Fake FSB Officer Allegedly Attempts to Extort Notorious Ransomware Group Conti
Published on: 2026-02-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
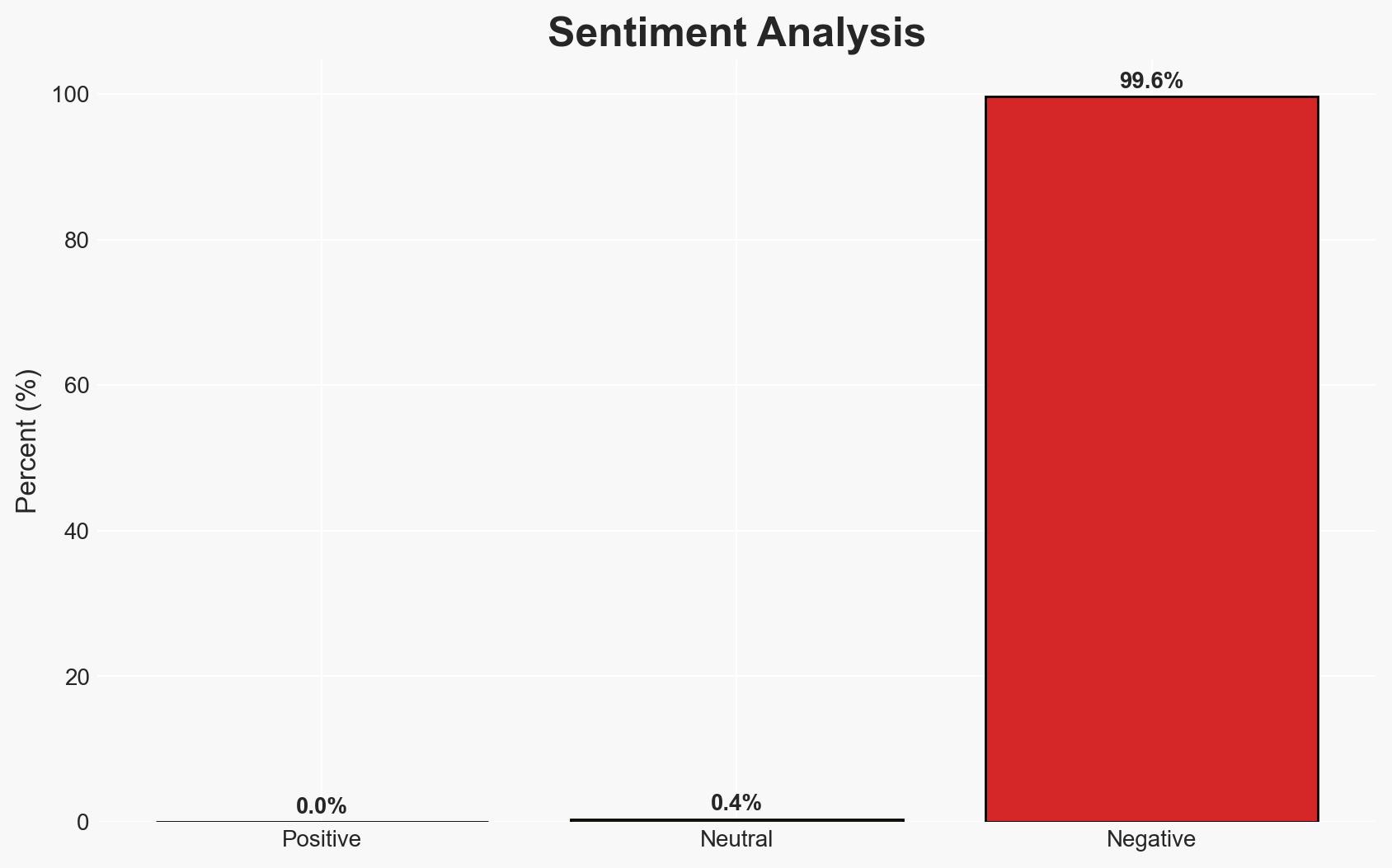
Intelligence Report: Notorious ransomware gang allegedly blackmailed by fake FSB officer
1. BLUF (Bottom Line Up Front)
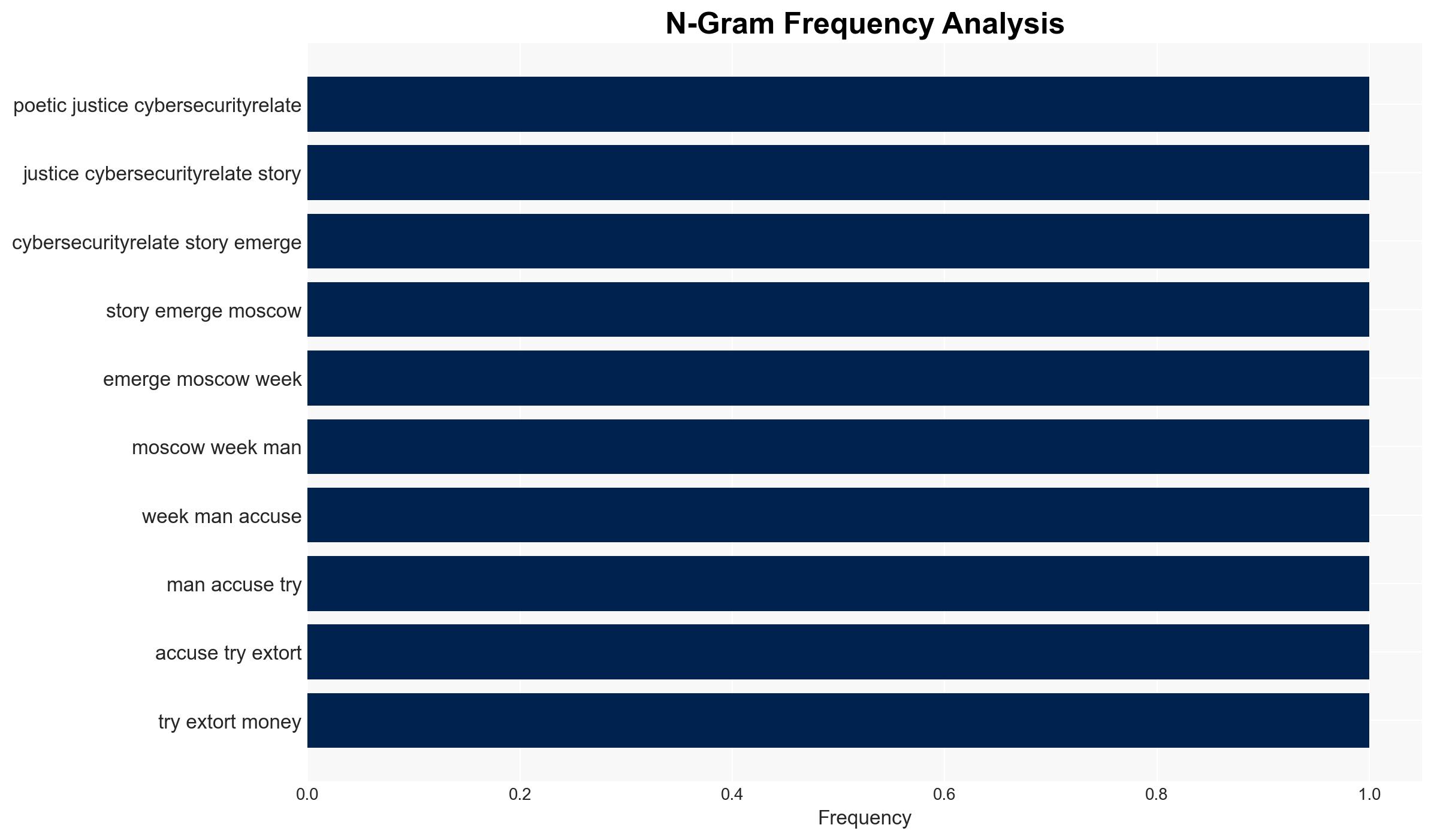
The alleged attempt to extort the Conti ransomware gang by an individual posing as an FSB officer highlights vulnerabilities within cybercriminal networks and potential state-criminal nexus. The incident underscores the complexity of cybercrime dynamics in Russia. Moderate confidence is placed in the hypothesis that this was an opportunistic scam rather than a state-sanctioned operation.
