Experts warn of rising cyber threats to Indian firms amid escalating Middle East tensions
Published on: 2026-03-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iran conflict Companies could see rise in digital threats say experts
1. BLUF (Bottom Line Up Front)
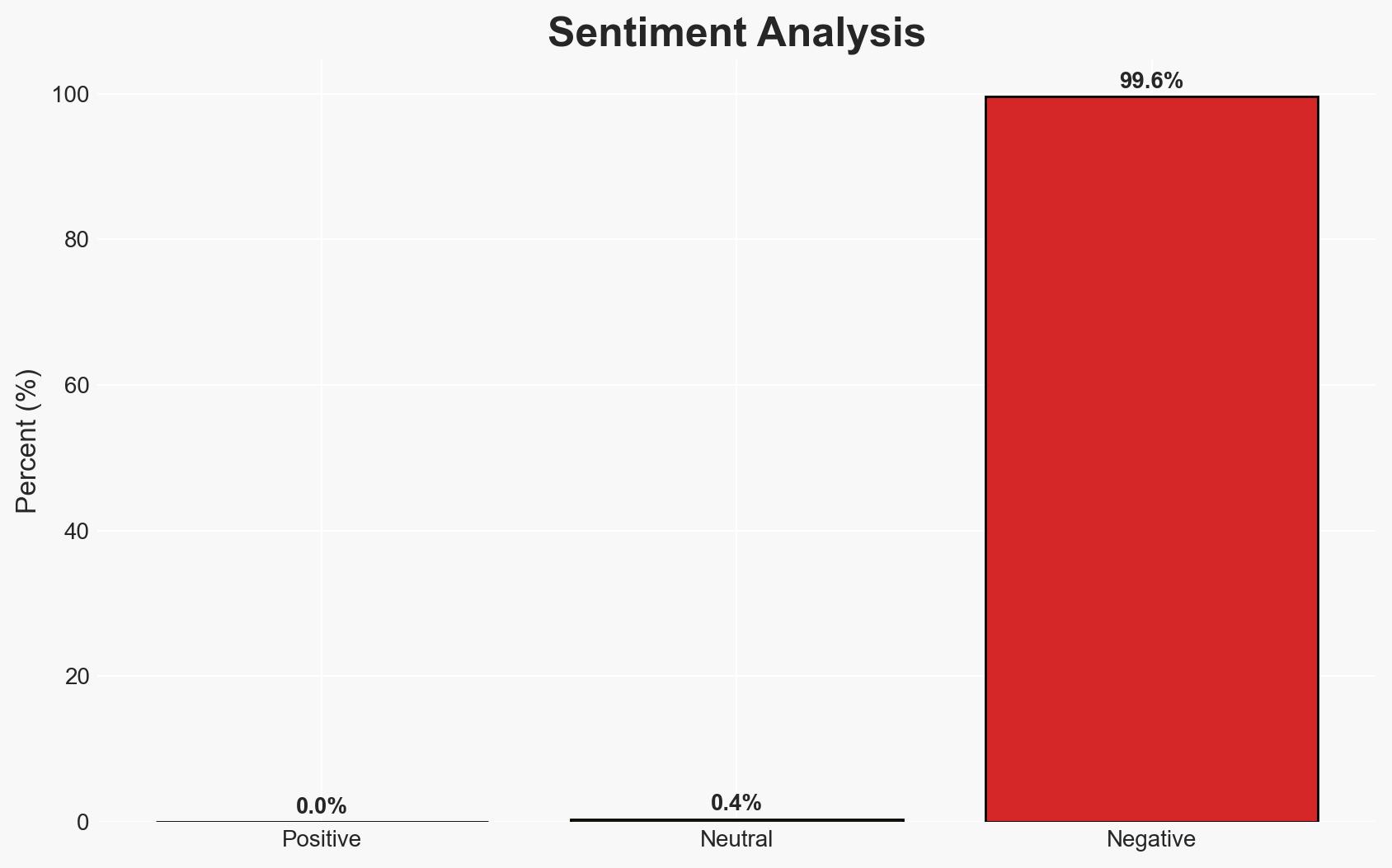
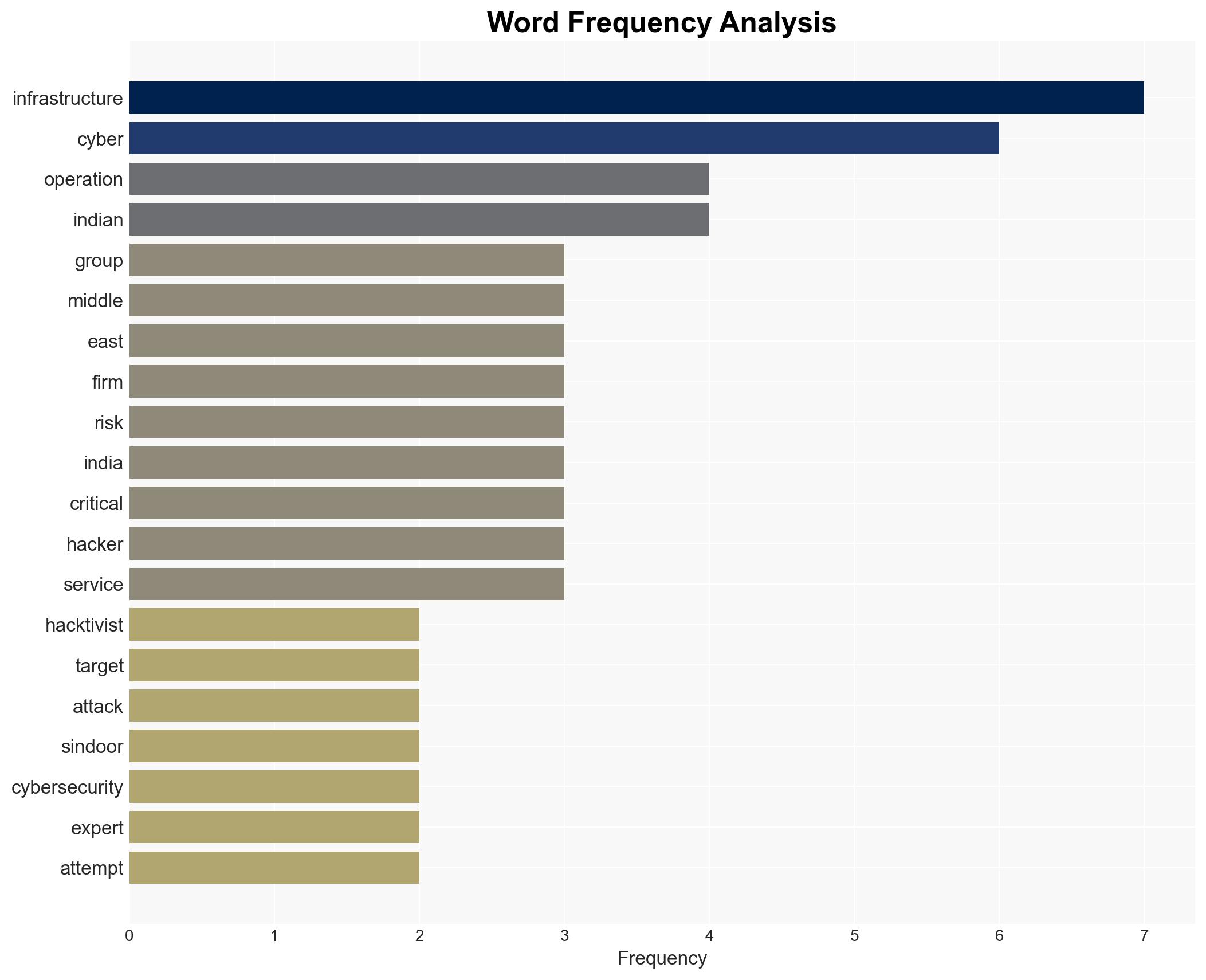
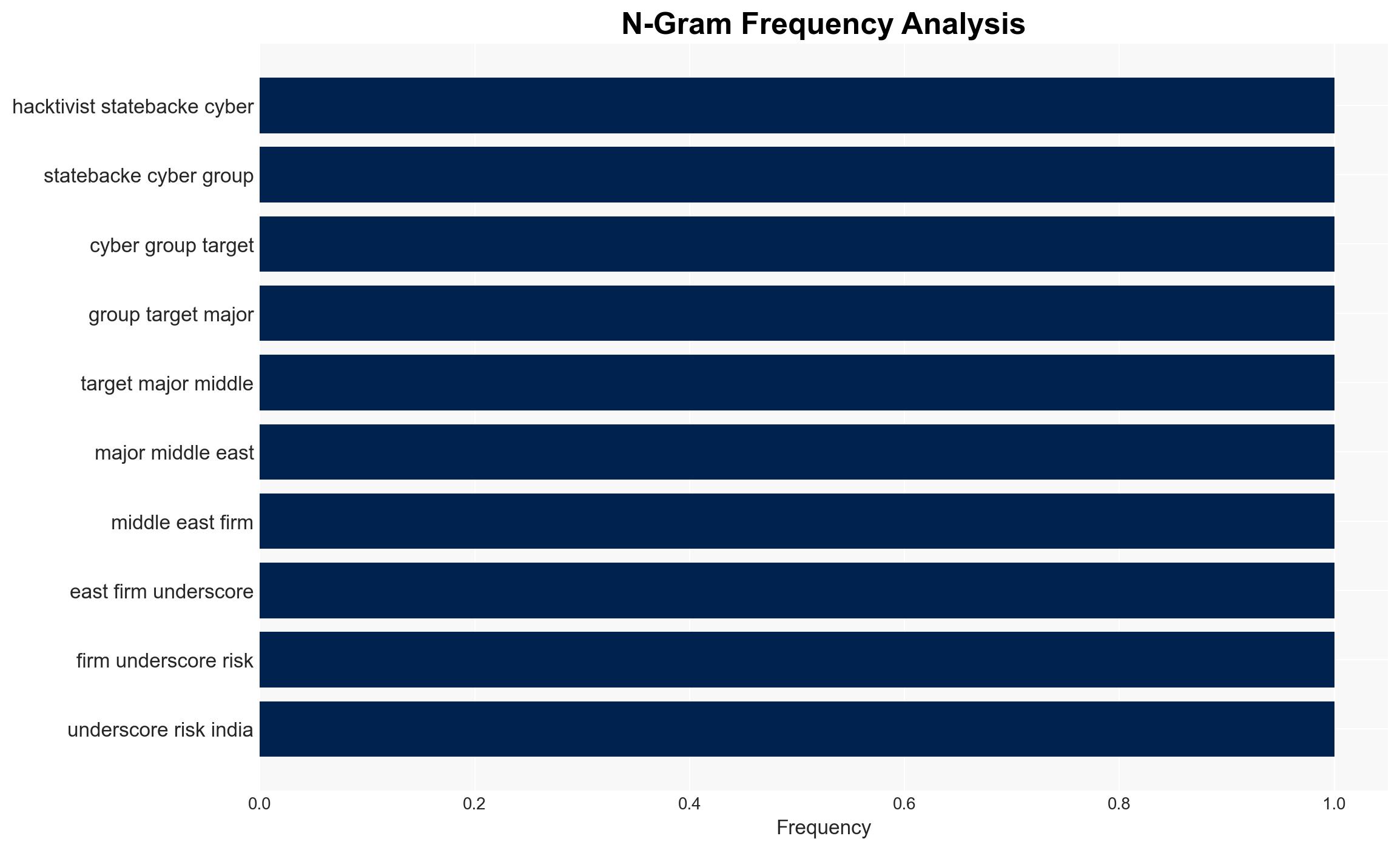
The escalation of cyber threats linked to the Iran conflict poses significant risks to Indian critical infrastructure, with potential spillover from Middle Eastern cyber operations. The most likely hypothesis is that Iranian-aligned groups will indirectly target Indian entities as part of broader geopolitical retaliation. This assessment is made with moderate confidence, given current evidence and historical patterns of cyber engagement in the region.
2. Competing Hypotheses
- Hypothesis A: Iranian-aligned APT groups and hacktivists will indirectly target Indian critical infrastructure as part of a broader geopolitical retaliation strategy. This is supported by historical precedents of cyber spillover during regional conflicts and recent advisories from cybersecurity experts. However, there is uncertainty regarding the specific timing and scale of such attacks.
