Exposed Spring Boot Actuator Leads to Credential Theft and MFA Bypass in SharePoint Data Breach
Published on: 2026-03-18
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: From Misconfigured Spring Boot Actuator to SharePoint Exfiltration How Stolen Credentials Bypass MFA
1. BLUF (Bottom Line Up Front)
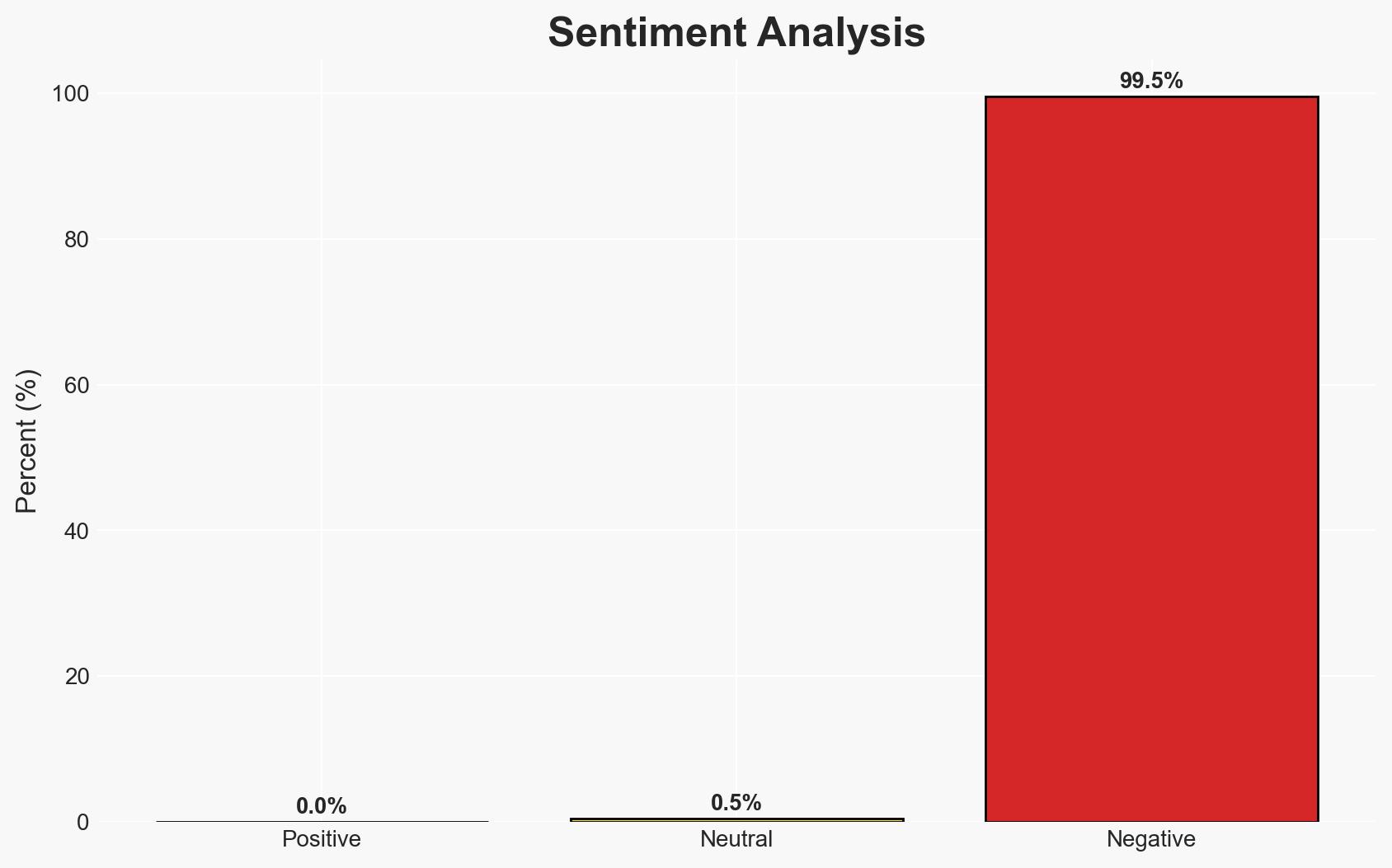
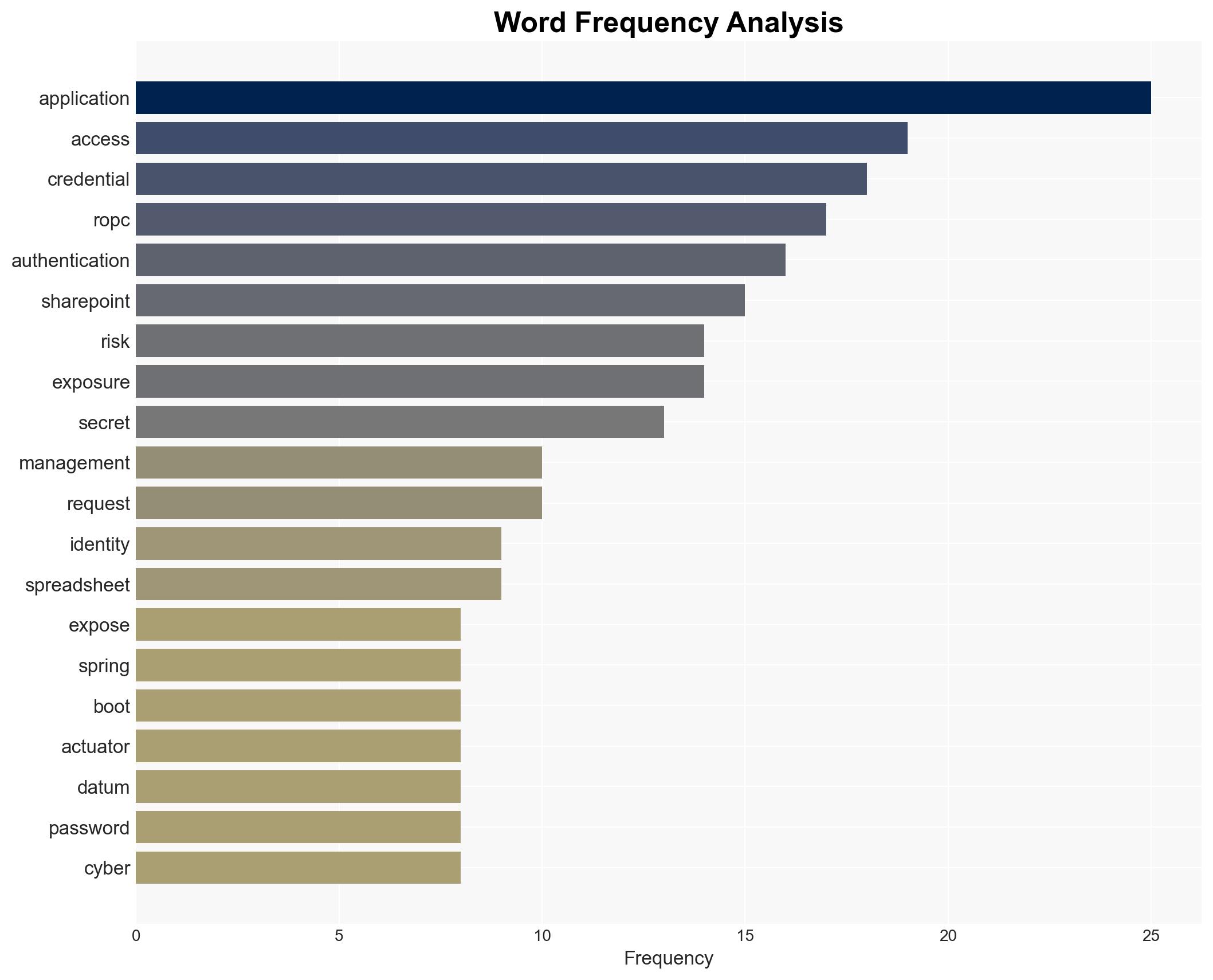
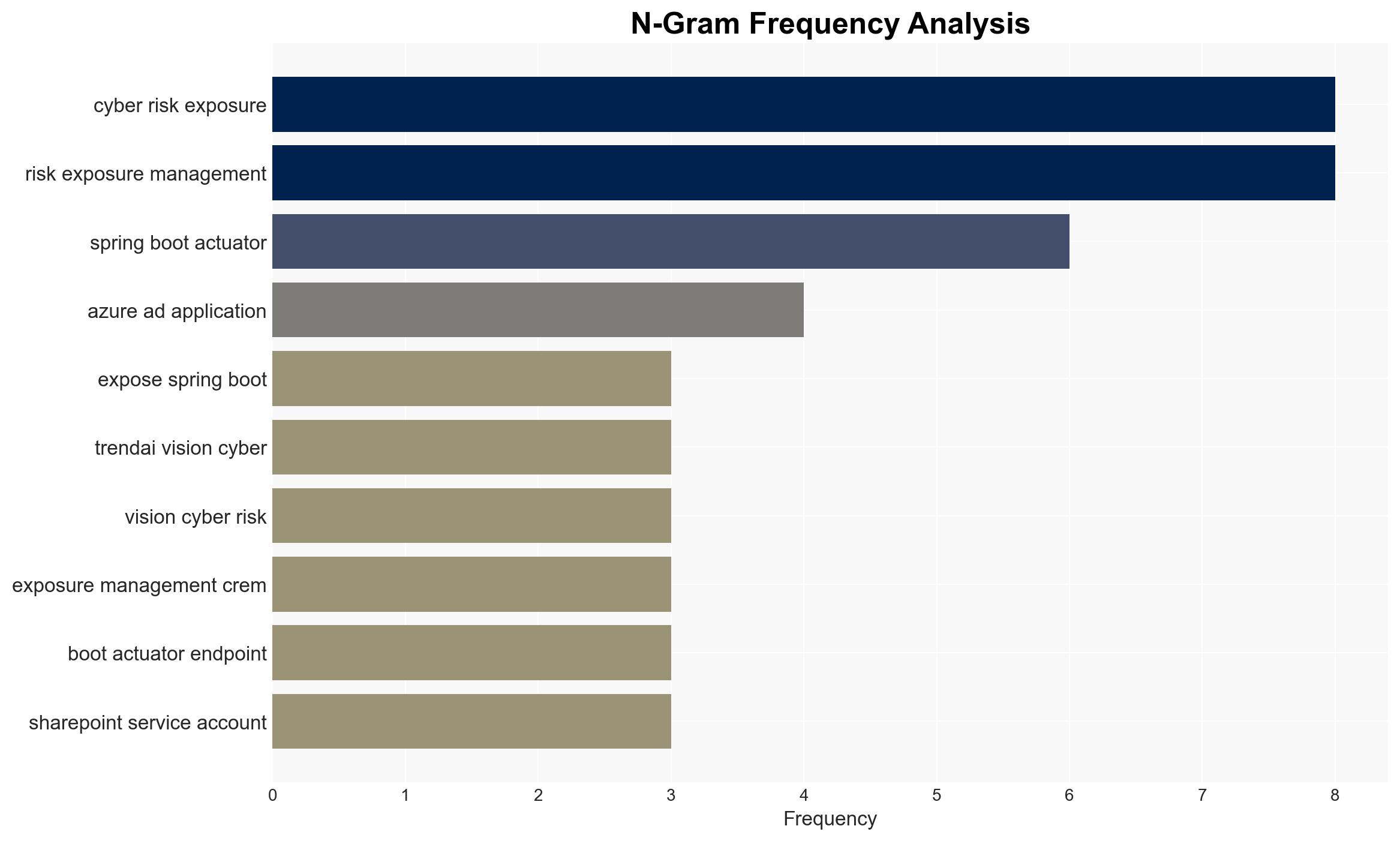
The incident involving misconfigured Spring Boot Actuator endpoints and poor credential management highlights significant vulnerabilities in cybersecurity practices, leading to potential data exfiltration from SharePoint Online. The most likely hypothesis is that these vulnerabilities were exploited by cybercriminals to gain unauthorized access, with moderate confidence in this assessment. Organizations using similar configurations are at risk.
2. Competing Hypotheses
