FBI identifies Chinese cyber breach of law enforcement data as a significant threat to U.S. national security
Published on: 2026-04-03
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: FBI labels suspected China hack of law enforcement data ‘a major cyber incident’
1. BLUF (Bottom Line Up Front)
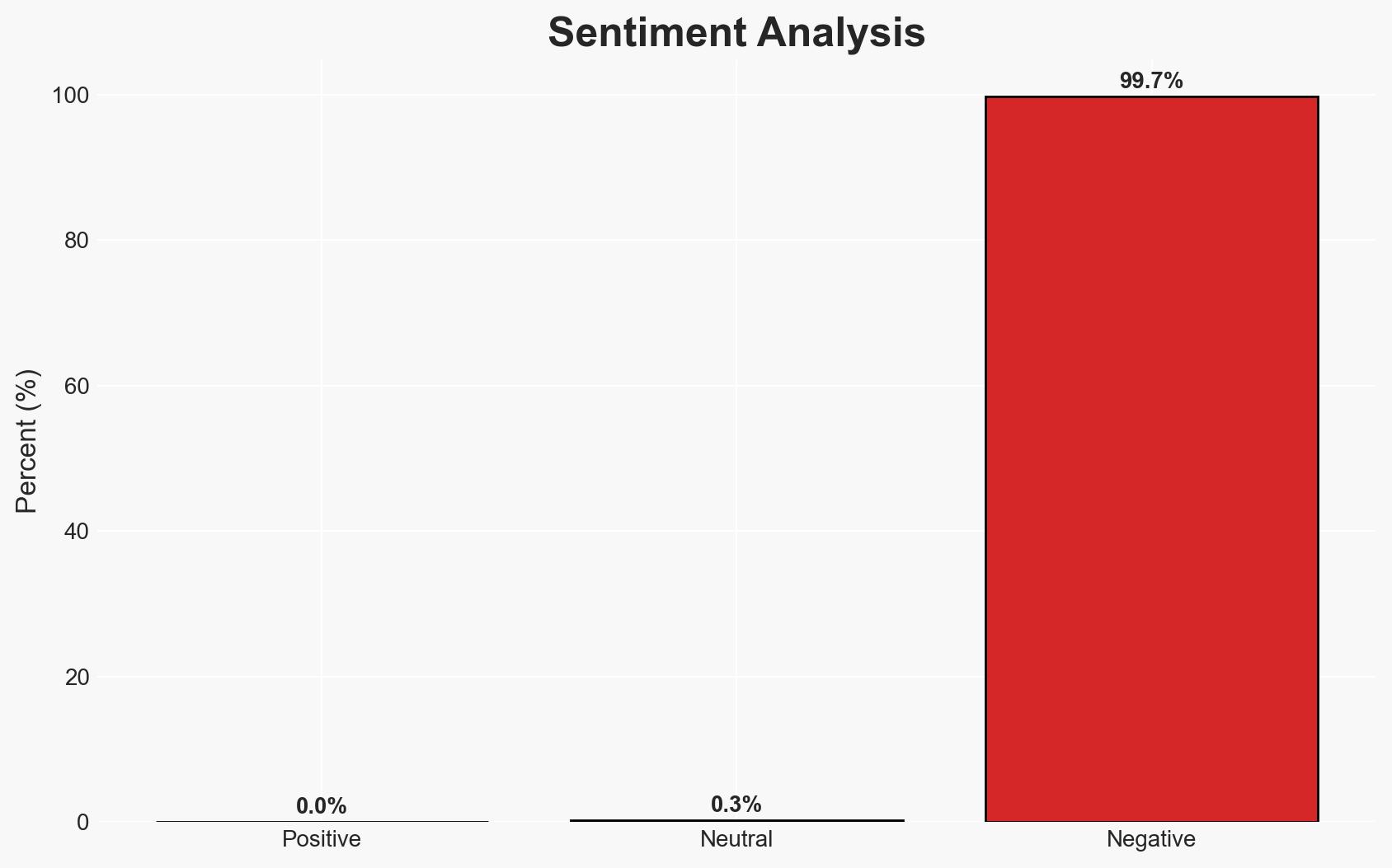
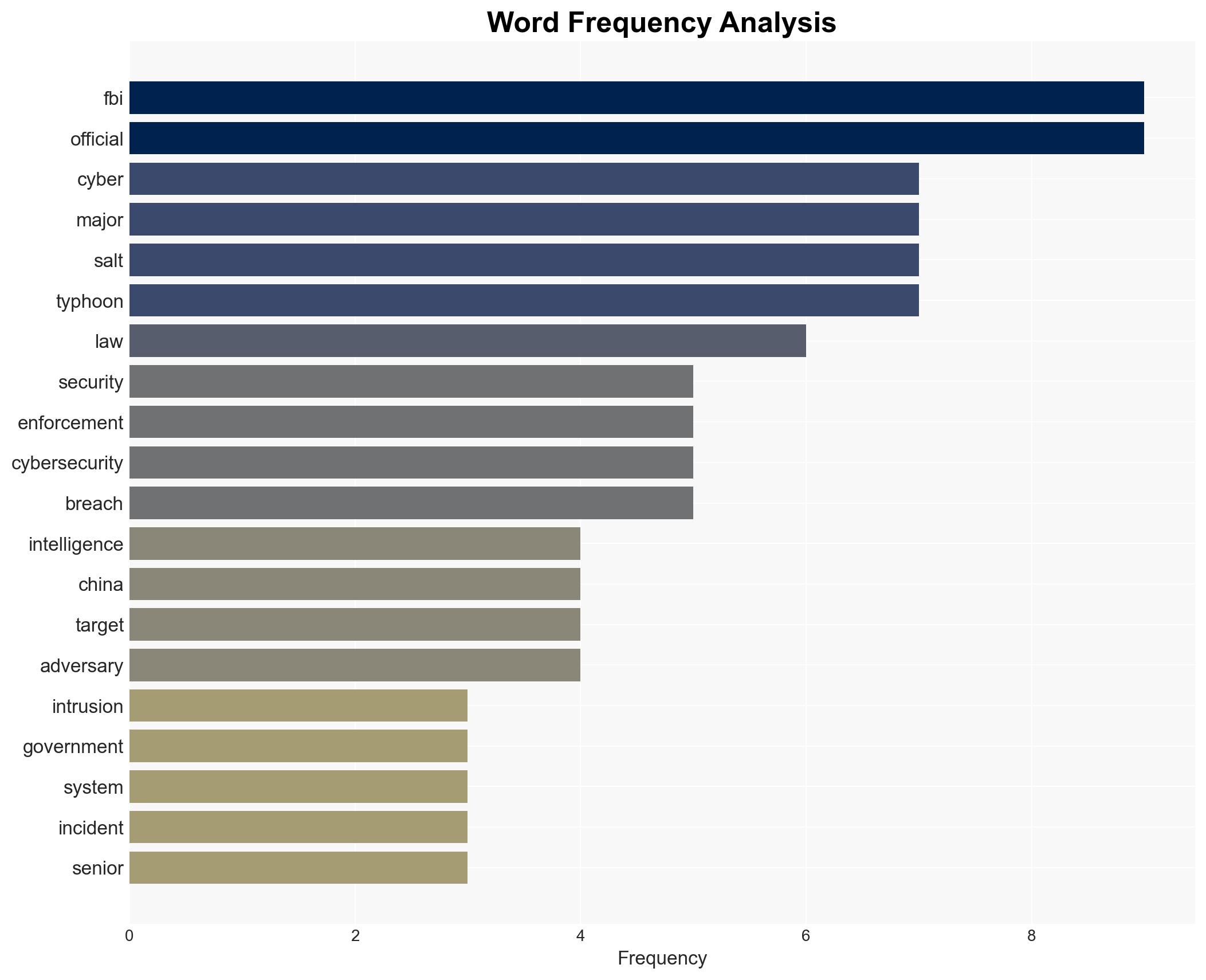
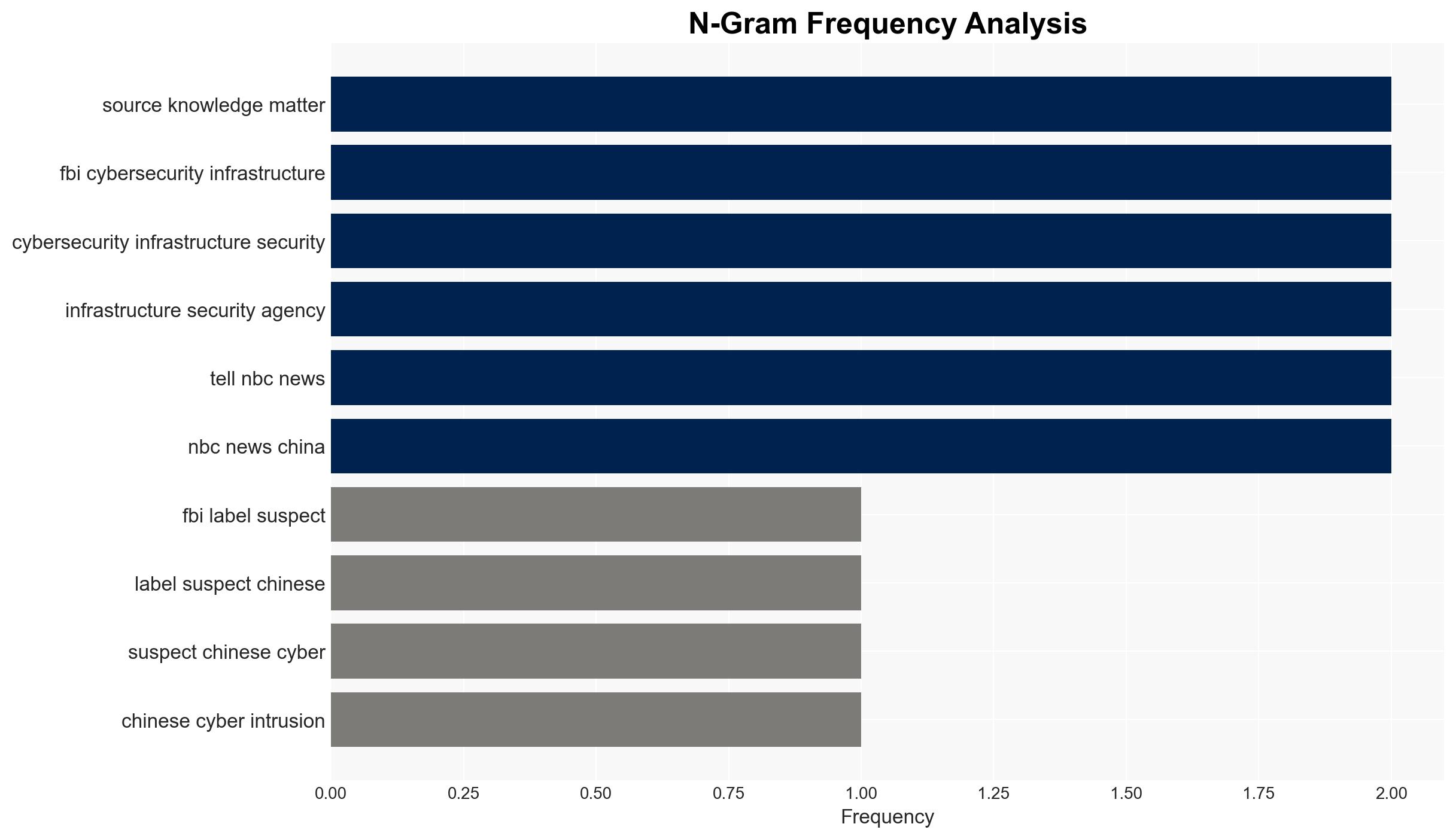
The FBI has identified a suspected Chinese cyber intrusion into a U.S. government surveillance system as a “major incident,” posing significant national security risks. This breach, linked to tactics similar to the Salt Typhoon campaign, highlights ongoing vulnerabilities in U.S. cyber defenses. The most likely hypothesis is that Chinese state-backed actors are responsible, continuing a pattern of aggressive cyber operations. Confidence in this assessment is moderate, given the lack of direct attribution evidence.