- Hypothesis B: The cyber threat to Indian infrastructure is overstated, and any incidents will be isolated and not part of a coordinated campaign. This could be supported by the lack of direct evidence linking current Middle Eastern cyber operations to specific threats against India. Contradicting evidence includes the ongoing advisories and historical patterns of cyber threats during regional conflicts.
- Assessment: Hypothesis A is currently better supported due to the alignment of expert advisories with historical patterns of cyber operations during geopolitical tensions. Indicators that could shift this judgment include a lack of cyber incidents targeting Indian infrastructure in the coming weeks or credible intelligence suggesting a de-escalation of cyber activities by Iranian-aligned groups.
3. Key Assumptions and Red Flags
- Assumptions: Iranian-aligned groups have the capability and intent to target Indian infrastructure; cyber operations will continue to be a tool of geopolitical influence; Indian infrastructure remains a viable target due to its strategic importance.
- Information Gaps: Specific intelligence on planned cyber operations targeting India; detailed attribution of recent cyber incidents in the Middle East to specific groups.
- Bias & Deception Risks: Potential over-reliance on historical patterns without considering new tactics; source bias from cybersecurity firms with vested interests in promoting threat awareness.
4. Implications and Strategic Risks
The evolving cyber threat landscape could exacerbate regional tensions and impact global cybersecurity postures. Indian entities may face increased operational risks, necessitating enhanced defensive measures.
- Political / Geopolitical: Escalation of cyber activities may strain diplomatic relations and complicate regional stability efforts.
- Security / Counter-Terrorism: Increased cyber threats could divert resources from traditional security operations, impacting counter-terrorism efforts.
- Cyber / Information Space: Potential for widespread misinformation campaigns and espionage activities targeting Indian and regional entities.
