FBI and Europol Take Down LeakBase Cybercrime Forum in Global Operation Against Cybercrime
Published on: 2026-03-05
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Operation Leak FBI and Europol dismantle LeakBase Cybercrime forum
1. BLUF (Bottom Line Up Front)
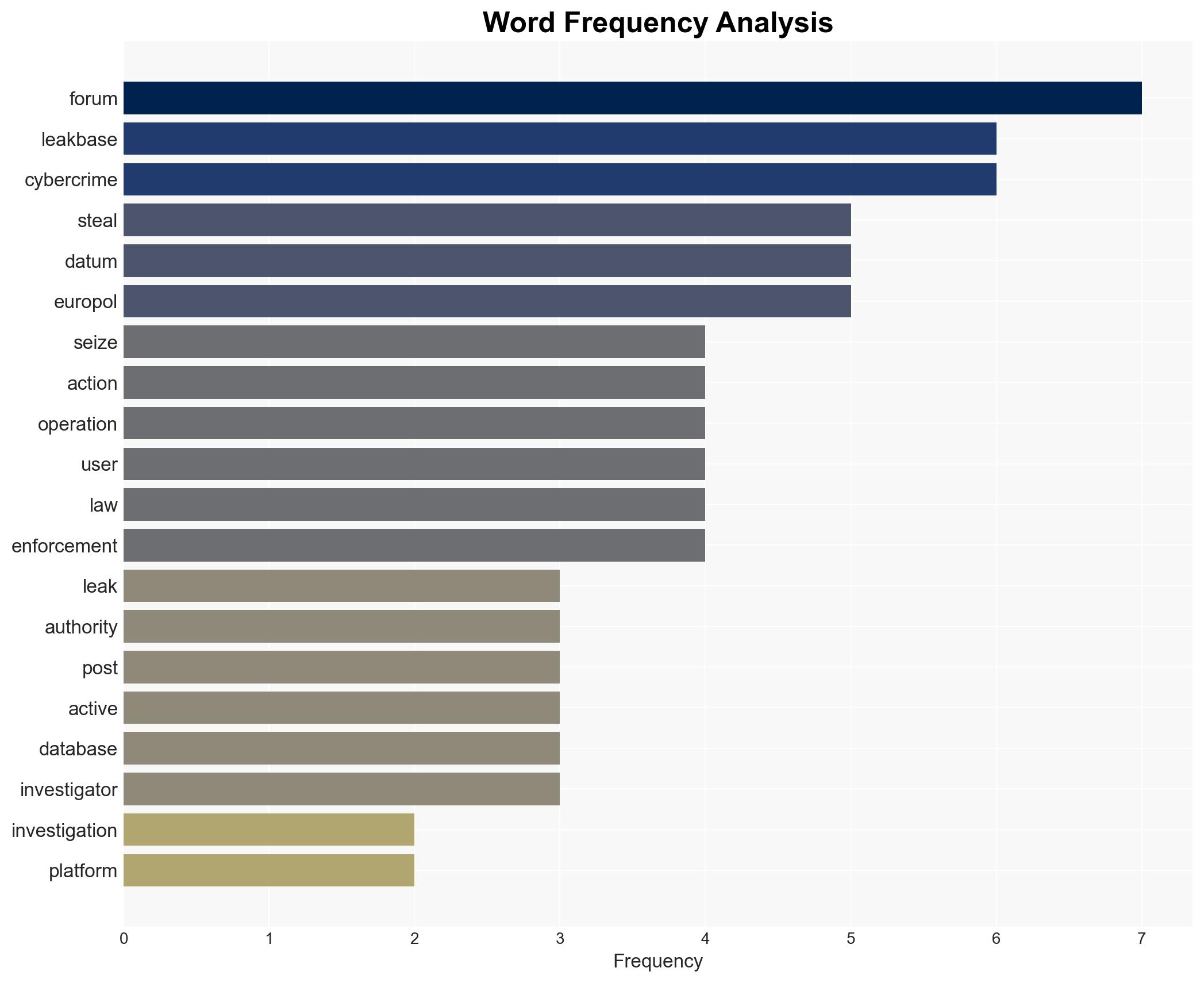
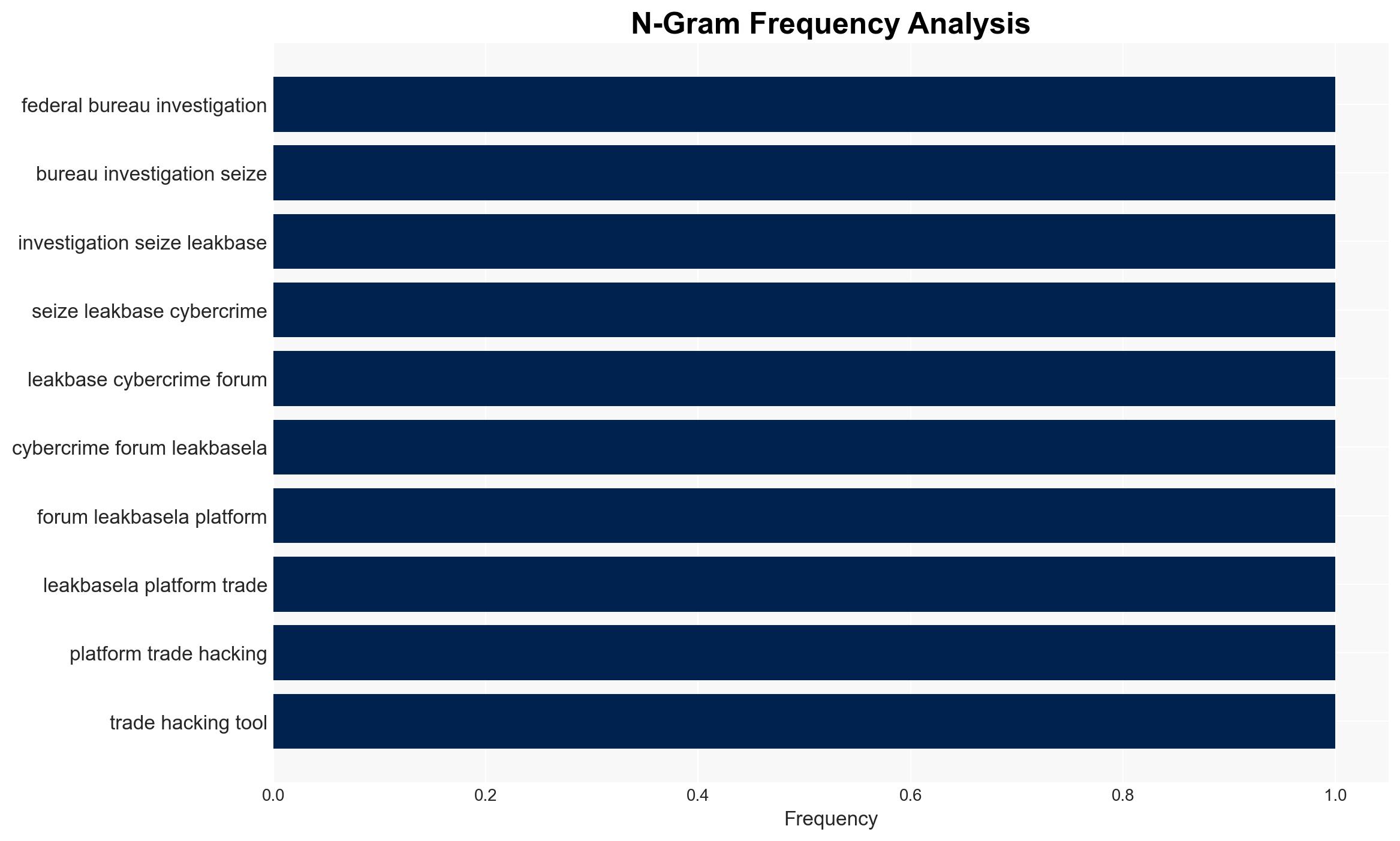
The dismantling of the LeakBase cybercrime forum by the FBI and Europol marks a significant disruption in the cybercrime ecosystem, targeting a major hub for trading stolen data and hacking tools. This operation, involving 14 countries, highlights international cooperation in cyber law enforcement. The most likely hypothesis is that this will temporarily disrupt cybercriminal activities but may lead to the emergence of alternative platforms. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The dismantling of LeakBase will significantly disrupt cybercriminal activities by removing a major platform for trading stolen data. Supporting evidence includes the seizure of the forum’s infrastructure and user data, which could lead to arrests and deterrence. Key uncertainties include the ability of cybercriminals to adapt and migrate to other platforms.
- Hypothesis B: The operation will have limited long-term impact as cybercriminals will quickly adapt by moving to alternative forums or creating new platforms. This is supported by historical patterns of resilience in cybercrime networks. Contradicting evidence includes the scale of the operation and the potential for law enforcement to use seized data for further investigations.
- Assessment: Hypothesis B is currently better supported due to the adaptability of cybercriminal networks and the likelihood of rapid migration to other platforms. Key indicators that could shift this judgment include the effectiveness of follow-up investigations and arrests based on seized data.
3. Key Assumptions and Red Flags
- Assumptions: The operation has effectively seized all critical infrastructure of LeakBase; cybercriminals will seek alternative platforms; international cooperation will continue in follow-up actions.
- Information Gaps: Details on the extent of data seized and the specific identities of key forum operators are lacking.
- Bias & Deception Risks: Potential bias in overestimating the deterrent effect of the operation; risk of deception by cybercriminals using false identities or misinformation to mislead investigators.
4. Implications and Strategic Risks
This development could lead to temporary disruption in cybercrime activities but may also drive innovation in cybercriminal tactics and platforms.
- Political / Geopolitical: Strengthened international law enforcement cooperation could enhance global cybercrime deterrence.