2. Competing Hypotheses
- Hypothesis A: The breach was conducted by Chinese state-sponsored actors using tactics consistent with previous operations like Salt Typhoon. Supporting evidence includes the use of similar techniques and the historical pattern of Chinese cyber activities targeting U.S. infrastructure. However, direct attribution remains unconfirmed.
- Hypothesis B: The intrusion could be the work of non-state actors or another nation-state actor using Chinese tactics as a false flag operation. This hypothesis is less supported due to the lack of evidence indicating alternative perpetrators and the alignment of tactics with known Chinese methods.
- Assessment: Hypothesis A is currently better supported due to the consistency of tactics with known Chinese operations and the strategic interests China has in accessing U.S. law enforcement data. Indicators that could shift this judgment include new intelligence on the origin of the attack or evidence of alternative actors.
3. Key Assumptions and Red Flags
- Assumptions: The breach was motivated by strategic intelligence gathering; Chinese state actors have the capability and intent to conduct such operations; U.S. cyber defenses have vulnerabilities that can be exploited.
- Information Gaps: Lack of direct evidence linking the breach to Chinese state actors; details on the specific data accessed and the methods used; potential involvement of insider threats.
- Bias & Deception Risks: Confirmation bias towards attributing cyber incidents to China; potential for Chinese disinformation campaigns to obscure attribution; reliance on sources with potential institutional biases.
4. Implications and Strategic Risks
This development underscores persistent vulnerabilities in U.S. cyber infrastructure and the ongoing threat from state-sponsored cyber operations. It may prompt a reassessment of U.S. cyber defense strategies and international cyber norms.
- Political / Geopolitical: Potential escalation of U.S.-China tensions; impact on diplomatic relations and negotiations.
- Security / Counter-Terrorism: Increased risk of further cyber intrusions; potential compromise of sensitive law enforcement operations.
- Cyber / Information Space: Highlighting the need for enhanced cybersecurity measures; potential for increased cyber espionage activities.
- Economic / Social: Potential economic impacts from compromised data; erosion of public trust in government cybersecurity capabilities.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive forensic analysis of the breach; enhance monitoring of critical systems; engage with international partners for intelligence sharing.
- Medium-Term Posture (1–12 months): Strengthen cyber defenses through public-private partnerships; invest in advanced threat detection technologies; develop a robust cyber deterrence strategy.
- Scenario Outlook:
- Best: Improved U.S.-China cyber dialogue reduces incidents.
- Worst: Escalation to broader cyber conflict with significant economic and security impacts.
- Most-Likely: Continued low-level cyber engagements with periodic breaches.
