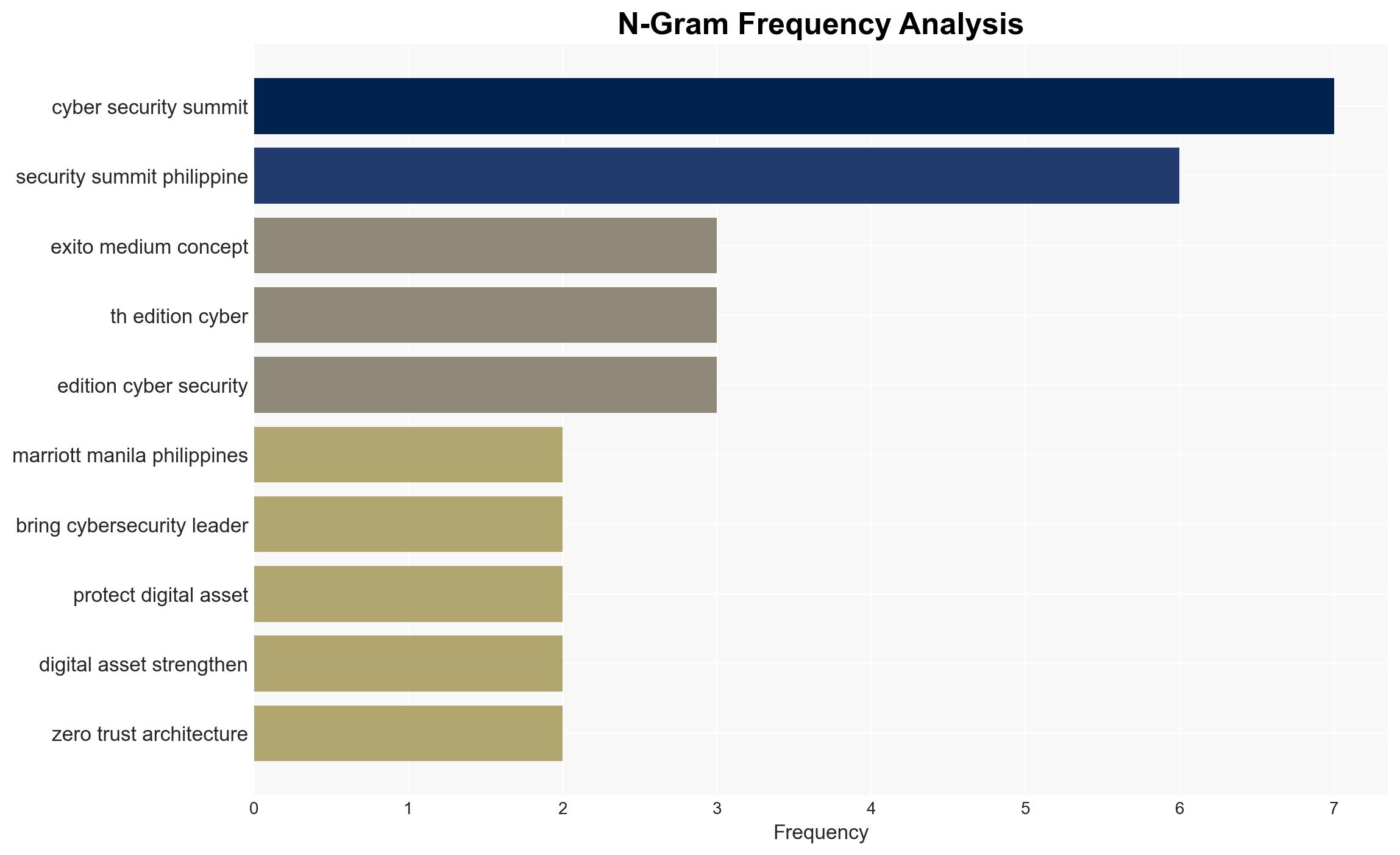
Exito Media Concepts to Host 30th Cyber Security Summit in Manila, Focusing on Future Threat Resilience
Published on: 2026-03-16
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
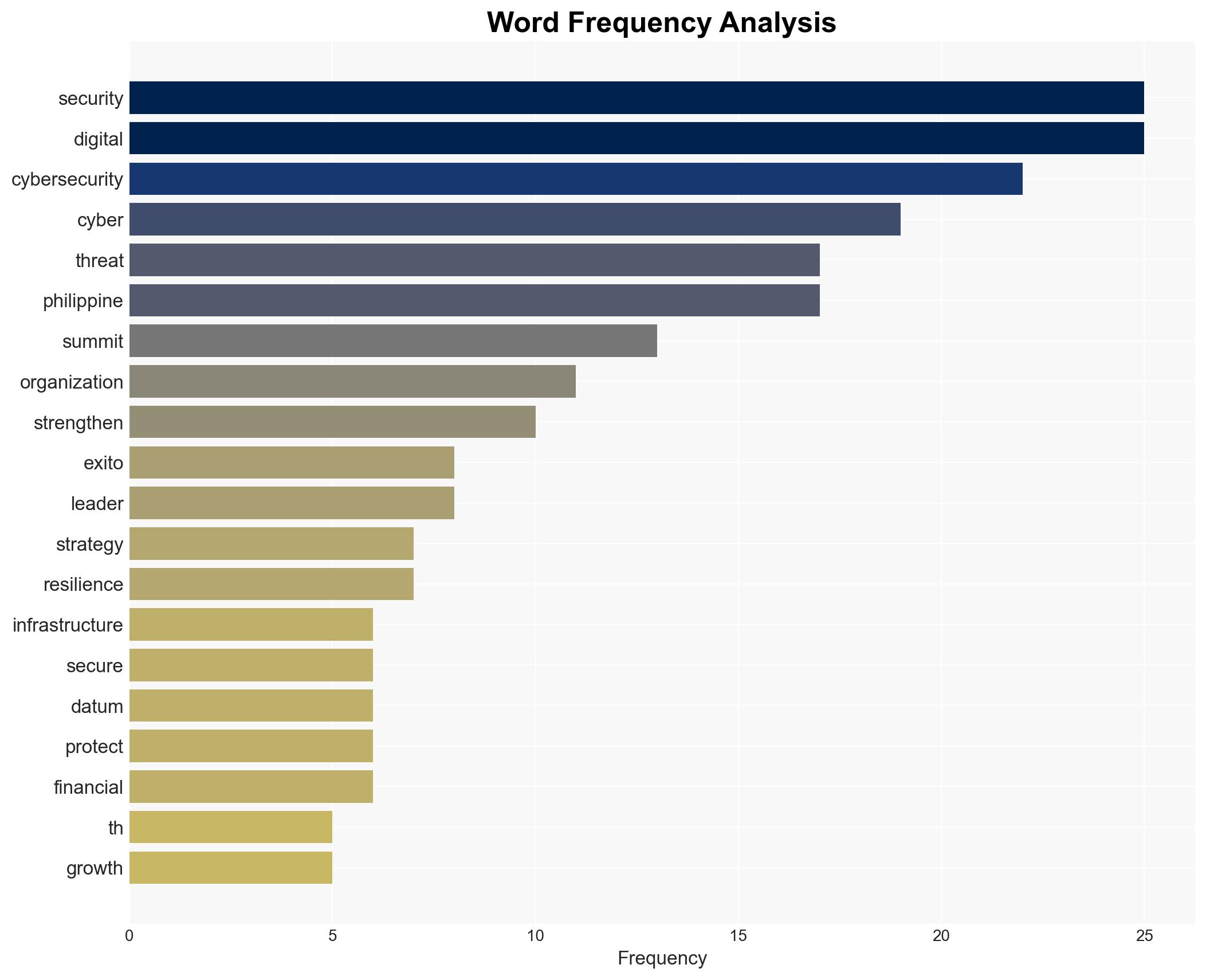
Intelligence Report: Exito Media Concepts Announces the 30th Edition of the Cyber Security Summit Philippines 2026
1. BLUF (Bottom Line Up Front)
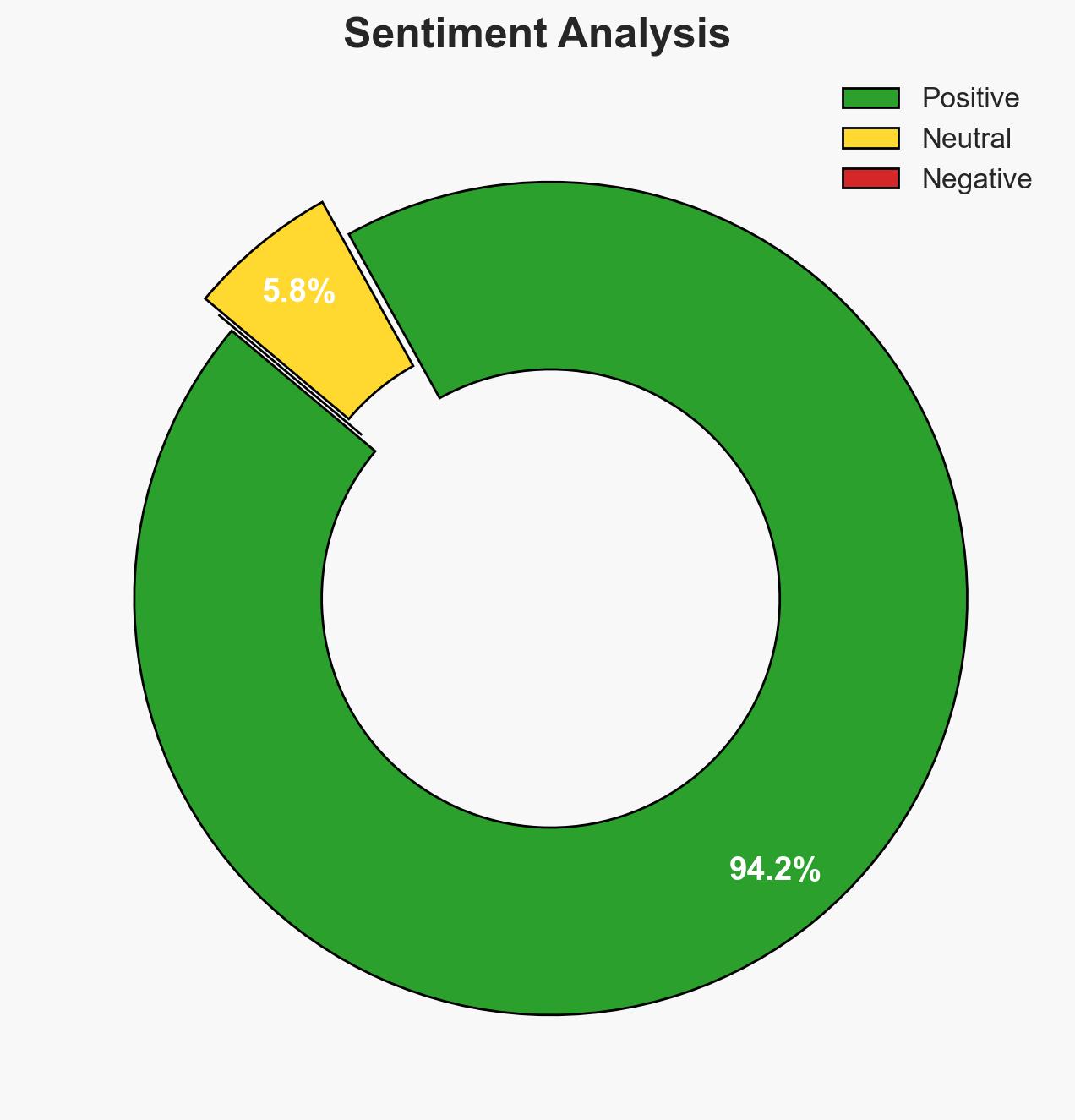
The Philippines is rapidly advancing as a digital economy, which increases its exposure to complex cyber threats. The 30th Cyber Security Summit aims to address these challenges by fostering collaboration and sharing best practices. The event is crucial for enhancing the nation’s cyber resilience. Overall confidence in this assessment is moderate due to existing information gaps and potential biases in source reporting.
2. Competing Hypotheses
