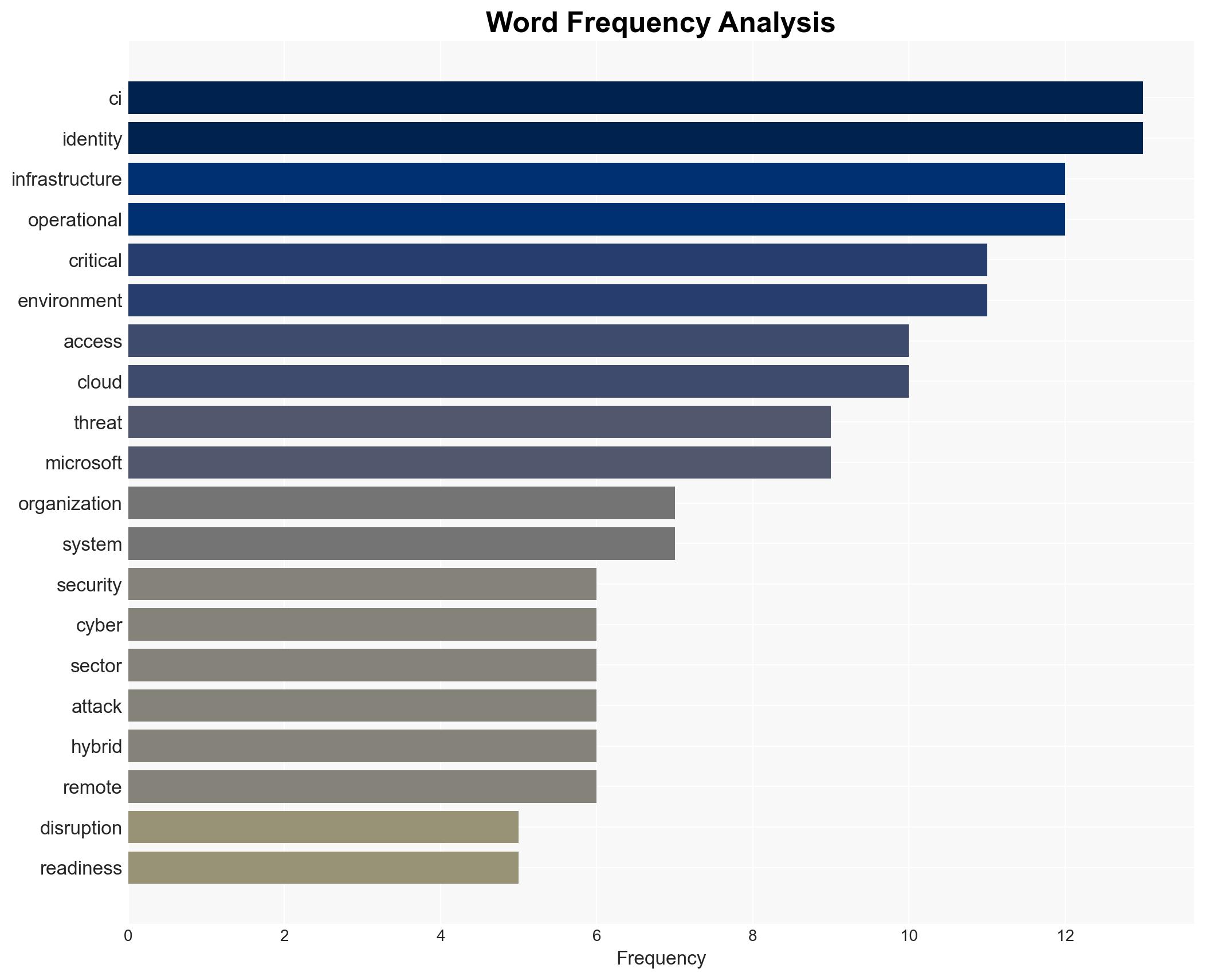
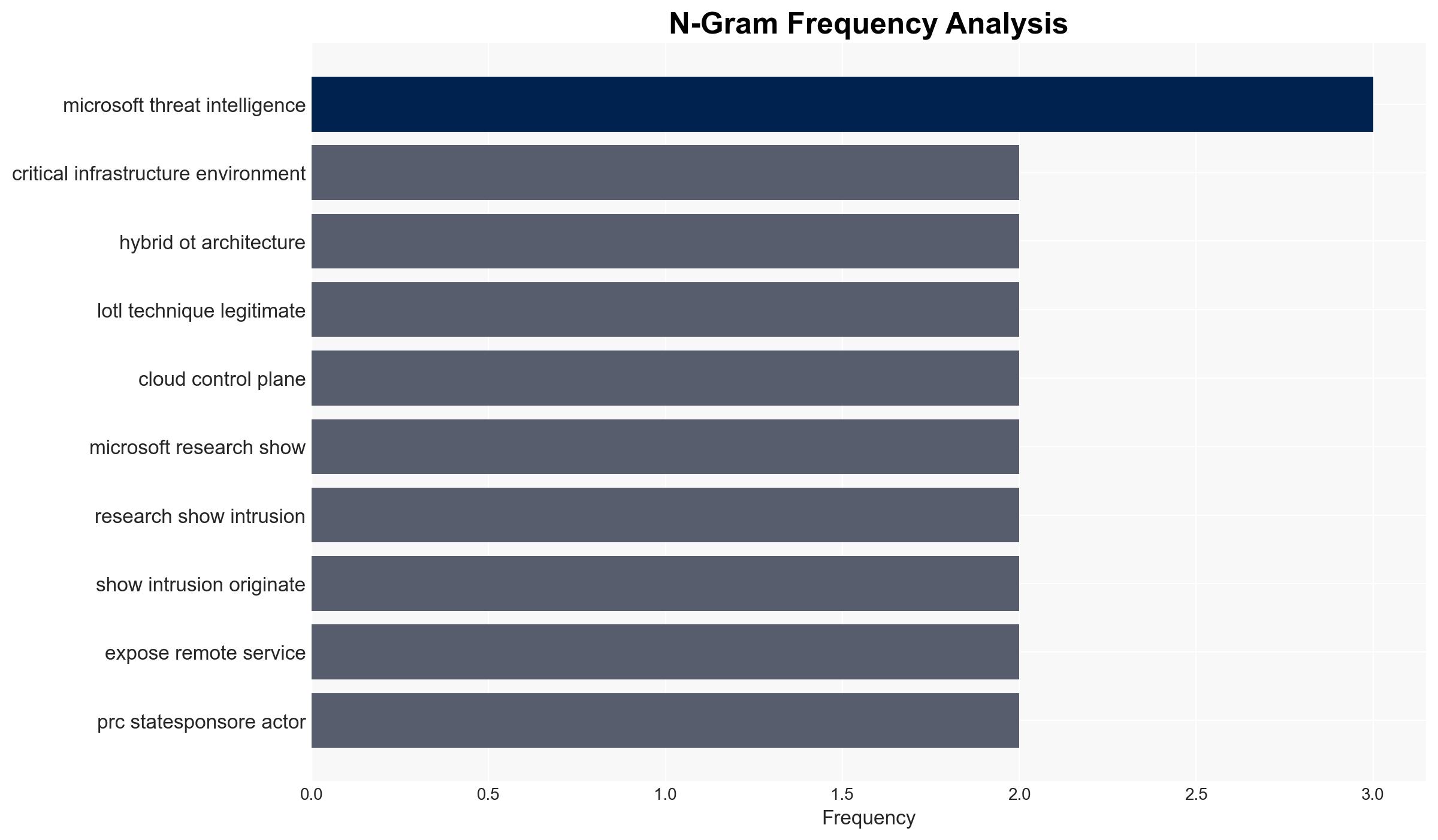
The cyber threat landscape for critical infrastructure (CI) has evolved, with threat actors now establishing persistent access for potential future disruptions. This shift necessitates immediate readiness and proactive defense strategies. The most likely hypothesis is that CI organizations are inadequately prepared for these advanced threats, affecting national security and public safety. Overall confidence in this judgment is moderate.
2. Competing Hypotheses
- Hypothesis A: CI organizations are unprepared for the current threat landscape, which includes persistent access by threat actors. This is supported by the need for new regulations and the implementation gap highlighted by initiatives like Operation Winter SHIELD. Key uncertainties include the extent of unpreparedness and the effectiveness of current mitigation efforts.
- Hypothesis B: CI organizations are adequately adapting to the evolving threat landscape through improved policies and proactive measures. This is contradicted by the ongoing need for regulatory changes and the reported implementation gaps in sectors like water utilities.
- Assessment: Hypothesis A is currently better supported due to consistent reports of implementation gaps and the necessity for regulatory interventions. Indicators such as successful mitigation of recent threats or significant improvements in readiness could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: CI organizations are critical to national security; threat actors are capable of establishing persistent access; regulatory changes will drive improvements in readiness.
- Information Gaps: Specific data on the current state of CI organizations’ cybersecurity readiness and the effectiveness of new regulations.