2. Competing Hypotheses
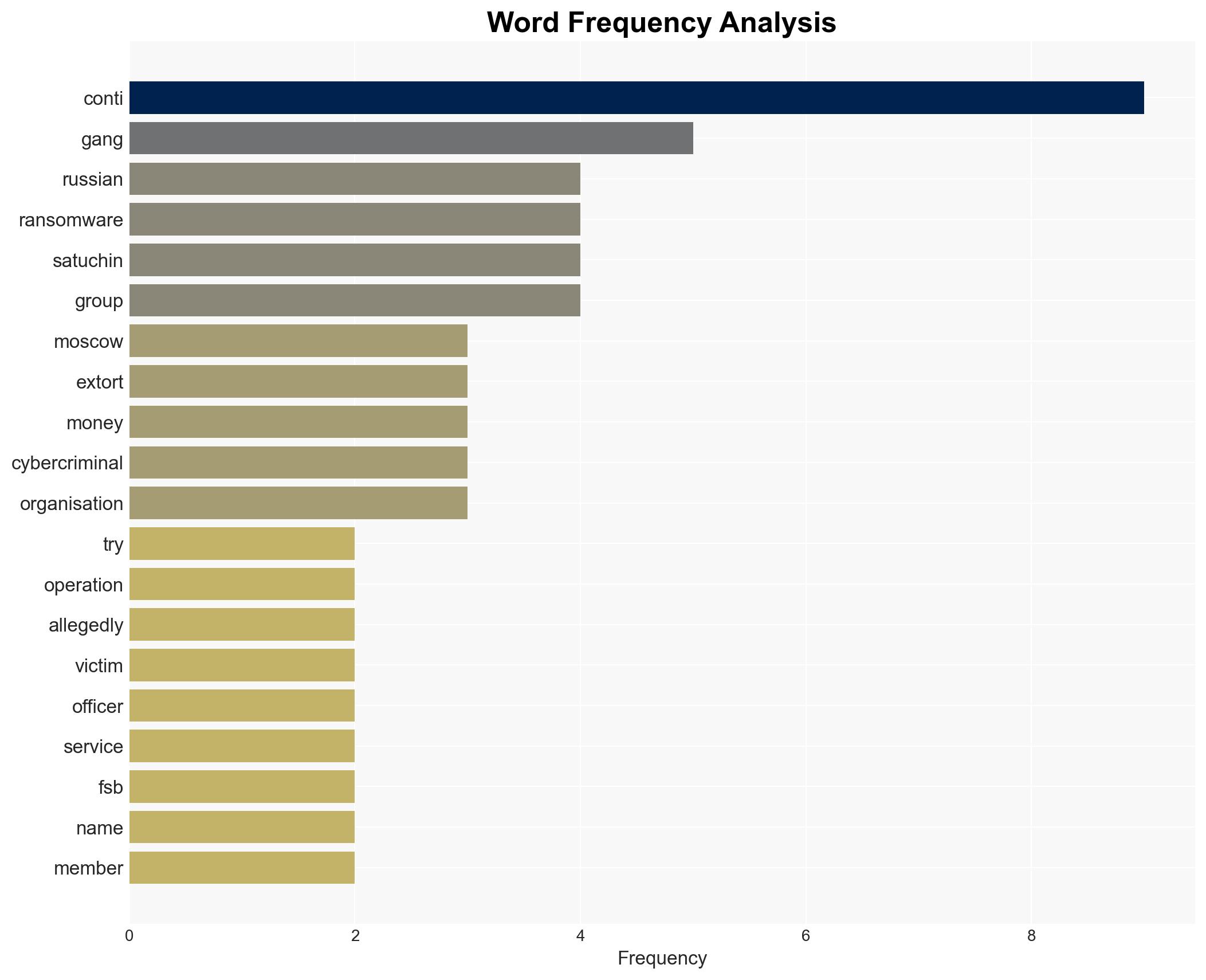
- Hypothesis A: The extortion attempt was an independent scam by Ruslan Satuchin, exploiting perceived protection of Conti by Russian authorities. This is supported by Satuchin’s arrest and lack of evidence of state involvement. Key uncertainties include Satuchin’s actual connections and motivations.
- Hypothesis B: The extortion was part of a broader intelligence operation, possibly sanctioned by a faction within Russian security services to exert control over cybercriminals. Contradicting evidence includes the lack of official support for Satuchin and his detention.
- Assessment: Hypothesis A is currently better supported due to the absence of clear indicators of state involvement and Satuchin’s arrest. Indicators that could shift this judgment include evidence of Satuchin’s connections to Russian security services or changes in state policy towards cybercriminals.
3. Key Assumptions and Red Flags
- Assumptions: The Russian state has a vested interest in controlling cybercriminal activities; Conti’s historical avoidance of Russian targets implies some level of tacit state protection; Satuchin acted independently without state backing.
- Information Gaps: Details on Satuchin’s background and connections; the extent of Conti’s current operations and affiliations; Russian state policy towards cybercriminals post-Conti leaks.
- Bias & Deception Risks: Potential bias in Russian media reporting; deception by Satuchin regarding his motives; cognitive bias in interpreting state-criminal relationships.
4. Implications and Strategic Risks
This development could influence the operational landscape of cybercriminal groups and state interactions. It may prompt shifts in cybercriminal strategies and state responses.
- Political / Geopolitical: Potential strain on Russia’s international relations if perceived as harboring cybercriminals; internal power dynamics within Russian security services.
- Security / Counter-Terrorism: Possible increase in cybercriminal activity as groups reassess their security and state relationships.
- Cyber / Information Space: Increased scrutiny on Russian cyber activities; potential for more leaks and exposure of cybercriminal operations.