- Security / Counter-Terrorism: Potential for increased cybercriminal activity as actors seek to re-establish networks, posing ongoing threats to data security.
- Cyber / Information Space: Possible emergence of more secure, decentralized platforms that are harder to infiltrate by law enforcement.
- Economic / Social: Continued risk of identity theft and financial fraud as stolen data remains in circulation; potential public awareness increase regarding cybersecurity practices.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor for the emergence of new cybercrime forums; enhance public awareness campaigns on cybersecurity.
- Medium-Term Posture (1–12 months): Strengthen international partnerships and information-sharing mechanisms; invest in cyber forensics and investigative capabilities.
- Scenario Outlook: Best: Sustained disruption of cybercrime networks; Worst: Rapid re-establishment of forums with enhanced security; Most-Likely: Gradual adaptation by cybercriminals with intermittent disruptions.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
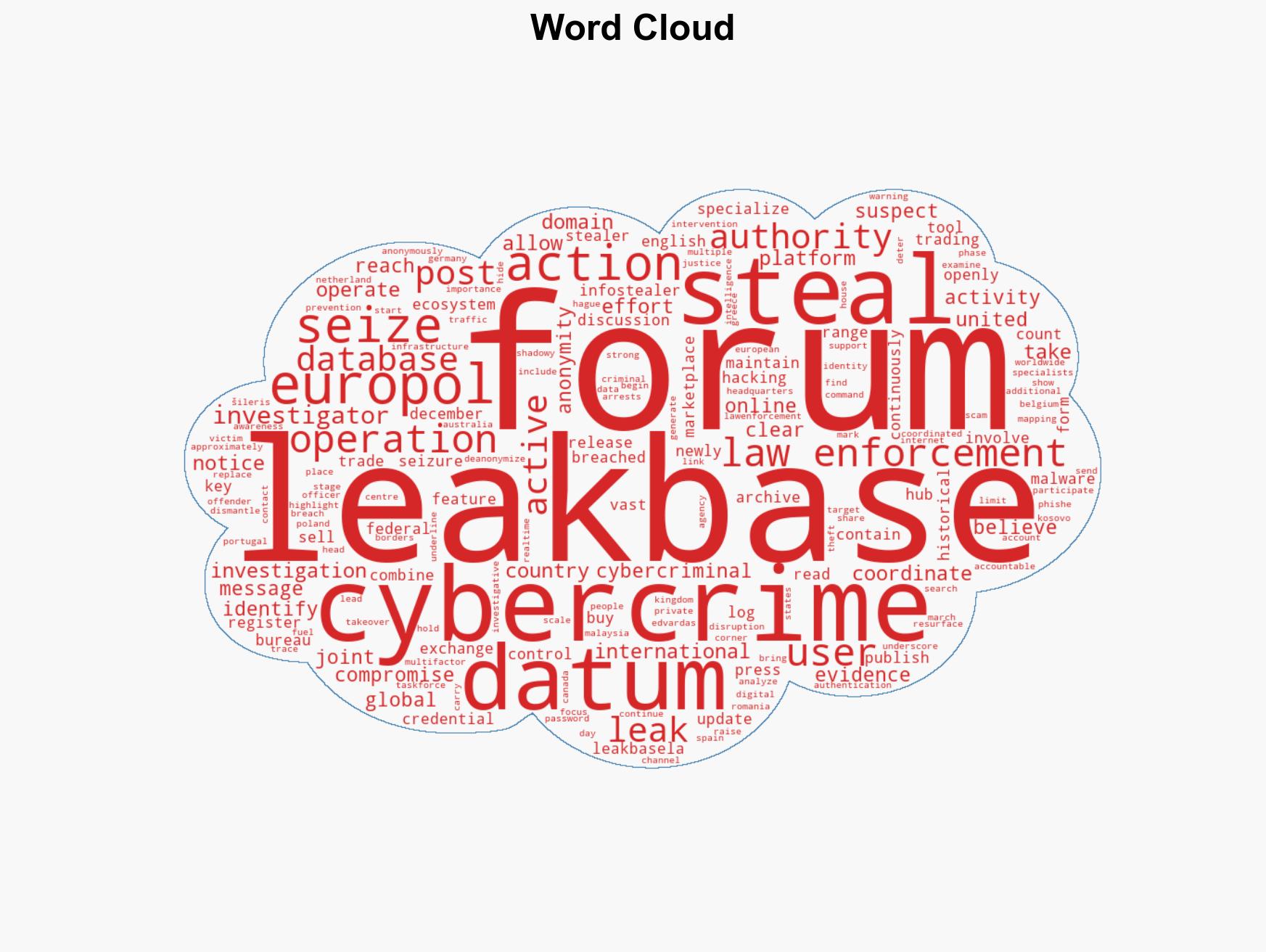
cybersecurity, cybercrime, international cooperation, data breaches, law enforcement, cyber security, identity theft, cyber resilience
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us