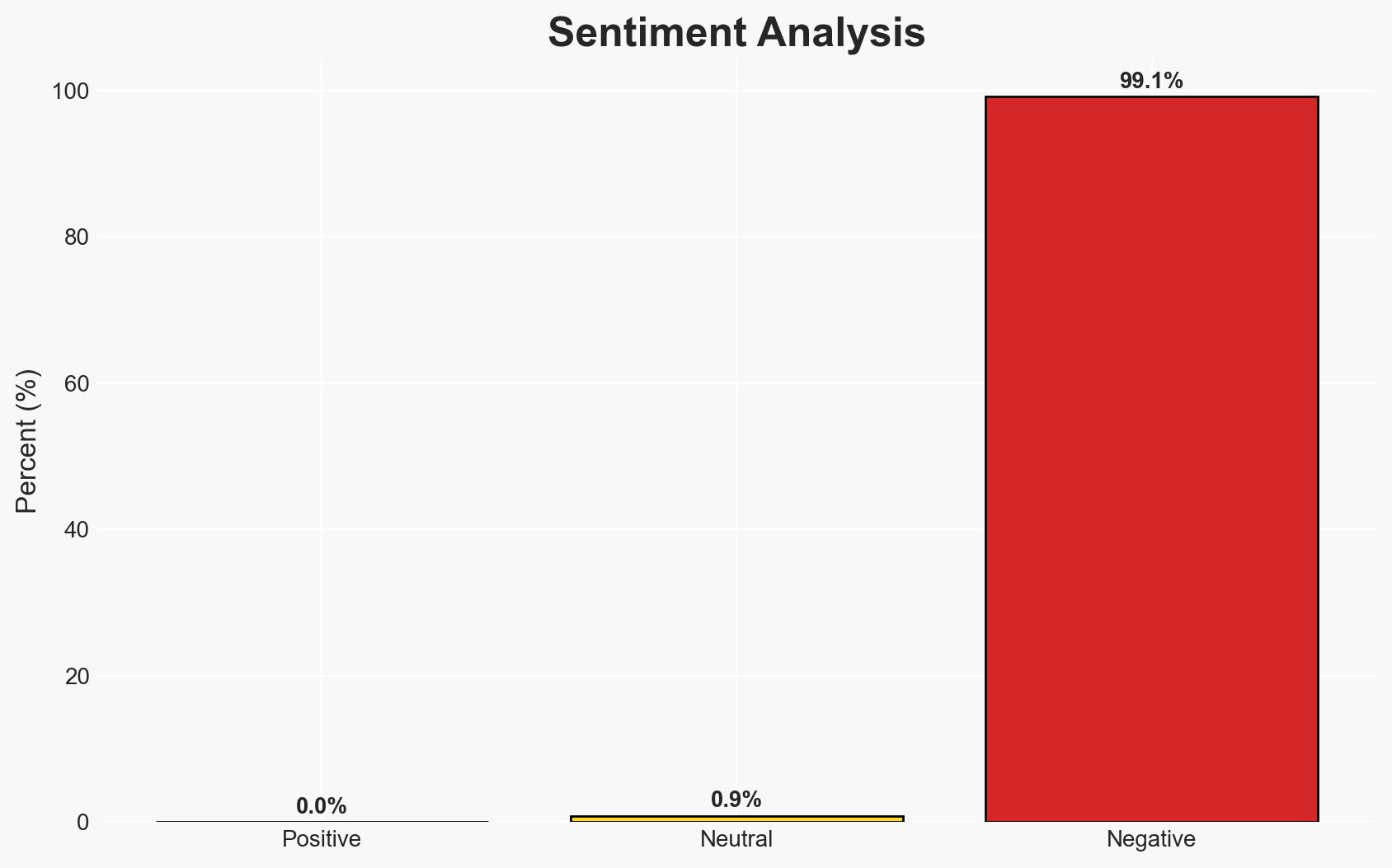
- Bias & Deception Risks: Potential bias in threat intelligence sources; risk of threat actors using misinformation to obscure their activities.
4. Implications and Strategic Risks
The evolution of cyber threats to CI could lead to significant disruptions if not adequately addressed. The interaction with broader dynamics includes regulatory changes and increased international cooperation.
- Political / Geopolitical: Increased international collaboration on cybersecurity policies could emerge, potentially leading to geopolitical tensions with states perceived as harboring threat actors.
- Security / Counter-Terrorism: Enhanced threat environment requiring more robust counter-terrorism strategies to protect CI sectors.
- Cyber / Information Space: Increased focus on identity-driven intrusions and the need for advanced cyber defense capabilities.