- Hypothesis A: The misconfigured Spring Boot Actuator and plaintext credential storage were exploited by cybercriminals to gain unauthorized access to SharePoint Online. Supporting evidence includes the exposed actuator endpoints and plaintext credentials. Key uncertainties involve the identity and intent of the threat actors.
- Hypothesis B: The vulnerabilities were identified by internal security teams or ethical hackers during routine audits, and no malicious exploitation occurred. This is contradicted by the data exfiltration evidence, but the lack of direct evidence of external actor involvement leaves room for consideration.
- Assessment: Hypothesis A is currently best supported due to the evidence of data exfiltration and the known vulnerabilities. Indicators such as unusual access patterns or external communications could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The exposed endpoints and plaintext credentials were accessible to external actors; the attackers had the capability to exploit these vulnerabilities.
- Information Gaps: The identity of the threat actors and their specific methods of exploiting the vulnerabilities remain unknown.
- Bias & Deception Risks: Confirmation bias may lead to overestimating the likelihood of external exploitation without considering internal security lapses. The possibility of deception by the attackers to mask their true methods should be considered.
4. Implications and Strategic Risks
This development could lead to increased scrutiny of cybersecurity practices and potential regulatory changes. The incident underscores the need for robust security measures and could influence organizational policies.
- Political / Geopolitical: Potential for increased regulatory pressure on cybersecurity standards.
- Security / Counter-Terrorism: Heightened threat environment due to potential exploitation by cybercriminals or state actors.