- Hypothesis A: The Cyber Security Summit will significantly enhance the Philippines’ cyber defense capabilities by promoting collaboration and sharing of global best practices. This is supported by the involvement of cybersecurity leaders and government representatives. However, the effectiveness of such summits in enacting real change remains uncertain.
- Hypothesis B: The summit will have limited impact on actual cybersecurity improvements due to potential bureaucratic inertia and insufficient follow-through on initiatives. The lack of detailed implementation strategies in the provided information supports this view.
- Assessment: Hypothesis A is currently better supported due to the structured involvement of key stakeholders and the focus on strategic discussions. Indicators such as increased public-private partnerships and policy changes could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The Philippines will continue its digital expansion; stakeholders will actively engage in the summit; cyber threats will evolve in complexity.
- Information Gaps: Specific details on the summit’s agenda, participant list, and post-summit action plans are missing.
- Bias & Deception Risks: Potential source bias due to promotional nature of the announcement; lack of independent verification of the summit’s impact.
4. Implications and Strategic Risks
The summit could catalyze improvements in the Philippines’ cybersecurity posture, but its success depends on sustained engagement and implementation of discussed strategies.
- Political / Geopolitical: Enhanced cybersecurity could improve national stability and international relations, particularly within ASEAN.
- Security / Counter-Terrorism: Improved cyber defenses may reduce vulnerabilities to cyber-terrorism and espionage.
- Cyber / Information Space: Increased focus on cyber resilience could deter cybercriminal activities and protect critical infrastructure.
- Economic / Social: Strengthened cybersecurity could bolster economic growth by safeguarding digital transactions and maintaining public trust.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor summit outcomes, identify key initiatives, and assess stakeholder engagement levels.