6. Key Individuals and Entities
- FBI
- Cybersecurity and Infrastructure Security Agency (CISA)
- Sen. Mark Warner, Vice Chair of the Senate Intelligence Committee
- Chinese state-sponsored actors (not specifically named)
7. Thematic Tags
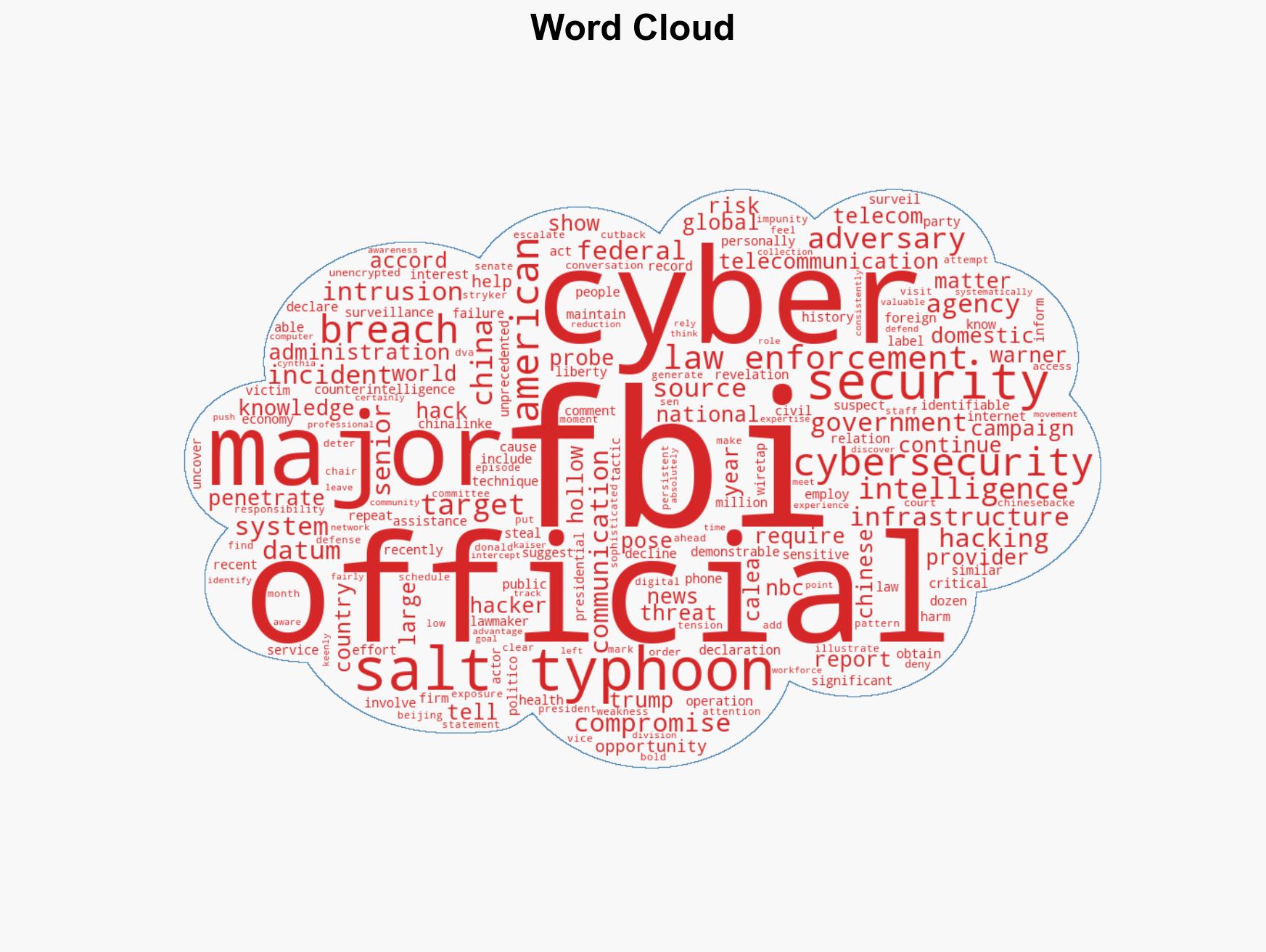
cybersecurity, cyber-espionage, national security, U.S.-China relations, cyber defense, intelligence failure, data breach, cyber operations
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us