- Economic / Social: Continued economic impact from ransomware activities; potential public perception issues regarding state involvement in cybercrime.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor Russian media and legal proceedings for further details; engage with cybersecurity partners to assess shifts in ransomware tactics.
- Medium-Term Posture (1–12 months): Strengthen international cybercrime cooperation; develop resilience measures against ransomware threats.
- Scenario Outlook: Best: Reduction in ransomware activities due to increased scrutiny. Worst: Escalation of cybercriminal activities with state complicity. Most-Likely: Continued opportunistic scams and minor shifts in cybercriminal strategies.
6. Key Individuals and Entities
- Ruslan Satuchin, alleged scammer
- Conti ransomware gang, cybercriminal group
- Federal Security Service (FSB), Russian security agency
7. Thematic Tags
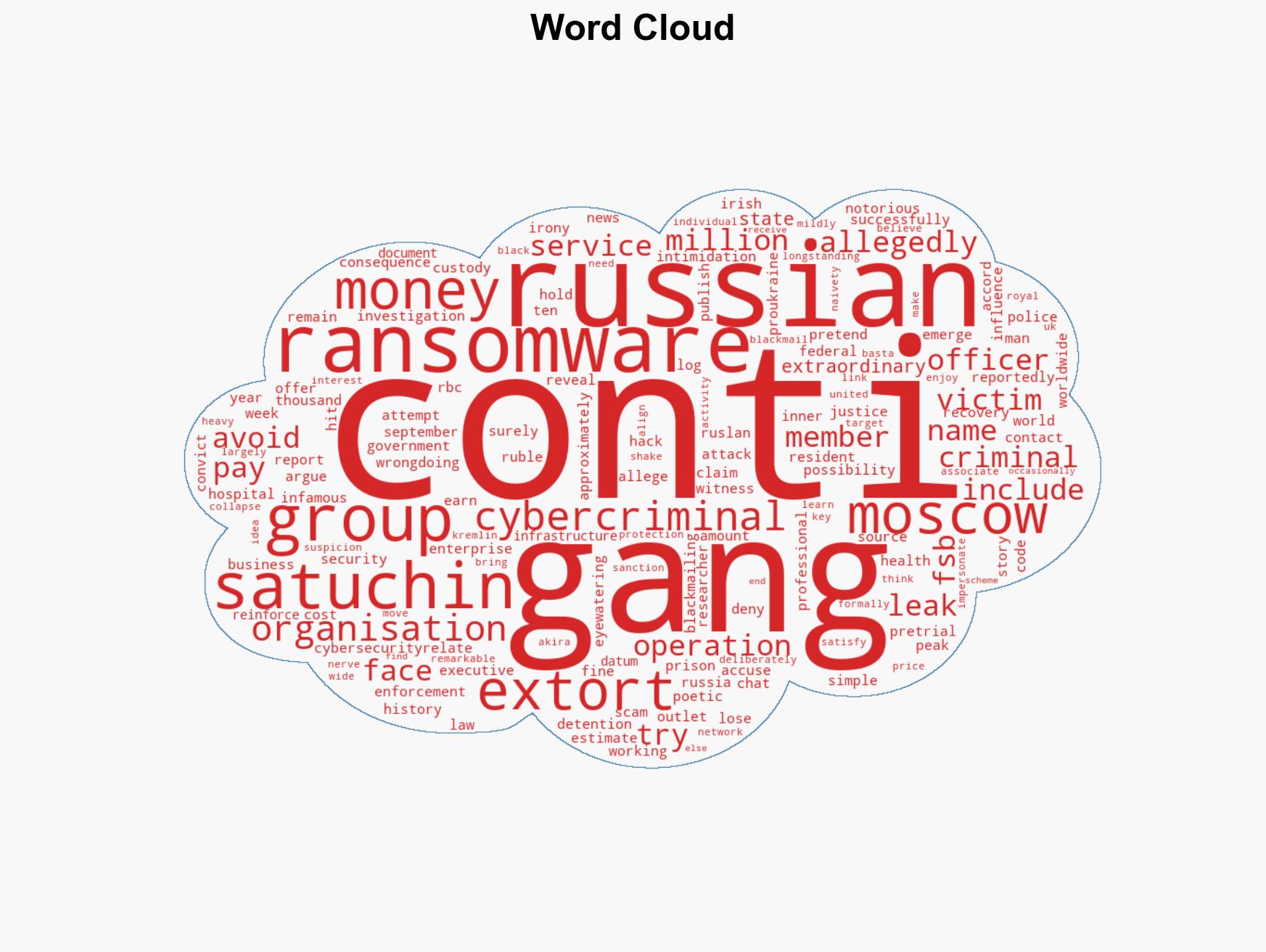
cybersecurity, cybercrime, ransomware, Russian security services, state-criminal nexus, cyber operations, information security, geopolitical risk
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us