- Economic / Social: Disruptions to critical infrastructure could have cascading effects on economic stability and public confidence in digital services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of critical infrastructure, conduct cyber readiness exercises, and increase information sharing with international partners.
- Medium-Term Posture (1–12 months): Develop resilience measures, strengthen public-private partnerships, and invest in cybersecurity capability development.
- Scenario Outlook:
- Best: De-escalation of cyber activities with minimal impact on Indian infrastructure.
- Worst: Coordinated cyberattacks causing significant disruptions to critical services.
- Most-Likely: Sporadic cyber incidents with manageable impact, requiring ongoing vigilance.
6. Key Individuals and Entities
- Siddharth Vishwanath, Partner and Risk Consulting Leader at PwC India
- CloudSEK, threat intelligence firm
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
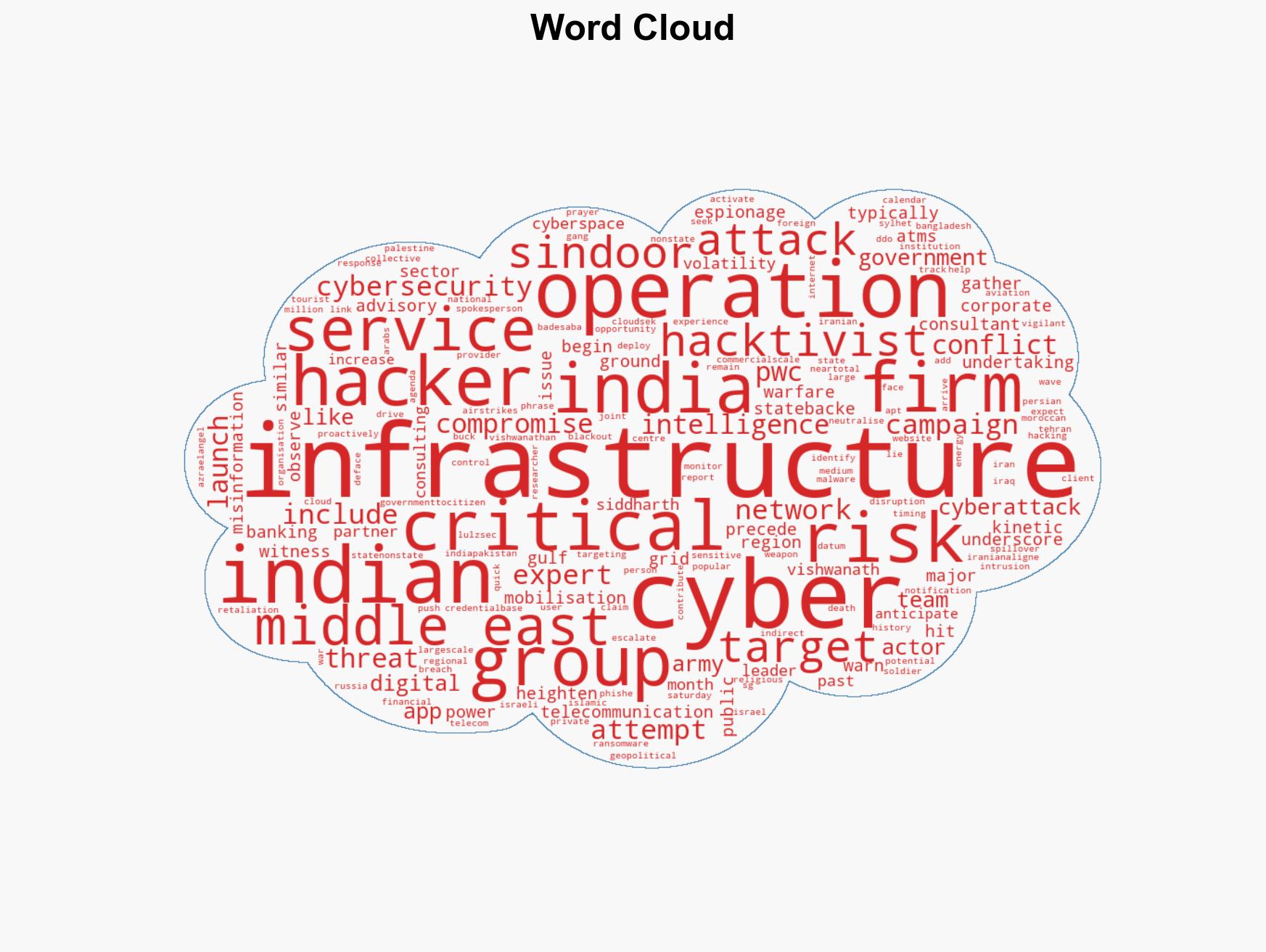
cybersecurity, geopolitical tensions, critical infrastructure, cyber warfare, misinformation campaigns, regional conflict, cyber resilience
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us