- Cyber / Information Space: Increased focus on securing application configurations and credential management practices.
- Economic / Social: Potential financial losses and reputational damage for affected organizations, impacting stakeholder trust.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct thorough security audits, restrict access to actuator endpoints, and remove plaintext credentials from insecure storage.
- Medium-Term Posture (1–12 months): Implement comprehensive cyber risk exposure management and enhance identity controls to prevent similar incidents.
- Scenario Outlook: Best: Strengthened security posture with no further incidents. Worst: Continued exploitation leading to significant data breaches. Most-Likely: Incremental improvements in security practices with occasional breaches.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
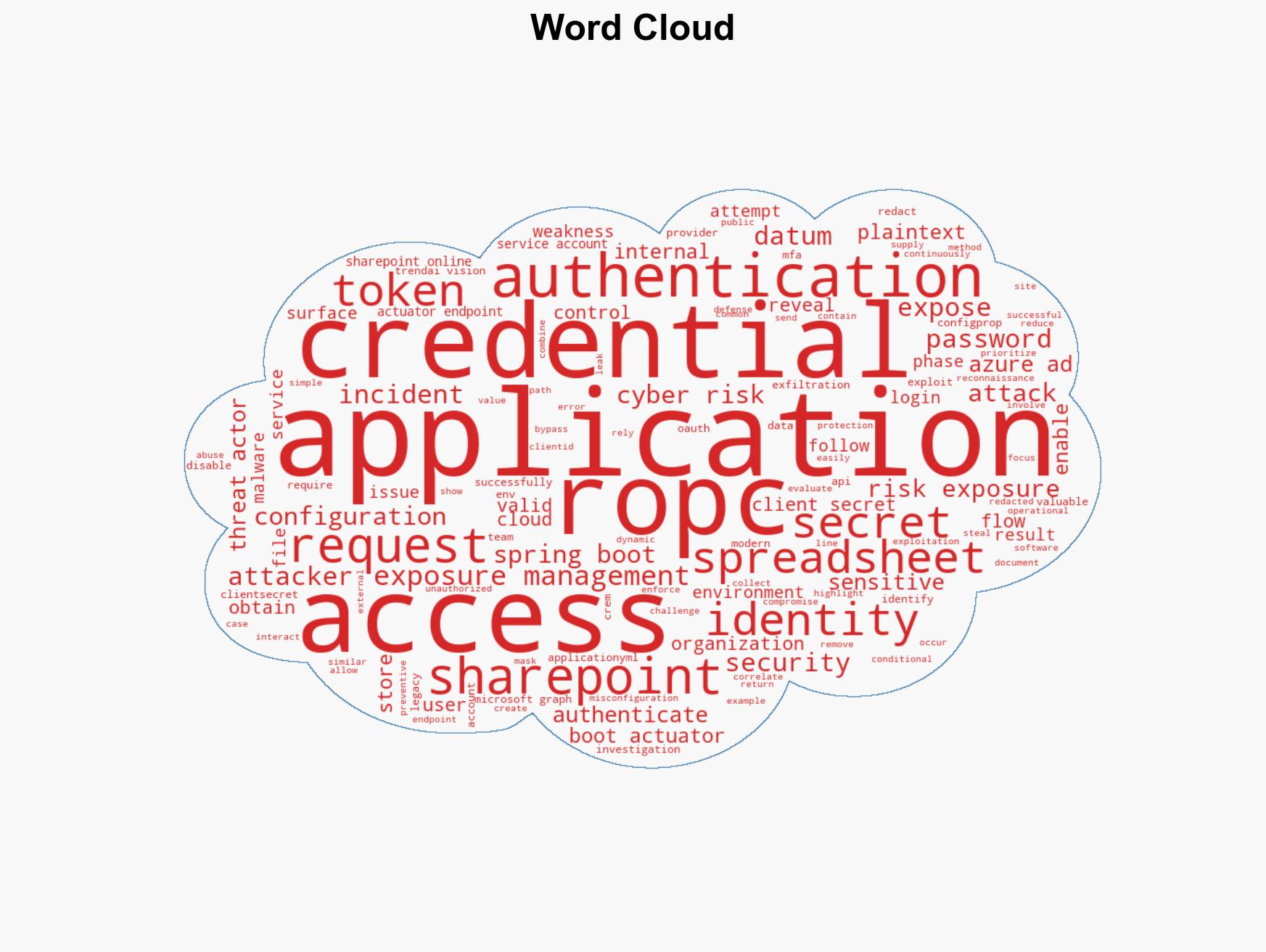
cybersecurity, data exfiltration, credential management, vulnerability exploitation, cyber risk management, information security, application security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us