- Medium-Term Posture (1–12 months): Develop partnerships with international cybersecurity entities, enhance public-private collaboration, and invest in cybersecurity education.
- Scenario Outlook:
- Best: Comprehensive cybersecurity reforms are implemented, leading to reduced cyber incidents.
- Worst: Summit outcomes are not acted upon, resulting in persistent vulnerabilities.
- Most-Likely: Incremental improvements in cybersecurity posture with ongoing challenges in implementation.
6. Key Individuals and Entities
- Exito Media Concepts
- Cybersecurity leaders (not clearly identifiable from open sources in this snippet)
- Philippine government representatives (not clearly identifiable from open sources in this snippet)
7. Thematic Tags
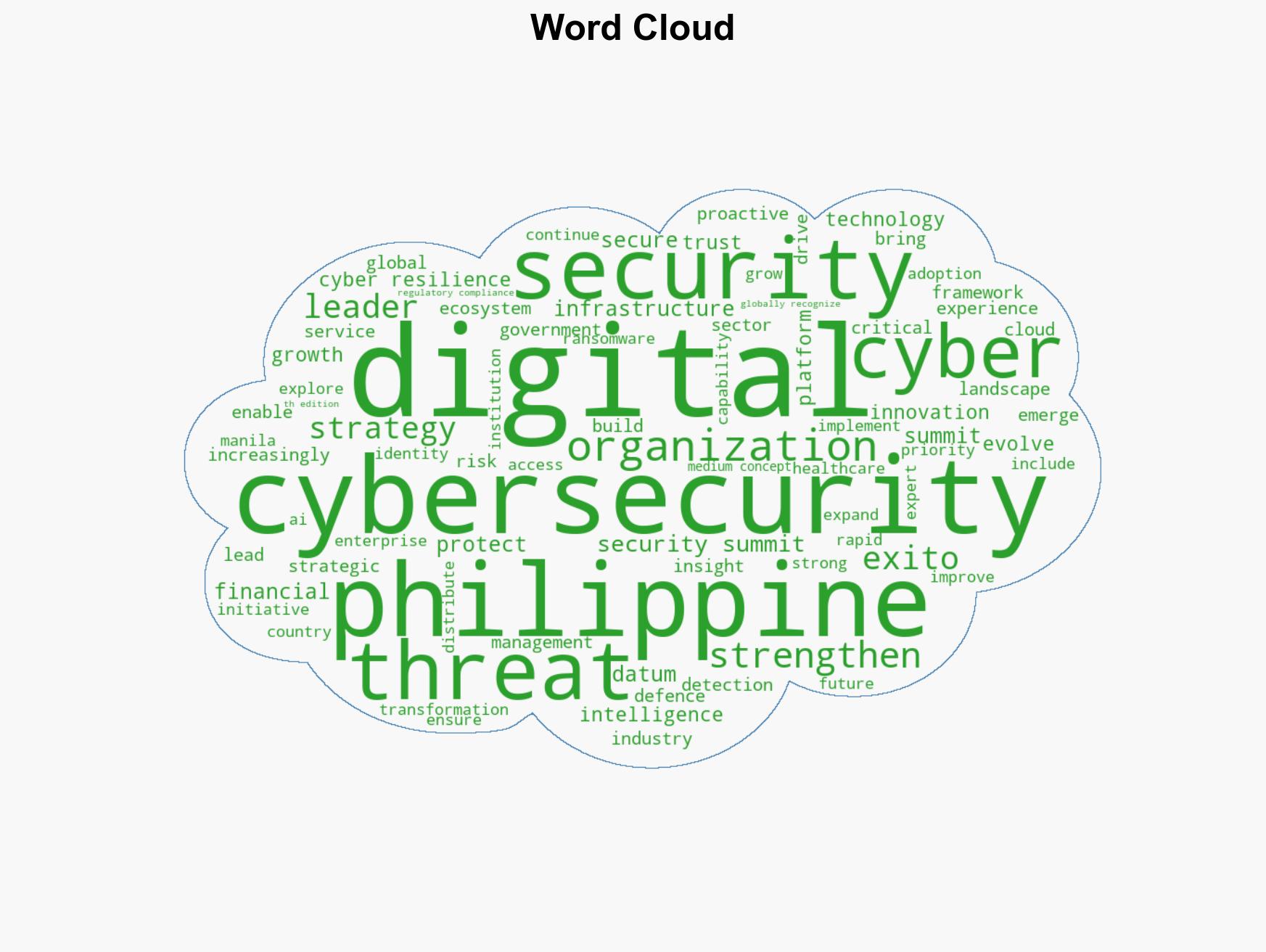
cybersecurity, digital economy, public-private partnership, cyber threats, Philippines, ASEAN, cyber resilience
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us