- Economic / Social: Potential economic impacts from service disruptions and loss of public trust in CI sectors.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct comprehensive cybersecurity audits of CI organizations; enhance monitoring and threat detection capabilities.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for continuous training; implement regulatory compliance measures.
- Scenario Outlook: Best: CI organizations achieve high readiness, minimizing disruptions. Worst: Persistent threats lead to significant service disruptions. Most-Likely: Gradual improvement in readiness with occasional disruptions.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
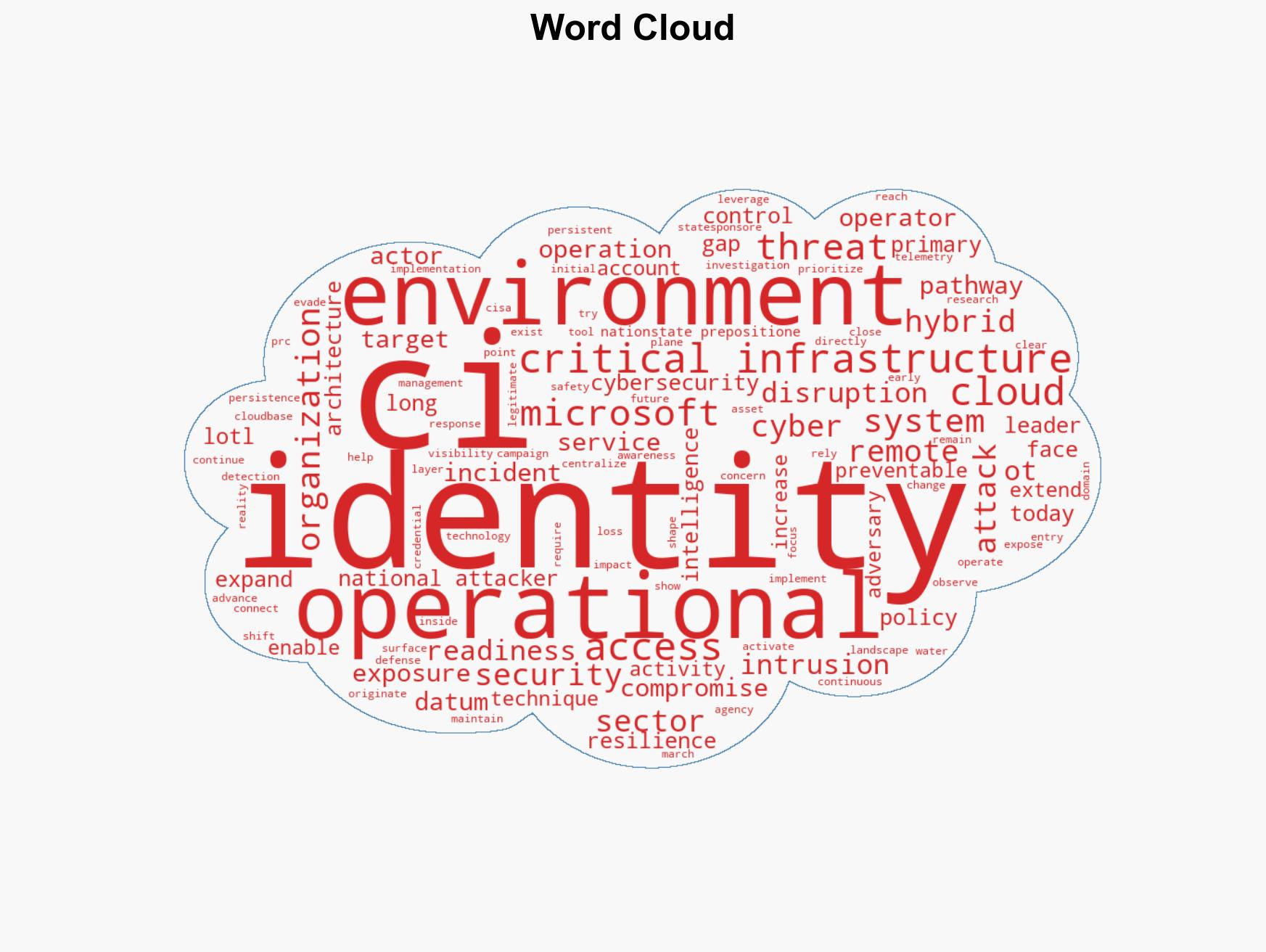
cybersecurity, critical infrastructure, national security, threat actors, regulatory compliance, cyber readiness, public safety
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us